- hackcon ctf 2018 | pwn wp
fantasy_learner
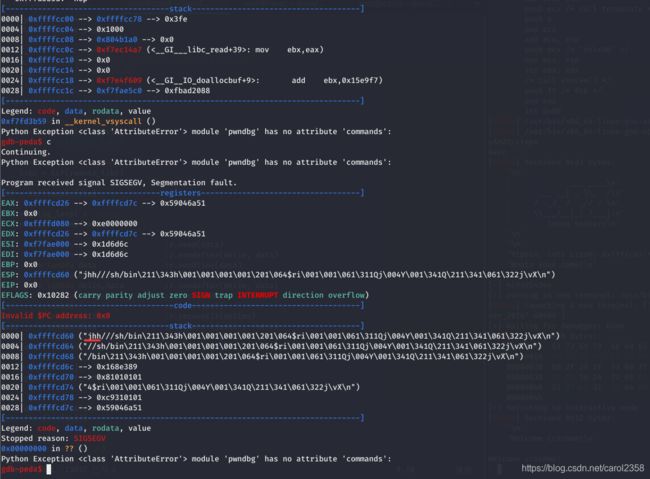
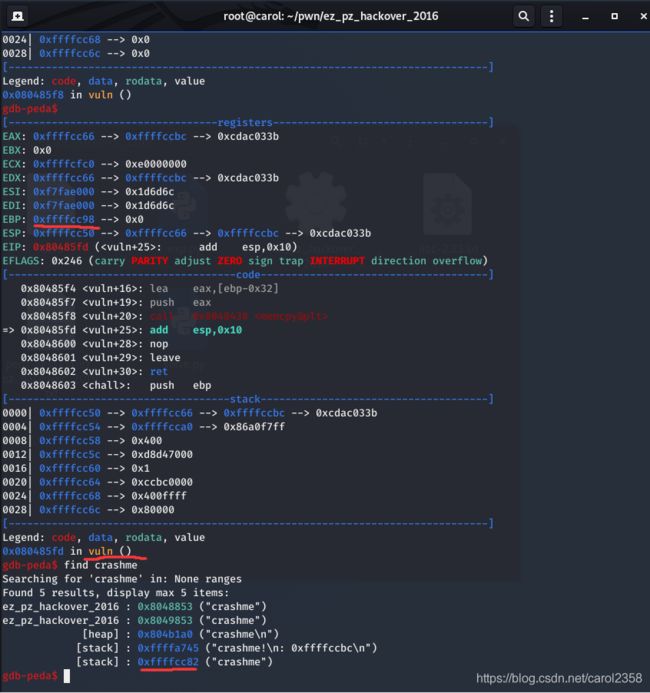
BOF漏洞点:栈溢出利用过程栈溢出跳转callMeMaybe函数获得flagexpSheSellsSeaShells90流程分析:给出了输入的栈地址有一个栈溢出点没有nx利用过程:根据以上三点,得出可以使用ret2shellcode使用shellcraft生成shellcode利用栈溢出,输入并跳转到shellcodeexpSimpleYetElegent150这道题目做了最久,卡在了能否根据_d
- BUUCTF 2021-10-4 Pwn
Ch1lkat
BUUCTFPwnlinuxpwn
文章目录保持手感echo分析EXPPwnme1分析EXPwdb_2018_1st_babyheap分析EXPFSOPhouseoforange_hitcon_2016分析前置知识House_of_orangeFSOPEXPzctf_2016_note3分析EXPgyctf_2020_document分析EXP动态调试复现护网杯_gettingstart分析EXPpicoctf_2018_buffe
- 【BUUCTF】[SWPU2019]神奇的二维码
shane_seven
ctfwp
0x00 刚拿到这题的时候,还以为很简单的样子,结果发现才是一坑接一坑,套娃坑套娃。(出题人友好点儿吧,球球了>_<)0x01 惯例下好文件,是个rar,打开发现是个“神奇的二维码”,直接扫描无果,拿到winhex下查看,发现好几个rar文件 分别手动复制粘贴到新文件,保存,共有四个rar,按照在文件里的位置先后顺序排列 1.rar打开是一行base64编码的字符串,解码后为 打开2.rar,里面
- BUUCTF misc 专题(127)[UTCTF2020]spectogram
tt_npc
安全网络安全音视频
下载下来一个音频,拖到au中没啥发现,也听不出来这题需要用到的一个工具是SonicVisualiser,也是看了大佬的博客才知道的DownloadSonicVisualiser打开是这样的一个界面右键选择Layer->AddSpectrogram能很明显看到flagflag{sp3tr0gr4m0ph0n3}
- BUUCTF msic 专题(128)[ACTF新生赛2020]剑龙
tt_npc
网络安全安全
下载附件,最后解压出来一张jpg,一个无后缀文件和一个pwd.txt先把无后缀文件拖进010查看一下,看不出来什么。看看明显的pwd.txtaaencode解密jjencode与aaencode解密工具-jjencode解密-aaencode解密-在线工具得到welcom3!;再看看图片,welcom3!;岷县是一个密码那么猜测是steghide隐写应该是需要des解密的密文,但是缺个密钥在图片的
- BUUCTF misc 专题(30)webshell后门
tt_npc
python网络安全安全
看题目,又是一道后门查杀的题目,下载了资源以后我们发现是一个rar的文件解压里面的文件后打开D盾进行后门查杀在这里找到了,并根据路径打开所在的文件夹,找到文件根据题目提示,我们在这里找到了md5再根据md5中的pass我们可以找到pass包上flag就是答案了flag{ba8e6c6f35a53933b871480bb9a9545c}
- BUUCTF misc 专题(126)voip
tt_npc
安全网络安全音视频
下载附件,是一个流量包,wireshark打开分析协议分级发现都是RTP流,也不是很懂,上网搜了一下,发现是一种语音通话技术然后wireshark中有电话的选项,可以选中分析rtp流,并且播放播放的音频就是flag,flag{9001IVR}
- BUUCTF misc 专题(11)wireshark
tt_npc
wireshark测试工具网络网络安全
读题,很明显,这是一波带领你收集工具的题目,就是wiresharkWireshark·Downloadhttps://www.wireshark.org/download.html先是对wireshark的下载和安装下载好题目资源以后进行解压,直接拖入到wireshark中由题知,管理员的密码就是答案那么我们直接用http.request.method=="POST"滤出post就行让我们再用TC
- buuctf-misc-[SWPU2019]神奇的二维码1
mlws1900
buuctfmiscctfjavaservletjvmctf
下载附件,看到一个二维码利用二维码工具进行扫码,获得信息flag不在此,用winhex打开观察到多个rar文件和类似base64编码的内容看到最后看到一个mp3文件,开始文件分离(用windows系统的foremost无法分离文件)用kali的binwalk进行分离发现四个rar文件一一打开查看第一个rar文件打开一个图片和一个无法打开的f图片第二个rar文件YXNkZmdoamtsMTIzNDU
- BUUCTF [SWPU2019]神奇的二维码 1
玥轩_521
BUUCTFMISC安全CTF笔记网络安全BUUCTFMisc
BUUCTF:https://buuoj.cn/challenges题目描述:得到的flag请包上flag{}提交。密文:下载附件,得到一个.png图片。解题思路:1、使用QRresearch扫一下,得到“swpuctf{flag_is_not_here}”的提示。2、放到010Editor中看一下,没找到什么明显的特征。使用Kali中的binwalk工具进行检测,发现四个rar压缩包。使用bin
- BUUCTF misc 专题(47)[SWPU2019]神奇的二维码
tt_npc
网络安全安全python
下载附件,得到一张二维码图片,并用工具扫描(因为图片违规了,所以就不放了哈。工具的话,一般的二维码扫描都可以)swpuctf{flag_is_not_here},(刚开始出了点小差错对不住各位师傅)根据提示知道答案并不在这里,拖入winhex进行查看搜索出多个Rar,将文件放入kali进行binwalk分离出了多个rar,先查看txt文档中的内容YXNkZmdoamtsMTIzNDU2Nzg5MA
- 【BUUCTF 加固题】Ezsql 速通
hacker-routing
webCTF夺旗赛开发语言前端javascriptweb安全htmlphpCTF
博主介绍博主介绍:大家好,我是hacker-routing,很高兴认识大家~✨主攻领域:【渗透领域】【应急响应】【Java】【VulnHub靶场复现】【面试分析】点赞➕评论➕收藏==养成习惯(一键三连)欢迎关注一起学习一起讨论⭐️一起进步文末有彩蛋作者水平有限,欢迎各位大佬指点,相互学习进步!目录前言一、访问web网址二、ssh远程登录三、加固网站源代码前言靶机地址解释:第一行:目标机器WEB服
- ctf刷题 ctfshow【网鼎杯】
路向阳_
CTF学习网络安全
Php-3、java-3、目录一、网鼎杯-青龙组-web--AreUserialZ1、源码见下:serialzcopy3、绕过语法详解:4、尝试绕过:二、php特性三、php反序列化漏洞四、Buuctf一、网鼎杯-青龙组-web--AreUserialZBuuctf1、源码见下:serialzcopyPhp反序列化:思路:先阅读源码,在分析思路//大致思路:新建一个对象filenameflag.p
- [WUSTCTF2020]CV Maker1 --不会编程的崽
不会编程的崽
网络安全web安全安全
写个简单的文件上传题目吧。不知道为什么buuctf很少人解这题看着有点高端,但实际花里胡哨的。随便注册一个账户就行很明显,文件上传。burp启动,先上传个php文件试试。提示太明显了。而且测试它还不检测后缀添加GIF89a上传成功,找到路径即可。去页面复制图像路径,或者数据包里找也行上蚁剑
- [Flask]SSTI1 buuctf
bK_Rose
ctfsstipython网络安全
声明:本篇文章csdn要我一天发两篇所以我来水的跟ssti注入的详细知识我这里写了https://blog.csdn.net/weixin_74790320/article/details/136154130上面链接我复现了vulhub的SSTI,其实本质上是一道题然后我们就用{{''.__class__}}看类的类型,但是无所谓,啥类型都可以,因为我们要找到的是他的基类,然后通过基类去找子类{{
- 【Crypto | CTF】RSA打法 集合
星盾网安
CTF安全密码学
天命:我发现题题不一样,已知跟求知的需求都不一样题目一:已知pqE,计算T,最后求D已知两个质数pq和公钥E,通过p和q计算出欧拉函数T,最后求私钥D【密码学|CTF】BUUCTFRSA-CSDN博客题目二:已知pqE,存在c,计算T,求出D,最后求m已知两个质数pq和公钥E,通过p和q计算出欧拉函数T,求出私钥,通过私钥解密密文c,得到明文m【Crypto|CTF】BUUCTFrsarsa1-C
- 【Crypto | CTF】BUUCTF RSA1
星盾网安
CTF算法
天命:都不知道别人那些底层公式是怎么来的,大神们推到了几页纸天命:无端端推导着就多了个k,多个一些奇奇怪怪的东西,一脸懵逼天命:没事,拿代码当成公式背也能解密出来已知:pqdpdqc求mc是密文,m是明文,dp和dq是一半的明文,但不知道为什么居然是相同的fromgmpy2import*fromCrypto.Util.numberimport*p=8637633767257008567099653
- 【web | CTF】BUUCTF [网鼎杯 2020 青龙组]AreUSerialz
星盾网安
CTFphp
天命:php的序列化题目简直是玄学,既不能本地复现,也不能求证靶场环境天命:本地php是复现不了反序列化漏洞的,都不知道是版本问题还是其他问题天命:这题也是有点奇怪的,明明用字符串2也应该是可以,但偏偏就不行,神奇了进来题目先看到php代码审计,是反序列化漏洞先看进来入口的逻辑,判断是不是正常的ascii码字符,然后反序列化,可以忽略校验,都是正常的//校验你是不是ascii码里面的合法字符fun
- BUUCTF-Real-[Jupyter]notebook-rce
真的学不了一点。。。
漏洞复现与研究jupyter安全ide网络安全
1、简介JupyterNotebook(此前被称为IPythonnotebook)是一个交互式笔记本,支持运行40多种编程语言。如果管理员未为JupyterNotebook配置密码,将导致未授权访问漏洞,游客可在其中创建一个console并执行任意Python代码和命令。2、复现环境buuctfGithub这里我使用buuctf进行复现,图个简单方便!3、漏洞复现直接新建一个终端窗口即可!!也可以
- [BJDCTF2020]ZJCTF,不过如此 1
林本
php开发语言
提示:文章写完后,目录可以自动生成,如何生成可参考右边的帮助文档[BJDCTF2020]ZJCTF,不过如此1题目一、做题步骤1.审计代码2.伪协议3.解密题目BUUCTF的[BJDCTF2020]ZJCTF,不过如此1一、做题步骤1.审计代码代码如下:".file_get_contents($text,'r')."";if(preg_match("/flag/",$file)){die("Not
- BUUCTF/强网杯2019 随便注.堆叠注入?
Visianlee
尝试注入发现过滤preg_match("/select|update|delete|drop|insert|where|\./i",$inject);/i不区分大小写匹配,也过滤了.sqlmap跑一波pythonsqlmap.py-u"http://web16.buuoj.cn/?inject=3"-v3--risk3-Dsupersqli--tables–test-skip=where能跑出数据
- buuctf [ACTF2020 新生赛]Include wp
又一片风
CTF_WP安全web安全
本题考查文件包含漏洞。文件包含漏洞是一种注入型漏洞,其本质就是输入一段用户能够控制的脚本或者代码,并让服务端执行。1.我们看标题就知道是文件包含漏洞,然后发现作者给了我们一个小tip,在url中:2.我们能够确定是文件包含漏洞了,那就以http伪协议来构造payload:payload:/?file=php://filter/read=convert.base64-encode/resource=
- buuctf [ACTF2020 新生赛]Exec1
又一片风
CTF_WPlinuxweb安全安全
本题考查linux命令,越权查询知识点:ls查看当前目录下的所有目录和文件ls/查看根目录下的所有目录和文件cat以文本形式读取文件1.我们进入靶机地址,看到有这样一个ping地址2.首先我们ping一下本机,即127.0.0.1,发现可以正常ping到3.那么我们就可以进行双重操作,即命令1&&命令2:在进行命令1成功后进行命令2;我们猜想服务器用的是linux系统4.发现在根目录下存在flag
- buuctf [HCTF 2018]WarmUp1
又一片风
CTF_WPweb安全php
本题考查的知识点有:php源码审计,url过滤1.首先我们进入,看到了一个大大的滑稽,所以先看看源代码2.看到提示:source.php,所以我们访问一下"source.php","hint"=>"hint.php"];//白名单列表if(!isset($page)||!is_string($page)){//检测变量page是不是被声明,变量page是不是字符串echo"youcan'tseei
- buuctf [极客大挑战 2019]EasySQL1
又一片风
CTF_WP数据库web安全
本题考的是sql注入基础知识点,我们先来了解一下什么是sql注入及基本语句。sql注入是一种数据库查询和程序设计语言,用于存取数据以及查询、更新和管理关系数据库系统。如果后端对用户所输入的数据管理不严,则可能会造成数据泄露,未授权查询等风险。对于本题,我们首先判断一下其闭合方式,sql报错如图,则闭合方式为单引号闭合。我们接着构造万能密码:1'or1=1#(#号为注释,将下个语句注释掉)得到回显f
- buuctf [极客大挑战 2019]Havefun1
又一片风
CTF_WP安全php
一道简单的源码审计。我们首先查看一下它的源码,发现此php代码:$cat为变量,采用get传参;如果cat弱等于dog,则echo(打印)flag。构造payload:得到flag。知识点普及:在php中,“==”表示弱等于,仅进行输入内容比较,不进行输入内容的形式比较;“===”表示强等于,进行输入内容比较,也进行输入内容的形式比较。
- [BUUCTF]-PWN:mrctf2020_easy_equation解析
Clxhzg
PWN网络安全安全
查看保护再看ida很明了,题目就是让我们用格式化字符串漏洞修改judge的值(可以用python脚本进行计算,最终算出来得2)使等式成立,然后getshell。虽然操作比较简单,但我还是列出了几种方法解法一:frompwnimport*context(log_level='debug')p=process('./equation')judge=0x60105Cpayload=b'bb'+b'%9$
- BUUCTF LKWA
有搞头-CC
BUUCTFweb安全安全前端安全性测试
1.访问页面。2.选择Variablesvariable关卡3.获得flaghttp://357dab81-78b8-4d74-976a-4a69dd894542.node5.buuoj.cn:81/variables/variable.php?func=passthru&input=cat+%2Fflagflag{0020ced6-8166-4fa5-87a7-7d93ee687c3e}
- 【BUUCTF N1BOOK】[第三章 web进阶] 通关
hacker-routing
webCTF夺旗赛前端javascript开发语言web安全BUUCTFCTF
博主介绍博主介绍:大家好,我是hacker-routing,很高兴认识大家~✨主攻领域:【渗透领域】【应急响应】【python】【VulnHub靶场复现】【面试分析】点赞➕评论➕收藏==养成习惯(一键三连)欢迎关注一起学习一起讨论⭐️一起进步文末有彩蛋作者水平有限,欢迎各位大佬指点,相互学习进步!目录前言[第三章web进阶]逻辑漏洞1、登录2、挣钱3、买flag[第三章web进阶]SSTISST
- 【 buuctf--刷新过的图片】
HeiOs.
CTF
前言:这题主要运用到了新的工具F5-steganography由于java环境不合适的原因,我不得不重新配java11.0.18。具体思路:非常帅气的一张图片。。。用binwalk,stegsolve,zsteg,exiftool等工具无果后,注意到题目说到刷新图片的问题,看了大佬的wp[BUUCTFmisc]刷新过的图片_buuctf刷新过的图片-CSDN博客,需要用到F5-steganogra
- springmvc 下 freemarker页面枚举的遍历输出
杨白白
enumfreemarker
spring mvc freemarker 中遍历枚举
1枚举类型有一个本地方法叫values(),这个方法可以直接返回枚举数组。所以可以利用这个遍历。
enum
public enum BooleanEnum {
TRUE(Boolean.TRUE, "是"), FALSE(Boolean.FALSE, "否");
- 实习简要总结
byalias
工作
来白虹不知不觉中已经一个多月了,因为项目还在需求分析及项目架构阶段,自己在这段
时间都是在学习相关技术知识,现在对这段时间的工作及学习情况做一个总结:
(1)工作技能方面
大体分为两个阶段,Java Web 基础阶段和Java EE阶段
1)Java Web阶段
在这个阶段,自己主要着重学习了 JSP, Servlet, JDBC, MySQL,这些知识的核心点都过
了一遍,也
- Quartz——DateIntervalTrigger触发器
eksliang
quartz
转载请出自出处:http://eksliang.iteye.com/blog/2208559 一.概述
simpleTrigger 内部实现机制是通过计算间隔时间来计算下次的执行时间,这就导致他有不适合调度的定时任务。例如我们想每天的 1:00AM 执行任务,如果使用 SimpleTrigger,间隔时间就是一天。注意这里就会有一个问题,即当有 misfired 的任务并且恢复执行时,该执行时间
- Unix快捷键
18289753290
unixUnix;快捷键;
复制,删除,粘贴:
dd:删除光标所在的行 &nbs
- 获取Android设备屏幕的相关参数
酷的飞上天空
android
包含屏幕的分辨率 以及 屏幕宽度的最大dp 高度最大dp
TextView text = (TextView)findViewById(R.id.text);
DisplayMetrics dm = new DisplayMetrics();
text.append("getResources().ge
- 要做物联网?先保护好你的数据
蓝儿唯美
数据
根据Beecham Research的说法,那些在行业中希望利用物联网的关键领域需要提供更好的安全性。
在Beecham的物联网安全威胁图谱上,展示了那些可能产生内外部攻击并且需要通过快速发展的物联网行业加以解决的关键领域。
Beecham Research的技术主管Jon Howes说:“之所以我们目前还没有看到与物联网相关的严重安全事件,是因为目前还没有在大型客户和企业应用中进行部署,也就
- Java取模(求余)运算
随便小屋
java
整数之间的取模求余运算很好求,但几乎没有遇到过对负数进行取模求余,直接看下面代码:
/**
*
* @author Logic
*
*/
public class Test {
public static void main(String[] args) {
// TODO A
- SQL注入介绍
aijuans
sql注入
二、SQL注入范例
这里我们根据用户登录页面
<form action="" > 用户名:<input type="text" name="username"><br/> 密 码:<input type="password" name="passwor
- 优雅代码风格
aoyouzi
代码
总结了几点关于优雅代码风格的描述:
代码简单:不隐藏设计者的意图,抽象干净利落,控制语句直截了当。
接口清晰:类型接口表现力直白,字面表达含义,API 相互呼应以增强可测试性。
依赖项少:依赖关系越少越好,依赖少证明内聚程度高,低耦合利于自动测试,便于重构。
没有重复:重复代码意味着某些概念或想法没有在代码中良好的体现,及时重构消除重复。
战术分层:代码分层清晰,隔离明确,
- 布尔数组
百合不是茶
java布尔数组
androi中提到了布尔数组;
布尔数组默认的是false, 并且只会打印false或者是true
布尔数组的例子; 根据字符数组创建布尔数组
char[] c = {'p','u','b','l','i','c'};
//根据字符数组的长度创建布尔数组的个数
boolean[] b = new bool
- web.xml之welcome-file-list、error-page
bijian1013
javaweb.xmlservleterror-page
welcome-file-list
1.定义:
<welcome-file-list>
<welcome-file>login.jsp</welcome>
</welcome-file-list>
2.作用:用来指定WEB应用首页名称。
error-page1.定义:
<error-page&g
- richfaces 4 fileUpload组件删除上传的文件
sunjing
clearRichfaces 4fileupload
页面代码
<h:form id="fileForm"> <rich:
- 技术文章备忘
bit1129
技术文章
Zookeeper
http://wenku.baidu.com/view/bab171ffaef8941ea76e05b8.html
http://wenku.baidu.com/link?url=8thAIwFTnPh2KL2b0p1V7XSgmF9ZEFgw4V_MkIpA9j8BX2rDQMPgK5l3wcs9oBTxeekOnm5P3BK8c6K2DWynq9nfUCkRlTt9uV
- org.hibernate.hql.ast.QuerySyntaxException: unexpected token: on near line 1解决方案
白糖_
Hibernate
文章摘自:http://blog.csdn.net/yangwawa19870921/article/details/7553181
在编写HQL时,可能会出现这种代码:
select a.name,b.age from TableA a left join TableB b on a.id=b.id
如果这是HQL,那么这段代码就是错误的,因为HQL不支持
- sqlserver按照字段内容进行排序
bozch
按照内容排序
在做项目的时候,遇到了这样的一个需求:
从数据库中取出的数据集,首先要将某个数据或者多个数据按照地段内容放到前面显示,例如:从学生表中取出姓李的放到数据集的前面;
select * fro
- 编程珠玑-第一章-位图排序
bylijinnan
java编程珠玑
import java.io.BufferedWriter;
import java.io.File;
import java.io.FileWriter;
import java.io.IOException;
import java.io.Writer;
import java.util.Random;
public class BitMapSearch {
- Java关于==和equals
chenbowen00
java
关于==和equals概念其实很简单,一个是比较内存地址是否相同,一个比较的是值内容是否相同。虽然理解上不难,但是有时存在一些理解误区,如下情况:
1、
String a = "aaa";
a=="aaa";
==> true
2、
new String("aaa")==new String("aaa
- [IT与资本]软件行业需对外界投资热情保持警惕
comsci
it
我还是那个看法,软件行业需要增强内生动力,尽量依靠自有资金和营业收入来进行经营,避免在资本市场上经受各种不同类型的风险,为企业自主研发核心技术和产品提供稳定,温和的外部环境...
如果我们在自己尚未掌握核心技术之前,企图依靠上市来筹集资金,然后使劲往某个领域砸钱,然
- oracle 数据块结构
daizj
oracle块数据块块结构行目录
oracle 数据块是数据库存储的最小单位,一般为操作系统块的N倍。其结构为:
块头--〉空行--〉数据,其实际为纵行结构。
块的标准大小由初始化参数DB_BLOCK_SIZE指定。具有标准大小的块称为标准块(Standard Block)。块的大小和标准块的大小不同的块叫非标准块(Nonstandard Block)。同一数据库中,Oracle9i及以上版本支持同一数据库中同时使用标
- github上一些觉得对自己工作有用的项目收集
dengkane
github
github上一些觉得对自己工作有用的项目收集
技能类
markdown语法中文说明
回到顶部
全文检索
elasticsearch
bigdesk elasticsearch管理插件
回到顶部
nosql
mapdb 支持亿级别map, list, 支持事务. 可考虑做为缓存使用
C
- 初二上学期难记单词二
dcj3sjt126com
englishword
dangerous 危险的
panda 熊猫
lion 狮子
elephant 象
monkey 猴子
tiger 老虎
deer 鹿
snake 蛇
rabbit 兔子
duck 鸭
horse 马
forest 森林
fall 跌倒;落下
climb 爬;攀登
finish 完成;结束
cinema 电影院;电影
seafood 海鲜;海产食品
bank 银行
- 8、mysql外键(FOREIGN KEY)的简单使用
dcj3sjt126com
mysql
一、基本概念
1、MySQL中“键”和“索引”的定义相同,所以外键和主键一样也是索引的一种。不同的是MySQL会自动为所有表的主键进行索引,但是外键字段必须由用户进行明确的索引。用于外键关系的字段必须在所有的参照表中进行明确地索引,InnoDB不能自动地创建索引。
2、外键可以是一对一的,一个表的记录只能与另一个表的一条记录连接,或者是一对多的,一个表的记录与另一个表的多条记录连接。
3、如
- java循环标签 Foreach
shuizhaosi888
标签java循环foreach
1. 简单的for循环
public static void main(String[] args) {
for (int i = 1, y = i + 10; i < 5 && y < 12; i++, y = i * 2) {
System.err.println("i=" + i + " y="
- Spring Security(05)——异常信息本地化
234390216
exceptionSpring Security异常信息本地化
异常信息本地化
Spring Security支持将展现给终端用户看的异常信息本地化,这些信息包括认证失败、访问被拒绝等。而对于展现给开发者看的异常信息和日志信息(如配置错误)则是不能够进行本地化的,它们是以英文硬编码在Spring Security的代码中的。在Spring-Security-core-x
- DUBBO架构服务端告警Failed to send message Response
javamingtingzhao
架构DUBBO
废话不多说,警告日志如下,不知道有哪位遇到过,此异常在服务端抛出(服务器启动第一次运行会有这个警告),后续运行没问题,找了好久真心不知道哪里错了。
WARN 2015-07-18 22:31:15,272 com.alibaba.dubbo.remoting.transport.dispatcher.ChannelEventRunnable.run(84)
- JS中Date对象中几个用法
leeqq
JavaScriptDate最后一天
近来工作中遇到这样的两个需求
1. 给个Date对象,找出该时间所在月的第一天和最后一天
2. 给个Date对象,找出该时间所在周的第一天和最后一天
需求1中的找月第一天很简单,我记得api中有setDate方法可以使用
使用setDate方法前,先看看getDate
var date = new Date();
console.log(date);
// Sat J
- MFC中使用ado技术操作数据库
你不认识的休道人
sqlmfc
1.在stdafx.h中导入ado动态链接库
#import"C:\Program Files\Common Files\System\ado\msado15.dll" no_namespace rename("EOF","end")2.在CTestApp文件的InitInstance()函数中domodal之前写::CoIniti
- Android Studio加速
rensanning
android studio
Android Studio慢、吃内存!启动时后会立即通过Gradle来sync & build工程。
(1)设置Android Studio
a) 禁用插件
File -> Settings... Plugins 去掉一些没有用的插件。
比如:Git Integration、GitHub、Google Cloud Testing、Google Cloud
- 各数据库的批量Update操作
tomcat_oracle
javaoraclesqlmysqlsqlite
MyBatis的update元素的用法与insert元素基本相同,因此本篇不打算重复了。本篇仅记录批量update操作的
sql语句,懂得SQL语句,那么MyBatis部分的操作就简单了。 注意:下列批量更新语句都是作为一个事务整体执行,要不全部成功,要不全部回滚。
MSSQL的SQL语句
WITH R AS(
SELECT 'John' as name, 18 as
- html禁止清除input文本输入缓存
xp9802
input
多数浏览器默认会缓存input的值,只有使用ctl+F5强制刷新的才可以清除缓存记录。如果不想让浏览器缓存input的值,有2种方法:
方法一: 在不想使用缓存的input中添加 autocomplete="off"; eg: <input type="text" autocomplete="off" name