使用Libtomcrypt RSA/ECC等加密算法到项目中
LibTomCrypt是一个非常不错的加解密开源库,支持C/C++编译,可以支持跨平台.更详细的信息请参考其官网:http://www.libtom.net/
一、材料准备
1、libtomcrypt
2、libtommath
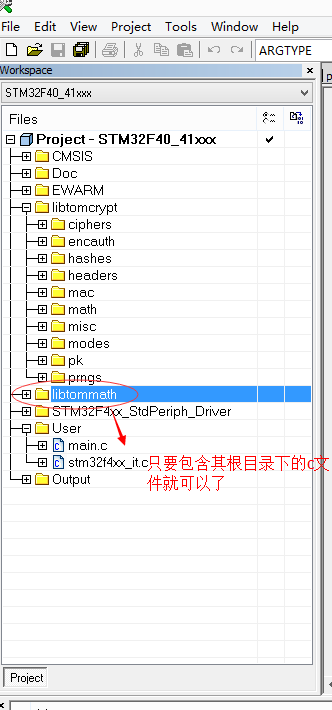
二、将项目增加到自己的项目工程中
以IAR为例子,直接上图片.
另外include路径按照自己项目存放的文件夹路径进行放置,以下是我自己的目录引用情况
$PROJ_DIR$\..\libtomcrypt\src\headers
$PROJ_DIR$\..\libtommath
三、修改代码
由于该文件用的是跨平台的,所以部分算法可能需要进行修改.例如,随机数产生.如果自己的芯片支持,则可以考虑使用芯片的随机数发生器进行产生随机数。
四、增加宏控制
在 tomcrypt_custom.h文件夹配置相关宏,用于控制其编译
如,在IAR中增加宏控制
LTC_EASY
_CRT_SECURE_NO_WARNINGS
LTC_SOURCE
LTM_DESC
五、开始使用库函数
在main.C中引用tomcrypt.h头文件
#include
六、修改tomcrypt_pk.h文件,使用 LTC_LTC_PKCS_1_V1_5 进行加解密 相关部分为
/* These use LTC_PKCS #1 v2.0 padding */
#define rsa_encrypt_key(_in, _inlen, _out, _outlen, _lparam, _lparamlen, _prng, _prng_idx, _hash_idx, _key) \
rsa_encrypt_key_ex(_in, _inlen, _out, _outlen, _lparam, _lparamlen, _prng, _prng_idx, _hash_idx, LTC_LTC_PKCS_1_V1_5, _key)
#define rsa_decrypt_key(_in, _inlen, _out, _outlen, _lparam, _lparamlen, _hash_idx, _stat, _key) \
rsa_decrypt_key_ex(_in, _inlen, _out, _outlen, _lparam, _lparamlen, _hash_idx, LTC_LTC_PKCS_1_V1_5, _stat, _key)
七、修改LTC_LTC_PKCS_1_V1_5后,需要修改pkcs_1_v1_5_encode.c文件的pkcs_1_v1_5_encode函数,使其随机数产生器使用MCU硬件产生.
如,我修改后的代码
/* LibTomCrypt, modular cryptographic library -- Tom St Denis
*
* LibTomCrypt is a library that provides various cryptographic
* algorithms in a highly modular and flexible manner.
*
* The library is free for all purposes without any express
* guarantee it works.
*
* Tom St Denis, [email protected], http://libtom.org
*/
#include "tomcrypt.h"
#include "security.h"
/*! \file pkcs_1_v1_5_encode.c
*
* LTC_PKCS #1 v1.5 Padding (Andreas Lange)
*/
#ifdef LTC_PKCS_1
/*! \brief LTC_PKCS #1 v1.5 encode.
*
* \param msg The data to encode
* \param msglen The length of the data to encode (octets)
* \param block_type Block type to use in padding (\sa ltc_pkcs_1_v1_5_blocks)
* \param modulus_bitlen The bit length of the RSA modulus
* \param prng An active PRNG state (only for LTC_LTC_PKCS_1_EME)
* \param prng_idx The index of the PRNG desired (only for LTC_LTC_PKCS_1_EME)
* \param out [out] The destination for the encoded data
* \param outlen [in/out] The max size and resulting size of the encoded data
*
* \return CRYPT_OK if successful
*/
int pkcs_1_v1_5_encode(const unsigned char *msg,
unsigned long msglen,
int block_type,
unsigned long modulus_bitlen,
prng_state *prng,
int prng_idx,
unsigned char *out,
unsigned long *outlen)
{
unsigned long modulus_len, ps_len, i;
unsigned char *ps;
int result;
/* valid block_type? */
if ((block_type != LTC_LTC_PKCS_1_EMSA) &&
(block_type != LTC_LTC_PKCS_1_EME)) {
return CRYPT_PK_INVALID_PADDING;
}
if (block_type == LTC_LTC_PKCS_1_EME) { /* encryption padding, we need a valid PRNG */
if ((result = prng_is_valid(prng_idx)) != CRYPT_OK) {
return result;
}
}
modulus_len = (modulus_bitlen >> 3) + (modulus_bitlen & 7 ? 1 : 0);
/* test message size */
if ((msglen + 11) > modulus_len) {
return CRYPT_PK_INVALID_SIZE;
}
if (*outlen < modulus_len) {
*outlen = modulus_len;
result = CRYPT_BUFFER_OVERFLOW;
goto bail;
}
/* generate an octets string PS */
ps = &out[2];
ps_len = modulus_len - msglen - 3;
if (block_type == LTC_LTC_PKCS_1_EME) {
#if 0
/* now choose a random ps */
if (prng_descriptor[prng_idx].read(ps, ps_len, prng) != ps_len) {
result = CRYPT_ERROR_READPRNG;
goto bail;
}
/* transform zero bytes (if any) to non-zero random bytes */
for (i = 0; i < ps_len; i++) {
while (ps[i] == 0) {
if (prng_descriptor[prng_idx].read(&ps[i], 1, prng) != 1) {
result = CRYPT_ERROR_READPRNG;
goto bail;
}
}
}
#else
for(i = 0;i < ps_len;)
{
Security_GenerateRandData(ps + i,1);
if(ps[i] != 0)
i++;
}
#endif
} else {
XMEMSET(ps, 0xFF, ps_len);
}
/* create string of length modulus_len */
out[0] = 0x00;
out[1] = (unsigned char)block_type; /* block_type 1 or 2 */
out[2 + ps_len] = 0x00;
XMEMCPY(&out[2 + ps_len + 1], msg, msglen);
*outlen = modulus_len;
result = CRYPT_OK;
bail:
return result;
} /* pkcs_1_v1_5_encode */
#endif /* #ifdef LTC_PKCS_1 */
/* $Source: /cvs/libtom/libtomcrypt/src/pk/pkcs1/pkcs_1_v1_5_encode.c,v $ */
/* $Revision: 1.4 $ */
/* $Date: 2007/05/12 14:32:35 $ */
![]()