Linux 端口转发 端口映射
摘要:端口转发也称端口映射,基本使用的有两种方式,本机端口转发,跨IP端口转发。
本机端口转发
应用场景:我要搭建一台Linux server,使用tomcat作为web容器,让别人维护web项目的发布,这时候会给他们一个普通用户(非root用户)。
分析:tomcat的默认端口是8080,所有用户都可以启动,但是除内部系统外,一般我们会选择使用80作为端口,可是普通用户没有对80的权限。怎么办,这个时候可以提前把80端口映射到8080端口,当tomcat以8080端口启动后就可以使用80端口访问。
具体配置:
[root@localhost sbin]# iptables -t nat -A PREROUTING -p tcp --dport 80 -j REDIRECT --to-ports 8080
[root@localhost sbin]# service iptables save
[root@localhost sbin]# service iptables restart会返回如下信息:
iptables: Saving firewall rules to /etc/sysconfig/iptables:[ OK ]这说明修改了iptables文件了,可以放心使用。清楚的知道规则报错到了/etc/sysconfig/iptables文件。
跨IP端口转发
应用场景:2年前购买了一台VPS1,由于价格高,所以100元买的配置很低,同时购买了域名,并且绑定的是这台VPS1。今年由于VPS降价,我又花100元买了台配置很高的VPS2。安装了很多服务在这台VPS2上。由于这台新买的VPS2没有绑定域名,我也不想换掉域名,所以我想通过域名访问到我新的VPS2上的服务。
分析:显而易见,这两台VPS的IP地址不同,属于跨IP的转发。假设需要通过域名:80到VPS2:8080。【1.1.1.1:80 -> 2.2.2.2:8080】由于是跨IP,所以首先要开启IP转发功能。
开启IP转发
开启IP转发有两种,一种是临时性的,重启就没有了,一种是永久性的。重启也会存在。
临时方案
配置如下:
echo 1 >/proc/sys/net/ipv4/ip_forward修改ip_forward文件,立即生效,重启失效。
永久方案
配置如下:
vi /etc/sysctl.conf
# 找到下面的值并将0改成1
net.ipv4.ip_forward = 1
sysctl –p(使之立即生效)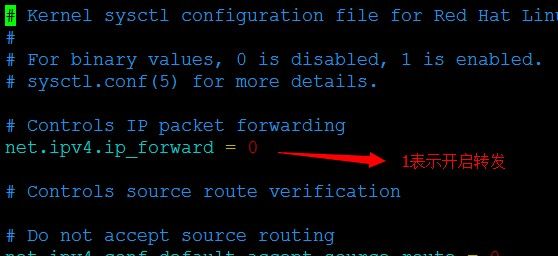
以上就开启了对IP转发的支持,然后再配置端口转发,此时的端口转发与本机的端口转发略有不同。
配置端口转发
# iptables -t nat -A PREROUTING -p tcp -d 1.1.1.1 --dport 80 -j DNAT --to-destination 2.2.2.2:8080
# iptables -t nat -A POSTROUTING -p tcp -s 2.2.2.2 --sport 8080 -j SNAT --to-source 1.1.1.1
# service iptables save当然也可以直接写到iptables文件中:
-A PREROUTING -p tcp -d 1.1.1.1 --dport 80 -j DNAT --to-destination 2.2.2.2:8080
-A POSTROUTING -p tcp -s 2.2.2.2 --sport 8080 -j SNAT --to-source 1.1.1.1注:如果你用的是一个没有开启的端口,比如小与1024的端口,假如说是800,而不是8080,那么要记着打开这些端口。
方式如下:
-A INPUT -p tcp -m state --state NEW -m tcp --dport 800 -j ACCEPT配置完成后,记着重启防火墙
# service iptables restart然后就可以使用了。
遇到的问题
端口映射设置好是成功的,可是过一会就失效。发现了一个问题
系统的iptables服务没有启动,比如可以使用如下命令查看:
# chkconfig
auditd 0:off 1:off 2:on 3:on 4:on 5:on 6:off
blk-availability 0:off 1:on 2:on 3:on 4:on 5:on 6:off
crond 0:off 1:off 2:on 3:on 4:on 5:on 6:off
ip6tables 0:off 1:off 2:off 3:off 4:off 5:off 6:off
iptables 0:off 1:off 2:off 3:off 4:off 5:off 6:off
lvm2-monitor 0:off 1:on 2:on 3:on 4:on 5:on 6:off
mcollective 0:off 1:off 2:on 3:on 4:on 5:on 6:off
netconsole 0:off 1:off 2:off 3:off 4:off 5:off 6:off
netfs 0:off 1:off 2:off 3:on 4:on 5:on 6:off
network 0:off 1:off 2:on 3:on 4:on 5:on 6:off
ntpd 0:off 1:off 2:on 3:on 4:on 5:on 6:off
ntpdate 0:off 1:off 2:off 3:off 4:off 5:off 6:off
puppet 0:off 1:off 2:on 3:on 4:on 5:on 6:off
rdisc 0:off 1:off 2:off 3:off 4:off 5:off 6:off
restorecond 0:off 1:off 2:off 3:off 4:off 5:off 6:off
rhnsd 0:off 1:off 2:on 3:on 4:on 5:on 6:off
rsyslog 0:off 1:off 2:on 3:on 4:on 5:on 6:off
saslauthd 0:off 1:off 2:off 3:off 4:off 5:off 6:off
sendmail 0:off 1:off 2:on 3:on 4:on 5:on 6:off
snmpd 0:off 1:off 2:on 3:on 4:on 5:on 6:off
snmptrapd 0:off 1:off 2:off 3:off 4:off 5:off 6:off
sshd 0:off 1:off 2:on 3:on 4:on 5:on 6:off
udev-post 0:off 1:on 2:on 3:on 4:on 5:on 6:off找到第6行,发现iptables对应的level开关都是off,这个时候要把off改成on即可。
# chkconfig --help
chkconfig version 1.3.49.3 - Copyright (C) 1997-2000 Red Hat, Inc.
This may be freely redistributed under the terms of the GNU Public License.
usage: chkconfig [--list] [--type ] [name]
chkconfig --add
chkconfig --del
chkconfig --override
chkconfig [--level ] [--type ]
使用命令:
# chkconfig --level 012345 iptables on重新查看:
# chkconfig
auditd 0:off 1:off 2:on 3:on 4:on 5:on 6:off
blk-availability 0:off 1:on 2:on 3:on 4:on 5:on 6:off
crond 0:off 1:off 2:on 3:on 4:on 5:on 6:off
ip6tables 0:off 1:off 2:off 3:off 4:off 5:off 6:off
iptables 0:on 1:on 2:on 3:on 4:on 5:on 6:on
lvm2-monitor 0:off 1:on 2:on 3:on 4:on 5:on 6:off
mcollective 0:off 1:off 2:on 3:on 4:on 5:on 6:off
netconsole 0:off 1:off 2:off 3:off 4:off 5:off 6:off
netfs 0:off 1:off 2:off 3:on 4:on 5:on 6:off
network 0:off 1:off 2:on 3:on 4:on 5:on 6:off
ntpd 0:off 1:off 2:on 3:on 4:on 5:on 6:off
ntpdate 0:off 1:off 2:off 3:off 4:off 5:off 6:off
puppet 0:off 1:off 2:on 3:on 4:on 5:on 6:off
rdisc 0:off 1:off 2:off 3:off 4:off 5:off 6:off
restorecond 0:off 1:off 2:off 3:off 4:off 5:off 6:off
rhnsd 0:off 1:off 2:on 3:on 4:on 5:on 6:off
rsyslog 0:off 1:off 2:on 3:on 4:on 5:on 6:off
saslauthd 0:off 1:off 2:off 3:off 4:off 5:off 6:off
sendmail 0:off 1:off 2:on 3:on 4:on 5:on 6:off
snmpd 0:off 1:off 2:on 3:on 4:on 5:on 6:off
snmptrapd 0:off 1:off 2:off 3:off 4:off 5:off 6:off
sshd 0:off 1:off 2:on 3:on 4:on 5:on 6:off
udev-post 0:off 1:on 2:on 3:on 4:on 5:on 6:off这个时候就解决问题了。
原文链接:Linux配置端口转发