DVWA之暴力破解攻击方法,审计,解决办法
一、攻击方法:
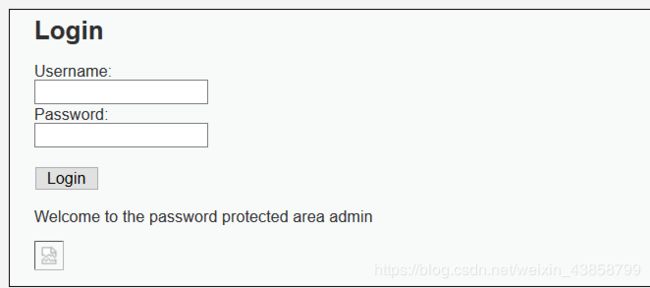
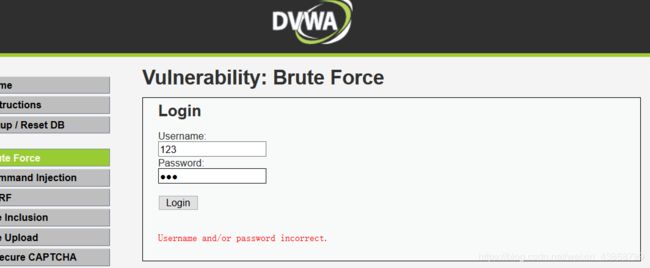
1.先随意输入账号和密码
2.用Burnsuite抓包并传到intruder中

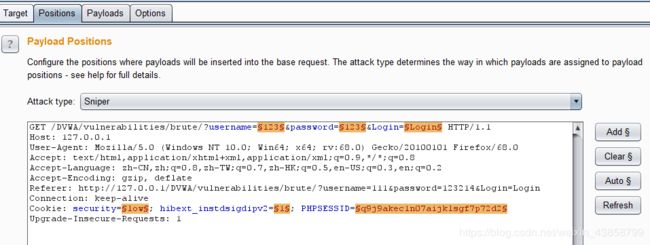
3.清除变量 并将username和password添加为新变量
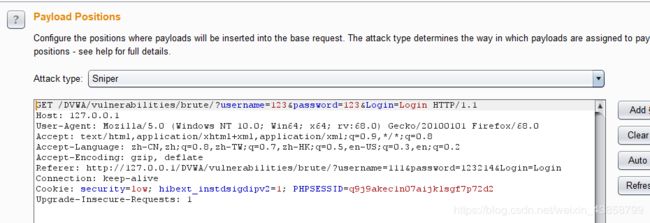

4.选择Cluster bomb方式 在payloads中导入字典
payload 1 2都导入相同的即可

点击start attack 开始暴力破解
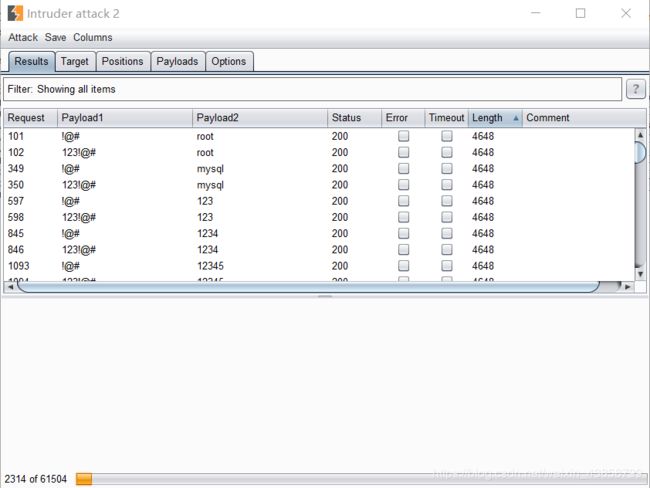
5.结束后 筛选length

拿到账号:admin
密码:password
二、代码审计:
' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . 'Welcome to the password protected area {$user}
"; echo ""; } ((is_null($___mysqli_res = mysqli_close($GLOBALS["___mysqli_ston"]))) ? false : $___mysqli_res); } ?>
Username and/or password incorrect.
通过这俩段代码审计得知
$query = "SELECT * FROM `users` WHERE user = '$user' AND password = '$pass';"; //将从数据库中查找对应的user和password的方法赋值给query变量
$result = mysqli_query($GLOBALS["___mysqli_ston"], $query ) or die( '' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . '
' );
//mysqli_query() 函数执行某个针对数据库的查询 //GLOBALS返回变量的字典 //die:输出一条消息,并退出当前脚本。 is_object:用于检测变量是否是一个对象。 类似于三目运算符
if( $result && mysqli_num_rows( $result ) == 1 ) {
// Get users details
$row = mysqli_fetch_assoc( $result );
$avatar = $row["avatar"];
PHP只接受了用户输入的账号密码 并通过匹配数据库中的账号密码 判断是否正确
if语句中也只做了简单判断 没有防止暴力破解
三、解决方法:
防止暴力破解的方法:
1、限制输入次数 例如:输入错误3次锁定输入5分钟
2、验证码 例如:图片 文字验证码
这里采用第一种解决方法:
在这里插入代码片' . ((is_object($GLOBALS["___mysqli_ston"])) ? mysqli_error($GLOBALS["___mysqli_ston"]) : (($___mysqli_res = mysqli_connect_error()) ? $___mysqli_res : false)) . 'Welcome to the password protected area {$user}
"; echo "Warning: Someone might of been brute forcing your account.
"; echo "Number of login attempts: {$failed_login}.
Last login attempt was at: ${last_login}.
"; // 更新登陆错误次数 $data = $db->prepare( 'UPDATE users SET failed_login = (failed_login + 1) WHERE user = (:user) LIMIT 1;' ); $data->bindParam( ':user', $user, PDO::PARAM_STR ); $data->execute(); } // 设置上次登录时间 $data = $db->prepare( 'UPDATE users SET last_login = now() WHERE user = (:user) LIMIT 1;' ); $data->bindParam( ':user', $user, PDO::PARAM_STR ); $data->execute(); } ?>
Username and/or password incorrect.
Alternative, the account has been locked because of too many failed logins.
If this is the case, please try again in {$lockout_time} minutes.
检查是否锁定 以及 如何锁定的关键代码:
// 默认值
$total_failed_login = 3;//尝试次数
$lockout_time = 15;//锁定时间
$account_locked = false;//默认不锁定
// 检查数据库(检查用户信息)
$data = $db->prepare( 'SELECT failed_login, last_login FROM users WHERE user = (:user) LIMIT 1;' ); //prepare:准备一个用于迭代执行的查询
$data->bindParam( ':user', $user, PDO::PARAM_STR ); //通过告诉数据库参数的数据类型,可以降低 SQL 注入的风险。
$data->execute();
$row = $data->fetch();
// 检查用户是否已被锁定。
if( ( $data->rowCount() == 1 ) && ( $row[ 'failed_login' ] >= $total_failed_login ) ) {
// 用户被锁定。
// 计算何时允许用户再次登录
$last_login = strtotime( $row[ 'last_login' ] );
$timeout = $last_login + ($lockout_time * 60);
$timenow = time();
// 如果尚未锁定帐户,请检查是否已经过了足够的时间
if( $timenow < $timeout ) {
$account_locked = true;
}
}
// 检查数据库(如果用户名与密码匹配)
$data = $db->prepare( 'SELECT * FROM users WHERE user = (:user) AND password = (:password) LIMIT 1;' );
$data->bindParam( ':user', $user, PDO::PARAM_STR);
$data->bindParam( ':password', $pass, PDO::PARAM_STR );
$data->execute();
$row = $data->fetch();
// 如果是有效登录...
if( ( $data->rowCount() == 1 ) && ( $account_locked == false ) ) {
// 获取用户详细信息
$avatar = $row[ 'avatar' ];
$failed_login = $row[ 'failed_login' ];
$last_login = $row[ 'last_login' ];
// 登陆成功
echo "Welcome to the password protected area {$user}
";
echo " ";
// 该帐户自上次登录后是否被锁定?
if( $failed_login >= $total_failed_login ) {
echo "
";
// 该帐户自上次登录后是否被锁定?
if( $failed_login >= $total_failed_login ) {
echo "Warning: Someone might of been brute forcing your account.
";
echo "Number of login attempts: {$failed_login}.
Last login attempt was at: ${last_login}.
";
}
// 重置错误登陆次数
$data = $db->prepare( 'UPDATE users SET failed_login = "0" WHERE user = (:user) LIMIT 1;' );
$data->bindParam( ':user', $user, PDO::PARAM_STR );
$data->execute();
} else {
// 登陆失败
sleep( rand( 2, 4 ) );
// 给用户一些反馈
echo "
Username and/or password incorrect.
Alternative, the account has been locked because of too many failed logins.
If this is the case, please try again in {$lockout_time} minutes.
";
// 更新登陆错误次数
$data = $db->prepare( 'UPDATE users SET failed_login = (failed_login + 1) WHERE user = (:user) LIMIT 1;' );
$data->bindParam( ':user', $user, PDO::PARAM_STR );
$data->execute();
}
// 设置上次登录时间
$data = $db->prepare( 'UPDATE users SET last_login = now() WHERE user = (:user) LIMIT 1;' );
$data->bindParam( ':user', $user, PDO::PARAM_STR );
$data->execute();
}