- [BJDCTF2020]JustRE
32304353
安全汇编
打开程序发现需要进行点击获取flag拖入IDA进行分析F5挨个查看代码发现疑似falg的数据经过判断,需要点击19999次获得flag把%d带入即可获取flagflag{1999902069a45792d233ac}提交flag解题思路参考文章BUUCTF-[BJDCTF2020]JustRE1-CSDN博客
- buuctf-变异凯撒
qis_qis
crypto其他
凯撒密码作为最古老的密码体制之一,相信大多数人都知道,即简单的移位操作,那么问题来了,变异的凯撒密码又会是什么呢?拿到题先比对acsii码值对比表:acsii码通过上面的acsii码值对比表可以看到第一个字符向后移了5,第二个向后移了6,第三个向后移了7,以此类推,很容易想到变异凯撒即每个向后移的位数是前一个加1:str="afZ_r9VYfScOeO_UL^RWUc"k=5foriinstr:p
- buuctf-Quoted-printable
qis_qis
crypto
解压打开:=E9=82=A3=E4=BD=A0=E4=B9=9F=E5=BE=88=E6=A3=92=E5=93=A6刚开始看到这一个字符串,误以为是什么编码特有的格式直到后面发现标题即提示,即Quoted-printable也是一种编码:得到flag:那你也很棒哦
- 138,【5】buuctf web [RootersCTF2019]I_<3_Flask
rzydal
flaskpython后端
进入靶场这段代码是利用Python的类继承和反射机制来尝试执行系统命令读取flag.txt文件内容''.__class__:空字符串对象调用__class__属性,得到str类,即字符串的类型。__class__.__base__:str类的__base__属性指向其基类,在Python中str是新式类,其基类是object。__base__.__subclasses__():object类的__
- 141,【1】buuctf web [SUCTF 2019]EasyWeb
rzydal
web安全
进入靶场代码审计18){die('Oneinchlong,oneinchstrong!');}//使用正则表达式检查$hhh是否包含特定字符集(包括一些常见字符和控制字符等),如果包含则终止脚本执行if(preg_match('/[\x00-0-9A-Za-z\'"\`~_&.,|=[\x7F]+/i',$hhh))die('Trysomethingelse!');//获取$hhh中使用到的字符,
- BUUCTF 逆向工程(reverse)之Java逆向解密
若丶时光破灭
CTF-逆向工程CTF逆向工程
程序员小张不小心弄丢了加密文件用的秘钥,已知还好小张曾经编写了一个秘钥验证算法,聪明的你能帮小张找到秘钥吗?注意:得到的flag请包上flag{}提交下载好题目后,发现它是个以.class为后缀的。所以用JD-GUI打开这个文件。就可以看到Java代码importjava.util.ArrayList;importjava.util.Scanner;publicclassReverse{publi
- BUUCTF——[极客大挑战 2019]PHP
south_1
webphpphp
打开题目,页面上显示说习惯备份,尝试下载备份www.zip,下载后打开查看flag文件里并不是flag,查看其他的在class文件中发现代码,应该是让我们反序列化,给出源代码username=$username;$this->password=$password;}function__wakeup(){$this->username='guest';}function__destruct(){if
- BUUCTF Crypto题目记录
Vigorousy
密码学
MD5e00cf25ad42683b3df678c61f42c6bda进行MD5加密flag{admin1}Url编码%66%6c%61%67%7b%61%6e%64%20%31%3d%31%7dflag{and1=1}看我回旋踢synt{5pq1004q-86n5-46q8-o720-oro5on0417r1}观察已知字符串已经存在flag雏形,猜测为凯撒密码flag{5cd1004d-86a5
- BUUCTF系列 // [极客大挑战 2019] Http
Ga1axy_z
CTF
前言本题知识点:常用HTTP请求头WP打开题目,在页面中没有发现明显的提示,查看网页源码,经搜索后发现一个似乎存在猫腻的网页‘Secret.php’访问该页面,得到第一个提示题目要求我们从‘https://www.Sycsecret.com’进入该页面,故使用burpsuite抓包,在请求头中增加Referer字段即可RefererHTTPReferer是header的一部分,当浏览器向Web服务
- buuctf [极客大挑战 2019]FinalSQL
cng_Capricornus
buuctfweb安全
进入题目,又是这个作者,试试万能密码经过实验,双写什么的都没用。作者说的神秘代码,点进去发现url变了发现并没有什么卵用……正当我没有头绪的时候,我突然看到一句话,审题真的很重要:盲注!这里附上大佬的脚本:importrequestsimporttimeurl="http://def9937b-1746-4f41-98c7-a2b55b95664a.node4.buuoj.cn:81/search
- 八月刷题总结
Uzero.
ctf
2021DASCTFJulyXCBCTF--catflag考察日志文件位置,escapeshellarg函数绕过DASCTFJulyXCBCTF4th--ezrceYAPIMock远程代码执行漏洞BUUCTF--[HarekazeCTF2019]EasyNotesSESSION反序列化BUUCTF--[SWPU2019]Web3伪造Session,生成linux中的软链接BUUCTF--[wate
- [BUUCTF][极客大挑战 2019]PHP
朋克归零膏
CTFphplinuxfirefox
备份根据提示应该就是网站备份文件能被爆破出来随手写了个爆破脚本,基于御剑字典,只供学习使用importrandomimportrequestsimporttimefrommultiprocessingimportPooldefmultiScan(target,file_name,pool_num,delay):local_pool=Pool(pool_num)dirs=get_path_dict(
- BUUCTF [极客大挑战 2019]Secret File 1
THEMIScale
还差一步这道题就出来了在想了在想了别骂了别骂了打开题目后一片黑这个时候根据经验有事没事先ctrl+a安排一下果然有问题在最下方有一个连接打开链接出现一个按钮按他就完事了并没有出来什么用burp拦截后发现提示:secr3t.php打开后提示flag在flag.php中并且给了一串php其中stristr函数不用绕过直接干就完了然后就是啊哈!你找到我了!可是你看不到我QAQ~~~我就在这里这边最后请教
- BUUCTF--[羊城杯 2020]Easyphp2
Uzero.
进入后的页面根据题目提示我们可以知道这是一道PHP代码审计的题所以使用伪协议查看源代码,这里使用的是两次url编码绕过/?file=php://filter/read=convert.quoted-printable-encode/resource=GWHT.php/?file=php://filter/read=convert.%2562%2561%2573%2565%2536%2534-enc
- BUUCTF:[ISITDTU 2019]EasyPHP --- rce 超级异或,,,吐了,,,字符之间异或, 成型的异或payload!!!
Zero_Adam
BUUCTF刷题记录RCEpython
目录:一、自己做:二、学的的三、学习WP1.这里先来个不限制字符个数的关于这个%ff以及异或的事情,咱们好好唠唠1.生成异或中间值的python脚本2.看有字符限制的时候,:参考:末初一、自己做:0xd)die('youaresoclose,omg');eval($_);?>过滤了,不少,我一般碰到rce的题,就看自己的笔记,然后把payload一股脑的网上怼,,,二、学的的正则看不明白的时候,可
- BUUCTF [b01lers2020]little_engine
皮皮蟹!
BUUCTF
1.拿到文件,进入主函数:这个是动调之前的主函数,开始动调:其中,已知字符串已经给出,为unk_5617CE521220,一共300位:进入加密函数sub_5608DAAB8510:通过多次动态调试,得到了加密算法的逻辑。看判断函数sub_5608DAAB85A0:综上,写出加密脚本:a=[0xE1,0xE
- BUUCTF--[羊城杯 2020]Blackcat
Uzero.
进入后查看源码发现提示都说听听歌了!下载Hei_Mao_Jing_Chang.mp3文件,使用命令stringsHei_Mao_Jing_Chang.mp3查看文件在文末看到一段PHP代码if(empty($_POST['Black-Cat-Sheriff'])||empty($_POST['One-ear'])){die('$clandestine=getenv("clandestine");i
- 84,【8】BUUCTF WEB [羊城杯 2020]Blackcat
rzydal
前端
进入靶场音乐硬控我3分钟回去看源码开始解题运行得到afd556602cf62addfe4132a81b2d62b9db1b6719f83e16cce13f51960f56791b最终组成payload:White-cat-monitor[]=1&Black-Cat-Sheriff=afd556602cf62addfe4132a81b2d62b9db1b6719f83e16cce13f51960f5
- BUUCTF--[HarekazeCTF2019]Avatar Uploader 1
Uzero.
name随便输一个,进入之后看到是让上传头像,这个应该是一个文件上传漏洞接下来分析所给的源码256000){error('Uploadedfileistoolarge.');}//checkfiletype$finfo=finfo_open(FILEINFO_MIME_TYPE);$type=finfo_file($finfo,$_FILES['file']['tmp_name']);finfo_
- BUUCTF_Crypto_[WUSTCTF2020]B@se
qq_58370970
经验分享
给了一个txt文件:从题目可以看出是与base64相关,不难发现是base64的变种,将base64的顺序改变了,但还有4个字符不知道可以写python脚本得到缺失的4个字符代码如下:importstrings='JASGBWcQPRXEFLbCDIlmnHUVKTYZdMovwipatNOefghq56rs****kxyz012789+/'j='ABCDEFGHIJKLMNOPQRSTUVWXY
- BUUCTF--October 2019 Twice SQL Injection
Uzero.
根据题目可以知道这是一个二次注入题注册时把我们sql语句放到username处,登录后即可看到我们想要的信息payload为:username=1'unionselectdatabase()#username=1'unionselectgroup_concat(table_name)frominformation_schema.tableswheretable_schema='ctftrainin
- BUUCTF gyctf_2020_borrowstack
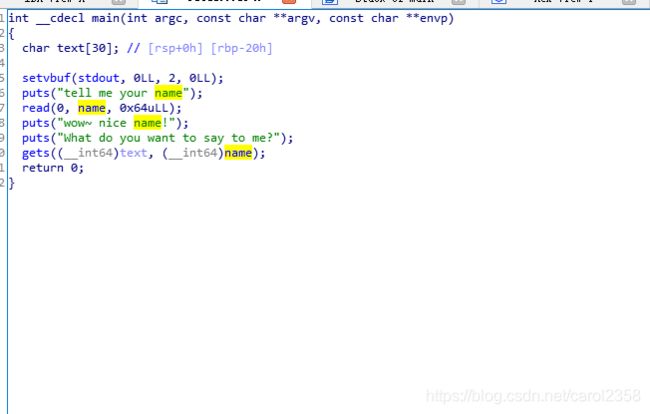
Bengd0u
第一个read的只能溢出0x10字节,也就是刚好覆盖返回地址,如果要ROP地方肯定不够所以栈迁移到bank,在那里ROP之前没遇到过这样的题,怎么迁过去我苦思冥想,最终还是看了wp,,用两个leave来控制rsp和rbp寄存器,太妙了leave是个伪代码,,分解开就是movrsp,rbppoprbp如果把栈构造成这样‘A’*0x60bank_addrleave_addr那么就有两次leavemov
- 2025.1.17—misc—一、黑客帝国 压缩包加密|图片文件格式问题
然然阿然然
“破晓”计划第一阶段训练安全网络安全misc
题目来源:buuctf黑客帝国目录一、解题思路step1:下载文件,查看情况step2:利用脚本转换数据step3:利用ARCHPR破解压缩包密码step4:解压后查看新文件一、解题思路step1:下载文件,查看情况下载附件,发现一堆数据有字母有数字,很像十六进制数据,利用python脚本将这些十六进制数据转换为二进制写入文件。step2:利用脚本转换数据importbinasciihex_dat
- hackcon ctf 2018 | pwn wp
fantasy_learner
BOF漏洞点:栈溢出利用过程栈溢出跳转callMeMaybe函数获得flagexpSheSellsSeaShells90流程分析:给出了输入的栈地址有一个栈溢出点没有nx利用过程:根据以上三点,得出可以使用ret2shellcode使用shellcraft生成shellcode利用栈溢出,输入并跳转到shellcodeexpSimpleYetElegent150这道题目做了最久,卡在了能否根据_d
- BUUCTF 2021-10-4 Pwn
Ch1lkat
BUUCTFPwnlinuxpwn
文章目录保持手感echo分析EXPPwnme1分析EXPwdb_2018_1st_babyheap分析EXPFSOPhouseoforange_hitcon_2016分析前置知识House_of_orangeFSOPEXPzctf_2016_note3分析EXPgyctf_2020_document分析EXP动态调试复现护网杯_gettingstart分析EXPpicoctf_2018_buffe
- 【BUUCTF】[SWPU2019]神奇的二维码
shane_seven
ctfwp
0x00 刚拿到这题的时候,还以为很简单的样子,结果发现才是一坑接一坑,套娃坑套娃。(出题人友好点儿吧,球球了>_<)0x01 惯例下好文件,是个rar,打开发现是个“神奇的二维码”,直接扫描无果,拿到winhex下查看,发现好几个rar文件 分别手动复制粘贴到新文件,保存,共有四个rar,按照在文件里的位置先后顺序排列 1.rar打开是一行base64编码的字符串,解码后为 打开2.rar,里面
- BUUCTF misc 专题(127)[UTCTF2020]spectogram
tt_npc
安全网络安全音视频
下载下来一个音频,拖到au中没啥发现,也听不出来这题需要用到的一个工具是SonicVisualiser,也是看了大佬的博客才知道的DownloadSonicVisualiser打开是这样的一个界面右键选择Layer->AddSpectrogram能很明显看到flagflag{sp3tr0gr4m0ph0n3}
- BUUCTF msic 专题(128)[ACTF新生赛2020]剑龙
tt_npc
网络安全安全
下载附件,最后解压出来一张jpg,一个无后缀文件和一个pwd.txt先把无后缀文件拖进010查看一下,看不出来什么。看看明显的pwd.txtaaencode解密jjencode与aaencode解密工具-jjencode解密-aaencode解密-在线工具得到welcom3!;再看看图片,welcom3!;岷县是一个密码那么猜测是steghide隐写应该是需要des解密的密文,但是缺个密钥在图片的
- BUUCTF misc 专题(30)webshell后门
tt_npc
python网络安全安全
看题目,又是一道后门查杀的题目,下载了资源以后我们发现是一个rar的文件解压里面的文件后打开D盾进行后门查杀在这里找到了,并根据路径打开所在的文件夹,找到文件根据题目提示,我们在这里找到了md5再根据md5中的pass我们可以找到pass包上flag就是答案了flag{ba8e6c6f35a53933b871480bb9a9545c}
- BUUCTF misc 专题(126)voip
tt_npc
安全网络安全音视频
下载附件,是一个流量包,wireshark打开分析协议分级发现都是RTP流,也不是很懂,上网搜了一下,发现是一种语音通话技术然后wireshark中有电话的选项,可以选中分析rtp流,并且播放播放的音频就是flag,flag{9001IVR}
- java封装继承多态等
麦田的设计者
javaeclipsejvmcencapsulatopn
最近一段时间看了很多的视频却忘记总结了,现在只能想到什么写什么了,希望能起到一个回忆巩固的作用。
1、final关键字
译为:最终的
&
- F5与集群的区别
bijian1013
weblogic集群F5
http请求配置不是通过集群,而是F5;集群是weblogic容器的,如果是ejb接口是通过集群。
F5同集群的差别,主要还是会话复制的问题,F5一把是分发http请求用的,因为http都是无状态的服务,无需关注会话问题,类似
- LeetCode[Math] - #7 Reverse Integer
Cwind
java题解MathLeetCodeAlgorithm
原题链接:#7 Reverse Integer
要求:
按位反转输入的数字
例1: 输入 x = 123, 返回 321
例2: 输入 x = -123, 返回 -321
难度:简单
分析:
对于一般情况,首先保存输入数字的符号,然后每次取输入的末位(x%10)作为输出的高位(result = result*10 + x%10)即可。但
- BufferedOutputStream
周凡杨
首先说一下这个大批量,是指有上千万的数据量。
例子:
有一张短信历史表,其数据有上千万条数据,要进行数据备份到文本文件,就是执行如下SQL然后将结果集写入到文件中!
select t.msisd
- linux下模拟按键输入和鼠标
被触发
linux
查看/dev/input/eventX是什么类型的事件, cat /proc/bus/input/devices
设备有着自己特殊的按键键码,我需要将一些标准的按键,比如0-9,X-Z等模拟成标准按键,比如KEY_0,KEY-Z等,所以需要用到按键 模拟,具体方法就是操作/dev/input/event1文件,向它写入个input_event结构体就可以模拟按键的输入了。
linux/in
- ContentProvider初体验
肆无忌惮_
ContentProvider
ContentProvider在安卓开发中非常重要。与Activity,Service,BroadcastReceiver并称安卓组件四大天王。
在android中的作用是用来对外共享数据。因为安卓程序的数据库文件存放在data/data/packagename里面,这里面的文件默认都是私有的,别的程序无法访问。
如果QQ游戏想访问手机QQ的帐号信息一键登录,那么就需要使用内容提供者COnte
- 关于Spring MVC项目(maven)中通过fileupload上传文件
843977358
mybatisspring mvc修改头像上传文件upload
Spring MVC 中通过fileupload上传文件,其中项目使用maven管理。
1.上传文件首先需要的是导入相关支持jar包:commons-fileupload.jar,commons-io.jar
因为我是用的maven管理项目,所以要在pom文件中配置(每个人的jar包位置根据实际情况定)
<!-- 文件上传 start by zhangyd-c --&g
- 使用svnkit api,纯java操作svn,实现svn提交,更新等操作
aigo
svnkit
原文:http://blog.csdn.net/hardwin/article/details/7963318
import java.io.File;
import org.apache.log4j.Logger;
import org.tmatesoft.svn.core.SVNCommitInfo;
import org.tmateso
- 对比浏览器,casperjs,httpclient的Header信息
alleni123
爬虫crawlerheader
@Override
protected void doGet(HttpServletRequest req, HttpServletResponse res) throws ServletException, IOException
{
String type=req.getParameter("type");
Enumeration es=re
- java.io操作 DataInputStream和DataOutputStream基本数据流
百合不是茶
java流
1,java中如果不保存整个对象,只保存类中的属性,那么我们可以使用本篇文章中的方法,如果要保存整个对象 先将类实例化 后面的文章将详细写到
2,DataInputStream 是java.io包中一个数据输入流允许应用程序以与机器无关方式从底层输入流中读取基本 Java 数据类型。应用程序可以使用数据输出流写入稍后由数据输入流读取的数据。
- 车辆保险理赔案例
bijian1013
车险
理赔案例:
一货运车,运输公司为车辆购买了机动车商业险和交强险,也买了安全生产责任险,运输一车烟花爆竹,在行驶途中发生爆炸,出现车毁、货损、司机亡、炸死一路人、炸毁一间民宅等惨剧,针对这几种情况,该如何赔付。
赔付建议和方案:
客户所买交强险在这里不起作用,因为交强险的赔付前提是:“机动车发生道路交通意外事故”;
如果是交通意外事故引发的爆炸,则优先适用交强险条款进行赔付,不足的部分由商业
- 学习Spring必学的Java基础知识(5)—注解
bijian1013
javaspring
文章来源:http://www.iteye.com/topic/1123823,整理在我的博客有两个目的:一个是原文确实很不错,通俗易懂,督促自已将博主的这一系列关于Spring文章都学完;另一个原因是为免原文被博主删除,在此记录,方便以后查找阅读。
有必要对
- 【Struts2一】Struts2 Hello World
bit1129
Hello world
Struts2 Hello World应用的基本步骤
创建Struts2的Hello World应用,包括如下几步:
1.配置web.xml
2.创建Action
3.创建struts.xml,配置Action
4.启动web server,通过浏览器访问
配置web.xml
<?xml version="1.0" encoding="
- 【Avro二】Avro RPC框架
bit1129
rpc
1. Avro RPC简介 1.1. RPC
RPC逻辑上分为二层,一是传输层,负责网络通信;二是协议层,将数据按照一定协议格式打包和解包
从序列化方式来看,Apache Thrift 和Google的Protocol Buffers和Avro应该是属于同一个级别的框架,都能跨语言,性能优秀,数据精简,但是Avro的动态模式(不用生成代码,而且性能很好)这个特点让人非常喜欢,比较适合R
- lua set get cookie
ronin47
lua cookie
lua:
local access_token = ngx.var.cookie_SGAccessToken
if access_token then
ngx.header["Set-Cookie"] = "SGAccessToken="..access_token.."; path=/;Max-Age=3000"
end
- java-打印不大于N的质数
bylijinnan
java
public class PrimeNumber {
/**
* 寻找不大于N的质数
*/
public static void main(String[] args) {
int n=100;
PrimeNumber pn=new PrimeNumber();
pn.printPrimeNumber(n);
System.out.print
- Spring源码学习-PropertyPlaceholderHelper
bylijinnan
javaspring
今天在看Spring 3.0.0.RELEASE的源码,发现PropertyPlaceholderHelper的一个bug
当时觉得奇怪,上网一搜,果然是个bug,不过早就有人发现了,且已经修复:
详见:
http://forum.spring.io/forum/spring-projects/container/88107-propertyplaceholderhelper-bug
- [逻辑与拓扑]布尔逻辑与拓扑结构的结合会产生什么?
comsci
拓扑
如果我们已经在一个工作流的节点中嵌入了可以进行逻辑推理的代码,那么成百上千个这样的节点如果组成一个拓扑网络,而这个网络是可以自动遍历的,非线性的拓扑计算模型和节点内部的布尔逻辑处理的结合,会产生什么样的结果呢?
是否可以形成一种新的模糊语言识别和处理模型呢? 大家有兴趣可以试试,用软件搞这些有个好处,就是花钱比较少,就算不成
- ITEYE 都换百度推广了
cuisuqiang
GoogleAdSense百度推广广告外快
以前ITEYE的广告都是谷歌的Google AdSense,现在都换成百度推广了。
为什么个人博客设置里面还是Google AdSense呢?
都知道Google AdSense不好申请,这在ITEYE上也不是讨论了一两天了,强烈建议ITEYE换掉Google AdSense。至少,用一个好申请的吧。
什么时候能从ITEYE上来点外快,哪怕少点
- 新浪微博技术架构分析
dalan_123
新浪微博架构
新浪微博在短短一年时间内从零发展到五千万用户,我们的基层架构也发展了几个版本。第一版就是是非常快的,我们可以非常快的实现我们的模块。我们看一下技术特点,微博这个产品从架构上来分析,它需要解决的是发表和订阅的问题。我们第一版采用的是推的消息模式,假如说我们一个明星用户他有10万个粉丝,那就是说用户发表一条微博的时候,我们把这个微博消息攒成10万份,这样就是很简单了,第一版的架构实际上就是这两行字。第
- 玩转ARP攻击
dcj3sjt126com
r
我写这片文章只是想让你明白深刻理解某一协议的好处。高手免看。如果有人利用这片文章所做的一切事情,盖不负责。 网上关于ARP的资料已经很多了,就不用我都说了。 用某一位高手的话来说,“我们能做的事情很多,唯一受限制的是我们的创造力和想象力”。 ARP也是如此。 以下讨论的机子有 一个要攻击的机子:10.5.4.178 硬件地址:52:54:4C:98
- PHP编码规范
dcj3sjt126com
编码规范
一、文件格式
1. 对于只含有 php 代码的文件,我们将在文件结尾处忽略掉 "?>" 。这是为了防止多余的空格或者其它字符影响到代码。例如:<?php$foo = 'foo';2. 缩进应该能够反映出代码的逻辑结果,尽量使用四个空格,禁止使用制表符TAB,因为这样能够保证有跨客户端编程器软件的灵活性。例
- linux 脱机管理(nohup)
eksliang
linux nohupnohup
脱机管理 nohup
转载请出自出处:http://eksliang.iteye.com/blog/2166699
nohup可以让你在脱机或者注销系统后,还能够让工作继续进行。他的语法如下
nohup [命令与参数] --在终端机前台工作
nohup [命令与参数] & --在终端机后台工作
但是这个命令需要注意的是,nohup并不支持bash的内置命令,所
- BusinessObjects Enterprise Java SDK
greemranqq
javaBOSAPCrystal Reports
最近项目用到oracle_ADF 从SAP/BO 上调用 水晶报表,资料比较少,我做一个简单的分享,给和我一样的新手 提供更多的便利。
首先,我是尝试用JAVA JSP 去访问的。
官方API:http://devlibrary.businessobjects.com/BusinessObjectsxi/en/en/BOE_SDK/boesdk_ja
- 系统负载剧变下的管控策略
iamzhongyong
高并发
假如目前的系统有100台机器,能够支撑每天1亿的点击量(这个就简单比喻一下),然后系统流量剧变了要,我如何应对,系统有那些策略可以处理,这里总结了一下之前的一些做法。
1、水平扩展
这个最容易理解,加机器,这样的话对于系统刚刚开始的伸缩性设计要求比较高,能够非常灵活的添加机器,来应对流量的变化。
2、系统分组
假如系统服务的业务不同,有优先级高的,有优先级低的,那就让不同的业务调用提前分组
- BitTorrent DHT 协议中文翻译
justjavac
bit
前言
做了一个磁力链接和BT种子的搜索引擎 {Magnet & Torrent},因此把 DHT 协议重新看了一遍。
BEP: 5Title: DHT ProtocolVersion: 3dec52cb3ae103ce22358e3894b31cad47a6f22bLast-Modified: Tue Apr 2 16:51:45 2013 -070
- Ubuntu下Java环境的搭建
macroli
java工作ubuntu
配置命令:
$sudo apt-get install ubuntu-restricted-extras
再运行如下命令:
$sudo apt-get install sun-java6-jdk
待安装完毕后选择默认Java.
$sudo update- alternatives --config java
安装过程提示选择,输入“2”即可,然后按回车键确定。
- js字符串转日期(兼容IE所有版本)
qiaolevip
TODateStringIE
/**
* 字符串转时间(yyyy-MM-dd HH:mm:ss)
* result (分钟)
*/
stringToDate : function(fDate){
var fullDate = fDate.split(" ")[0].split("-");
var fullTime = fDate.split("
- 【数据挖掘学习】关联规则算法Apriori的学习与SQL简单实现购物篮分析
superlxw1234
sql数据挖掘关联规则
关联规则挖掘用于寻找给定数据集中项之间的有趣的关联或相关关系。
关联规则揭示了数据项间的未知的依赖关系,根据所挖掘的关联关系,可以从一个数据对象的信息来推断另一个数据对象的信息。
例如购物篮分析。牛奶 ⇒ 面包 [支持度:3%,置信度:40%] 支持度3%:意味3%顾客同时购买牛奶和面包。 置信度40%:意味购买牛奶的顾客40%也购买面包。 规则的支持度和置信度是两个规则兴
- Spring 5.0 的系统需求,期待你的反馈
wiselyman
spring
Spring 5.0将在2016年发布。Spring5.0将支持JDK 9。
Spring 5.0的特性计划还在工作中,请保持关注,所以作者希望从使用者得到关于Spring 5.0系统需求方面的反馈。