https://leetcode-cn.com/conte...
还以为是算法题,好不容易做了 2 道,赛后峰哥帮忙又做了第四题
第一题 100265. qqqqqqqqqqqqqqqy 的热身题
网上抄答案,稍微改了一下过了
qqqqqqqqqqqqqqqy-的热身题-返回代码本身的函数
第二题 100269. 狼人杀模拟器(没过)
有点麻烦,答案错误,不知道哪错了
第三题 100266. 小胖子的日常(没做出来)
第一个图片,用文本编辑器打开,可以看到最后有 base64 编码的一个串:
ZmxhZyU3QkBMZWV0Q29kZXIlMkMlMjBIYXBweSUyME5ldyUyMFllYXIlMjAlMjhPM08lMjklMjAlMjElN0Q=
解码
>>> import base64
>>> base64.b64decode('ZmxhZyU3QkBMZWV0Q29kZXIlMkMlMjBIYXBweSUyME5ldyUyMFllYXIlMjAlMjhPM08lMjklMjAlMjElN0Q=')
b'flag%7B@LeetCoder%2C%20Happy%20New%20Year%20%28O3O%29%20%21%7D'这个又是 urlencoding 的串
再解
>>> x=_
>>> x
b'flag%7B@LeetCoder%2C%20Happy%20New%20Year%20%28O3O%29%20%21%7D'
>>> import urllib.parse
>>> urllib.parse.unquote(x.decode())
'flag{@LeetCoder, Happy New Year (O3O) !}'然后就不会了
第四题 100263. SyM 的
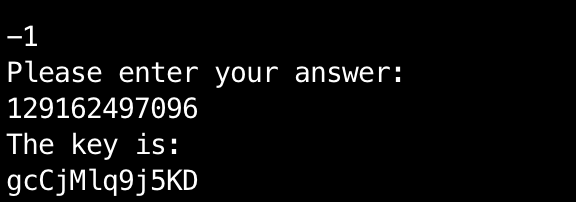
最终答案是:gcCjMlq9j5KD
objdump -h bomb 显示文件中的段
bomb: 文件格式 elf64-x86-64
节:
Idx Name Size VMA LMA File off Algn
0 .interp 0000001c 0000000000400238 0000000000400238 00000238 2**0
CONTENTS, ALLOC, LOAD, READONLY, DATA
1 .note.ABI-tag 00000020 0000000000400254 0000000000400254 00000254 2**2
CONTENTS, ALLOC, LOAD, READONLY, DATA
2 .note.gnu.build-id 00000024 0000000000400274 0000000000400274 00000274 2**2
CONTENTS, ALLOC, LOAD, READONLY, DATA
3 .gnu.hash 00000024 0000000000400298 0000000000400298 00000298 2**3
CONTENTS, ALLOC, LOAD, READONLY, DATA
4 .dynsym 00000168 00000000004002c0 00000000004002c0 000002c0 2**3
CONTENTS, ALLOC, LOAD, READONLY, DATA
5 .dynstr 00000098 0000000000400428 0000000000400428 00000428 2**0
CONTENTS, ALLOC, LOAD, READONLY, DATA
6 .gnu.version 0000001e 00000000004004c0 00000000004004c0 000004c0 2**1
CONTENTS, ALLOC, LOAD, READONLY, DATA
7 .gnu.version_r 00000030 00000000004004e0 00000000004004e0 000004e0 2**3
CONTENTS, ALLOC, LOAD, READONLY, DATA
8 .rela.dyn 00000030 0000000000400510 0000000000400510 00000510 2**3
CONTENTS, ALLOC, LOAD, READONLY, DATA
9 .rela.plt 00000120 0000000000400540 0000000000400540 00000540 2**3
CONTENTS, ALLOC, LOAD, READONLY, DATA
10 .init 0000001a 0000000000400660 0000000000400660 00000660 2**2
CONTENTS, ALLOC, LOAD, READONLY, CODE
11 .plt 000000d0 0000000000400680 0000000000400680 00000680 2**4
CONTENTS, ALLOC, LOAD, READONLY, CODE
12 .plt.got 00000008 0000000000400750 0000000000400750 00000750 2**3
CONTENTS, ALLOC, LOAD, READONLY, CODE
13 .text 000006d2 0000000000400760 0000000000400760 00000760 2**4
CONTENTS, ALLOC, LOAD, READONLY, CODE
14 .fini 00000009 0000000000400e34 0000000000400e34 00000e34 2**2
CONTENTS, ALLOC, LOAD, READONLY, CODE
15 .rodata 00000774 0000000000400e40 0000000000400e40 00000e40 2**5
CONTENTS, ALLOC, LOAD, READONLY, DATA
16 .eh_frame_hdr 00000064 00000000004015b4 00000000004015b4 000015b4 2**2
CONTENTS, ALLOC, LOAD, READONLY, DATA
17 .eh_frame 000001b4 0000000000401618 0000000000401618 00001618 2**3
CONTENTS, ALLOC, LOAD, READONLY, DATA
18 .init_array 00000008 0000000000601e10 0000000000601e10 00001e10 2**3
CONTENTS, ALLOC, LOAD, DATA
19 .fini_array 00000008 0000000000601e18 0000000000601e18 00001e18 2**3
CONTENTS, ALLOC, LOAD, DATA
20 .jcr 00000008 0000000000601e20 0000000000601e20 00001e20 2**3
CONTENTS, ALLOC, LOAD, DATA
21 .dynamic 000001d0 0000000000601e28 0000000000601e28 00001e28 2**3
CONTENTS, ALLOC, LOAD, DATA
22 .got 00000008 0000000000601ff8 0000000000601ff8 00001ff8 2**3
CONTENTS, ALLOC, LOAD, DATA
23 .got.plt 00000078 0000000000602000 0000000000602000 00002000 2**3
CONTENTS, ALLOC, LOAD, DATA
24 .data 00000010 0000000000602078 0000000000602078 00002078 2**3
CONTENTS, ALLOC, LOAD, DATA
25 .bss 0002a718 00000000006020a0 00000000006020a0 00002088 2**5
ALLOC
26 .comment 00000035 0000000000000000 0000000000000000 00002088 2**0
CONTENTS, READONLY
objdump -j .rodata -S bomb
bomb: 文件格式 elf64-x86-64
Disassembly of section .rodata:
0000000000400e40 <_IO_stdin_used>:
400e40: 01 00 02 00 00 00 00 00 00 00 00 00 00 00 00 00 ................
...
0000000000400e60 :
400e60: 41 42 43 44 45 46 47 48 49 4a 4b 4c 4d 4e 4f 50 ABCDEFGHIJKLMNOP
400e70: 51 52 53 54 55 56 57 58 59 5a 61 62 63 64 65 66 QRSTUVWXYZabcdef
400e80: 67 68 69 6a 6b 6c 6d 6e 6f 70 71 72 73 74 75 76 ghijklmnopqrstuv
400e90: 77 78 79 7a 30 31 32 33 34 35 36 37 38 39 00 00 wxyz0123456789..
400ea0: 57 65 6c 63 6f 6d 65 20 74 6f 20 53 79 4d 27 73 Welcome to SyM's
400eb0: 20 63 6f 64 65 20 73 61 66 65 21 0a 0a 49 6e 73 code safe!..Ins
400ec0: 74 72 75 63 74 69 6f 6e 73 3a 0a 20 20 20 20 59 tructions:. Y
400ed0: 6f 75 20 6e 65 65 64 20 74 6f 20 73 6f 6c 76 65 ou need to solve
400ee0: 20 74 68 69 73 20 62 69 6e 61 72 79 20 74 6f 20 this binary to
400ef0: 67 65 74 20 74 68 65 20 6b 65 79 2e 0a 20 20 20 get the key..
400f00: 20 54 68 65 20 66 69 6e 61 6c 20 6b 65 79 20 69 The final key i
400f10: 73 20 61 20 31 32 2d 77 6f 72 64 20 73 74 72 69 s a 12-word stri
400f20: 6e 67 2e 0a 20 20 20 20 4f 6e 63 65 20 79 6f 75 ng.. Once you
400f30: 27 76 65 20 67 6f 74 20 69 74 2c 20 6d 61 6b 65 've got it, make
400f40: 20 73 75 72 65 20 74 6f 20 73 75 62 6d 69 74 20 sure to submit
400f50: 69 74 20 73 6f 6d 65 77 68 65 72 65 2c 20 73 69 it somewhere, si
400f60: 6e 63 65 20 69 74 20 73 68 6f 75 6c 64 20 62 65 nce it should be
400f70: 20 71 75 69 74 65 20 76 61 6c 75 61 62 6c 65 21 quite valuable!
400f80: 0a 0a 54 68 65 72 65 20 61 72 65 20 74 77 6f 20 ..There are two
400f90: 70 68 61 73 65 73 2e 20 48 65 72 65 20 69 73 20 phases. Here is
400fa0: 74 68 65 20 66 69 72 73 74 20 6f 6e 65 20 66 6f the first one fo
400fb0: 72 20 77 61 72 6d 75 70 3a 0a 50 6c 65 61 73 65 r warmup:.Please
400fc0: 20 65 6e 74 65 72 20 61 20 70 61 73 73 77 6f 72 enter a passwor
400fd0: 64 20 74 6f 20 67 65 74 20 74 6f 20 74 68 65 20 d to get to the
400fe0: 6e 65 78 74 20 73 74 61 67 65 20 28 68 69 6e 74 next stage (hint
400ff0: 3a 20 74 68 65 20 6c 65 6e 67 74 68 20 6f 66 20 : the length of
401000: 70 61 73 73 77 6f 72 64 20 69 73 20 38 29 00 54 password is 8).T
401010: 68 69 73 20 69 73 20 6e 6f 74 20 67 6f 6e 6e 61 his is not gonna
401020: 20 77 6f 72 6b 21 00 31 65 65 74 43 30 64 65 00 work!.1eetC0de.
401030: 43 6f 6e 67 72 61 74 75 6c 61 74 69 6f 6e 73 21 Congratulations!
401040: 20 59 6f 75 27 76 65 20 70 61 73 73 65 64 20 74 You've passed t
401050: 68 65 20 66 69 72 73 74 20 73 74 61 67 65 2e 0a he first stage..
401060: 00 57 72 6f 6e 67 20 70 61 73 73 77 6f 72 64 21 .Wrong password!
发现里面有一个 1eetC0de 果然是密码
程序输出:
_ _______ _______ _________ _______ _______ ______ _______
( \ ( ____ \( ____ \\__ __/( ____ \( ___ )( __ \ ( ____ \
| ( | ( \/| ( \/ ) ( | ( \/| ( ) || ( \ )| ( \/
| | | (__ | (__ | | | | | | | || | ) || (__
| | | __) | __) | | | | | | | || | | || __)
| | | ( | ( | | | | | | | || | ) || (
| (____/\| (____/\| (____/\ | | | (____/\| (___) || (__/ )| (____/\
(_______/(_______/(_______/ )_( (_______/(_______)(______/ (_______/
Welcome to SyM's code safe!
Instructions:
You need to solve this binary to get the key.
The final key is a 12-word string.
Once you've got it, make sure to submit it somewhere, since it should be quite valuable!
There are two phases. Here is the first one for warmup:
Please enter a password to get to the next stage (hint: the length of password is 8)
1eetC0de
Congratulations! You've passed the first stage.
===== Generating Key =====
Key generation complete.
==========================
Here comes the second (and final) phase. It is a puzzle.
The puzzle input is 202020202020.
You need to find out the answer (a 64-bit integer as well) in order to get the key.
Surprisingly, I am kind enough to offer you some help.
You may enter any integer from 1 to 5, and I will calculate the answer to that input for you!
But for input like 202020202020, you need to do something special :)
If you've figured out the answer, simply enter -1 and then your answer to get the key!
Have fun decoding! (P.S. enter -2 to exit)
1
Try hard calculating...
Finished!!! The answer is:
01 - 5 的答案是
1 0
2 0
3 2
4 0
5 2
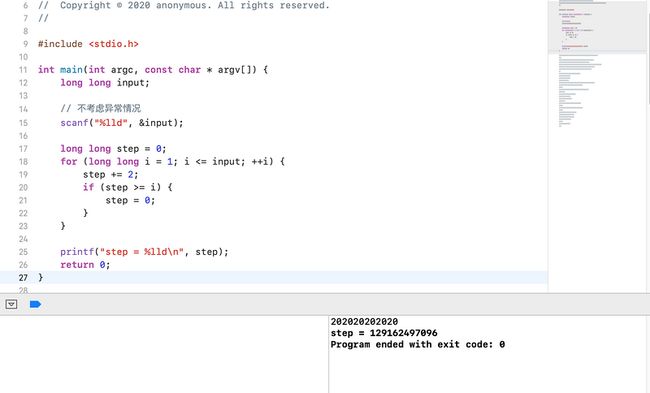
请峰哥帮我用 IDA 反汇编找到一个函数:
__int64 __fastcall puzzle(__int64 a1)
{
__int64 i; // [rsp+10h] [rbp-30h]
int v3; // [rsp+1Ch] [rbp-24h]
signed __int64 v4; // [rsp+20h] [rbp-20h]
__int64 v5; // [rsp+28h] [rbp-18h]
_DWORD *v6; // [rsp+30h] [rbp-10h]
v6 = malloc(4 * a1);
v5 = 0LL;
v4 = 0LL;
v3 = 0;
__memset_chk(v6, 0LL, 4 * a1, -1LL);
while ( v5 != a1 - 1 )
{
if ( !v6[v4] && ++v3 == 2 )
{
v6[v4] = 1;
++v5;
v3 = 0;
}
v4 = (v4 + 1) % a1;
}
for ( i = 0LL; ; ++i )
{
if ( i >= a1 )
exit(-1);
if ( !v6[i] )
break;
}
return i;
}改写该函数:
答案
gcCjMlq9j5KD
第五题 1000002. 找出隐藏信息
答案是 '明年再战狼人杀!'
第八题 100272. 年快乐(没做)
答案是 Happy Chinese New YeaR!
别人写的解决方法