VulnHub—DC-5
01 环境搭建
- 靶机环境下载:https://www.vulnhub.com/entry/dc-5,314/
- 题目信息如下,只有一个flag
Description
DC-5 is another purposely built vulnerable lab with the intent of gaining experience in the world of penetration testing.
The plan was for DC-5 to kick it up a notch, so this might not be great for beginners, but should be ok for people with intermediate or better experience. Time will tell (as will feedback).
As far as I am aware, there is only one exploitable entry point to get in (there is no SSH either). This particular entry point may be quite hard to identify, but it is there. You need to look for something a little out of the ordinary (something that changes with a refresh of a page). This will hopefully provide some kind of idea as to what the vulnerability might involve.
And just for the record, there is no phpmailer exploit involved. :-)
The ultimate goal of this challenge is to get root and to read the one and only flag.
Linux skills and familiarity with the Linux command line are a must, as is some experience with basic penetration testing tools.
For beginners, Google can be of great assistance, but you can always tweet me at @DCAU7 for assistance to get you going again. But take note: I won't give you the answer, instead, I'll give you an idea about how to move forward.
But if you're really, really stuck, you can watch this video which shows the first step.
Technical Information
DC-5 is a VirtualBox VM built on Debian 64 bit, but there shouldn't be any issues running it on most PCs.
I have tested this on VMWare Player, but if there are any issues running this VM in VMware, have a read through of this.
It is currently configured for Bridged Networking, however, this can be changed to suit your requirements. Networking is configured for DHCP.
Installation is simple - download it, unzip it, and then import it into VirtualBox or VMWare and away you go.
Important
While there should be no problems using this VM, by downloading it, you accept full responsibility for any unintentional damage that this VM may cause.
In saying that, there shouldn't be any problems, but I feel the need to throw this out there just in case.
Contact
I'm also very interested in hearing how people go about solving these challenges, so if you're up for writing a walkthrough, please do so and send me a link, or alternatively, follow me on Twitter, and DM me (you can unfollow after you've DM'd me if you'd prefer).
I can be contacted via Twitter - @DCAU7
02 信息收集
将靶机环境恢复到virtualbox之后,开始第一步信息收集工作。
发现靶机
查看攻击机的ip为192.168.56.1(环境恢复时采用Host-Only Adapter)
![]()
使用nmap扫描网段内的ip地址
nmap -sP 192.168.56.1/24
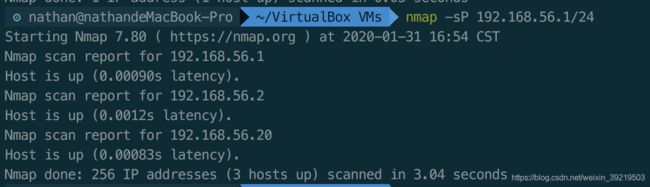 扫描发现的
扫描发现的192.168.56.20就是目标靶机的ip地址。
端口扫描
使用nmap对目标靶机开放的端口进行扫描
nmap -Pn -n -sV 192.168.56.20
web
访问web页面,发现有个contract页面,可以提交些信息。
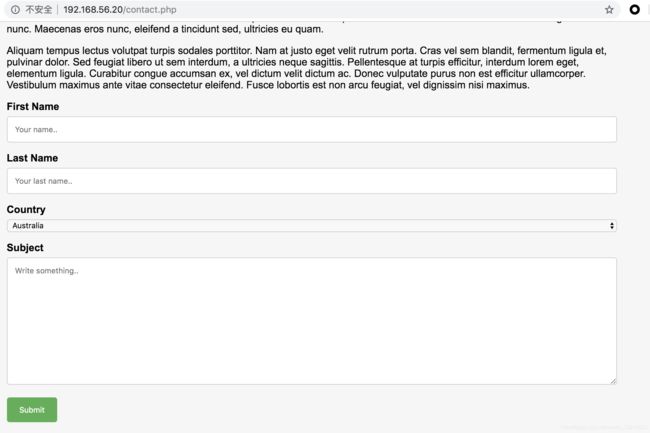
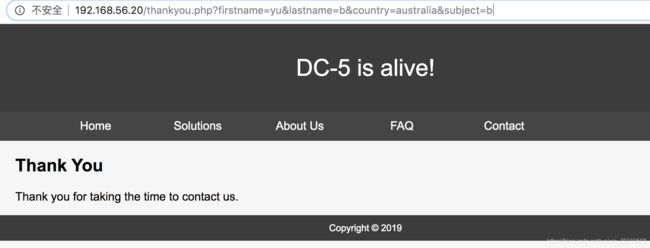
点击提交后进入thankyou.php页面。
03 Get Shell
LFI
提交后的页面url中带有很多参数,尝试用wfuzz对页面对参数进行fuzz。
wfuzz -c -z file,/usr/local/share/wfuzz/wordlist/general/common.txt -z file,/usr/local/share/wfuzz/wordlist/Injections/All_attack.txt --hl 42 --hw 66 --hh 852 http://192.168.56.19/thankyou.php\?FUZZ\=FUZ2Z
发现在参数为file=../../../../../../../../../../../../etc/hosts时,返回页面的长度有变化。
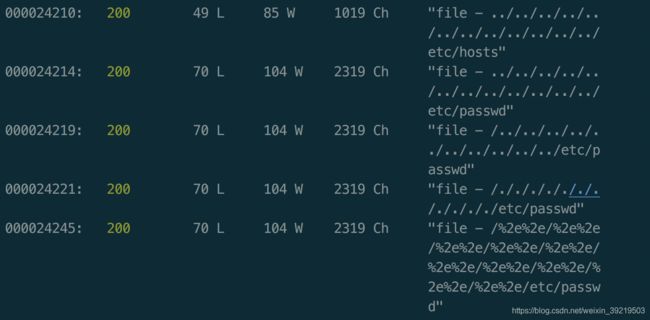
访问后发现返回了文件内容,该页面有个本地文件包含漏洞。

尝试包含远程文件,失败。
Shell
本地文件包含漏洞需要找到一个可以被利用的文件,当前无法上传文件,只能在本地找可以被利用的文件。
web采用nginx架构,尝试寻找nginx的日志文件,里面会记录请求的信息。通过请求信息来注入恶意代码。
最终发现nginx的日志文件在/var/log/nginx/目录下,有access.log和error.log。
访问http://192.168.56.19/thankyou.php?file=/var/log/nginx/access.log发现有xss注入。由于用wfuzz的fuzz结果。

重新恢复环境,重新提交请求http://192.168.56.20/thankyou.php?注入到日志文件中(使用bp发送),然后访问/var/log/nginx/access.log即可获得反弹 shell。

04 提权
查询suid程序,发现一个/bin/screen-4.5.0
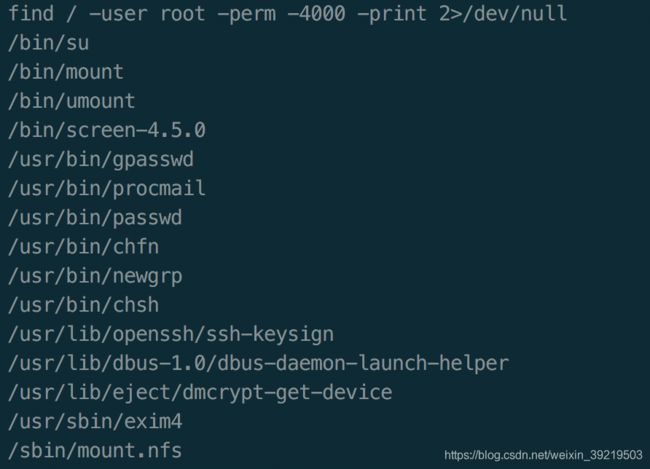
搜索发现,该程序存在一个本地提权漏洞。

下载poc上传到靶机后执行,发现无法编译成功

查看poc,将代码在本地编译后上传到靶机执行。
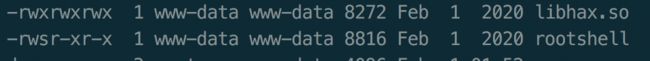

获得root权限,最终获得flag
