web
这里什么都没有的签到
网页名是LFI,LFI是本地包含漏洞的缩写,先用伪协议看看index.php的源代码
php://filter/read=convert.base64-encode/resource=index.php
base64解密后得到
LFI
�����没�~
佳瓦的秘密
查看源代码,发现登陆是用js实现的。
js一看就是混淆过的,解混淆得
_f = function () {
var f = document.createElement("form");
document.getElementById('login').appendChild(f);
f.name = "login";
return f
}();
_uname = function () {
var uname = document.createElement("input");
uname.type = "text";
uname.id = "uname";
uname.value = 'Input Username';
uname.style.margin = "0px 0px 0px 60px";
_f.appendChild(uname);
uname.onfocus = function () {
if (this.value == 'Input Username') this.value = ''
};
uname.onblur = function () {
if (this.value == '') this.value = 'Input Username'
};
return uname
}();
_br = function () {
var br = document.createElement("br");
_f.appendChild(br);
br = document.createElement("br");
_f.appendChild(br);
return br
}();
_upass = function () {
var upass = document.createElement("input");
upass.type = "password";
upass.id = "upass";
upass.value = 'Input Password';
upass.style.margin = "0px 0px 0px 60px";
_f.appendChild(upass);
upass.onfocus = function () {
if (this.value == 'Input Password') this.value = ''
};
upass.onblur = function () {
if (this.value == '') this.value = 'Input Password'
};
return upass
}();
_btn = function () {
var btn = document.createElement("input");
_f.appendChild(btn);
btn.type = "button";
btn.value = "login";
btn.onclick = function () {
uname = document.getElementById('uname').value;
upass = document.getElementById('upass').value;
if (uname == "") alert('Please Input Username!');
else if (upass == "") alert('Please Input Password!');
else {
eval(unescape("var%20strKey1%20%3D%20%22JaVa3C41ptIsAGo0DStAff%22%3B%0Avar%20strKey2%20%3D%20%22CaNUknOWThIsK3y%22%3B%0Avar%20strKey3%20%3D%20String.fromCharCode%2871%2C%2048%2C%20111%2C%20100%2C%2033%29%3B%0Aif%20%28uname%20%3D%3D%20%28strKey3%20+%20%28%28%28strKey1.toLowerCase%28%29%29.substring%280%2C%20strKey1.indexOf%28%220%22%29%29%20+%20strKey2.substring%282%2C%206%29%29.toUpperCase%28%29%29.substring%280%2C%2015%29%29%29%20%7B%0A%20%20%20%20var%20strKey4%20%3D%20%27Java_Scr1pt_Pa4sW0rd_K3y_H3re%27%3B%0A%20%20%20%20if%20%28upass%20%3D%3D%20%28strKey4.substring%28strKey4.indexOf%28%271%27%2C%205%29%2C%20strKey4.length%20-%20strKey4.indexOf%28%27_%27%29%20+%205%29%29%29%20%7B%0A%20%20%20%20%20%20%20%20alert%28%27Login%20Success%21%27%29%3B%0A%20%20%20%20%20%20%20%20document.getElementById%28%27key%27%29.innerHTML%20%3D%20unescape%28%22%253Cfont%2520color%253D%2522%2523000%2522%253Ea2V5X0NoM2NrXy50eHQ%3D%253C/font%253E%22%29%3B%0A%20%20%20%20%7D%20else%20%7B%0A%20%20%20%20%20%20%20%20alert%28%27Password%20Error%21%27%29%3B%0A%20%20%20%20%7D%0A%7D%20else%20%7B%0A%20%20%20%20alert%28%27Login%20Failed%21%27%29%3B%0A%7D"))
}
};
return false
}();
解密下面的代码得
var strKey1 = "JaVa3C41ptIsAGo0DStAff";
var strKey2 = "CaNUknOWThIsK3y";
var strKey3 = String.fromCharCode(71, 48, 111, 100, 33);
if (uname == (strKey3 + (((strKey1.toLowerCase()).substring(0, strKey1.indexOf("0")) + strKey2.substring(2, 6)).toUpperCase()).substring(0, 15))) {
var strKey4 = 'Java_Scr1pt_Pa4sW0rd_K3y_H3re';
if (upass == (strKey4.substring(strKey4.indexOf('1', 5), strKey4.length - strKey4.indexOf('_') + 5))) {
alert('Login Success!');
document.getElementById('key').innerHTML = unescape("%3Cfont%20color%3D%22%23000%22%3Ea2V5X0NoM2NrXy50eHQ=%3C/font%3E");
} else {
alert('Password Error!');
}
} else {
alert('Login Failed!');
}
计算得
uname = G0od!JAVA3C41PTISAGO
upass = 1pt_Pa4sW0rd_K3y_H3re
returntxt = a2V5X0NoM2NrXy50eHQ=
base64解码得key_Ch3ck_.txt,访问后得Ch3ck_Au7h.php,然后用post方式提交uname和upass得到flag。
我叫良辰!不服人肉我
qq号访问空间,用提示的生日进入,得到手机号,用手机号得到flag
逆向
py逆向1
用python官方给的工具EasyPythonDecompiler将pyc文件转化为可读的py文件。
# Embedded file name: unVm.py
import md5
md5s = [40872900234340200352311496849171786925L,
37774871274387226911544626909853297147L,
136364329640288194110852557127415197202L,
197102543045186090881257886713375686009L,
46282790971609926574181364879232245714L,
199788626591470902691740865303843697496L,
139155483798021197733301619201494834453L,
105977393849615850942572250680575701536L,
103383262965894787541607484291344857033L,
193549894376121578282270539756256252317L]
print 'Can you turn me back to python ? ...'
flag = raw_input('well as you wish.. what is the flag: ')
if len(flag) > 50:
print 'nice try'
exit()
if len(flag) % 5 != 0:
print 'nice try'
exit()
for i in range(0, len(flag), 5):
s = flag[i:i + 5]
if int('0x' + md5.new(s).hexdigest(), 16) != md5s[i / 5]:
print 'nice try'
exit()
print 'Congratz now you have the flag'
读程序可以发现flag每五位对应的MD5值转化为十进制后等于md5s里的数据。
用format()将数据还原成32位16进制数
for md5 in md5s:
print('{:32x}'.format(md5))
因为我们已经知道这些md5值是5个字符加密而成的,所以可以使用MD5Crack之类的工具爆破md5值。
杂项
深入敌后
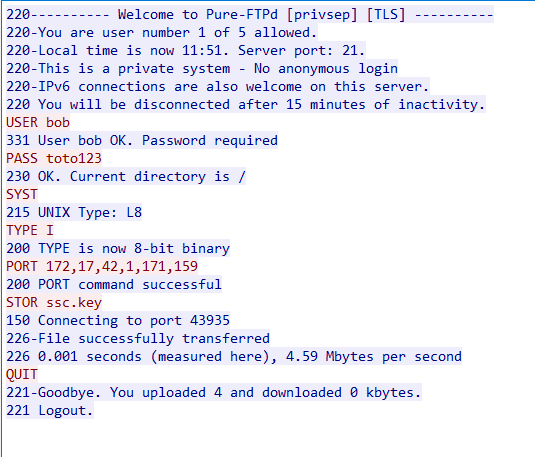
用wireshark打开数据包,分析一下数据包的构成。
先看看smtp(邮件)
关键应该在于这个网址,结合前面分析数据包的构成加上https,我们需要找到ssl证书。
分析ftp协议发现传输了ssc.key
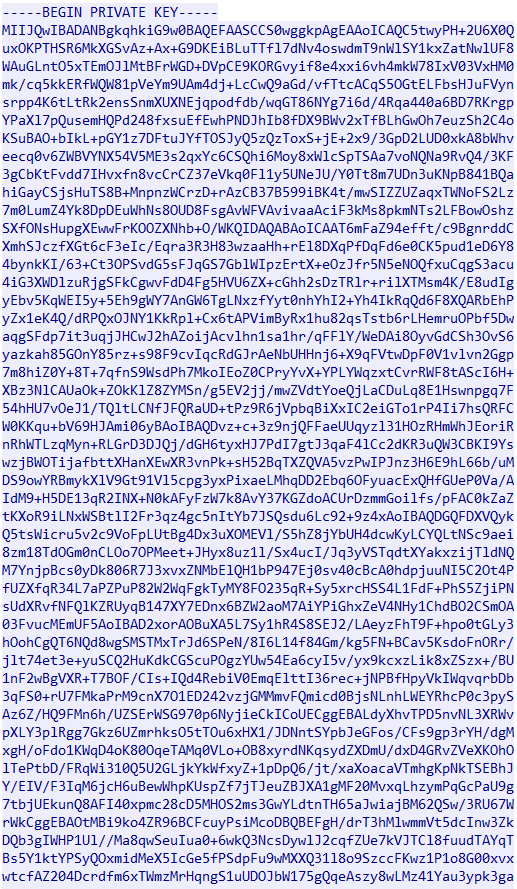
在ftp-date协议获取获取到ssc.key的内容
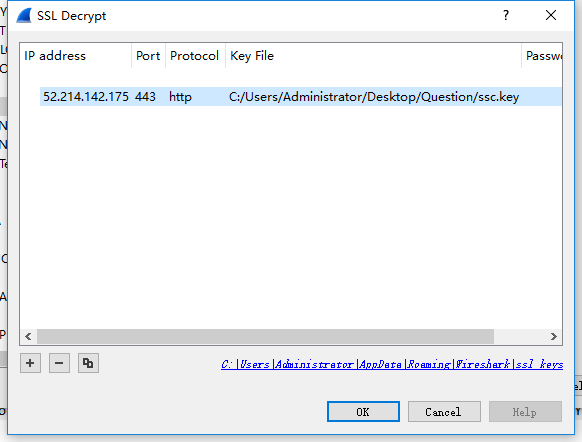
导入ssl证书
在邮件里提到的那个网站上搜索FLAG得到FLAG
隐写
奇怪的图片
图片隐写常见操作来一遍,用binwalk发现里面藏了个rar
用foremost取出这个压缩包,内容如下
第一个文本里面写的是不要太心急,pdf里面写的好像是关于隐写的一些东西。
压缩包里面是一堆二维码,i am useless用二进制编辑器可以看出是一张图片
改成图片后发现是张二维码,扫描后出现了一句话
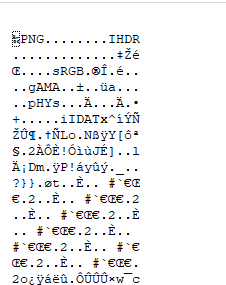
image.png
对这张图片尝试各种图片隐写操作,发现这是色道隐写
这玩意看着就像摩斯电码,将其记录后用工具转换一下就能得到FLAG