Centos 安装 L2tp
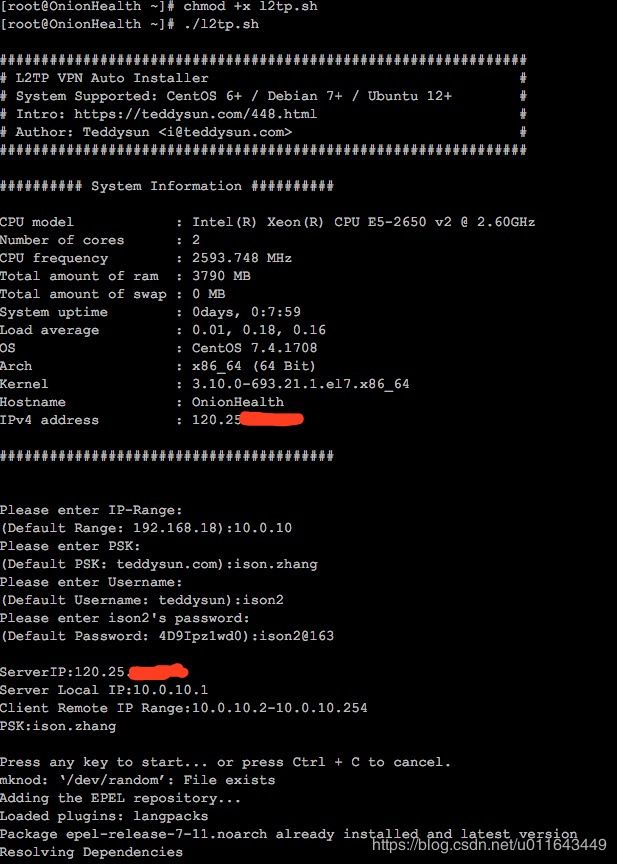
wget --no-check-certificate https://raw.githubusercontent.com/teddysun/across/master/.sh
chmod +x .sh
./.sh
如果你要想对用户进行操作,可以使用如下命令:
-a 新增用户
-d 删除用户
-m 修改现有的用户的密码
-l 列出所有用户名和密码
-h 列出帮助信息
其他事项:
1、脚本在安装完成后,已自动启动进程,并加入了开机自启动。
2、脚本会改写 iptables 或 firewalld 的规则。
3、脚本安装时,会即时将安装日志写到 /root/.log 文件里,如果你安装失败,可以通过此文件来寻找错误信息。
使用命令:
ipsec status (查看 IPSec 运行状态)
ipsec verify (查看 IPSec 检查结果)
/etc/init.d/ipsec start|stop|restart|status (CentOS6 下使用)
/etc/init.d/xd start|stop|restart (CentOS6 下使用)
systemctl start|stop|restart|status ipsec (CentOS7 下使用)
systemctl start|stop|restart xd (CentOS7 下使用)
service ipsec start|stop|restart|status (Debian/Ubuntu 下使用)
service xd start|stop|restart (Debian/Ubuntu 下使用)
1.安装 ipsec 所需要的软件包
yum install epel-release
yum install openswan xd ppp lsof
2.设置ipsec
2.1 编辑 /etc/ipsec.conf
vi /etc/ipsec.conf
把下面xx.xxx.xxx.xxx换成你自己主机实际的外网固定IP。其他的不动。
config setup
protostack=netkey
dumpdir=/var/run/pluto/
nat_traversal=yes
virtual_private=%v4:10.0.0.0/8,%v4:192.168.0.0/16,%v4:172.16.0.0/12,%v4:25.0.0.0/8,%v4:100.64.0.0/10,%v6:fd00::/8,%v6:fe80::/10
conn L2TP-PSK-NAT
rightsubnet=vhost:%priv
also=L2TP-PSK-noNAT
conn L2TP-PSK-noNAT
authby=secret
pfs=no
auto=add
keyingtries=3
dpddelay=30
dpdtimeout=120
dpdaction=clear
rekey=no
ikelifetime=8h
keylife=1h
type=transport
left=xxx.xxx.xxx.xxx
leftprotoport=17/1701
right=%any
rightprotoport=17/%any
2.2 编辑/etc/ipsec.secrets
vi /etc/ipsec.secrets
include /etc/ipsec.d/default.secrets
/etc/ipsec.secrets 文件里面默认有一句包含
/etc/ipsec.d/*.secrets
的语句.所以可以直接在 /etc/ipsec.d 目录下新建一自己的个 default.secrets 文件.也可以直接把它注释掉,添加下面的配置语句.
vi /etc/ipsec.d/my.secrets
xxx.xxx.xxx.xxx %any: PSK "kuaile"
xx.xxx.xxx.xxx换成你自己VPS实际的外网固定IP, YourPsk你自己定一个,到时候连VPN的时候用,比如可以填csdn.net, 注意空格。
2.3 修改/添加 /etc/sysctl.conf
vi /etc/sysctl.conf
确保下面的字段都有,对应的值或下面一样。省事的话直接在/etc/sysctl.conf的末尾直接把下面内容的粘过去。
net.ipv4.ip_forward = 1
net.ipv4.conf.default.accept_redirects = 0
net.ipv4.conf.default.send_redirects = 0
net.ipv4.conf.eth0.rp_filter = 0
net.ipv4.conf.default.rp_filter = 0
2.4 让修改后的sysctl.conf生效
sysctl -p
2.5 验证ipsec运行状态
ipsec setup start
ipsec verify
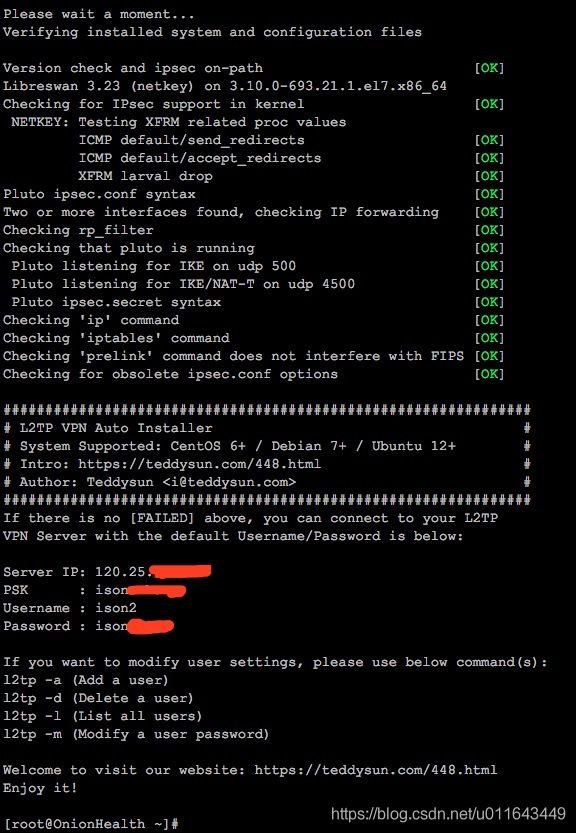
verify的内容如下所示,那么就离成功不远了。没有 红色 的fail 就可以了.
Verifying installed system and configuration files
Version check and ipsec on-path [OK]
Libreswan 3.15 (netkey) on 3.10.0-123.9.3.el7.x86_64
Checking for IPsec support in kernel [OK]
NETKEY: Testing XFRM related proc values
ICMP default/send_redirects [OK]
ICMP default/accept_redirects [OK]
XFRM larval drop [OK]
Pluto ipsec.conf syntax [OK]
Hardware random device [N/A]
Two or more interfaces found, checking IP forwarding [OK]
Checking rp_filter [OK]
Checking that pluto is running [OK]
Pluto listening for IKE on udp 500 [OK]
Pluto listening for IKE/NAT-T on udp 4500 [OK]
Pluto ipsec.secret syntax [OK]
Checking 'ip' command [OK]
Checking 'iptables' command [OK]
Checking 'prelink' command does not interfere with FIPSChecking for obsolete ipsec.conf options [OK]
Opportunistic Encryption [DISABLED]
3. 设置
3.1 编辑 /etc/xd/xd.conf
vim /etc/xd/xd.conf
[global]
ipsec saref = yes
listen-addr = xxx.xxx.xxx.xxx ;这里是你的主机外网ip地址,;号是注释,和一般的配置文件不同
; Use refinfo of 22 if using an SAref kernel patch based on openswan 2.6.35 or
; when using any of the SAref kernel patches for kernels up to 2.6.35.
; saref refinfo = 30
;
force userspace = yes
;
; debug tunnel = yes
[lns default]
ip range = 10.0.10.2-10.0.10.100 ;这里是VPN client的内网ip地址范围
local ip = 10.0.10.1 ;这里是VPN server的内网地址
refuse chap = yes
refuse pap = yes
require authentication = yes
name = LinuxVPNserver
ppp debug = yes
pppoptfile = /etc/ppp/options.xd
length bit = yes
3.2 编辑 /etc/ppp/options.xd
vi /etc/ppp/options.xd
name d
require-mschap-v2
ms-dns 180.76.76.76
ms-dns 223.5.5.5
ms-dns 8.8.8.8
ipcp-accept-local
ipcp-accept-remote
#ms-dns 8.8.8.8
noccp
auth
crtscts
idle 1800
mtu 1410
mru 1410
nodefaultroute
debug
lock
proxyarp
connect-delay 5000
3.3 配置用户名,密码:编辑 /etc/ppp/chap-secrets
vim /etc/ppp/chap-secrets
client和secret自己填,server和IP留号, 可以用上面自己设定的 d . 通用
# Secrets for authentication using CHAP
# client server secret IP addresses
ison * 123456 *
3.4 启动x
service xd start
4. 开放端口以及转发
原样执行下面所有命令
/sbin/iptables -A INPUT -p udp -m policy --dir in --pol ipsec -m udp --dport 1701 -j ACCEPT
/sbin/iptables -A INPUT -p udp -m udp --dport 1701 -j ACCEPT
/sbin/iptables -A INPUT -p udp -m udp --dport 500 -j ACCEPT
/sbin/iptables -A INPUT -p udp -m udp --dport 4500 -j ACCEPT
/sbin/iptables -A INPUT -p esp -j ACCEPT
/sbin/iptables -A INPUT -m policy --dir in --pol ipsec -j ACCEPT
/sbin/iptables -A FORWARD -d 10.0.10.0/24 -j ACCEPT
/sbin/iptables -A FORWARD -s 10.0.10.0/24 -j ACCEPT
/sbin/iptables -A FORWARD -i ppp+ -m state --state NEW,RELATED,ESTABLISHED -j ACCEPT
/sbin/iptables -A FORWARD -m state --state RELATED,ESTABLISHED -j ACCEPT
/sbin/iptables -t nat -A POSTROUTING -s 10.0.10.0/24 -o eth0 -j MASQUERADE
再执行下面保存iptables
service iptables save
service iptables restart
添加开机自启动
systemd enabled ipsec
systemd enabled xd
如果连接不上的话, 先关掉iptalbes试试 service iptables stop
如果这时还连不上了,那么就是iptables的问题了
特别注意iptables里的顺序, INPUT和FORWARD里的REJECT一定是写在最后面,否则写在他们之后的port就都被REJECT了!
下面是我自己的iptables,可供参考
#############
*nat
:PREROUTING ACCEPT [3:160]
:INPUT ACCEPT [3:160]
:OUTPUT ACCEPT [3:180]
:POSTROUTING ACCEPT [3:180]
-A POSTROUTING -s 10.0.10.0/24 -o eth0 -j MASQUERADE
COMMIT
# Completed on Sat Mar 18 22:21:34 2017
# Generated by iptables-save v1.4.21 on Sat Mar 18 22:21:34 2017
*filter
:INPUT ACCEPT [237:33515]
:FORWARD ACCEPT [0:0]
:OUTPUT ACCEPT [162:45870]
-A INPUT -m state --state ESTABLISHED,RELATED -j ACCEPT
-A INPUT -p icmp -j ACCEPT
-A INPUT -i lo -j ACCEPT
-A INPUT -m state --state NEW -m tcp -p tcp --dport 80 -j ACCEPT
-A INPUT -m state --state NEW -m tcp -p tcp --dport 443 -j ACCEPT
-A INPUT -m state --state NEW -m tcp -p tcp --dport 22 -j ACCEPT
-A INPUT -p udp -m policy --dir in --pol ipsec -m udp --dport 1701 -j ACCEPT
-A INPUT -p udp -m udp --dport 1701 -j ACCEPT
-A INPUT -p udp -m udp --dport 500 -j ACCEPT
-A INPUT -p udp -m udp --dport 4500 -j ACCEPT
-A INPUT -p esp -j ACCEPT
-A INPUT -m policy --dir in --pol ipsec -j ACCEPT
-A FORWARD -d 10.0.10.0/24 -j ACCEPT
-A FORWARD -s 10.0.10.0/24 -j ACCEPT
-A FORWARD -i ppp+ -m state --state NEW,RELATED,ESTABLISHED -j ACCEPT
-A FORWARD -m state --state RELATED,ESTABLISHED -j ACCEPT
-A INPUT -j REJECT --reject-with icmp-host-prohibited
-A FORWARD -j REJECT --reject-with icmp-host-prohibited
COMMIT
# Completed on Sat Mar 18 22:21:34 2017