Centos7搭建ossec-hids2.8.3入侵检测系统
1、故事背景,项目要求三级等保,大家懂的。
2、操作系统版本
[root@ossec01 yum.repos.d]# cat /etc/redhat-release
CentOS Linux release 7.6.1810 (Core)
3、安装wget
安装wget(如果有外网的话可以直接使用centos7安装后自带的yum源安装wget,没有外网使用本地安装镜像配置个本地源安装)
yum -y install wget
获取国内阿里源
wget http://mirrors.aliyun.com/repo/Centos-7.repo
在该目录会产生下面这个文件:
/etc/yum.repos.d/Centos-7.repo
将原有的那些yum源备份掉:
mkdir /etc/yum.repos.d/backup
mv *.repo backup/
备份后如下:
[root@ossec01 yum.repos.d]# ll
total 12
drwxr-xr-x 2 root root 187 Aug 17 18:23 backup
-rw-r--r-- 1 root root 2523 Jun 16 2018 Centos-7.repo
创建yum源缓存
yum clean all
yum makecache
4、关闭selinux
vi /etc/selinux/config
SELINUX=disabled
然后重启:
reboot
5、防火墙
关于防火墙,我们先开着
systemctl restart firewalld
systemctl enable firewalld
6、安装配置mysql5.7
wget http://repo.mysql.com/mysql57-community-release-el7.rpm
该语句会在当前目录下载一个mysql的rpm包,安装即可:
[root@ossec01 soft]# ll
total 28
-rw-r--r-- 1 root root 25680 Apr 27 2017 mysql57-community-release-el7.rpm
安装mysql yum源:
[root@ossec01 soft]# rpm -ivh mysql57-community-release-el7.rpm
warning: mysql57-community-release-el7.rpm: Header V3 DSA/SHA1 Signature, key ID 5072e1f5: NOKEY
Preparing... ################################# [100%]
Updating / installing...
1:mysql57-community-release-el7-11 ################################# [100%]
安装yum源完成后会在/etc/yum.repos.d目录下产生如下两个repo源文件:
[root@ossec01 yum.repos.d]# ll mysql*
-rw-r--r-- 1 root root 1838 Apr 27 2017 mysql-community.repo
-rw-r--r-- 1 root root 1885 Apr 27 2017 mysql-community-source.repo
[root@ossec01 yum.repos.d]# pwd
/etc/yum.repos.d
重新缓存新mysql源(原阿里源和mysql源同时用,只有mysql源可能报缺少依赖包):
yum clean all
yum makecache
安装mysql及lib库
yum -y install -y mysql-server mariadb-server mariadb mariadb-devel
这个源安装的狂慢。
启动mysql
systemctl start mysqld
systemctl status mysqld
systemctl enable mysqld
netstat -ntlp
[root@ossec01 yum.repos.d]# netstat -ntlp
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 6729/sshd
tcp 0 0 127.0.0.1:25 0.0.0.0:* LISTEN 6955/master
tcp6 0 0 :::3306 :::* LISTEN 22059/mysqld
tcp6 0 0 :::22 :::* LISTEN 6729/sshd
tcp6 0 0 ::1:25 :::* LISTEN 6955/master
获取mysql密码:
[root@ossec01 yum.repos.d]# grep 'temporary password' /var/log/mysqld.log
2019-08-17T16:14:26.656418Z 1 [Note] A temporary password is generated for root@localhost: rs.flfh<)5vQ
7、配置mysql
设置mysql密码策略
mysql -uroot -p
设置密码策略为low
mysql> set global validate_password_policy=0;
Query OK, 0 rows affected (0.00 sec)
设置密码长度
mysql> set global validate_password_length=1;
Query OK, 0 rows affected (0.00 sec)
修改密码
mysql> ALTER USER 'root'@'localhost' IDENTIFIED BY 'root#123';
Query OK, 0 rows affected (0.00 sec)
授权其他机器登陆
mysql> grant all privileges on *.* to 'root'@'%' identified by "root#123" with grant option ;
Query OK, 0 rows affected, 1 warning (0.00 sec)
刷新权限
mysql> flush privileges ;
Query OK, 0 rows affected (0.00 sec)
8、创建ossec相关数据库
创建ossec相关数据库
创建ossec数据库
mysql> create database ossec;
Query OK, 1 row affected (0.00 sec)
创建ossec用户并授权
mysql> grant INSERT,SELECT,UPDATE,CREATE,DELETE,EXECUTE on ossec.* to ossec@localhost identified by 'ossec';
Query OK, 0 rows affected, 1 warning (0.00 sec)
刷新权限
mysql> flush privileges ;
Query OK, 0 rows affected (0.00 sec)
9、安装相关依赖包
首先我们安装需要用到的关联库和软件,
由于我们最终是需要把日志导入到MySQL中进行分析,
以及需要通过web程序对报警结果进行展示,
同时需要把本机当做SMTP,所以需要在本机安装MySQL、Apache和sendmail服务。
在当前的终端中执行如下命令
yum install wget gcc make httpd php php-mysql sendmail
10、启动httpd
启动http并设置随机自启动
systemctl start httpd
systemctl status httpd
systemctl enable httpd
11、服务端安装ossec-hids
[root@ossec01 soft]# ll ossec*
-rw-r--r-- 1 root root 1642095 Aug 16 14:53 ossec-hids-2.8.3.tar.gz
[root@ossec01 soft]# pwd
/soft
为了使OSSEC支持MySQL,需要在安装前执行make setdb命令,如下
tar -zxvf ossec-hids-2.8.3.tar.gz
cd ossec-hids-2.8.3
cd src
[root@ossec01 src]# pwd
/soft/ossec-hids-2.8.3/src
[root@ossec01 src]# make setdb
Error: PostgreSQL client libraries not installed.
Info: Compiled with MySQL support.
[root@ossec01 src]#
看到如下的信息说明可以正常支持MySQL:
Info: Compiled with MySQL support.
安装服务端
cd ..
[root@ossec01 ossec-hids-2.8.3]# pwd
/soft/ossec-hids-2.8.3
./install.sh
会要输入一些信息,
选择语言:cn
安装类型:server安装路径:默认(/var/ossec)
是否email告警:y
email地址:[email protected]
smtp服务器ip或主机名:smtp.qq.com
您希望运行系统完整性检测模块吗:y
您希望运行 rootkit检测吗:y
您希望开启联动(active response)功能吗:y
您希望开启防火墙联动(firewall-drop)功能吗:y
联动功能默认的白名单是:可以添加服务端,也可以n
您希望接收远程机器syslog吗:y
...
cp -pr agent-auth ossec-authd ../../bin
make[1]: Leaving directory `/soft/ossec-hids-2.8.3/src/os_auth'
useradd: warning: the home directory already exists.
Not copying any file from skel directory into it.
useradd: warning: the home directory already exists.
Not copying any file from skel directory into it.
useradd: warning: the home directory already exists.
Not copying any file from skel directory into it.
- 系统类型是 Redhat Linux.
- 修改启动脚本使 OSSEC HIDS 在系统启动时自动运行
- 已正确完成系统配置.
- 要启动 OSSEC HIDS:
/var/ossec/bin/ossec-control start
- 要停止 OSSEC HIDS:
/var/ossec/bin/ossec-control stop
- 要查看或修改系统配置,请编辑 /var/ossec/etc/ossec.conf
感谢使用 OSSEC HIDS.
如果您有任何疑问,建议或您找到任何bug,
请通过 [email protected] 或邮件列表 [email protected] 联系我们.
( http://www.ossec.net/en/mailing_lists.html ).
您可以在 http://www.ossec.net 获得更多信息
--- 请按 ENTER 结束安装 (下面可能有更多信息). ---
- 为使代理能够联接服务器端, 您需要将每个代理添加到服务器.
允许'manage_agents'来添加活删除代理:
/var/ossec/bin/manage_agents
详细信息请参考:
http://www.ossec.net/en/manual.html#ma
[root@ossec01 ossec-hids-2.8.3]#
看到上面的信息,表示安装成功
12、配置ossec数据库支持
为了配置服务端,使其工作正常,执行下面命令启用数据库支持
/var/ossec/bin/ossec-control enable database
13、导入ossec相关数据结构到mysql数据库中
导入mysql表结构到mysql库中
mysql -uossec -possec ossec < src/os_dbd/mysql.schema
检查导入:
mysql> use ossec ;
mysql> show tables ;
+----------------------------+
| Tables_in_ossec |
+----------------------------+
| agent |
| alert |
| category |
| data |
| location |
| server |
| signature |
| signature_category_mapping |
+----------------------------+
8 rows in set (0.00 sec)
可以看到导入这些对象,这些表都是空的,未导入之前这个库是空的,没有这些表。
14、修改配置文件权限
修改配置文件的权限,否则启动服务可能会失败
chmod u+w /var/ossec/etc/ossec.conf
15、修改配置文件,添加数据库连接信息
添加mysql数据库连接信息,加在该文件最后,节点之前:
vi /var/ossec/etc/ossec.conf
16、修改配置文件,添加客户端允许连接ip地址
由于服务端安装过程中设置了支持接受远程机器的syslog,所以需要对ossec.conf文件中的 syslog部分进行配置,修改ossec.conf文件,将需要收集的网段全添加进去。
17、启动ossec服务
[root@ossec01 ossec-hids-2.8.3]# /var/ossec/bin/ossec-control start
Starting OSSEC HIDS v2.8.3 (by Trend Micro Inc.)...
Started ossec-dbd...
Started ossec-maild...
Started ossec-execd...
Started ossec-analysisd...
Started ossec-logcollector...
Started ossec-remoted...
Started ossec-syscheckd...
Started ossec-monitord...
Completed.
[root@ossec01 ossec-hids-2.8.3]# /var/ossec/bin/ossec-control status
ossec-monitord is running...
ossec-logcollector is running...
ossec-remoted is running...
ossec-syscheckd is running...
ossec-analysisd is running...
ossec-maild not running...
ossec-execd is running...
ossec-dbd is running...
所有能看到的服务都应该是运行的状态(因为前面我们没有配置发送邮件,所以mail服务没有运行)
18、添加客户端
此时就可以在服务端添加客户端并导出客户端的key(此时客户端还没装)
[root@ossec01 ossec-hids-2.8.3]# /var/ossec/bin/manage_agents
****************************************
* OSSEC HIDS v2.8.3 Agent manager. *
* The following options are available: *
****************************************
(A)dd an agent (A).
(E)xtract key for an agent (E).
(L)ist already added agents (L).
(R)emove an agent (R).
(Q)uit.
Choose your action: A,E,L,R or Q: a
- Adding a new agent (use '\q' to return to the main menu).
Please provide the following:
* A name for the new agent: 192.168.10.178
* The IP Address of the new agent: 192.168.10.178
* An ID for the new agent[001]:
Agent information:
ID:001
Name:192.168.10.178
IP Address:192.168.10.178
Confirm adding it?(y/n): y
Agent added.
****************************************
* OSSEC HIDS v2.8.3 Agent manager. *
* The following options are available: *
****************************************
(A)dd an agent (A).
(E)xtract key for an agent (E).
(L)ist already added agents (L).
(R)emove an agent (R).
(Q)uit.
Choose your action: A,E,L,R or Q: e
Available agents:
ID: 001, Name: 192.168.10.178, IP: 192.168.10.178
Provide the ID of the agent to extract the key (or '\q' to quit): 001
Agent key information for '001' is:
MDAxIDE5Mi4xNjguMTAuMTc4IDE5Mi4xNjguMTAuMTc4IDg0OTRiM2EzMzVkMjE0ZWU1M2U5OTkzZTU0MGQxNjU1MjgzMTgwNmMxNzA1MDJhZTQ1YzRhZWU5OTFjNTlmN2Q=
** Press ENTER to return to the main menu.
上面导出的那个key要记下来,后面要复制粘贴到客户端使用:
MDAxIDE5Mi4xNjguMTAuMTc4IDE5Mi4xNjguMTAuMTc4IDg0OTRiM2EzMzVkMjE0ZWU1M2U5OTkzZTU0MGQxNjU1MjgzMTgwNmMxNzA1MDJhZTQ1YzRhZWU5OTFjNTlmN2Q=
19、安装客户端
安装客户端192.168.10.178
从服务端将安装包拷贝到客户端
scp ossec-hids-2.8.3.tar.gz 192.168.10.178:/soft/
然后在客户端解压缩
tar -xzvf ossec-hids-2.8.3.tar.gz
cd ossec-hids-2.8.3
20、客户端安装必要的依赖包
客户端安装必要的依赖包
yum -y install make gcc cmake
21、安装ossec客户端
[root@ossec02 ossec-hids-2.8.3]# ./install.sh
which: no host in (/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/root/bin)
** Para instala??o em português, escolha [br].
** 要使用中文进行安装, 请选择 [cn].
** Fur eine deutsche Installation wohlen Sie [de].
** Για εγκατ?σταση στα Ελληνικ?, επιλ?ξτε [el].
** For installation in English, choose [en].
** Para instalar en Espa?ol , eliga [es].
** Pour une installation en fran?ais, choisissez [fr]
** A Magyar nyelv? telepítéshez válassza [hu].
** Per l'installazione in Italiano, scegli [it].
** 日本語でインストールします.選択して下さい.[jp].
** Voor installatie in het Nederlands, kies [nl].
** Aby instalowa? w j?zyku Polskim, wybierz [pl].
** Для инструкций по установке на русском ,введите [ru].
** Za instalaciju na srpskom, izaberi [sr].
** Türk?e kurulum i?in se?in [tr].
(en/br/cn/de/el/es/fr/hu/it/jp/nl/pl/ru/sr/tr) [en]: cn
which: no host in (/usr/local/sbin:/usr/local/bin:/usr/sbin:/usr/bin:/root/bin)
OSSEC HIDS v2.8.3 安装脚本 - http://www.ossec.net
您将开始 OSSEC HIDS 的安装.
请确认在您的机器上已经正确安装了 C 编译器.
如果您有任何疑问或建议,请给 [email protected] (或 [email protected]) 发邮件.
- 系统类型: Linux ossec02 3.10.0-957.el7.x86_64
- 用户: root
- 主机: ossec02
-- 按 ENTER 继续或 Ctrl-C 退出. --
1- 您希望哪一种安装 (server, agent, local or help)? agent
- 选择了 Agent(client) 类型的安装.
2- 正在初始化安装环境.
- 请选择 OSSEC HIDS 的安装路径 [/var/ossec]:
- OSSEC HIDS 将安装在 /var/ossec .
3- 正在配置 OSSEC HIDS.
3.1- 请输入 OSSEC HIDS 服务器的IP地址或主机名: 192.168.10.177
- 添加服务器IP 192.168.10.177
3.2- 您希望运行系统完整性检测模块吗? (y/n) [y]:
- 系统完整性检测模块将被部署.
3.3- 您希望运行 rootkit检测吗? (y/n) [y]:
- rootkit检测将被部署.
3.4 - 您希望开启联动(active response)功能吗? (y/n) [y]:
3.5- 设置配置文件以分析一下日志:
-- /var/log/messages
-- /var/log/secure
-- /var/log/maillog
-如果你希望监控其他文件, 只需要在配置文件ossec.conf中
添加新的一项.
任何关于配置的疑问您都可以在 http://www.ossec.net 找到答案.
--- 按 ENTER 以继续 ---
...(一堆编译安装的内容省略...)
- 系统类型是 Redhat Linux.
- 修改启动脚本使 OSSEC HIDS 在系统启动时自动运行
- 已正确完成系统配置.
- 要启动 OSSEC HIDS:
/var/ossec/bin/ossec-control start
- 要停止 OSSEC HIDS:
/var/ossec/bin/ossec-control stop
- 要查看或修改系统配置,请编辑 /var/ossec/etc/ossec.conf
感谢使用 OSSEC HIDS.
如果您有任何疑问,建议或您找到任何bug,
请通过 [email protected] 或邮件列表 [email protected] 联系我们.
( http://www.ossec.net/en/mailing_lists.html ).
您可以在 http://www.ossec.net 获得更多信息
--- 请按 ENTER 结束安装 (下面可能有更多信息). ---
- 您必须首先将该代理添加到服务器端以使他们能够相互通信.
这样做了以后,您可以运行'manage_agents'工具导入
服务器端产生的认证密匙.
/var/ossec/bin/manage_agents
详细信息请参考:
http://www.ossec.net/en/manual.html#ma
[root@ossec02 ossec-hids-2.8.3]#
看到上面的信息,说明agent安装成功。
22、在客户端导入key
[root@ossec02 bin]# /var/ossec/bin/manage_agents
****************************************
* OSSEC HIDS v2.8.3 Agent manager. *
* The following options are available: *
****************************************
(I)mport key from the server (I).
(Q)uit.
Choose your action: I or Q: i
* Provide the Key generated by the server.
* The best approach is to cut and paste it.
*** OBS: Do not include spaces or new lines.
Paste it here (or '\q' to quit): MDAxIDE5Mi4xNjguMTAuMTc4IDE5Mi4xNjguMTAuMTc4IDg0OTRiM2EzMzVkMjE0ZWU1M2U5OTkzZTU0MGQxNjU1MjgzMTgwNmMxNzA1MDJhZTQ1YzRhZWU5OTFjNTlmN2Q=
Agent information:
ID:001
Name:192.168.10.178
IP Address:192.168.10.178
Confirm adding it?(y/n): y
Added.
** Press ENTER to return to the main menu.
23、启动客户端
[root@ossec02 bin]# /var/ossec/bin/ossec-control start
Starting OSSEC HIDS v2.8.3 (by Trend Micro Inc.)...
Started ossec-execd...
2019/08/18 01:23:11 ossec-agentd: INFO: Using notify time: 600 and max time to reconnect: 1800
Started ossec-agentd...
Started ossec-logcollector...
Started ossec-syscheckd...
Completed.
[root@ossec02 bin]# /var/ossec/bin/ossec-control status
ossec-logcollector is running...
ossec-syscheckd is running...
ossec-agentd is running...
ossec-execd is running...
24、去服务端检查客户端是否已经连接上
[root@ossec01 bin]# /var/ossec/bin/agent_control -l
OSSEC HIDS agent_control. List of available agents:
ID: 000, Name: ossec01 (server), IP: 127.0.0.1, Active/Local
ID: 001, Name: 192.168.10.178, IP: 192.168.10.178, Never connected
List of agentless devices:
[root@ossec01 bin]#
发现是192.168.10.178是Never connected的状态。
去客户端查看日志:
view /var/ossec/logs/ossec.log
2019/08/18 01:24:42 ossec-agentd(4101): WARN: Waiting for server reply (not started). Tried: '192.168.10.177'.
2019/08/18 01:25:20 ossec-agentd: INFO: Trying to connect to server (192.168.10.177:1514).
2019/08/18 01:25:20 ossec-agentd: INFO: Using IPv4 for: 192.168.10.177 .
2019/08/18 01:25:30 ossec-agentd(1218): ERROR: Unable to send message to server.
2019/08/18 01:25:42 ossec-agentd(1218): ERROR: Unable to send message to server.
发现是服务端没有响应,客户端连接的是服务端的1514端口。我们去服务端查看下1514端口是否正常。
[root@ossec01 bin]# netstat -ntpl
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
tcp 0 0 0.0.0.0:22 0.0.0.0:* LISTEN 6729/sshd
tcp 0 0 127.0.0.1:25 0.0.0.0:* LISTEN 6955/master
tcp6 0 0 :::3306 :::* LISTEN 22059/mysqld
tcp6 0 0 :::80 :::* LISTEN 22305/httpd
tcp6 0 0 :::22 :::* LISTEN 6729/sshd
tcp6 0 0 ::1:25 :::* LISTEN 6955/master
[root@ossec01 bin]# netstat -nupl
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
udp 0 0 0.0.0.0:68 0.0.0.0:* 6549/dhclient
udp 0 0 0.0.0.0:514 0.0.0.0:* 24225/ossec-remoted
[root@ossec01 bin]#
很遗憾,服务端1514端口应该是udp协议,经过查询发现不管是tcp还是udp的端口都没有1514.
[root@ossec01 init.d]# /etc/init.d/ossec start
Starting OSSEC: [ OK ]
然后重启下ossec服务
/var/ossec/bin/ossec-control stop
/var/ossec/bin/ossec-control start
在查看下端口1514:
[root@ossec01 init.d]# netstat -nulp
Active Internet connections (only servers)
Proto Recv-Q Send-Q Local Address Foreign Address State PID/Program name
udp 0 0 0.0.0.0:1514 0.0.0.0:* 25218/ossec-remoted
udp 0 0 0.0.0.0:68 0.0.0.0:* 6549/dhclient
udp 0 0 0.0.0.0:514 0.0.0.0:* 25217/ossec-remoted
发现已经有了。
24、验证服务端1514端口是否通
我们在本地windows下测试一下是否能连该端口
测试tcp端口(在客户端测试):
nc -zv 192.168.10.177 80
[root@ossec02 bin]# nc -zv 192.168.10.177 80
Ncat: Version 7.50 ( https://nmap.org/ncat )
Ncat: Connected to 192.168.10.177:80.
Ncat: 0 bytes sent, 0 bytes received in 0.01 seconds.
[root@ossec02 bin]#
nc -zvu 192.168.10.177 1514
[root@ossec02 bin]# nc -zvu 192.168.10.177 1514
Ncat: Version 7.50 ( https://nmap.org/ncat )
Ncat: Connected to 192.168.10.177:1514.
Ncat: UDP packet sent successfully
Ncat: 1 bytes sent, 0 bytes received in 2.01 seconds.
[root@ossec02 bin]#
看到上面的信息就表示端口是通的。因为1514端口是使用的udp,所以需要使用下面的一个语句测试。
25、如果无法连接,把防火墙端口开一下。(我们上面防火墙是开着的,如果直接把防火墙关了就不需要了)
发现无法连接,这个是因为防火墙没开此端口,我们把需要的端口都开一下:
firewall-cmd --zone=public --add-port=80/tcp --permanent
firewall-cmd --zone=public --add-port=3306/tcp --permanent
firewall-cmd --zone=public --add-port=1514/udp --permanent
firewall-cmd --zone=public --add-port=514/udp --permanent
firewall-cmd --zone=public --add-port=514/tcp --permanent
firewall-cmd --zone=public --add-port=1514/tcp --permanent
重启防火墙:
[root@ossec01 init.d]# systemctl restart firewalld
26、内核参数提前配好
##########Shared Memory###############
kernel.shmmax=3221225472
kernel.shmmni=4096
kernel.shmall=786432
##########Semaphore Arrays############
kernel.sem=6144 50331648 4096 8192
##########open file###################
fs.file-max=6815744
##########aio#########################
fs.aio-max-nr=3145728
##########network#####################
net.ipv4.icmp_echo_ignore_broadcasts=1
net.ipv4.icmp_ignore_bogus_error_responses=1
net.ipv4.conf.all.rp_filter=1
net.ipv4.conf.default.rp_filter=1
net.ipv4.tcp_syncookies=1
net.ipv4.tcp_fin_timeout=30
net.ipv4.tcp_keepalive_time=1500
net.ipv4.tcp_keepalive_probes=5
net.ipv4.tcp_keepalive_intvl=60
net.ipv4.tcp_window_scaling=1
net.core.rmem_default=262144
net.core.wmem_default=262144
net.core.rmem_max=4194304
net.core.wmem_max=4194304
net.ipv4.tcp_rmem=8192 262144 4194304
net.ipv4.tcp_wmem=8192 262144 4194304
net.ipv4.ip_local_port_range=9000 65500
##########CORE######################
kernel.core_uses_pid=1
##########Message Queues##############
kernel.msgmax=655360
kernel.msgmni=4096
kernel.msgmnb=1024000
##########vm config###################
vm.min_free_kbytes=1048576
vm.vfs_cache_pressure=200
vm.swappiness=10
27、再次在服务端验证状态
再次在服务端查询客户端连接状态,就可以看到客户端是active的状态了。
如果还有问题,可以查询日志:
服务端:
/var/ossec/logs/ossec.log
客户端:
/var/ossec/logs/ossec.log
一般有问题的话日志里面就会报的比较详细。
28、图形界面安装
服务端和客户端都安装好了,并且也连接上了,下一步就需要有个界面管理我们的服务端和客户端。
安装文件:
[root@ossec01 soft]# ll *ossec-wui*
-rw-r--r-- 1 root root 397357 Aug 19 18:27 ossec-wui.tar.gz
解压解包:
tar -xzvf ossec-wui.tar.gz
cd ossec-wui
[root@ossec01 ossec-wui]# ll
total 68
-rwxr-xr-x 1 root root 317 Aug 16 16:52 CONTRIB
drwxr-xr-x 3 root root 50 Aug 16 16:52 css
-rw-r--r-- 1 root root 218 Aug 16 16:52 htaccess_def.txt
drwxr-xr-x 2 root root 168 Aug 16 16:52 img
-rwxr-xr-x 1 root root 5177 Aug 16 16:52 index.php
drwxr-xr-x 2 root root 107 Aug 16 16:52 js
drwxr-xr-x 3 root root 273 Aug 16 16:52 lib
-rw-r--r-- 1 root root 35745 Aug 16 16:52 LICENSE
-rw-r--r-- 1 root root 462 Aug 16 16:52 ossec_conf.php
-rw-r--r-- 1 root root 2106 Aug 16 16:52 README
-rw-r--r-- 1 root root 923 Aug 16 16:52 README.search
-rwxr-xr-x 1 root root 2471 Aug 16 16:52 setup.sh
drwxr-xr-x 2 root root 175 Aug 16 16:52 site
29、创建目录
mkdir -p /opt/ossec
拷贝解压目录下的所有文件到目标/opt/ossec目录下
cp -R /soft/ossec-wui/* /opt/ossec/
[root@ossec01 ossec]# pwd
/opt/ossec
[root@ossec01 ossec]# ll
total 68
-rwxr-xr-x 1 root root 317 Aug 19 18:30 CONTRIB
drwxr-xr-x 3 root root 50 Aug 19 18:30 css
-rw-r--r-- 1 root root 218 Aug 19 18:30 htaccess_def.txt
drwxr-xr-x 2 root root 168 Aug 19 18:30 img
-rwxr-xr-x 1 root root 5177 Aug 19 18:30 index.php
drwxr-xr-x 2 root root 107 Aug 19 18:30 js
drwxr-xr-x 3 root root 273 Aug 19 18:30 lib
-rw-r--r-- 1 root root 35745 Aug 19 18:30 LICENSE
-rw-r--r-- 1 root root 462 Aug 19 18:30 ossec_conf.php
-rw-r--r-- 1 root root 2106 Aug 19 18:30 README
-rw-r--r-- 1 root root 923 Aug 19 18:30 README.search
-rwxr-xr-x 1 root root 2471 Aug 19 18:30 setup.sh
drwxr-xr-x 2 root root 175 Aug 19 18:30 site
30、进行安装ossec-wui
cd /opt/ossec/
./setup.sh
[root@ossec01 ossec]# ./setup.sh
Setting up ossec ui...
Username: ossec
New password:
Re-type new password:
Adding password for user ossec
Enter your web server user name (e.g. apache, www, nobody, www-data, ...)
apache
You must restart your web server after this setup is done.
Setup completed successfully.
[root@ossec01 ossec]#
上面输入的用户名和密码需要记住,这个就是后面登陆web界面的凭证。
31、配置http
对ossec.config进行配置,需要添加虚拟目录
[root@ossec01 opt]# vi /etc/httpd/conf.d/ossce.conf
Alias /ossec "/opt/ossec/"
Options Indexes FollowSymLinks
AllowOverride None
Order deny,allow
Deny from all
Allow from 192.168.0.0/16
# Order deny,allow
# Deny from all
# Allow from 127.0.0.1
AuthName "OSSEC AUTH"
AuthType Basic
AuthUserFile /opt/ossec/.htpasswd
Require valid-user
32、赋权
对ossec-wui目录的权限授权给apache用户
cd /opt
chown -R apache:apache ossec
33、重启httpd服务
重新启动httpd服务
systemctl restart httpd
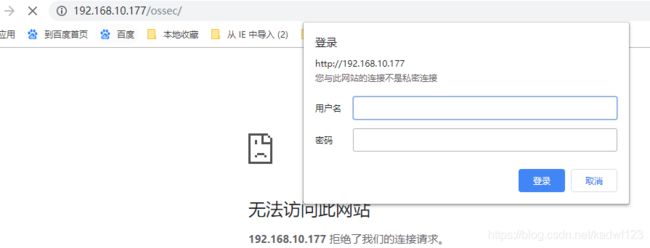
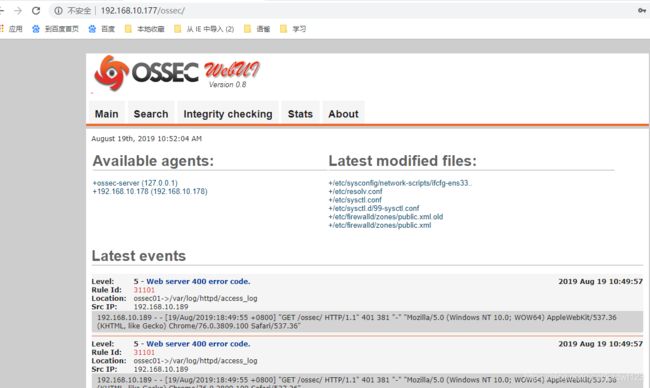
34、通过web浏览器访问
然后就可以通过以下地址访问:
http://192.168.10.177/ossec/
访问界面如下:
输入刚才的输入的用户名ossec和对应的密码。