远程访问控制 (SShd、 TCP Wrappers)
SSH远程管理和TCP Wrappers控制
SSH远程管理
SSH协议
为客户机提供安全的Shell环境,用于远程管理
默认端口:TCP 22
OpenSSH
服务名称:sshd
服务端主程序:/usr/sbin/sshd
服务端配置文件:/etc/ssh/sshd_config
服务监听选项
端口号、协议版本、监听IP地址
禁用反向解析
用户登录控制
禁止root用户、空密码用户
登录时间、重试次数
AllowUsers、DenyUsers
AllowUsers不要与DenyUsers同时使用
登录验证对象
服务器中的本地用户账号
登录验证方式
密码验证:核对用户名、密码是否匹配
秘钥对验证:核对客户的私钥、服务端公钥是否匹配
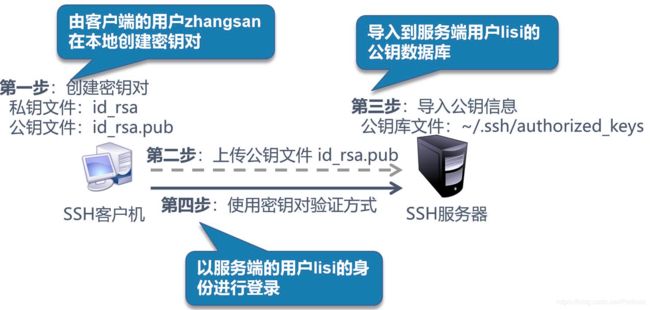
构建秘钥对验证的SSH体系
整体实现过程
本章环境:VM虚拟机,一台服务器作为服务端,一台服务器作为客户端
本章目的:了解sshd远程登录管理,密钥对验证,Tcp wappers访问控制
一.sshd远程登录
1.查看sshd服务
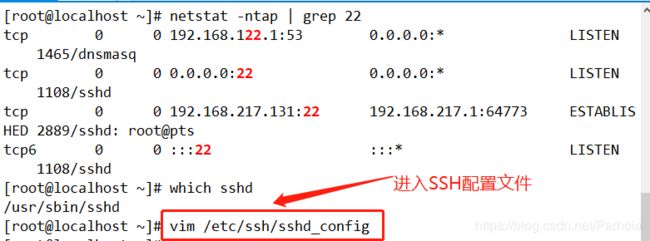
[root@localhost ~]# netstat -ntap | grep 22
tcp 0 0 192.168.122.1:53 0.0.0.0:* LISTEN 3252/dnsm
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 968/sshd //默认我们的SSHD是开启的
tcp 0 0 127.0.0.1:6010 0.0.0.0:* LISTEN 16227/sshot@pt
tcp 0 0 192.168.17.128:49342 180.97.251.226:80 TIME_WAIT -
tcp 0 0 192.168.17.128:42522 202.141.176.110:80
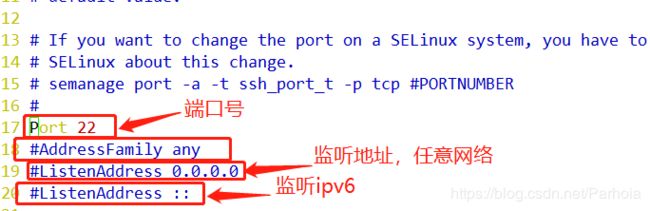
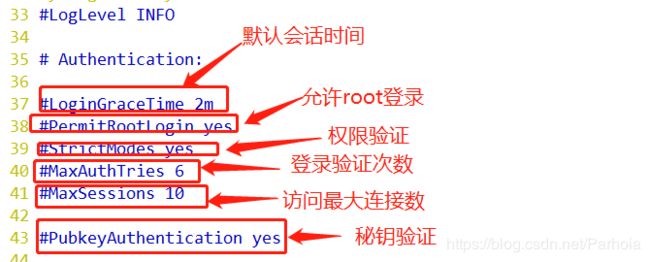
2.了解SSHD服务端配置文件
[root@localhost ~]# vim /etc/ssh/sshd_config //服务端的SSHD配置文件
17 #Port 22 //端口
18 #AddressFamily any
19 #ListenAddress 0.0.0.0 //监听地址
20 #ListenAddress :: //IPV6地址
37#LoginGraceTime 2m //2分钟会话时间
38 #PermitRootLogin yes //允许ROOT登录
39 #StrictModes yes //验证你的访问权限
40 #MaxAuthTries 6 //验证次数
41 #MaxSessions 10 // 访问最大连接数10个
#PubkeyAuthentication yes //公钥验证开启
3.使用客户端去远程登录服务端的ROOT用户
[root@test02 ~]# ssh [email protected]
The authenticity of host '192.168.17.128 (192.168.17.128)' can't be established.
ECDSA key fingerprint is SHA256:Rpsrtp0nMlVYADWOhRjM0UVz6wVl682cNuzxhF0Q7C8.
ECDSA key fingerprint is MD5:fa:c3:d9:5c:96:87:ce:16:d8:63:b3:0c:7b:26:45:1f.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '192.168.17.128' (ECDSA) to the list of known hosts.
[email protected]'s password:
Last login: Mon Sep 16 12:07:36 2019
4.把服务端的远程登录ROOT用户关掉
37 #LoginGraceTime 2m
38 #PermitRootLogin no //禁止远程用户用ROOT登录
39 #StrictModes yes
40 #MaxAuthTries 6
41 #MaxSessions 10
5.去服务端验证是否能登录ROOT用户
[root@test02 ~]# ssh [email protected]
[email protected]'s password:
Permission denied, please try again.
[email protected]'s password:
6.客户端切换到普通用户lisi,再切到ROOT用户也行(不安全)
[root@test02 ~]# ssh [email protected]
[email protected]'s password:
[lisi@test01 ~]$ su - root
密码:
上一次登录:一 9月 16 12:17:31 CST 2019pts/2 上
最后一次失败的登录:一 9月 16 12:25:59 CST 2019pts/2 上
最有一次成功登录后有 1 次失败的登录尝试。
[root@test01 ~]#
7.把服务端开启PAM认证
vim /etc/pam.d/su
//把“#”号去掉auth required pam_wheel.so use_uid
auth substack system-auth
auth include postlogin
8.再去客户端去验证一下
[lisi@test01 ~]$ su - root
密码:
su: 拒绝权限
9.在客户端尝试输错三次密码,发现就退出来了,我们原本服务端设置的是验证次数是6次
[root@test02 ~]# ssh [email protected]
[email protected]'s password:
Permission denied, please try again.
[email protected]'s password:
Permission denied, please try again.
[email protected]'s password:
Permission denied, please try again.
[root@test02 ~]#
10.在客户端切到ROOT用户,设置验证次数为8次
[root@test01 ~]# ssh -o NumberOfPasswordPrompts=8 [email protected]
The authenticity of host '192.168.17.128 (192.168.17.128)' can't be established.
ECDSA key fingerprint is SHA256:Rpsrtp0nMlVYADWOhRjM0UVz6wVl682cNuzxhF0Q7C8.
ECDSA key fingerprint is MD5:fa:c3:d9:5c:96:87:ce:16:d8:63:b3:0c:7b:26:45:1f.
Are you sure you want to continue connecting (yes/no)? yes
Warning: Permanently added '192.168.17.128' (ECDSA) to the list of known hosts.
[email protected]'s password:
Permission denied, please try again.
[email protected]'s password:
Permission denied, please try again.
[email protected]'s password:
Permission denied, please try again.
[email protected]'s password:
Permission denied, please try again.
[email protected]'s password:
Permission denied, please try again.
[email protected]'s password:
Received disconnect from 192.168.17.128 port 22:2: Too many authentication failures
Authentication failed.
[root@test01 ~]#
11.设置SSH远程登录的黑白名单
37 #LoginGraceTime 2m
38 #PermitRootLogin no
39 #StrictModes yes
40 #MaxAuthTries 6
41 #MaxSessions 10
42 Allow Users [email protected]
//只允许chen这个用户用192.168.17.130地址登录
[root@test01 ~]# systemctl restart sshd
12.了解三种远程管理
scp 远程复制
sftp get 远程下载文件
sftp put 远程上传文件
二.密钥对验证登录
1.服务端开启公私钥验证登录
[root@localhost ~]# vim /etc/ssh/sshd_config //服务端的SSHD配置文件
43 PubkeyAuthentication yes 把“#”去掉开启公私钥验证登录
44
45 # The default is to check both .ssh/authorized_keys and .ssh/authorized_keys 2
46 # but this is overridden so installations will only check .ssh/authorized_ke ys
47 AuthorizedKeysFile .ssh/authorized_keys
//生成的公私密钥会在这个目录底下
2.客户端,给chen用户生成密钥
[root@client ~]# ls /home/
chen
[root@client ~]# ssh-keygen -t ecdsa
Generating public/private ecdsa key pair.
Enter file in which to save the key (/root/.ssh/id_ecdsa):
Enter passphrase (empty for no passphrase):
Enter same passphrase again:
Your identification has been saved in /root/.ssh/id_ecdsa.
Your public key has been saved in /root/.ssh/id_ecdsa.pub.
The key fingerprint is:
SHA256:HqV9MQWYPqLHSodJciQEDpGhsbQheF3gVqXLMD6mhTo root@client
The key's randomart image is:
+---[ECDSA 256]---+
|B*.+ooo.. o... |
|*=+.o... o . |
|oo. =o. .. o |
| +.+o..+o o |
| . =+o=S.... |
| . + .=.+. . |
|E . . +. |
| . . |
| |
+----[SHA256]-----+
3.查看chen用户当中的公私钥目录
[root@client ~]# ls -a
. .bash_logout .dbus .mozilla 模板
.. .bash_profile .esd_auth .ssh 视频
.1234.txt.swp .bashrc .ICEauthority .tcshrc 图片
abc .cache initial-setup-ks.cfg test 文档
abc.txt chen is this 下载
anaconda-ks.cfg chenchen .lesshst .viminfo 音乐
.anacond-ks.cfg.swp .config .local .Xauthority 桌面
.bash_history .cshrc lshelp1.txt 公共
[root@client ~]# cd .ssh/
[root@client .ssh]# ls
id_ecdsa id_ecdsa.pub known_hosts
4.把chen公钥发送给服务端的公钥目录中
[root@client .ssh]# ssh-copy-id -i id_ecdsa.pub [email protected]
/usr/bin/ssh-copy-id: INFO: Source of key(s) to be installed: "id_ecdsa.pub"
The authenticity of host '192.168.17.128 (192.168.17.128)' can't be established.
ECDSA key fingerprint is SHA256:Rpsrtp0nMlVYADWOhRjM0UVz6wVl682cNuzxhF0Q7C8.
ECDSA key fingerprint is MD5:fa:c3:d9:5c:96:87:ce:16:d8:63:b3:0c:7b:26:45:1f.
Are you sure you want to continue connecting (yes/no)? yes
/usr/bin/ssh-copy-id: INFO: attempting to log in with the new key(s), to filter out any that are already installed
/usr/bin/ssh-copy-id: INFO: 1 key(s) remain to be installed -- if you are prompted now it is to install the new keys
[email protected]'s password:
Number of key(s) added: 1
Now try logging into the machine, with: "ssh '[email protected]'"
and check to make sure that only the key(s) you wanted were added.
5.去服务端查看有没有chen用户的公钥
[root@localhost chen]# cd .ssh/
[root@localhost .ssh]# ls
authorized_keys
[root@localhost .ssh]# cat authorized_keys
ecdsa-sha2-nistp256 AAAAE2VjZHNhLXNoYTItbmlzdHAyNTYAAAAIbmlzdHAyNTYAAABBBC3jJu7k3skpOWd5azNtHhohBCyQvcE5vMQblIICOn48GGL3h1tQ9d7m34liu7YdXcdY+oLyQvgl23xiP9Au8ug= root@client
6.客户端远程密钥对登录验证
[root@client .ssh]# ssh [email protected]
Enter passphrase for key '/root/.ssh/id_ecdsa':
Last login: Sat Aug 10 00:32:52 2019
7.免交互,免去密钥对登录验证
[chen@localhost ~]$ exit
登出
Connection to 192.168.17.128 closed.
[root@client .ssh]# ssh-agent bash //代理bash环境
[root@client .ssh]# ssh-add //添加我们密钥对的密码
Enter passphrase for /root/.ssh/id_ecdsa:
Identity added: /root/.ssh/id_ecdsa (/root/.ssh/id_ecdsa)
[root@client .ssh]# ssh [email protected]
Last login: Mon Sep 16 13:09:06 2019 from 192.168.17.134
[chen@localhost ~]$
三.Tcp wappers 访问控制
访问控制策略:
先检查hosts.allow,找到匹配则允许访问
否则再检查hosts.deny,找到则拒绝访问
若两个文件中均无匹配策略,则默认允许
访问
1.到服务端设置访问控制
[root@localhost ~]# vim /etc/hosts.allow
hosts.allow This file contains access rules which are used to
allow or deny connections to network services that
either use the tcp_wrappers library or that have been
started through a tcp_wrappers-enabled xinetd.
See 'man 5 hosts_options' and 'man 5 hosts_access'
for information on rule syntax.
See 'man tcpd' for information on tcp_wrappers
sshd:192.168.17.130 //添加只允许访问的地址
~
[root@localhost ~]# vim /etc/hosts.deny
hosts.deny This file contains access rules which are used to
deny connections to network services that either use
the tcp_wrappers library or that have been
started through a tcp_wrappers-enabled xinetd.
The rules in this file can also be set up in
/etc/hosts.allow with a 'deny' option instead.
See 'man 5 hosts_options' and 'man 5 hosts_access'
for information on rule syntax.
See 'man tcpd' for information on tcp_wrappers
sshd:192.168.17.128
~
~
~