Kubernetes部署etcd集群
目录
-
- 一、 k8s概述
-
- 1、k8s是什么
- 2、k8s特性
- 3、k8s群集架构与组件
- 4、k8s核心概念
- 二、自签SSL证书
- 三、k8s三种部署方式
- 四、k8s单节点部署(etcd)
一、 k8s概述
1、k8s是什么
kubernetes是Google在2014年开源的一个容器群集管理系统,kubernetes简称k8s
- k8s用于容器化应用程序的部署,扩展和管理
- k8s提供了容器编排,资源调度,弹性伸缩,部署管理,服务发现等一系列功能
- kubernetes目标是让部署容器化应用简单高效
- 官方网站:http://www.kubernetes.io
2、k8s特性
- 自我修复
在节点故障时重新启动失败的容器,替换和重新部署,保证预期的副本数量;杀死健康检查失败的容器,并且在未准备好之前不会处理客户端请求,确保线上服务不中断。 - 弹性伸缩
使用命令、UI或者基于CPU使用情况自动快速扩容和缩容应用程序实例,保证应用业务高峰并发时的高可用性;业务低峰时回收资源,以最小成本运行服务。 - 自动部署和回滚
K8S采用滚动更新策略更新应用,一次更新 一个Pod,而不是同时删除所有Pod,如果更新过程中出现问题,将回滚更改,确保升级不受影响业务。 - 服务发现和负载均衡
K8S为多个容器提供一个统一访问入口(内部IP地址和一个DNS名称),并且负载均衡关联的所有容器,使得用户无需考虑容器IP问题。 - 机密和配置管理
管理机密数据和应用程序配置,而不需要把敏感数据暴露在镜像里,提高敏感数据安全性。并可以将一些常用的配置存储在K8S中,方便应用程序使用。 - 存储编排
挂载外部存储系统,无论是来自本地存储,公有云(如AWS),还是网络存储(如NFS、GlusterFS、 Ceph)都作为集群资源的一部分使用, 极大提高存储使用灵活性。 - 批处理
提供一次性任务,定时任务;满足批量数据处理和分析的场景
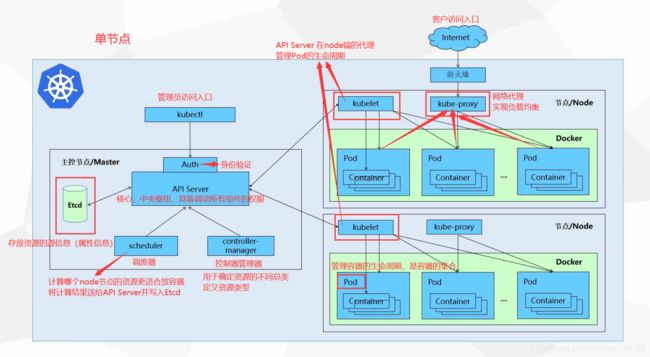
3、k8s群集架构与组件
master 组件
- kube-apiserver
Kubernetes API,集群的统一入口, 各组件协调者,以RESTful API提供接口服务,所有对象资源的增删改查和监听操作都交给APIServer处理后再提交给Etcd存储。 - kube-controller-manager
处理集群中常规后台任务,一个资源对应一个控制器,而ControllerManager就是负责管理这些控制器的。 - kube-scheduler
根据调度算法为新创建的Pod选择一个Node节点,可以任意部署可以部署在同一个节点上,也可以部署在不同的节点上。 - etcd
分布式键值存储系统,用于保存群集状态数据,比如Pod、Service等对象信息
Node组件
- kubelet
kubelet是Master在Node节点上的Agent,管理本机运行容器的生命周期,比如创建容器、Pod挂载数据卷、下载secret、获取容器和节点状态等工作。kubelet将每个Pod转换成一组容器 - kube-proxy
在Node节点上实现Pod网络代理,维护网络规则和四层负载均衡工作 - docker或rocket
容器引擎,运行容器
4、k8s核心概念
Pod
- 最小部署单元
- 一组容器的集合
- 一个Pod中的容器共享网络命名空间
- Pod是短暂的、
Controllers
- ReplicaSet:确保预期的Pod副本数量
- Deployment:无状态应用部署
- StatefulSet:有状态应用部署
- DaemonSet:确保所有Node运行同一个Pod
- Job:一次性任务
- Cronjob:定时任务
Service
- 防止Pod失联
- 定义一组Pod的访问策略
- Lable:标签,附加到某个资源上,用于关联对象、查询和筛选
- Namespaces:命名空间,将对象逻辑上隔离
- Annotations:注释
二、自签SSL证书
| 组件 | 使用的证书 |
|---|---|
| etcd | ca.pem,server.pem,server-key.pem |
| flannel | ca.pem,server.pem,server-key.pem |
| kube-apiserver | ca.pem,server.pem,server-key.pem |
| kubelet | ca.pem,ca-key.pem |
| kube-proxy | ca.pem,kube-proxy.pem,kube-proxy-key.pem |
| kubectl | ca.pem,admin.pem,admin-key.pem |
三、k8s三种部署方式
- minikube
Minikube是一个工具,可以在本地快速运行一个单点的Kubernetes,仅用于尝试Kubernetes或日常开发的用户使用 - kubeadm
Kubeadm也是一个工具,提供kubeadm init 和kubeadm join,用于快速部署Kubernetes群集 - 二进制包
推荐,从官方下载发行版的二进制包,手动部署每个组件,组成Kubernetes群集
生产环境中使用kubeadm和二进制安装的比较多
四、k8s单节点部署(etcd)
实现环境:
Master:192.168.223.10/24 kube-apiserver kube-controller-manager kube-scheduler etcd
Node01:192.168.223.20/24 kubelet kube-proxy docker flannel etcd
Node02:192.168.223.30/24 kubelet kube-proxy docker flannel etcd
master操作:
[root@localhost ~]# mkdir k8s
[root@localhost ~]# cd k8s/
[root@localhost k8s]# ls #从宿主机拖进来
etcd-cert.sh etcd.sh
[root@localhost k8s]# mkdir etcd-cert
[root@localhost k8s]# mv etcd-cert.sh etcd-cert
下载证书制作工具:
[root@localhost k8s]# vim cfssl.sh
curl -L https://pkg.cfssl.org/R1.2/cfssl_linux-amd64 -o /usr/local/bin/cfssl
curl -L https://pkg.cfssl.org/R1.2/cfssljson_linux-amd64 -o /usr/local/bin/cfssljson
curl -L https://pkg.cfssl.org/R1.2/cfssl-certinfo_linux-amd64 -o /usr/local/bin/cfssl-certinfo
chmod +x /usr/local/bin/cfssl /usr/local/bin/cfssljson /usr/local/bin/cfssl-certinfo
[root@localhost k8s]# bash cfssl.sh #下载cfssl官方包
如果有证书制作工具的
[root@localhost k8s]# cd /usr/local/bin/ #宿主机直接拖进此目录
cfssl cfssl-certinfo cfssljson
[root@localhost k8s]# chmod + /usr/local/bin/*
开始制作证书:
cfssl 生成证书工具 cfssljson通过传入json文件生成证书 cfssl-certinfo查看证书信息
[root@localhost k8s]# cd etcd-cert/
cat > ca-config.json <<EOF #定义ca证书
{
"signing": {
"default": {
"expiry": "87600h"
},
"profiles": {
"www": {
"expiry": "87600h",
"usages": [
"signing",
"key encipherment",
"server auth",
"client auth"
]
}
}
}
}
EOF
cat > ca-csr.json <<EOF #实现证书签名
{
"CN": "etcd CA",
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "Beijing",
"ST": "Beijing"
}
]
}
EOF
cfssl gencert -initca ca-csr.json | cfssljson -bare ca - #生产证书,生成ca-key.pem ca.pem
cat > server-csr.json <<EOF #指定etcd三个节点之间的通信验证
{
"CN": "etcd",
"hosts": [
"192.168.241.20",
"192.168.241.4",
"192.168.241.3"
],
"key": {
"algo": "rsa",
"size": 2048
},
"names": [
{
"C": "CN",
"L": "BeiJing",
"ST": "BeiJing"
}
]
}
EOF
cfssl gencert -ca=ca.pem -ca-key=ca-key.pem -config=ca-config.json -profile=www server-csr.json | cfssljson -bare server #生成ETCD证书 server-key.pem server.pem
源码安装etcd:
[root@localhost k8s]# ls
etcd-cert etcd.sh etcd-v3.3.10-linux-amd64.tar.gz
[root@localhost k8s]# tar zxvf etcd-v3.3.10-linux-amd64.tar.gz
etcd-cert etcd.sh etcd-v3.3.10-linux-amd64 etcd-v3.3.10-linux-amd64.tar.gz
[root@localhost k8s]# mkdir /opt/etcd/{
cfg,bin,ssl} -p #配置文件,命令文件,证书
[root@localhost k8s]# cd etcd-v3.3.10-linux-amd64/
[root@localhost etcd-v3.3.10-linux-amd64]# ls
Documentation etcd etcdctl README-etcdctl.md README.md READMEv2-etcdctl.md
[root@localhost etcd-v3.3.10-linux-amd64]# mv etcd etcdctl /opt/etcd/bin/
[root@localhost k8s]# cd etcd-cert/
[root@localhost etcd-cert]# ls
ca-config.json ca.csr ca-csr.json ca-key.pem ca.pem etcd-cert.sh server.csr server-csr.json server-key.pem server.pem
[root@localhost etcd-cert]# mv *.pem /opt/etcd/ssl #证书拷贝
[root@localhost k8s]# bash etcd.sh etcd01 192.168.223.10 etcd02=https://192.168.223.20:2380,etcd03=https://192.168.223.30:2380 #进入卡住状态等待其他节点加入
[root@localhost ~]# ps -ef | grep etcd #使用另外一个会话打开,会发现etcd进程已经开启
将证书和启动脚本推送/复制到两台node节点中
[root@localhost k8s]# scp -r /opt/etcd/ root@192.168.223.20:/opt/ #拷贝证书去其他节点
[root@localhost k8s]# scp -r /opt/etcd/ root@192.168.223.30:/opt #拷贝证书去其他节点
[root@localhost k8s]# scp /usr/lib/systemd/system/etcd.service root@192.168.223.20:/usr/lib/systemd/system/ #启动脚本拷贝其他节点
[root@localhost k8s]# scp /usr/lib/systemd/system/etcd.service root@192.168.223.30:/usr/lib/systemd/system/ #启动脚本拷贝其他节点
在node01和node02节点修改
[root@localhost ~]# vim /opt/etcd/cfg/etcd
#[Member]
ETCD_NAME="etcd02"
ETCD_DATA_DIR="/var/lib/etcd/default.etcd"
ETCD_LISTEN_PEER_URLS="https://192.168.223.20:2380" #ip地址修改对应的node节点
ETCD_LISTEN_CLIENT_URLS="https://192.168.223.20:2379" #ip地址修改对应的node节点
#[Clustering]
ETCD_INITIAL_ADVERTISE_PEER_URLS="https://192.168.223.30:2380" #ip地址修改对应的node节点
ETCD_ADVERTISE_CLIENT_URLS="https://192.168.223.30:2379" #ip地址修改对应的node节点
ETCD_INITIAL_CLUSTER="etcd01=https://192.168.241.20:2380,etcd02=https://192.168.241.4:2380,etcd03=https://192.168.241.3:2380"
ETCD_INITIAL_CLUSTER_TOKEN="etcd-cluster"
ETCD_INITIAL_CLUSTER_STATE="new"
[root@localhost ssl]# systemctl start etcd
[root@localhost ssl]# systemctl enable etcd
[root@localhost ssl]# systemctl status etcd
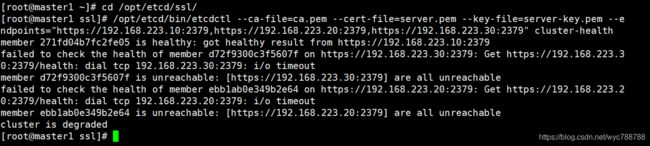
在Master检查集群状态
检查群集状态(需要在有证书的目录下使用此命令)
[root@localhost ~]# cd /opt/etcd/ssl
[root@localhost ~]# /opt/etcd/bin/etcdctl --ca-file=ca.pem --cert-file=server.pem --key-file=server-key.pem --endpoints="https://192.168.223:10:2379,https://192.168.223.20:2379,https://192.168.223.30:2379" cluster-health