DASCTF X BUU DASCTF2021 misc all WP
去******的猜************
MISC WP
签到:
flag{welcome_to_dasctf_may}
Holmes:
文件尾有rar,分离出来发现加了密,然鹅图片上面又有跳舞小人(他这个表和大小写都。。。一言难尽,你们去百度就知道为什么了…)

对应解码,得到密码
YOUAREHOLMES
得到一个flag.py
flag="flag{********************************}"
encflag=[]
for i in range(len(flag)):
encflag.append((ord(flag[i])+i)%128)
print(encflag)
'''
[102, 109, 99, 106, 127, 57, 60, 104, 60, 107, 61, 62, 65, 68, 115, 64, 67, 119, 66, 74, 73, 74, 119, 75, 74, 79, 79,
76, 78, 82, 78, 85, 83, 84, 82, 86, 92, 34]
'''
逆一下就好了
s = [102, 109, 99, 106, 127, 57, 60, 104, 60, 107, 61, 62, 65, 68, 115, 64, 67, 119, 66, 74, 73, 74, 119, 75, 74, 79, 79,76, 78, 82, 78, 85, 83, 84, 82, 86, 92, 34]
flag = ""
for i in range(len(s)):
flag += chr((s[i]-i)%128)
print(flag)

rickroll_u
zip里面也有一个ah_old_time.txt,考虑明文攻击
![]()
算法选择存储把这个txt压缩
然后复制一份加密的压缩包,删掉音频
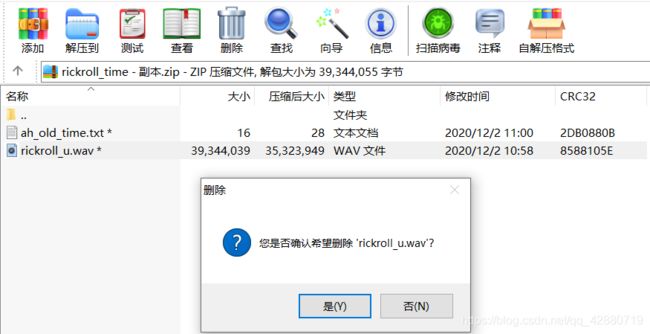
然后明文攻击

得到这个wav,010打开发现文件尾还有一个wav文件
 分离出来,用AU查看,妥妥的拨号音
分离出来,用AU查看,妥妥的拨号音
 用DTMF,得到flag,将其小写之后md5一下再包上flag提交即可
用DTMF,得到flag,将其小写之后md5一下再包上flag提交即可

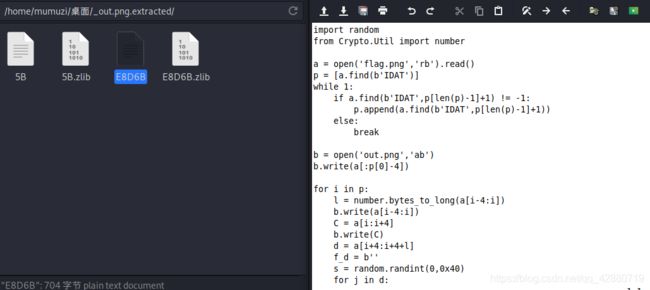
CRC_check
import random
from Crypto.Util import number
a = open('flag.png','rb').read()
p = [a.find(b'IDAT')]
while 1:
if a.find(b'IDAT',p[len(p)-1]+1) != -1:
p.append(a.find(b'IDAT',p[len(p)-1]+1))
else:
break
b = open('out.png','ab')
b.write(a[:p[0]-4])
for i in p:
l = number.bytes_to_long(a[i-4:i])
b.write(a[i-4:i])
C = a[i:i+4]
b.write(C)
d = a[i+4:i+4+l]
f_d = b''
s = random.randint(0,0x40)
for j in d:
f_d += number.long_to_bytes(j^s)
if i == p[0]:
b.write(d)
else:
b.write(f_d)
c = a[i+4+l:i+4+l+4]
b.write(c)
if i == p[-1]:
b.write(a[i+4+l+4:])
b.close()
就随机一个数与每个IDAT异或,反过来写脚本的时候只需要异或回来然后与实际的CRC做对比即可,只需要在原脚本基础上稍微修改即可
解密脚本:
import random
import zlib
from Crypto.Util import number
f_d = b''
a = open('out.png','rb').read()
p = [a.find(b'IDAT')]
while 1:
if a.find(b'IDAT',p[len(p)-1]+1) != -1:
p.append(a.find(b'IDAT',p[len(p)-1]+1))
else:
break
b = open('flag.png','wb')
b.write(a[:p[0]-4])
for i in p:
l = number.bytes_to_long(a[i-4:i])
b.write(a[i-4:i])
C = a[i:i+4]
b.write(C)
d = a[i+4:i+4+l]
c = a[i+4+l:i+4+l+4]
for j in range(0,256):
f_d = b''
f_d += C
for k in d:
f_d += number.long_to_bytes(k^j)
if zlib.crc32(f_d)==number.bytes_to_long(c):
break
if i == p[0]:
b.write(d)
else:
b.write(f_d[4:])
b.write(c)
if i == p[-1]:
b.write(a[i+4+l+4:])
b.close()

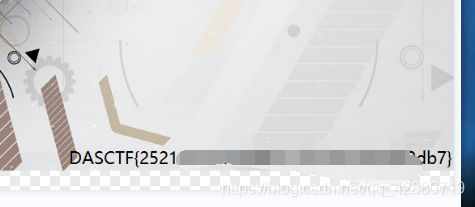
010打开还是显示CRC错误,修改一下图片高度即可得到flag
sseddoG
打开附件就看到有png,尝试导出发现还有一个rar,就一并导出

其中rar里面有secert
再看流量包发现有一个10000字节的流量,追踪tcp流拉到最底下发现RSA的公钥私钥

公钥解签名,私钥解密文。这里数字要n2s然后base64
import libnum
import base64
print(base64.b64encode(libnum.n2s(6945004599188163993695415369835695903301224003136994252560594956191090963121611565339316899123749651980866032846579298200421747380583546633355992903073674181349057044030322829788264132202636849376954935277228938532451604402772829242424577058024238656161078439246537271516326863255516855631753446705292842229626286876548916801469642547513456705866784202623394305276451128865785358297012288872815722144655832856702699498675579782594166664458814522864775862036884859354259378908758433643337060342583622920263235497780709801069090899910257671959718315799533292405361650450010152269010240983236777594133358567962307235569)))
print(base64.b64encode(libnum.n2s(2657375403899004421682435875591648757169751001935445937761677813563331237751296771655965799410203548200444843121899114276425174188686046977514392352233441829494629361400810323413751538449142557000621910082199277027187814332458889139635831754705831808451385798544850324418189973193940364270700678684371080465070928269782397410454121628205746311654719735981174781630012234885865191874665887323338400055601894791632973447395440378983992188376105785566869556895986983889219094640854379267584790389009829385657891279182819588524435817909919666674804622368593843455996806164859962400637898116212711639490474051288221345806)))
DCT domain steganography & crack
这题*************
其中官方给了一个密码表,而DCT一般就考虑outguess和F5,outguess写个劣质改编爆破脚本
from os import system
f = open("top1000_password.txt",'r').read().splitlines()
i=0
def getNextKey():
global key
global i
key = f[i]
i += 1
return 1
def main():
while getNextKey():
cmd = "outguess -k " + key + " -r out.jpg ./output/" + key +".txt"
print(cmd)
system(cmd)
if __name__ == "__main__":
main()
然后就跑啊跑
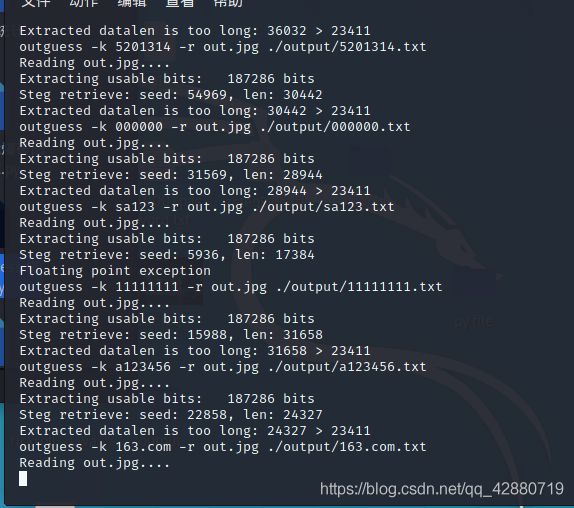
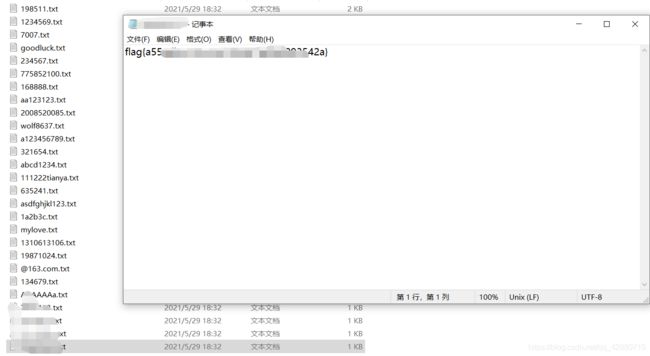
跑完放windows来,考虑到flag占用字节很少,将文件按照大小排序后一次从最小的打开,第一个就是flag
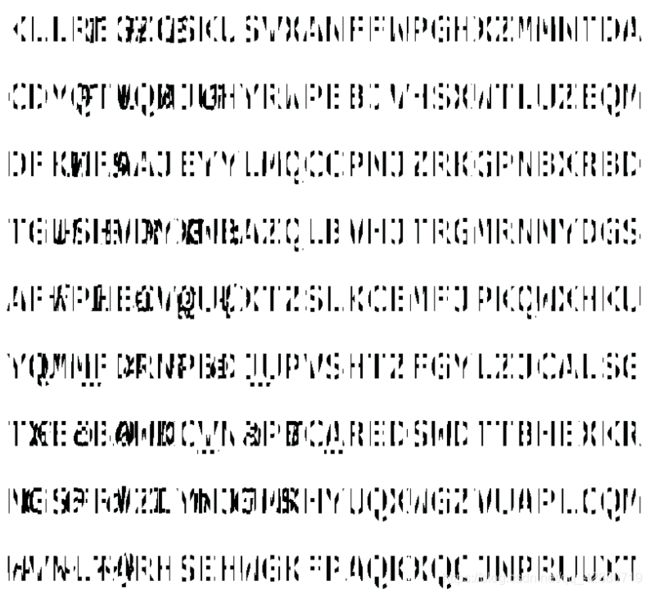
A New Base
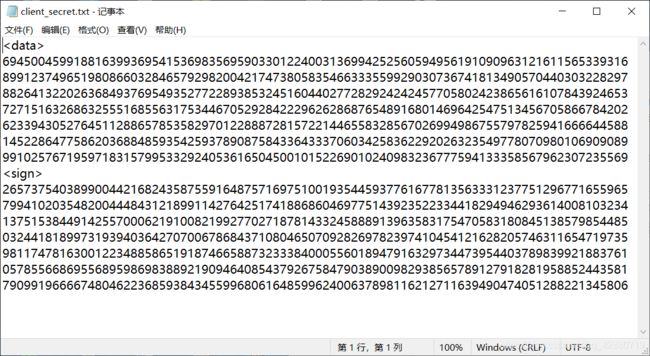
先看txt
![]()
然后看流量包,搜一下flag

查看一下

将其复制下来,base64转码一下,发现是俄语,并且正好33

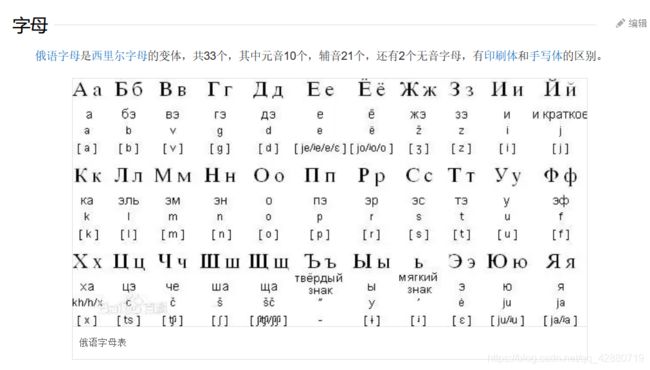
根据base33,可以知道表为数字+字母表前23,这里放春哥的脚本
import base64
from collections import Counter
import string
from Crypto.Util.number import *
with open('flag2.txt') as f:
s = f.read()
s = ''.join(s.splitlines())
s = base64.b64decode(s).decode()
ru = 'АБВГДЕЁЖЗИЙКЛМНОПРСТУФХЦЧШЩЪЫЬЭЮЯ'
ru = ''.join(ru.splitlines())
base = string.digits + string.ascii_uppercase[:23]
print(ru)
s = s.translate(str.maketrans(ru, base))
s = long_to_bytes(int(s, 33))
print(s)
with open('gao.png', 'wb') as f:
f.write(s)
from PIL import Image
img = Image.open("gao.png")
width,height = img.size[0],img.size[1]
img2 = Image.new('RGB',(1000,1000))
w1 = 0
for w in range(1,width,10):
b = (w,0,w+5,height)
re = img.crop(b)
img2.paste(re,(w1,0))
img2.save('tmp.png')
w1 = w1 +5
img2.save("flag.png")