Jarvis OJ - DD-Hello -Writeup
转载请注明出处http://www.cnblogs.com/WangAoBo/p/7239216.html
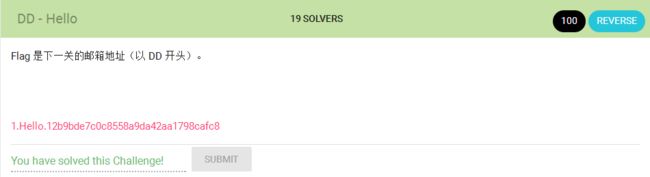
题目:
分析:
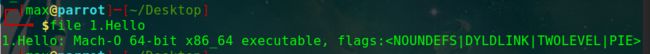
第一次做这道题时,file查看发现是OS X和IOS的可执行文件,就果断放弃了
后来又一想,OS X是基于FreeBSD的,那Mach-O文件和elf应该也有相通之处,于是就尝试用IDA打开文件,居然真的打开了
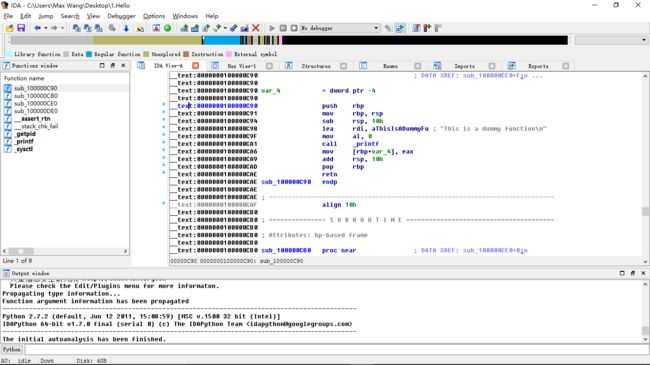
函数较少,并且都可F5出伪代码,逐个分析,整理如下:
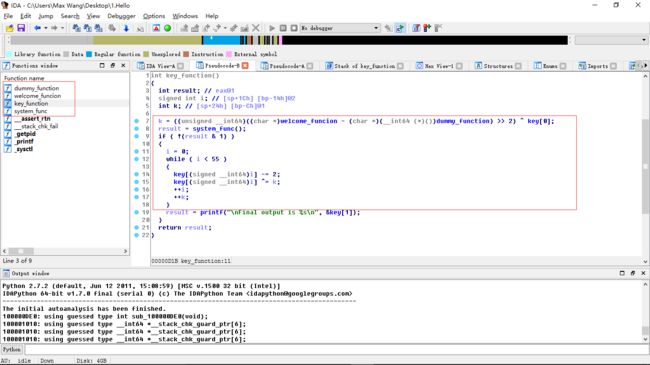
关键代码:
if ( !(result & 1) ) { i = 0; while ( i < 55 ) { key[(signed __int64)i] -= 2; key[(signed __int64)i] ^= k; ++i; ++k; }
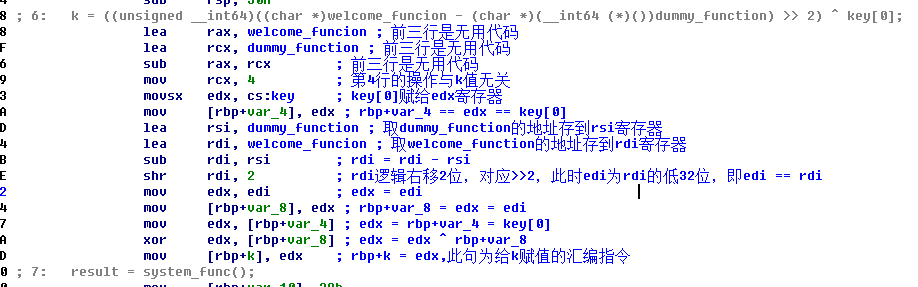
key[]是已知的,i是循环变量,因此只需要找到k的值,从伪代码看不出什么
![]()
但k肯定是固定的,因此首先尝试爆破,脚本如下:
for kk in range(0, 256): key = [0x41, 0x10, 0x11, 0x11, 0x1B, 0x0A, 0x64, 0x67, 0x6A, 0x68, 0x62, 0x68, 0x6E, 0x67, 0x68, 0x6B, 0x62, 0x3D, 0x65, 0x6A, 0x6A, 0x3D, 0x68, 0x4, 0x5, 0x8, 0x3, 0x2, 0x2, 0x55, 0x8, 0x5D, 0x61, 0x55, 0x0A, 0x5F, 0x0D, 0x5D, 0x61, 0x32, 0x17, 0x1D, 0x19, 0x1F, 0x18, 0x20, 0x4, 0x2, 0x12, 0x16, 0x1E, 0x54, 0x20, 0x13, 0x14, 0x0, 0x0] try: k = kk i = 0 while i < 55: key[i] -= 2 key[i] ^= k i += 1 k += 1 ans = '' for c in key: ans += chr(c) print ans except: pass
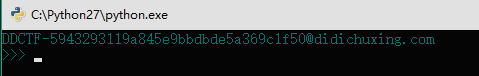
运行并提取flag如下:
后来请教了学长,从汇编代码里找出了k的值,就不用爆破了
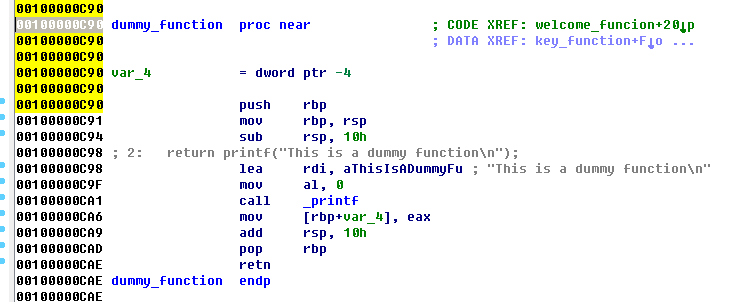
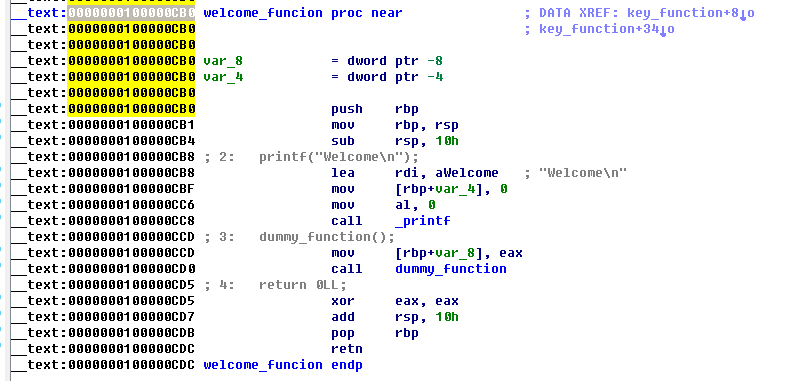
于是k即为dummy_function与welcome_function的地址差值右移两位在与key[0]亦或,从IDA中可以看出dummy_function和welcome_function的地址
得到新的非爆破脚本如下:
key = [0x41, 0x10, 0x11, 0x11, 0x1B, 0x0A, 0x64, 0x67, 0x6A, 0x68, 0x62, 0x68, 0x6E, 0x67, 0x68, 0x6B, 0x62, 0x3D, 0x65, 0x6A, 0x6A, 0x3D, 0x68, 0x4, 0x5, 0x8, 0x3, 0x2, 0x2, 0x55, 0x8, 0x5D, 0x61, 0x55, 0x0A, 0x5F, 0x0D, 0x5D, 0x61, 0x32, 0x17, 0x1D, 0x19, 0x1F, 0x18, 0x20, 0x4, 0x2, 0x12, 0x16, 0x1E, 0x54, 0x20, 0x13, 0x14, 0x0, 0x0] k = ((0x0000000100000CB0 - 0x0000000100000C90) >> 2) ^ key[0] i = 0 while i < 55: key[i] -= 2 key[i] ^= k i += 1 k += 1 ans = '' for c in key: ans += chr(c) print ans[1: ]
运行
于是flag即为[email protected]