【OpenVP* 】Centos 部署OpenVP* 证书+多客户端+密码认证
1、添加epel yum源
[root@open ~]# wget -O /etc/yum.repos.d/epel.repo http://mirrors.aliyun.com/repo/epel-6.repo
2、下载证书生成工具easy-rsa
[root@open ~]# yum -y install easy-rsa
3、创建证书环境目录
[root@open ~]# mkdir -p /opt/easy-rsa
[root@open ~]# cp -a /usr/share/easy-rsa/3.0.8/* /opt/easy-rsa/
[root@open ~]# cp -a /usr/share/doc/easy-rsa-3.0.8/vars.example /opt/easy-rsa/vars
4、修改vars配置文件,取消下面配置的注释
[root@open ~]# vi /opt/easy-rsa/vars
set_var EASYRSA_DN "cn_only"
set_var EASYRSA_REQ_COUNTRY "CN"
set_var EASYRSA_REQ_PROVINCE "GuangDong"
set_var EASYRSA_REQ_CITY "GuangZhou"
set_var EASYRSA_REQ_ORG "IT"
set_var EASYRSA_REQ_EMAIL "[email protected]"
set_var EASYRSA_NS_SUPPORT "yes"
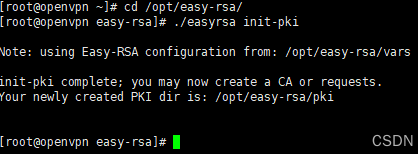
5、初始化,创建pki目录用于存储证书(以下都在/opt/easy-rsa目录下操作)
[root@open ~]# cd /opt/easy-rsa/
[root@open easy-rsa]# ./easyrsa init-pki
6、创建根证书,根证书用于ca对之后生成的server和client证书签名时使用
[root@open easy-rsa]# ./easyrsa build-ca
7、创建server端证书和密钥文件(nopass表示不加密密钥文件,生成过程中直接默认回车)
[root@open easy-rsa]# ./easyrsa gen-req server nopass
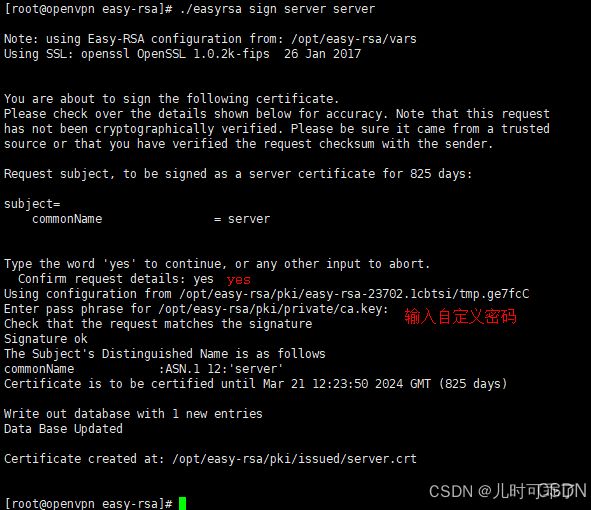
8、给server端证书签名
[root@open easy-rsa]# ./easyrsa sign server server
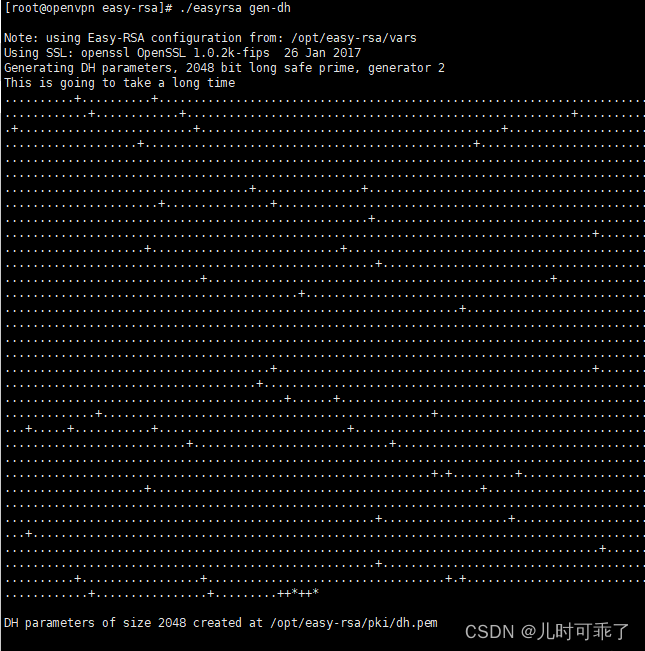
9、创建Diffie-Hellman文件,密钥交换时的Diffie-Hellman算法
[root@open easy-rsa]# ./easyrsa gen-dh
10、创建client端证书和密钥文件(nopass表示不加密密钥文件,生成过程中直接默认回车)
[root@open easy-rsa]# ./easyrsa gen-req client nopass
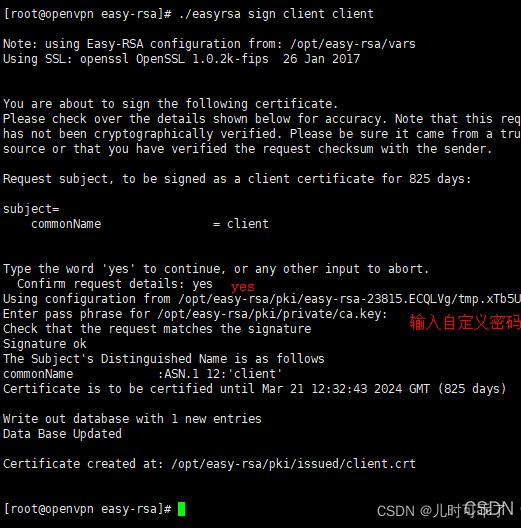
11、给client端证书签名
[root@open easy-rsa]# ./easyrsa sign client client
三、OpenVPN服务端部署
1、安装open
[root@open ~]# yum install -y open
2、创建TLS认证密钥
[root@open ~]# open --genkey --secret /etc/open/ta.key
3、创建新的配置文件/etc/open/server.conf
[root@open ~]# vi /etc/open/server.conf
#监听本机端口
port 1194
#指定采用的传输协议,可选tcp或udp
proto tcp
#指定创建的通信隧道类型,可选tun或tap
dev tun
#指定CA证书的文件路径
ca ca.crt
#指定服务器端的证书文件路径
cert server.crt
#指定服务器端的私钥文件路径
key server.key
#指定迪菲赫尔曼参数的文件路径,也就是交换证书
dh dh.pem
#给客户端分配地址池,注意:不能和VPN服务器内网网段有相同
server 10.8.0.0 255.255.255.0
#允许客户端访问内网网段
push "route 10.5.10.0 255.255.255.0"
#服务器自动给客户端分配IP后,客户端下次连接时,仍然采用上次的IP地址"第一次分配的IP保存在ipp.txt中,下一次分配其中保存的IP"
ifconfig-pool-persist ipp.txt
#存活时间,10秒ping一次,120如未收到响应则视为断线
keepalive 10 120
#最多允许100个客户端连接
max-clients 100
#日志记录位置
status open-status.log
#open版本
verb 3
#允许客户端与客户端相连接,默认情况下客户端只能与服务器相连接
client-to-client
#open日志记录位置
log /var/log/open.log
#通过keepalive检测超时后,重新启动VPN,不重新读取keys,保留第一次使用的keys
persist-key
#检测超时后,重新启动VPN,一直保持tun是linkup的.否则网络会先linkdown然后再linkup
persist-tun
#开启TLS-auth,使用ta.key防御攻击.服务器端的第二个参数值为0,客户端的为1
tls-auth /etc/open/ta.key 0
#开启多人同时登录
duplicate-cn
#允许使用自定义脚本
script-security 3
#脚本路径
auth-user-pass-verify /etc/open/check.sh via-env
#用户密码登陆方式验证:加上client-cert-not-required则代表只使用用户名密码方式验证登录,如果不加,则代表需要证书和用户名密码双重验证登录
username-as-common-name
#绑定客户端IP
client-config-dir /etc/open/ccd
4、拷贝证书到open主配置文件目录下
[root@open ~]# cp -a /opt/easy-rsa/pki/ca.crt /etc/open/
[root@open ~]# cp -a /opt/easy-rsa/pki/issued/server.crt /etc/open/
[root@open ~]# cp -a /opt/easy-rsa/pki/private/server.key /etc/open/
[root@open ~]# cp -a /opt/easy-rsa/pki/dh.pem /etc/open/
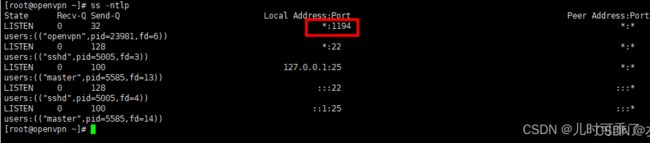
5、设置开机启动,检查服务端口
[root@open ~]# systemctl start open@server
[root@open ~]# systemctl status open@server
四、OpenVPN客户端部署
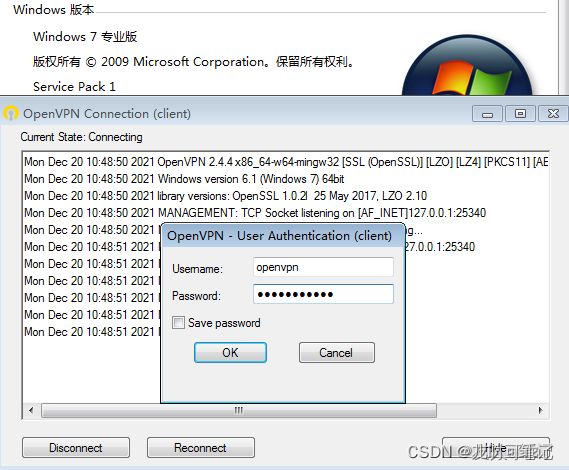
1、win7客户端安装,默认安装(open客户端需要.net支持,网络正常会自动安装)
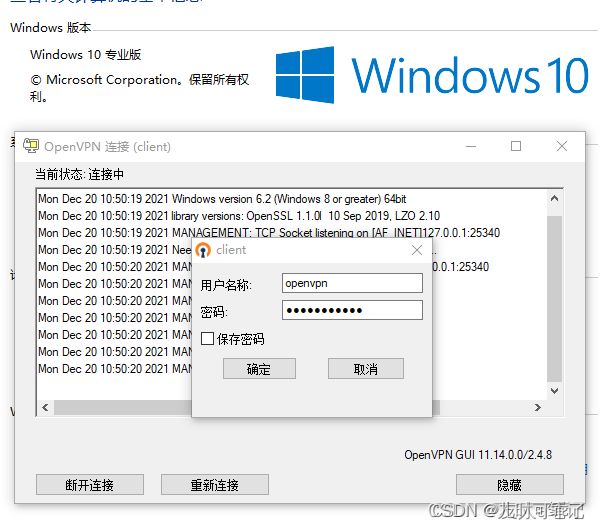
2、win10安装,默认安装(open客户端需要.net支持,网络正常会自动安装)
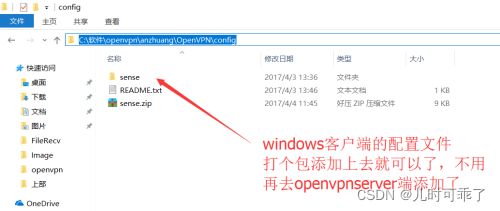
3、拷贝服务端生成的证书到open客户端安装目录的config目录下
/opt/easy-rsa/pki/ca.crt
/opt/easy-rsa/pki/issued/client.crt
/opt/easy-rsa/pki/private/client.key
/etc/open/ta.key
4、在客户端open安装目录的config目录下,新建一个client.o文件,写入配置
#指定当前VPN是客户端
client
#使用tun隧道传输协议
dev tun
#使用udp协议传输数据
proto tcp
#open服务器IP地址端口号
remote 10.5.10.202 1194
#断线自动重新连接,在网络不稳定的情况下非常有用
resolv-retry infinite
#不绑定本地特定的端口号
nobind
#指定CA证书的文件路径
ca ca.crt
#指定当前客户端的证书文件路径
cert client.crt
#指定当前客户端的私钥文件路径
key client.key
#指定日志文件的记录详细级别,可选0-9,等级越高日志内容越详细
verb 3
#通过keepalive检测超时后,重新启动VPN,不重新读取keys,保留第一次使用的keys
persist-key
#检测超时后,重新启动VPN,一直保持tun是linkup的。否则网络会先linkdown然后再linkup
persist-tun
#使用ta.key防御攻击。服务器端的第二个参数值为0,客户端的为1
tls-auth ta.key 1
#账号密码认证
auth-user-pass
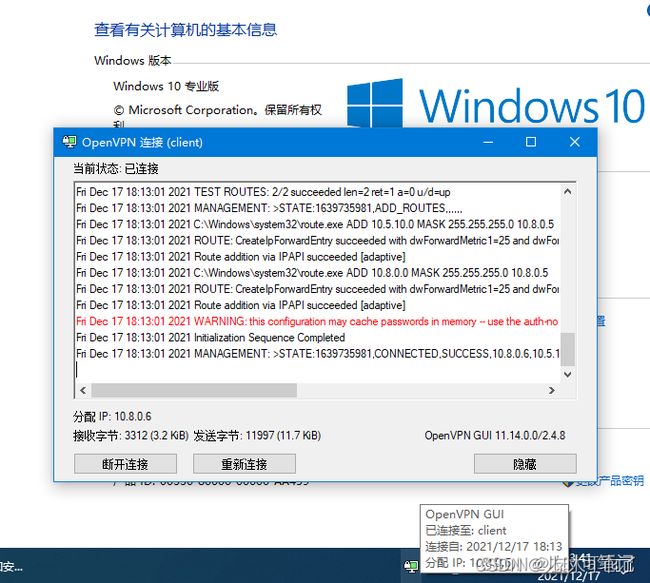
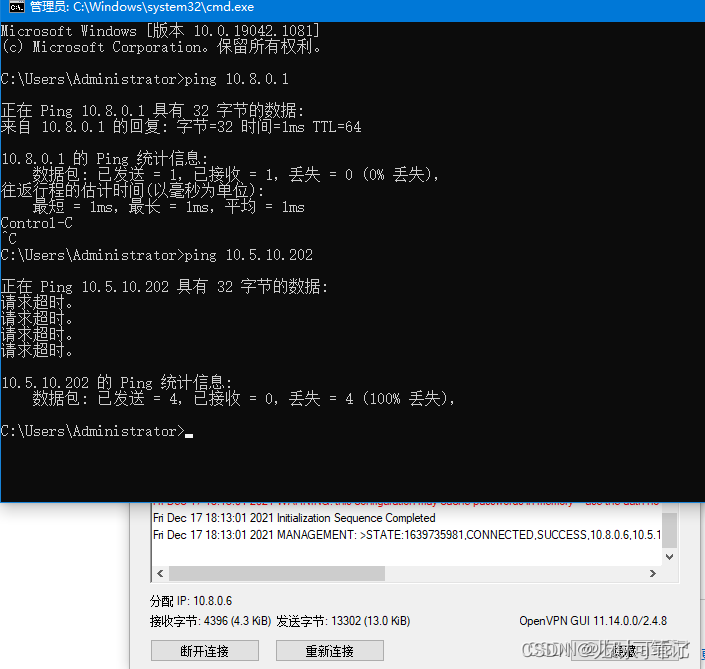
5、启动Open VPN客户端软件,连接成功OpenVPN的图标会变成绿色
win10连接成功
OpenVPN会分配一个IP地址给客户端,客户端会使用该虚拟网络IP地址与服务端进行通信。
6、目前客户端只能ping虚拟网络的IP,不能跟内网其他主机互通
五、OpenVPN客户端访问内网
1、客户端要想跟内网通讯还需要open服务端开启内核转发
[root@open ~]# echo "net.ipv4.ip_forward = 1" >> /etc/sysctl.conf
[root@open ~]# sysctl -p
net.ipv4.ip_forward = 1
2、方法一:添加路由规则方式访问内部网络
在内网主机上添加一条路由规则,让内网主机有回到OpenVPN客户端的路由。如果不添加,那内网主机只能接受到来自客户端的包,但是没法把响应的包传回去。
弊端:如果有成白上千台主机时,每一台主机都要添加路由规则,这样任务量是比较大的。
3、方法二:添加防火墙方式访问内部网络
在服务端开启防火墙,放行open服务,并且开启masquerade
优点:只需在OpenVPN服务端配置防火墙规则,内部网络主机无需配置
[root@open ~]# systemctl start firewalld
[root@open ~]# firewall-cmd --add-masquerade --permanent
[root@open ~]# firewall-cmd --add-service=open --permanent
[root@open ~]# firewall-cmd --add-port=1194/tcp --permanent
[root@open ~]# firewall-cmd --reload
六、证书+密码认证
1、修改OpenVPN服务端配置文件
#在最后增加以下配置
[root@open ~]# vi /etc/open/server.conf
#允许使用自定义脚本
script-security 3
#脚本路径
auth-user-pass-verify /etc/open/check.sh via-env
#用户密码登陆方式验证
username-as-common-name
加上client-cert-not-required则代表只使用用户名密码方式验证登录,如果不加,则代表需要证书和用户名密码双重验证登录
2、添加脚本
[root@open ~]# vi /etc/open/check.sh
#!/bin/sh
###########################################################
PASSFILE="/etc/open/openpass"
LOG_FILE="/var/log/open-password.log"
TIME_STAMP=`date "+%Y-%m-%d %T"`
if [ ! -r "${PASSFILE}" ]; then
echo "${TIME_STAMP}: Could not open password file \"${PASSFILE}\" for reading." >> ${LOG_FILE}
exit 1
fi
CORRECT_PASSWORD=`awk '!/^;/&&!/^#/&&$1=="'${username}'"{print $2;exit}' ${PASSFILE}`
if [ "${CORRECT_PASSWORD}" = "" ]; then
echo "${TIME_STAMP}: User does not exist: username=\"${username}\", password=\"${password}\"." >> ${LOG_FILE}
exit 1
fi
if [ "${password}" = "${CORRECT_PASSWORD}" ]; then
echo "${TIME_STAMP}: Successful authentication: username=\"${username}\"." >> ${LOG_FILE}
exit 0
fi
echo "${TIME_STAMP}: Incorrect password: username=\"${username}\", password=\"${password}\"." >> ${LOG_FILE}
exit 1
3、增加执行权限
[root@open ~]# chmod +x /etc/open/check.sh
4、增加用户密码文件
[root@open ~]# vi /etc/open/openpass
open open@123
5、重启open服务
[root@open ~]# systemctl restart open@server
6、修改客户端安装路径config目录下的client.opvn配置文件,在最后增加
auth-user-pass
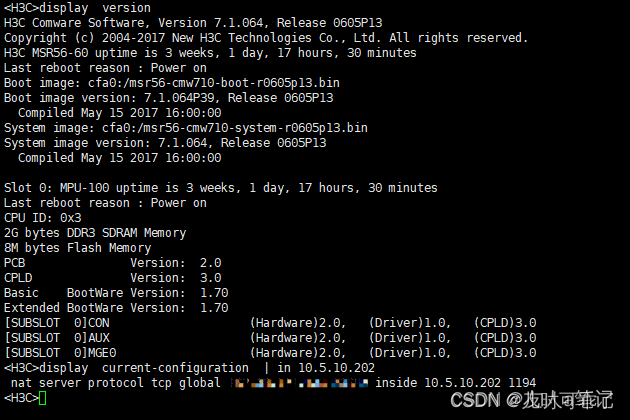
七、出口防火墙设置
1、在出口设备配置映射,映射open 1194端口到公网,允许用户通过对应的公网地址+端口访问
2、修改客户端的client.o文件,把远程地址改为公网IP+端口
#open服务器IP地址端口号
remote 公网IP 1194
Linux安装客户端
linux客户端的安装和服务器端一样就是配置文件不一样
[root@server liuhx]# wget http://www.oberhumer.com/opensource/lzo/download/lzo-2.06.tar.gz
--2017-04-02 15:42:36-- http://www.oberhumer.com/opensource/lzo/download/lzo-2.06.tar.gz
正在解析主机 www.oberhumer.com... 193.170.194.40
正在连接 www.oberhumer.com|193.170.194.40|:80... 已连接。
已发出 HTTP 请求,正在等待回应... 200 OK
长度:583045 (569K) [application/x-gzip]
正在保存至: “lzo-2.06.tar.gz”
100%[=======================================================================================================================================================================>] 583,045 200K/s in 2.8s
2017-04-02 15:42:42 (200 KB/s) - 已保存 “lzo-2.06.tar.gz” [583045/583045])
[root@server liuhx]# wget https://swupdate.open.org/community/releases/open-2.0.9.tar.gz
--2017-04-02 15:42:54-- https://build.open.net/downloads/releases/open-2.0.9.tar.gz
正在解析主机 build.open.net... 54.215.128.159
正在连接 build.open.net|54.215.128.159|:443... 已连接。
已发出 HTTP 请求,正在等待回应... 200 OK
长度:911158 (890K) [application/octet-stream]
正在保存至: “open-2.2.2.tar.gz”
93% [============================================================================================================================================================> ] 851,710 266K/s eta(英国中部时100%[=======================================================================================================================================================================>] 911,158 268K/s in 3.3s
2017-04-02 15:42:58 (268 KB/s) - 已保存 “open-2.2.2.tar.gz” [911158/911158])
[root@server liuhx]# ll
总用量 1464
-rw-r--r-- 1 root root 583045 8月 13 2011 lzo-2.06.tar.gz
-rw-r--r-- 1 root root 911158 5月 9 2013 open-2.2.2.tar.gz
[root@server liuhx]
2.安装依赖包
yum -y install openssl*
[root@server yum.repos.d]# rpm -qa |grep openssl*
openssl098e-0.9.8e-20.el6.centos.1.x86_64
openssh-server-5.3p1-111.el6.x86_64 #要有
openssl-1.0.1e-48.el6_8.4.x86_64
openssl-devel-1.0.1e-48.el6_8.4.x86_64 #要有
openssl-perl-1.0.1e-48.el6_8.4.x86_64
openssh-clients-5.3p1-111.el6.x86_64
openssl-static-1.0.1e-48.el6_8.4.x86_64
openssh-5.3p1-111.el6.x86_64
[root@server yum.repos.d]#
cd /usr/src/
tar zxf lzo-2.06.tar.gz
cd lzo-2.06
./configure&& make && make install
3.安装open (make是出现缺失gcc,需先安装gcc:yum -y install gcc)
[root@server lzo-2.06]# cd /usr/src/
[root@server liuhx]# ll
总用量 1468
drwxr-xr-x 13 root root 4096 4月 2 15:44 lzo-2.06
-rw-r--r-- 1 root root 583045 8月 13 2011 lzo-2.06.tar.gz
-rw-r--r-- 1 root root 911158 5月 9 2013 open-2.0.9.tar.gz
[root@server liuhx]# tar xf open-2.2.2.tar.gz
[root@server liuhx]# cd open-2.2.2
[root@server open-2.2.2]# ./configure --with-lzo-headers=/usr/local/include --with-lzo-lib=/usr/local/lib
[root@server open-2.2.2]# make && make install
[root@server open-2.2.2]# which open
/usr/local/sbin/open
查看网卡可以看出多了一个tun网卡
[root@client open]# ifconfig
eth0 Link encap:Ethernet HWaddr 00:0C:29:A8:84:76
inet addr:10.0.0.29 Bcast:10.0.0.255 Mask:255.255.255.0
inet6 addr: fe80::20c:29ff:fea8:8476/64 Scope:Link
UP BROADCAST RUNNING MULTICAST MTU:1500 Metric:1
RX packets:21461 errors:0 dropped:0 overruns:0 frame:0
TX packets:12361 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:1000
RX bytes:26250834 (25.0 MiB) TX bytes:1137891 (1.0 MiB)
lo Link encap:Local Loopback
inet addr:127.0.0.1 Mask:255.0.0.0
inet6 addr: ::1/128 Scope:Host
UP LOOPBACK RUNNING MTU:65536 Metric:1
RX packets:2 errors:0 dropped:0 overruns:0 frame:0
TX packets:2 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:0
RX bytes:200 (200.0 b) TX bytes:200 (200.0 b)
tun0 Link encap:UNSPEC HWaddr 00-00-00-00-00-00-00-00-00-00-00-00-00-00-00-00
inet addr:10.8.0.6 P-t-P:10.8.0.5 Mask:255.255.255.255
UP POINTOPOINT RUNNING NOARP MULTICAST MTU:1500 Metric:1
RX packets:2 errors:0 dropped:0 overruns:0 frame:0
TX packets:2 errors:0 dropped:0 overruns:0 carrier:0
collisions:0 txqueuelen:100
RX bytes:168 (168.0 b) TX bytes:168 (168.0 b)
[root@client open]#
[root@client open]# ll
总用量 16
-rw-r--r-- 1 root root 1306 4月 2 16:22 ca.crt
-rw-r--r-- 1 root root 3440 4月 3 13:13 sense.conf
-rw-r--r-- 1 root root 3870 4月 2 17:06 sense.crt
-rw-r--r-- 1 root root 916 4月 2 17:06 sense.key
[root@client open]# pwd
/etc/open
[root@client open]#
在证书所在目录下执行 /etc/open/:
[root@client open]# /usr/local/sbin/open --config /etc/open/client.o &
[1] 11068
[root@client open]# Tue Apr 4 11:54:07 2017 Open××× 2.2.2 x86_64-unknown-linux-gnu [SSL] [LZO2] [EPOLL] [eurephia] built on Apr 4 2017
Tue Apr 4 11:54:07 2017 NOTE: Open××× 2.1 requires '--script-security 2' or higher to call user-defined scripts or executables
Tue Apr 4 11:54:07 2017 WARNING: file 'sense.key' is group or others accessible
Tue Apr 4 11:54:07 2017 LZO compression initialized
Tue Apr 4 11:54:07 2017 Control Channel MTU parms [ L:1544 D:140 EF:40 EB:0 ET:0 EL:0 ]
Tue Apr 4 11:54:07 2017 Socket Buffers: R=[87380->131072] S=[16384->131072]
Tue Apr 4 11:54:07 2017 Data Channel MTU parms [ L:1544 D:1450 EF:44 EB:135 ET:0 EL:0 AF:3/1 ]
Tue Apr 4 11:54:07 2017 Local Options hash (VER=V4): '69109d17'
Tue Apr 4 11:54:07 2017 Expected Remote Options hash (VER=V4): 'c0103fa8'
Tue Apr 4 11:54:07 2017 Attempting to establish TCP connection with 10.0.0.28:52115 [nonblock]
Tue Apr 4 11:54:08 2017 TCP connection established with 10.0.0.28:52115
Tue Apr 4 11:54:08 2017 TCPv4_CLIENT link local: [undef]
Tue Apr 4 11:54:08 2017 TCPv4_CLIENT link remote: 10.0.0.28:52115
Tue Apr 4 11:54:08 2017 TLS: Initial packet from 10.0.0.28:52115, sid=4a60fbc1 111eb0e6
Tue Apr 4 11:54:08 2017 VERIFY OK: depth=1, /C=CN/ST=BJ/L=BeiJing/O=liuhx/OU=liuhx/CN=liuhx/name=liuhx/emailAddress=[email protected]
Tue Apr 4 11:54:08 2017 VERIFY OK: nsCertType=SERVER
Tue Apr 4 11:54:08 2017 VERIFY OK: depth=0, /C=CN/ST=BJ/L=BeiJing/O=liuhx/OU=liuhx/CN=server/name=liuhx/emailAddress=[email protected]
Tue Apr 4 11:54:09 2017 Data Channel Encrypt: Cipher 'BF-CBC' initialized with 128 bit key
Tue Apr 4 11:54:09 2017 Data Channel Encrypt: Using 160 bit message hash 'SHA1' for HMAC authentication
Tue Apr 4 11:54:09 2017 Data Channel Decrypt: Cipher 'BF-CBC' initialized with 128 bit key
Tue Apr 4 11:54:09 2017 Data Channel Decrypt: Using 160 bit message hash 'SHA1' for HMAC authentication
Tue Apr 4 11:54:09 2017 Control Channel: TLSv1, cipher TLSv1/SSLv3 DHE-RSA-AES256-SHA, 1024 bit RSA
Tue Apr 4 11:54:09 2017 [server] Peer Connection Initiated with 10.0.0.28:52115
Tue Apr 4 11:54:11 2017 SENT CONTROL [server]: 'PUSH_REQUEST' (status=1)
Tue Apr 4 11:54:11 2017 PUSH: Received control message: 'PUSH_REPLY,route 172.16.1.0 255.255.255.0,route 10.8.0.1,topology net30,ping 10,ping-restart 120,ifconfig 10.8.0.6 10.8.0.5'
Tue Apr 4 11:54:11 2017 OPTIONS IMPORT: timers and/or timeouts modified
Tue Apr 4 11:54:11 2017 OPTIONS IMPORT: --ifconfig/up options modified
Tue Apr 4 11:54:11 2017 OPTIONS IMPORT: route options modified
Tue Apr 4 11:54:11 2017 ROUTE default_gateway=10.0.0.254
Tue Apr 4 11:54:11 2017 TUN/TAP device tun0 opened
Tue Apr 4 11:54:11 2017 TUN/TAP TX queue length set to 100
Tue Apr 4 11:54:11 2017 /sbin/ifconfig tun0 10.8.0.6 pointopoint 10.8.0.5 mtu 1500
Tue Apr 4 11:54:11 2017 /sbin/route add -net 172.16.1.0 netmask 255.255.255.0 gw 10.8.0.5
Tue Apr 4 11:54:11 2017 /sbin/route add -net 10.8.0.1 netmask 255.255.255.255 gw 10.8.0.5
Tue Apr 4 11:54:11 2017 Initialization Sequence Completed
[root@client open]#
[root@client open]# ping 172.16.1.17
PING 172.16.1.17 (172.16.1.17) 56(84) bytes of data.
64 bytes from 172.16.1.17: icmp_seq=1 ttl=63 time=0.897 ms
64 bytes from 172.16.1.17: icmp_seq=2 ttl=63 time=1.57 ms
^C
--- 172.16.1.17 ping statistics ---
2 packets transmitted, 2 received, 0% packet loss, time 1434ms
rtt min/avg/max/mdev = 0.897/1.234/1.572/0.339 ms
[root@client open]#