大纲
一、引子(案例)
二、持久连接定义与原理
三、持久连接分类
四、持久连接命令
五、LVS-DR模式
六、PPC 演示
七、PCC 演示
八、PNMP 演示
注:实验环境,操作系统 CentOS 6.4 X86_64
一、引子(案例)
对于电子商务网站来说,用户在挑选商品的时候使用的是80端口来浏览的,当付款的时候则是通过443的ssl加密的方式,当然当用户挑选完商品付款的时候,我们当然不希望https的443跳转到另外一台REAL SERVER上,很显然应该是同一REAL SERVER才对,这时候就要用到基于防火墙标记的持久连接,通过定义端口的姻亲关系来实现。在生产环境中用的最多的也是PNMP即基于防火墙标记的持久连接。好了引子就说到这下面我们就来详细说说LVS的持久连接……
二、持久连接定义与原理
1.定义
持久连接是指无论使用什么算法,LVS持久都能实现在一定时间内,将来自同一个客户端请求派发至此前选定的RS。
2.原理
当使用LVS持久性的时候,Director在内部使用一个连接根据记录称之为“持久连接模板”来确保所有来自同一个客户端的请求被分发到同一台Real Server上。
说明:持久连接模板是指每一个客户端 及分配给它的RS的映射关系;
三、持久连接分类
1.PPC(Persistent Port Connections):将来自于同一个客户端对同一个集群服务的请求,始终定向至此前选定的RS;(持久端口连接)
例如:client---->LVS(80)---->RS1 或 client---->LVS(23)---->RS2
缺陷:期望访问不同的端口到同一台RS上,无法实现。
配置:
ipvsadm -A -t 172.16.100.1:80 -s rr -p 3600 ipvsadm -a -t 172.16.100.1:80 -r 172.16.100.10 -g -w 2 ipvsadm -a -t 172.16.100.1:80 -r 172.16.100.11 -g -w 2
2.PCC(Persistent Client Connections):将来自于同一个客户端对所有端口的请求,始终定向至此前选定的RS;(持久客户端连接)
说明:PCC是一个虚拟服务没有端口号(或者端口号为0),以"-p" 来标识服务。
缺陷:定向所有服务,期望访问不同的Real Server无法实现。
配置:
ipvsadm -A -t 172.16.100.1:0 -s rr -p 3600 ipvsadm -a -t 172.16.100.1:0 -r 172.16.100.10 -g -w 2 ipvsadm -a -t 172.16.100.1:0 -r 172.16.100.11 -g -w 2
3.PNMPP(Persistent Netfilter Marked Packet Persistence):持久防火墙标记连接,根据iptables 的规则,将对于某类服务几个不同端口的访问定义为一类;
先对某一特定类型的数据包打上标记,然后再将基于某一类标记的服务送到后台的Real Server上去,后台的Real Server 并不识别这些标记。将持久和防火墙标记结合起来就能够实现端口姻亲功能,只要是来自某一客户端的对某一特定服务(需要不同的端口)的访问都定义到同一台Real Server上去。
案例:一个用户在访问购物网站时同时使用HTTP(80)和HTTPS(443)两种协议,我们需要将其定义到同一台Real Server上,而其他的服务不受限制。
配置:
iptables -t mangle -A PREROUTING -d 172.16.100.1 -i eth0 -p tcp --dport 80 -j MARK --set-mark 8 iptables -t mangle -A PREROUTING -d 172.16.100.1 -i eth0 -p tcp --dport 443 -j MARK --set-mark 8 ipvsadm -A -f 8 -s rr -p 600 ipvsadm -a -f 8 -r 172.16.100.10 -g -w 2 ipvsadm -a -f 8 -r 172.16.100.11 -g -w 1
四、持久连接命令
ipvsadm -A|E … -p timeout 选项 -p timeout 指定持久连接时长,默认为360秒,单位是秒,即6分钟。
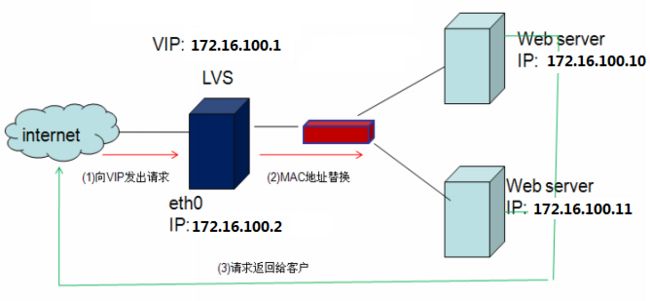
五、LVS-DR模式
1.实验效果图
2.具体说明
说明: 这里有四台虚拟机,一台Director,两台Real Server,一台CA证书颁发机构(在演示PNMP时用到),所以有虚拟机都是单网卡!所有的网卡模式都是NAT模式,方便与本机进行测试!
3.配置Director
(1).配置ip地址
eth0 172.16.100.2 DIP eth0:0 172.16.100.1 VIP
(2).查看
[root@master ~]# ifconfig
eth0 Link encap:Ethernet HWaddr 00:0C:29:E5:AE:A1
inet addr:172.16.100.2 Bcast:172.16.100.255 Mask:255.255.255.0
inet6 addr: fe80::20c:29ff:fee5:aea1/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:226 errors:0 dropped:0 overruns:0 frame:0
TX packets:143 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:21199 (20.7 KiB) TX bytes:15679 (15.3 KiB)
eth0:0 Link encap:Ethernet HWaddr 00:0C:29:E5:AE:A1
inet addr:172.16.100.1 Bcast:172.16.100.255 Mask:255.255.255.0
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:16436 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:0 (0.0 b) TX bytes:0 (0.0 b)
4.配置Real Server 1
RS1:
eth0: 172.16.100.10 RIP lo0:0 172.16.100.1 VIP
(1).关闭arp响应
[root@rs1 ~]# sysctl -w net.ipv4.conf.eth0.arp_announce=2 [root@rs1 ~]# sysctl -w net.ipv4.conf.all.arp_announce=2 [root@rs1 ~]# echo 1 > /proc/sys/net/ipv4/conf/eth0/arp_ignore [root@rs1 ~]# echo 1 > /proc/sys/net/ipv4/conf/all/arp_ignore
(2).配置VIP
[root@rs1 ~]# ifconfig lo:0 172.16.100.1 broadcast 172.16.100.1 netmask 255.255.255.255 up
[root@rs1 ~]# ifconfig
eth0 Link encap:Ethernet HWaddr 00:0C:29:91:45:90
inet addr:172.16.100.10 Bcast:172.16.100.255 Mask:255.255.255.0
inet6 addr: fe80::20c:29ff:fe91:4590/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:735 errors:0 dropped:0 overruns:0 frame:0
TX packets:528 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:66150 (64.5 KiB) TX bytes:75461 (73.6 KiB)
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:16436 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:0 (0.0 b) TX bytes:0 (0.0 b)
lo:0 Link encap:Local Loopback
inet addr:172.16.100.1 Mask:255.255.255.255
UP LOOPBACK RUNNING MTU:16436 Metric:1
(3).增加路由
[root@rs1 ~]# route add -host 172.16.100.1 dev lo:0 [root@rs1 ~]# route Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface 172.16.100.1 * 255.255.255.255 UH 0 0 0 lo 172.16.100.0 * 255.255.255.0 U 0 0 0 eth0 link-local * 255.255.0.0 U 1002 0 0 eth0
(4).安装httpd
[root@rs1 ~]# yum install -y httpd [root@rs1 ~]# vim /var/www/html/index.html #增加测试页面 rs1.test.com
5.配置Real Server 2
RS2:
eth0: 172.16.100.11 RIP lo0:0 172.16.100.1 VIP
(1).关闭arp响应
sysctl -w net.ipv4.conf.eth0.arp_announce=2 sysctl -w net.ipv4.conf.all.arp_announce=2 echo 1 > /proc/sys/net/ipv4/conf/eth0/arp_ignore echo 1 > /proc/sys/net/ipv4/conf/all/arp_ignore
(2).配置VIP
[root@rs2 ~]# ifconfig lo:0 172.16.100.1 broadcast 172.16.100.1 netmask 255.255.255.255 up
[root@rs2 ~]# ifconfig
eth0 Link encap:Ethernet HWaddr 00:0C:29:61:92:17
inet addr:172.16.100.11 Bcast:172.16.100.255 Mask:255.255.255.0
inet6 addr: fe80::20c:29ff:fe61:9217/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:413 errors:0 dropped:0 overruns:0 frame:0
TX packets:170 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:37254 (36.3 KiB) TX bytes:19865 (19.3 KiB)
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:16436 Metric:1
RX packets:0 errors:0 dropped:0 overruns:0 frame:0
TX packets:0 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:0 (0.0 b) TX bytes:0 (0.0 b)
lo:0 Link encap:Local Loopback
inet addr:172.16.100.1 Mask:255.255.255.255
UP LOOPBACK RUNNING MTU:16436 Metric:1
(3).增加路由
[root@rs2 ~]# route add -host 172.16.100.1 dev lo:0 [root@rs2 ~]# route Kernel IP routing table Destination Gateway Genmask Flags Metric Ref Use Iface 172.16.100.1 * 255.255.255.255 UH 0 0 0 lo 172.16.100.0 * 255.255.255.0 U 0 0 0 eth0 link-local * 255.255.0.0 U 1002 0 0 eth0
(4).安装httpd
[root@rs2 ~]# yum install -y httpd [root@rs2 ~]# vim /var/www/html/index.html #增加测试页面 rs2.test.com
6.配置LVS-DR
[root@master ~]# yum install -y ipvsadm [root@master ~]# ipvsadm -A -t 172.16.100.1:80 -s rr #为了演示效果我这里用了rr调度算法 [root@master ~]# ipvsadm -a -t 172.16.100.1:80 -r 172.16.100.10 -g -w 1 [root@master ~]# ipvsadm -a -t 172.16.100.1:80 -r 172.16.100.11 -g -w 1 [root@master ~]# ipvsadm -L -n IP Virtual Server version 1.2.1 (size=4096) Prot LocalAddress:Port Scheduler Flags -> RemoteAddress:Port Forward Weight ActiveConn InActConn TCP 172.16.100.1:80 rr -> 172.16.100.10:80 Route 1 0 0 -> 172.16.100.11:80 Route 1 0 0
7.测试
[root@master ~]# ipvsadm -L -n IP Virtual Server version 1.2.1 (size=4096) Prot LocalAddress:Port Scheduler Flags -> RemoteAddress:Port Forward Weight ActiveConn InActConn TCP 172.16.100.1:80 rr -> 172.16.100.10:80 Route 1 0 12 -> 172.16.100.11:80 Route 1 0 12
准备工作全部完成下面我们来演示LVS持久连接功能!
六、PPC 演示
1.配置持久连接为3600秒
[root@master ~]# ipvsadm -E -t 172.16.100.1:80 -s rr -p 3600
2.查看持久连接
[root@master ~]# ipvsadm -L -n IP Virtual Server version 1.2.1 (size=4096) Prot LocalAddress:Port Scheduler Flags -> RemoteAddress:Port Forward Weight ActiveConn InActConn TCP 172.16.100.1:80 rr persistent 3600 -> 172.16.100.10:80 Route 1 0 0 -> 172.16.100.11:80 Route 1 0 0
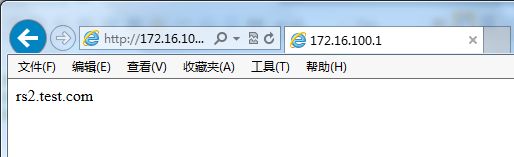
3.测试持久连接
[root@master ~]# ipvsadm -L -n IP Virtual Server version 1.2.1 (size=4096) Prot LocalAddress:Port Scheduler Flags -> RemoteAddress:Port Forward Weight ActiveConn InActConn TCP 172.16.100.1:80 rr persistent 3600 -> 172.16.100.10:80 Route 1 0 0 -> 172.16.100.11:80 Route 1 0 37
大家可以看到,不断的刷新,请求始终在Real Server 2上! 说明,lvs持久连接 PPC 模式测试成功,下面我们继续
4.在Real Server 1与Real Server2 上开启telnet 与 ssh 并做成集群
(1).安装telnet服务
RS1:
[root@rs1 ~]# yum install -y telnet*
[root@rs1 ~]# vim /etc/xinetd.d/telnet
# default: on
# description: The telnet server serves telnet sessions; it uses \
# unencrypted username/password pairs for authentication.
service telnet
{
flags = REUSE
socket_type = stream
wait = no
user = root
server = /usr/sbin/in.telnetd
log_on_failure += USERID
disable = no #将yes改为no
}
[root@rs1 ~]# service xinetd restart
[root@rs1 ~]# netstat -ntulp | grep :23
tcp 0 0 :::23 :::* LISTEN 2149/xinetd
RS2:
[root@rs ~]# yum install -y telnet*
[root@rs2 ~]# vim /etc/xinetd.d/telnet
# default: on
# description: The telnet server serves telnet sessions; it uses \
# unencrypted username/password pairs for authentication.
service telnet
{
flags = REUSE
socket_type = stream
wait = no
user = root
server = /usr/sbin/in.telnetd
log_on_failure += USERID
disable = no #将yes改为no
}
[root@rs2 ~]# service xinetd restart
[root@rs2 ~]# netstat -ntulp | grep :23
tcp 0 0 :::23 :::* LISTEN 2149/xinetd
(2).增加user
说明:由于telnet服务是拒绝root用户登录的,所以我们增加一个free的用户,密码为123456
RS1:
[root@rs1 ~]# useradd free [root@rs1 ~]# passwd free 更改用户 free 的密码 。 新的 密码: 无效的密码: 过于简单化/系统化 无效的密码: 过于简单 重新输入新的 密码: passwd: 所有的身份验证令牌已经成功更新。
RS2:
[root@rs2 ~]# useradd free [root@rs2 ~]# passwd free 更改用户 free 的密码 。 新的 密码: 无效的密码: 过于简单化/系统化 无效的密码: 过于简单 重新输入新的 密码: passwd: 所有的身份验证令牌已经成功更新。
(3).增加集群服务
[root@master ~]# ipvsadm -A -t 172.16.100.1:80 -s rr -p 600 [root@master ~]# ipvsadm -a -t 172.16.100.1:80 -r 172.16.100.10 -g [root@master ~]# ipvsadm -a -t 172.16.100.1:80 -r 172.16.100.11 -g [root@master ~]# ipvsadm -A -t 172.16.100.1:23 -s rr -p 600 [root@master ~]# ipvsadm -a -t 172.16.100.1:23 -r 172.16.100.10 -g [root@master ~]# ipvsadm -a -t 172.16.100.1:23 -r 172.16.100.11 -g [root@master ~]# ipvsadm -A -t 172.16.100.1:22 -s rr -p 600 [root@master ~]# ipvsadm -a -t 172.16.100.1:22 -r 172.16.100.10 -g [root@master ~]# ipvsadm -a -t 172.16.100.1:22 -r 172.16.100.11 –g
(4).测试
[root@master ~]# ipvsadm -L -n IP Virtual Server version 1.2.1 (size=4096) Prot LocalAddress:Port Scheduler Flags -> RemoteAddress:Port Forward Weight ActiveConn InActConn TCP 172.16.100.1:22 rr persistent 600 -> 172.16.100.10:22 Route 1 2 0 -> 172.16.100.11:22 Route 1 4 0 TCP 172.16.100.1:23 rr persistent 600 -> 172.16.100.10:23 Route 1 3 0 -> 172.16.100.11:23 Route 1 6 0 TCP 172.16.100.1:80 rr persistent 600 -> 172.16.100.10:80 Route 1 0 0 -> 172.16.100.11:80 Route 1 0 39
总结,以上测试证明了,PPC模式的缺点,期望访问不同的端口到同一台Real Server上,无法实现。
七、PCC 演示
1.清空所有规则
root@master ~]# ipvsadm -C [root@master ~]# ipvsadm -L -n IP Virtual Server version 1.2.1 (size=4096) Prot LocalAddress:Port Scheduler Flags -> RemoteAddress:Port Forward Weight ActiveConn InActConn
2.配置PCC模式规则
[root@master ~]# ipvsadm -A -t 172.16.100.1:0 -s rr -p 600 [root@master ~]# ipvsadm -a -t 172.16.100.1:0 -r 172.16.100.10 -g [root@master ~]# ipvsadm -a -t 172.16.100.1:0 -r 172.16.100.11 -g
3.查看
[root@master ~]# ipvsadm -L -n IP Virtual Server version 1.2.1 (size=4096) Prot LocalAddress:Port Scheduler Flags -> RemoteAddress:Port Forward Weight ActiveConn InActConn TCP 172.16.100.1:0 rr persistent 600 -> 172.16.100.10:0 Route 1 0 0 -> 172.16.100.11:0 Route 1 0 0
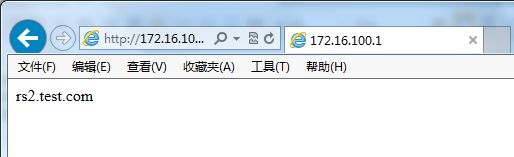
4.测试
[root@master ~]# ipvsadm -L -n IP Virtual Server version 1.2.1 (size=4096) Prot LocalAddress:Port Scheduler Flags -> RemoteAddress:Port Forward Weight ActiveConn InActConn TCP 172.16.100.1:0 rr persistent 600 -> 172.16.100.10:0 Route 1 0 0 -> 172.16.100.11:0 Route 1 3 1
总结:以上测试证明了,PCC的缺点,定向所有服务到同一台Real Server上,期望访问不同的Real Server上,无法实现。
八、PNMP 演示(常用)
说明:对于电子商务网站来说,用户在挑选商品的时候使用的是80端口来浏览的,当付款的时候则是通过443的ssl加密的方式,当然当用户挑选完商品付款的时候我们当然不希望https的443跳转到另外一台REALSERVER,很显然应该是同一REALSERVER才对,这时候就要用到基于防火墙标记的持久连接,通过定义端口的姻亲关系来实现。
1.配置CA证书颁发机构
(1).修改openssl配置文件
[root@ca ~]# vim /etc/pki/tls/openssl.cnf dir = /etc/pki/CA #工作目录 ,此处需要指定,不然给客户到签证的时候必须在特定的目录下才能实现 certs = $dir/certs #客户端证书目录 crl_dir = $dir/crl #证书吊销列表 database = $dir/index.txt #证书记录信息 new_certs_dir = $dir/newcerts #新生成证书的目录 certificate = $dir/cacert.pem #CA自己的证书位置 serial = $dir/serial #序列号 crlnumber = $dir/crlnumbe #证书吊销列表序列号 crl = $dir/crl.pem #证书吊销列表文件 private_key = $dir/private/cakey.pem #CA自己的私钥 RANDFILE = $dir/private/.rand #随机数文件 [ req_distinguished_name ] countryName = Country Name (2 letter code) countryName_default = CN #国家 countryName_min = 2 countryName_max = 2 stateOrProvinceName = State or Province Name (full name) stateOrProvinceName_default = shanghai #省份 localityName = Locality Name (eg, city) localityName_default = xujiahui #地区 0.organizationName = Organization Name (eg, company) 0.organizationName_default = jjhh #公司名称 organizationalUnitName = Organizational Unit Name (eg, section) organizationalUnitName_default =tech #所在部门 :wq #保存退出 [root@ca ~]# cd /etc/pki/CA/ [root@ca CA]# ll 总用量 16 drwxr-xr-x. 2 root root 4096 2月 22 07:45 certs drwxr-xr-x. 2 root root 4096 2月 22 07:45 crl drwxr-xr-x. 2 root root 4096 2月 22 07:45 newcerts drwx------. 2 root root 4096 2月 22 07:45 private
(2).生成密钥与证书
[root@ca CA]# (umask 077; openssl genrsa -out private/cakey.pem 2048) #生成密钥 Generating RSA private key, 2048 bit long modulus ..............................+++ ..................................................+++ e is 65537 (0x10001) [root@ca CA]# openssl req -new -x509 -key private/cakey.pem -out cacert.pem #生成自签证书 You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [CN]: State or Province Name (full name) [shanghai]: Locality Name (eg, city) [xujiahui]: Organization Name (eg, company) [jjhh]: Organizational Unit Name (eg, section) [tech]: Common Name (eg, your name or your server's hostname) []:rs.test.com Email Address []:admin.test.com [root@ca CA]# touch index.txt #新建索引文件 [root@ca CA]# touch serial #建立序列号文件 [root@ca CA]# echo 01 > serial #写入起始序列号
2.RS1与RS2申请证书
RS1:
(1).生成证书申请
[root@rs1 ~]# cd /etc/httpd #web服务器的配置目录 [root@rs1 ~]# mkdir ssl #创建ssl目录 [root@rs1 ~]# cd ssl #每一种服务要想使用证书,必须有私钥,每一种应用都需要自己的证书 [root@rs1 ssl]# (umask 077; openssl genrsa -out httpd.key 1024)#给自己生成密钥 -bash: (umask: command not found Generating RSA private key, 1024 bit long modulus ............++++++ ...................................................++++++ e is 65537 (0x10001) [root@rs1 ssl]# ll 总用量 4 -rw-r--r-- 1 root root 887 7月 29 00:36 httpd.key [root@rs1 ssl]# openssl req -new -key httpd.key -out httpd.csr #证书签署请求文件,机构和其他名字必须和CA颁发机构上的一样 You are about to be asked to enter information that will be incorporated into your certificate request. What you are about to enter is what is called a Distinguished Name or a DN. There are quite a few fields but you can leave some blank For some fields there will be a default value, If you enter '.', the field will be left blank. ----- Country Name (2 letter code) [XX]:CN State or Province Name (full name) []:shanghai Locality Name (eg, city) [Default City]:xujiahui Organization Name (eg, company) [Default Company Ltd]:jjhh Organizational Unit Name (eg, section) []:tech Common Name (eg, your name or your server's hostname) []:rs.test.com Email Address []:admin.test.com Please enter the following 'extra' attributes to be sent with your certificate request A challenge password []: An optional company name []:
(2).将证书申请发送到CA颁发机构上
[root@rs1 ssl]# scp ./httpd.csr [email protected]:/tmp
(3).CA颁发机构,签名并签发证书
[root@ca CA]# cd /tmp/
[root@ca tmp]# ls
httpd.csr
[root@ca tmp]# openssl ca -in httpd.csr -out httpd.crt -days 3650 #签发证书的有效期为10年
Using configuration from /etc/pki/tls/openssl.cnf
Check that the request matches the signature
Signature ok
Certificate Details:
Serial Number: 1 (0x1)
Validity
Not Before: Jul 28 15:53:01 2013 GMT
Not After : Jul 26 15:53:01 2023 GMT
Subject:
countryName = CN
stateOrProvinceName = shanghai
organizationName = jjhh
organizationalUnitName = tech
commonName = rs.test.com
emailAddress = admin.test.com
X509v3 extensions:
X509v3 Basic Constraints:
CA:FALSE
Netscape Comment:
OpenSSL Generated Certificate
X509v3 Subject Key Identifier:
68:9C:B1:46:ED:24:6A:2D:94:C6:89:21:0B:D0:CE:D5:C7:70:A6:75
X509v3 Authority Key Identifier:
keyid:E2:98:87:A6:76:F5:47:84:48:68:68:F9:DF:C1:0C:AD:4C:B9:30:61
Certificate is to be certified until Jul 26 15:53:01 2023 GMT (3650 days)
Sign the certificate? [y/n]:y
1 out of 1 certificate requests certified, commit? [y/n]y
Write out database with 1 new entries
Data Base Updated
[root@ca tmp]# ll
总用量 8
-rw-r--r-- 1 root root 3825 7月 28 23:53 httpd.crt
-rw-r--r-- 1 root root 692 7月 28 23:52 httpd.csr
(4).将生成的证书复制到Real Server 1上
[root@ca tmp]# scp ./httpd.crt [email protected]:/etc/httpd/ssl/httpd.crt
(5).查看收到的证书
[root@rs1 ssl]# ll 总用量 12 -rw-r--r-- 1 root root 3825 7月 29 00:47 httpd.crt -rw-r--r-- 1 root root 692 7月 29 00:37 httpd.csr -rw-r--r-- 1 root root 887 7月 29 00:36 httpd.key
RS2:(同RS1操作一致,我们就不重复演示了,这里使用一个简单的方法,直接复制RS1的证书)
[root@rs2 ~]# cd /etc/httpd #web服务器的配置目录 [root@rs2 ~]# mkdir ssl #创建ssl目录 [root@rs2 ssl]# scp [email protected]:/etc/httpd/ssl/* ./ [email protected]'s password: httpd.crt 100% 3825 3.7KB/s 00:00 httpd.csr 100% 692 0.7KB/s 00:00 httpd.key 100% 887 0.9KB/s 00:00 [root@rs2 ssl]# ll 总用量 12 -rw-r--r-- 1 root root 3825 7月 29 00:27 httpd.crt -rw-r--r-- 1 root root 692 7月 29 00:27 httpd.csr -rw-r--r-- 1 root root 887 7月 29 00:27 httpd.key
好了,现在RS1与RS2都有证书了,下面我们继续!
3.配置RS1与RS2支持SSL
RS1:
(1).安装httpd和ssl联系的装载模块mod_ssl
[root@rs1 ssl]# yum install -y mod_ssl
(2).修改ssl配置文件
[root@rs1 ssl]# vim /etc/httpd/conf.d/ssl.conf SSLCertificateFile /etc/httpd/ssl/httpd.crt #指定证书位置 SSLCertificateKeyFile /etc/httpd/ssl/httpd.key #指定key位置
(3).重启httpd
[root@rs1 ssl]# service httpd restart
(4).查看443端口
[root@rs1 ssl]# netstat -ntulp | grep :443 tcp 0 0 :::443 :::* LISTEN 1226/httpd
RS2:
(1).安装httpd和ssl联系的装载模块mod_ssl
[root@rs2 ssl]# yum install -y mod_ssl
(2).修改ssl配置文件
[root@rs2 ssl]# vim /etc/httpd/conf.d/ssl.conf SSLCertificateFile /etc/httpd/ssl/httpd.crt #指定证书位置 SSLCertificateKeyFile /etc/httpd/ssl/httpd.key #指定key位置
(3).重启httpd
[root@rs2 ssl]# service httpd restart
(4).查看443端口
[root@rs2 ssl]# netstat -ntulp | grep :443 tcp 0 0 :::443 :::* LISTEN 1226/httpd
简单测试一下:
大家可以看到测试成功,没有问题,下面我们继续!
4.清除所有LVS规则
[root@master ~]# ipvsadm -C [root@master ~]# ipvsadm -L -n IP Virtual Server version 1.2.1 (size=4096) Prot LocalAddress:Port Scheduler Flags -> RemoteAddress:Port Forward Weight ActiveConn InActConn
5.定义端口的姻亲关系,给80和443端口打上同样的防火墙标记
[root@master ~]# iptables -t mangle -A PREROUTING -d 172.16.100.1 -i eth0 -p tcp --dport 80 -j MARK --set-mark 8 [root@master ~]# iptables -t mangle -A PREROUTING -d 172.16.100.1 -i eth0 -p tcp --dport 443 -j MARK --set-mark 8
6.配置实现基于防火墙标记的LVS
[root@master ~]# ipvsadm -A -f 8 -s rr -p 600 [root@master ~]# ipvsadm -a -f 8 -r 172.16.100.10 -g [root@master ~]# ipvsadm -a -f 8 -r 172.16.100.11 -g [root@master ~]# ipvsadm -L -n IP Virtual Server version 1.2.1 (size=4096) Prot LocalAddress:Port Scheduler Flags -> RemoteAddress:Port Forward Weight ActiveConn InActConn FWM 8 rr persistent 600 -> 172.16.100.10:0 Route 1 0 0 -> 172.16.100.11:0 Route 1 0 0
7.测试
[root@master ~]# ipvsadm -L -n IP Virtual Server version 1.2.1 (size=4096) Prot LocalAddress:Port Scheduler Flags -> RemoteAddress:Port Forward Weight ActiveConn InActConn FWM 8 rr persistent 600 -> 172.16.100.10:0 Route 1 0 0 -> 172.16.100.11:0 Route 1 0 102
从上面我们可以看出由于持久连接,我们始终访问在Real Server 2上,下面我们测试一下https效果,
[root@master ~]# ipvsadm -L -n IP Virtual Server version 1.2.1 (size=4096) Prot LocalAddress:Port Scheduler Flags -> RemoteAddress:Port Forward Weight ActiveConn InActConn FWM 8 rr persistent 600 -> 172.16.100.10:0 Route 1 0 0 -> 172.16.100.11:0 Route 1 0 160
大家可以看到,我们访问https时,也始终访问Real Server 2上,嘿嘿……到此所有演示全部完成!^_^……