Docker与微服务实战(入门)
文章目录
- 前言
- 一、简介
-
- 1.1 Docker是什么
- 1.2 为什么会出现Docker
- 1.3 虚拟机技术的发展
- 1.4 一句话概括
- 1.5 能干嘛
- 二、入门
-
- 2.1 部署
-
- 2.1.1 阿里云镜像加速
- 2.2 Docker的基本组成
-
- 2.2.1 镜像
- 2.2.2 容器
- 2.2.3 仓库
- 2.2.4 小总结
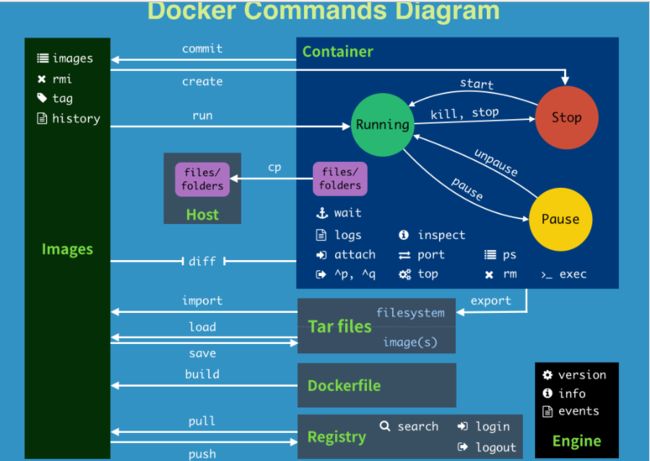
- 2.3 架构图解
-
- 2.3.1 运行流程
- 2.3.2 为什么docker比vm快
- 三、常用命令
-
- 3.1 帮助启动类命令
- 3.2 镜像命令
-
- 3.2.2 虚悬镜像
- 3.2.1 docker system df
- 3.3 容器命令
-
- 3.3.1 常用命令
- 四、镜像
-
- 4.1 是什么
- 4.2 镜像加载原理
- 4.3 为什么镜像要分层
- 4.4 重点理解
- 4.5 操作案例
- 4.6 小总结
- 五、容器卷
-
- 5.1 是什么
- 5.2 能干嘛
- 5.3 数据卷案例
- 5.4 卷的继承
- 六、常用软件安装
-
- 6.1 Tomcat
- 6.2 Mysql
-
- 6.2.1 编码问题的解决
- 6.3 Redis
-
- 6.3.1 Redis配置文件
- 6.3.2 启动实例
前言
文章参考于来自尚硅谷docker课堂笔记
一、简介
1.1 Docker是什么
Docker是基于Go语言实现的云开源项目。
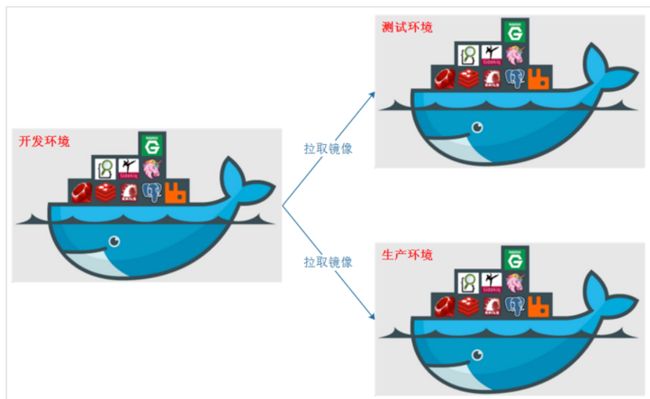
Docker的主要目标是“Build,Ship and Run Any App,Anywhere”,也就是通过对应用组件的封装、分发、部署、运行等生命周期的管理,使用户的APP(可以是一个WEB应用或数据库应用等等)及其运行环境能够做到“一次镜像,处处运行”。
1.2 为什么会出现Docker
环境配置沟通过于繁琐,用docker的话把自己配好的环境写好的项目直接打包成镜像,别人拿到镜像后就可以运行成为一个容器,直接运行
1.3 虚拟机技术的发展
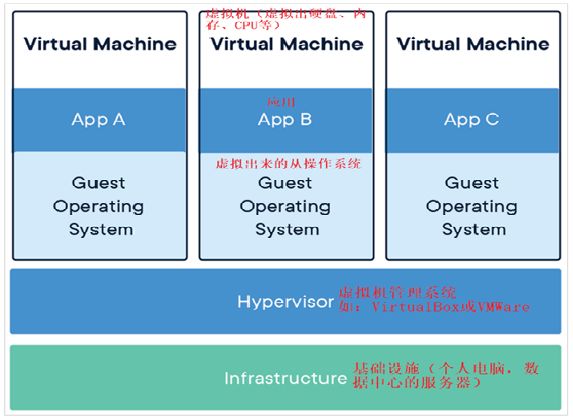
传统虚拟机技术
它可以在一种操作系统里面运行另一种操作系统,比如在Windows10系统里面运行Linux系统CentOS7。应用程序对此毫无感知,因为虚拟机看上去跟真实系统一模一样,而对于底层系统来说,虚拟机就是一个普通文件,不需要了就删掉,对其他部分毫无影响。这类虚拟机完美的运行了另一套系统,能够使应用程序,操作系统和硬件三者之间的逻辑不变。
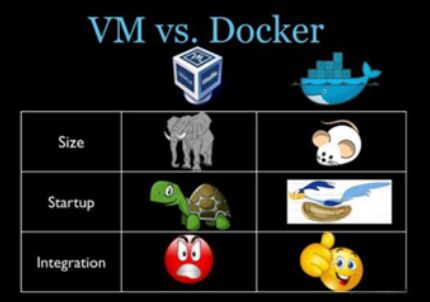
虚拟机的缺点:
1 资源占用多 2 冗余步骤多 3 启动慢
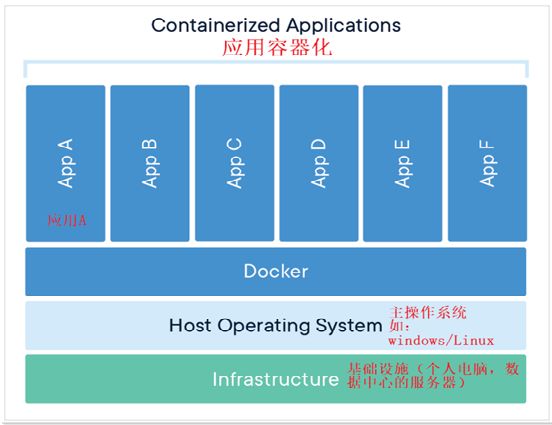
容器虚拟化技术
Linux 容器不是模拟一个完整的操作系统而是对进程进行隔离。有了容器,就可以将软件运行所需的所有资源打包到一个隔离的容器中。容器与虚拟机不同,不需要捆绑一整套操作系统,只需要软件工作所需的库资源和设置。系统因此而变得高效轻量并保证部署在任何环境中的软件都能始终如一地运行。
对比
1.4 一句话概括
解决了运行环境和配置问题的软件容器,方便做持续集成并有助于整体发布的容器虚拟化技术
1.5 能干嘛
docker能够一次构建处处运行
1.更快速的应用交付和部署
传统的应用开发完成后,需要提供一堆安装程序和配置说明文档,安装部署后需根据配置文档进行繁杂的配置才能正常运行。Docker化之后只需要交付少量容器镜像文件,在正式生产环境加载镜像并运行即可,应用安装配置在镜像里已经内置好,大大节省部署配置和测试验证时间。
2.更高效的计算资源利用
Docker是内核级虚拟化,其不像传统的虚拟化技术一样需要额外的Hypervisor支持,所以在一台物理机上可以运行很多个容器实例,可大大提升物理服务器的CPU和内存的利用率。
3.更简单的系统运维
应用容器化运行后,生产环境运行的应用可与开发、测试环境的应用高度一致,容器会将应用程序相关的环境和状态完全封装起来,不会因为底层基础架构和操作系统的不一致性给应用带来影响,产生新的BUG。当出现程序异常时,也可以通过测试环境的相同容器进行快速定位和修复。
4.更便捷的升级和扩缩容
随着微服务架构和Docker的发展,大量的应用会通过微服务方式架构,应用的开发构建将变成搭乐高积木一样,每个Docker容器将变成一块“积木”,应用的升级将变得非常容易。当现有的容器不足以支撑业务处理时,可通过镜像运行新的容器进行快速扩容,使应用系统的扩容从原先的天级变成分钟级甚至秒级。
Docker借鉴了标准集装箱的概念。标准集装箱将货物运往世界各地,Docker将这个模型运用到自己的设计中,唯一不同的是:集装箱运输货物,而Docker运输软件。-
二、入门
2.1 部署
云服务器部署docker
直接用带docker的镜像,开机就可以用docker的命令
命令行部署docker
保证虚拟机能稳定上网即可
第一步
yum -y install gcc
yum -y install gcc-c++
sudo yum install -y yum-utils
第二步使用阿里云镜像
sudo yum-config-manager --add-repo http://mirrors.aliyun.com/docker-ce/linux/centos/docker-ce.repo
yum makecache fast
第三步安装
sudo yum install docker-ce docker-ce-cli containerd.io
systemctl start docker
systemctl enable docker
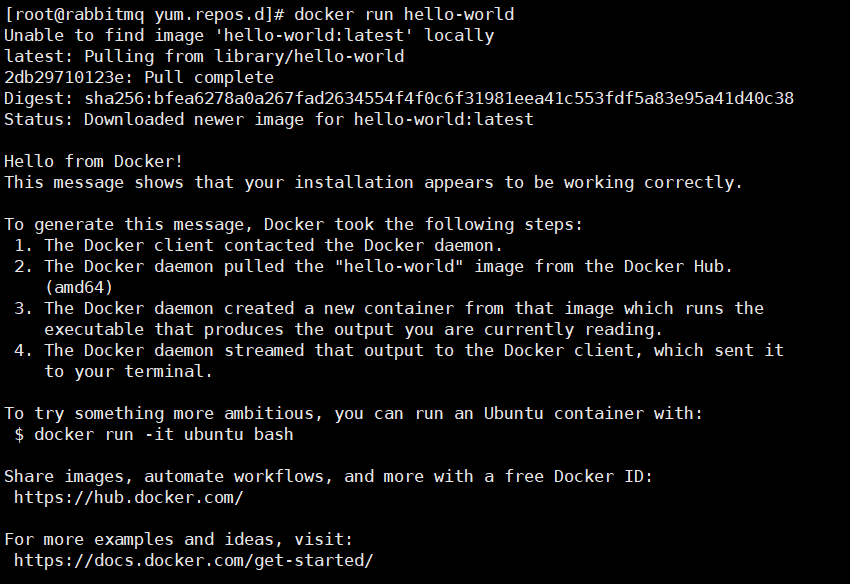
docker run hello-world
测试hello-world
2.1.1 阿里云镜像加速
2.2 Docker的基本组成
2.2.1 镜像
Docker 镜像(Image)就是一个只读的模板。镜像可以用来创建 Docker 容器,一个镜像可以创建很多容器。
它也相当于是一个root文件系统。比如官方镜像 centos:7 就包含了完整的一套 centos:7 最小系统的 root 文件系统。
相当于容器的“源代码”,docker镜像文件类似于Java的类模板,而docker容器实例类似于java中new出来的实例对象。
2.2.2 容器
1 从面向对象角度
**Docker 利用容器(Container)独立运行的一个或一组应用,应用程序或服务运行在容器里面,容器就类似于一个虚拟化的运行环境,容器是用镜像创建的运行实例。**就像是Java中的类和实例对象一样,镜像是静态的定义,容器是镜像运行时的实体。容器为镜像提供了一个标准的和隔离的运行环境,它可以被启动、开始、停止、删除。每个容器都是相互隔离的、保证安全的平台
2 从镜像容器角度
可以把容器看做是一个简易版的 Linux 环境(包括root用户权限、进程空间、用户空间和网络空间等)和运行在其中的应用程序。
2.2.3 仓库
仓库(Repository)是集中存放镜像文件的场所。
类似于
Maven仓库,存放各种jar包的地方;
github仓库,存放各种git项目的地方;
Docker公司提供的官方registry被称为Docker Hub,存放各种镜像模板的地方。
仓库分为公开仓库(Public)和私有仓库(Private)两种形式。
最大的公开仓库是 Docker Hub(https://hub.docker.com/),
存放了数量庞大的镜像供用户下载。国内的公开仓库包括阿里云 、网易云等
2.2.4 小总结
Docker 本身是一个容器运行载体或称之为管理引擎。我们把应用程序和配置依赖打包好形成一个可交付的运行环境,这个打包好的运行环境就是image镜像文件。只有通过这个镜像文件才能生成Docker容器实例(类似Java中new出来一个对象)。
image文件可以看作是容器的模板。Docker 根据 image 文件生成容器的实例。同一个 image 文件,可以生成多个同时运行的容器实例。
镜像文件
- image 文件生成的容器实例,本身也是一个文件,称为镜像文件。
容器实例
- 一个容器运行一种服务,当我们需要的时候,就可以通过docker客户端创建一个对应的运行实例,也就是我们的容器
仓库
- 就是放一堆镜像的地方,我们可以把镜像发布到仓库中,需要的时候再从仓库中拉下来就可以了。
2.3 架构图解
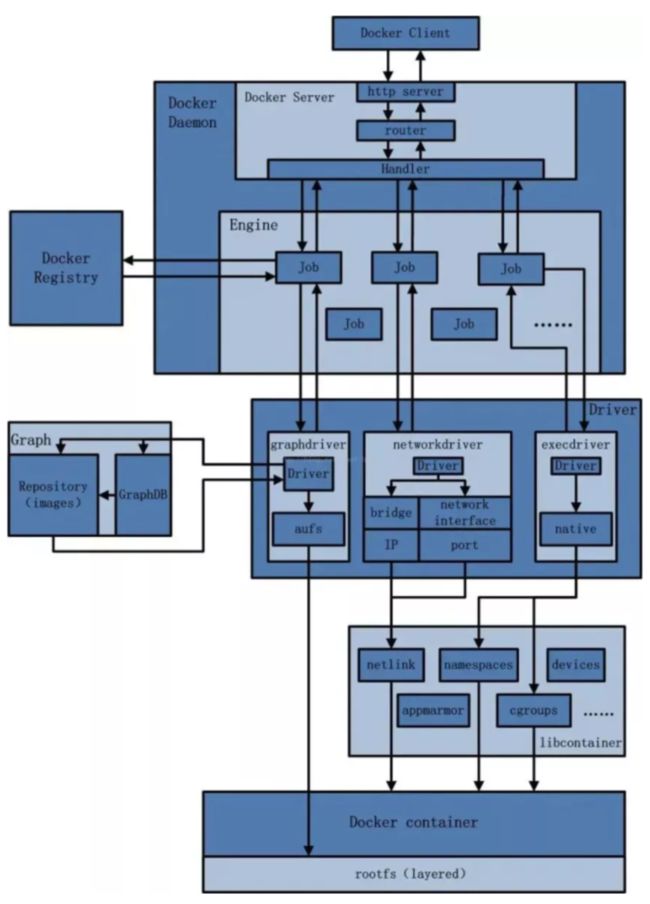
2.3.1 运行流程
- 用户是使用Docker Client与Docker Daemon建立通信,并发送请求给后者
- Docker Daemon作为Docker架构中的主体部分,首先提供Docker Server的功能可以接受Docker Client请求
- Docker Engine执行Docker内部的一些列工作,每一项工作都是一个Job的形式存在
- Job的运行过程中,当需要容器镜像时,则从docker registry中下载镜像,并通过镜像管理驱动Graph driver将下载镜像以graph的形式存储
- 当需docker创建网络环境时,通过网络管理驱动networkdriver创建并配置Docker容器网络环境
- 当需要限制docker容器运行资源或执行用户指令等操作时,则通过Exec driver来完成
- Libcontainer是一项独立的容器管理包,Network driver以及Exec driver都是通过Libcontainer来实现具体对容器进行的操作。
以上给爷理解着背,面试必考
你就想着容器创建的过程,通过dockerclient与dockerdaemon建立通信
dockerdaemon是核心部分,它提供的第一个功能就是与用户通信docker server
docker engine执行的是容器的内部工作,每一项工作都是一个job的形式
然后job需要镜像,去registry拉,注册进graph,需要网络有网络驱动给创建
最后需要一些特殊的指令的话通过exec driver来完成
Libcontainer字如其名
2.3.2 为什么docker比vm快
(1)docker有着比虚拟机更少的抽象层
由于docker不需要Hypervisor(虚拟机)实现硬件资源虚拟化,运行在docker容器上的程序直接使用的都是实际物理机的硬件资源。因此在CPU、内存利用率上docker将会在效率上有明显优势。
(2)docker利用的是宿主机的内核,而不需要加载操作系统OS内核
当新建一个容器时,docker不需要和虚拟机一样重新加载一个操作系统内核。进而避免引寻、加载操作系统内核返回等比较费时费资源的过程,当新建一个虚拟机时,虚拟机软件需要加载OS,返回新建过程是分钟级别的。而docker由于直接利用宿主机的操作系统,则省略了返回过程,因此新建一个docker容器只需要几秒钟。
三、常用命令
3.1 帮助启动类命令
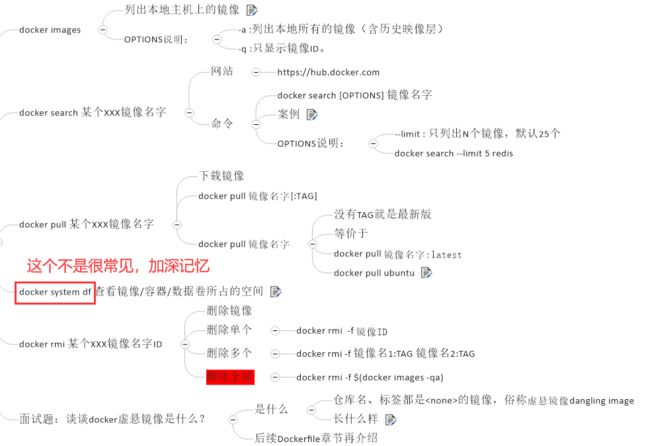
3.2 镜像命令
3.2.2 虚悬镜像
仓库名、标签都是的镜像,俗称虚悬镜像dangling image
3.2.1 docker system df
查看镜像/容器/数据卷所占的空间
[root@docker ~]# docker system df
TYPE TOTAL ACTIVE SIZE RECLAIMABLE
Images 2 0 177MB 177MB (100%)
Containers 2 0 0B 0B
Local Volumes 0 0 0B 0B
Build Cache 0 0 0B 0B
3.3 容器命令
docker run
–name=“容器新名字” 为容器指定一个名称;
-d: 后台运行容器并返回容器ID,也即启动守护式容器(后台运行);
-i:以交互模式运行容器,通常与 -t 同时使用;
-t:为容器重新分配一个伪输入终端,通常与 -i 同时使用;
也即启动交互式容器(前台有伪终端,等待交互);
-P: 随机端口映射,大写P
-p: 指定端口映射,小写p
docker run -it centos /bin/bash
-i: 交互式操作。
-t: 终端。
centos : centos 镜像。
/bin/bash:放在镜像名后的是命令,这里我们希望有个交互式 Shell,因此用的是 /bin/bash。
要退出终端,直接输入 exit:
docker logs
docker inspect
查看容器内部细节,很重要!
能看挂载相关信息,和网络等详细信息
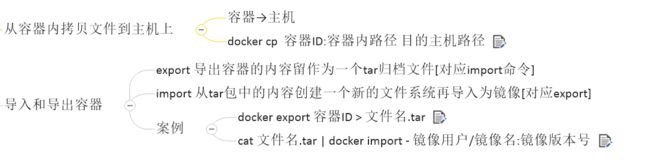
docker cp
3.3.1 常用命令
- attach Attach to a running container # 当前 shell 下 attach 连接指定运行镜像
- build Build an image from a Dockerfile # 通过 Dockerfile 定制镜像
- commit Create a new image from a container changes # 提交当前容器为新的镜像
- cp Copy files/folders from the containers filesystem to the host path #从容器中拷贝指定文件或者目录到宿主机中
- create Create a new container # 创建一个新的容器,同 run,但不启动容器
- diff Inspect changes on a container’s filesystem # 查看 docker 容器变化
- events Get real time events from the server # 从 docker 服务获取容器实时事件
- exec Run a command in an existing container # 在已存在的容器上运行命令
- export Stream the contents of a container as a tar archive # 导出容器的内容流作为一个 tar 归档文件[对应 import ]
- history Show the history of an image # 展示一个镜像形成历史
- images List images # 列出系统当前镜像
- import Create a new filesystem image from the contents of a tarball # 从tar包中的内容创建一个新的文件系统映像[对应export]
- info Display system-wide information # 显示系统相关信息
- inspect Return low-level information on a container # 查看容器详细信息
- kill Kill a running container # kill 指定 docker 容器
- load Load an image from a tar archive # 从一个 tar 包中加载一个镜像[对应 save]
- login Register or Login to the docker registry server # 注册或者登陆一个 docker 源服务器
- logout Log out from a Docker registry server # 从当前 Docker registry 退出
- logs Fetch the logs of a container # 输出当前容器日志信息
- port Lookup the public-facing port which is NAT-ed to PRIVATE_PORT # 查看映射端口对应的容器内部源端口
- pause Pause all processes within a container # 暂停容器
- ps List containers # 列出容器列表
- pull Pull an image or a repository from the docker registry server # 从docker镜像源服务器拉取指定镜像或者库镜像
- push Push an image or a repository to the docker registry server # 推送指定镜像或者库镜像至docker源服务器
- restart Restart a running container # 重启运行的容器
- rm Remove one or more containers # 移除一个或者多个容器
- rmi Remove one or more images # 移除一个或多个镜像[无容器使用该镜像才可删除,否则需删除相关容器才可继续或 -f 强制删除]
- run Run a command in a new container # 创建一个新的容器并运行一个命令
- save Save an image to a tar archive # 保存一个镜像为一个 tar 包[对应 load]
- search Search for an image on the Docker Hub # 在 docker hub 中搜索镜像
- start Start a stopped containers # 启动容器
- stop Stop a running containers # 停止容器
- tag Tag an image into a repository # 给源中镜像打标签
- top Lookup the running processes of a container # 查看容器中运行的进程信息
- unpause Unpause a paused container # 取消暂停容器
- version Show the docker version information # 查看 docker 版本号
- wait Block until a container stops, then print its exit code # 截取容器停止时的退出状态值
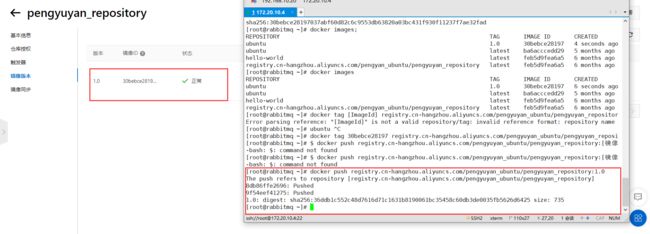
镜像服务的密码和阿里云账户的密码不是同一个密码,
上传成功
docker exec -it 1f1ed5798baa /bin/bash
docker commit -m=“ifconfig cmd add” -a=“pyy” 1f1ed5798baa:1.0
[root@VM-16-8-centos ~]# docker run -d -p 5000:5000 -v /myregistry:/tmp/registry --privileged=true registry
[root@VM-16-8-centos ~]# curl -XGET http://124.221.228.148:5000/v2/_catalog
{“repositories”:[“pyyubuntu”]}
四、镜像
4.1 是什么
镜像
是一种轻量级、可执行的独立软件包,它包含运行某个软件所需的所有内容,我们把应用程序和配置依赖打包好形成一个可交付的运行环境(包括代码、运行时需要的库、环境变量和配置文件等),这个打包好的运行环境就是image镜像文件。
只有通过这个镜像文件才能生成Docker容器实例(类似Java中new出来一个对象)。
分层的镜像
我们拉取镜像的时候好像是一层一层下载的,这是为什么呢?
UnionFS(联合文件系统):Union文件系统(UnionFS)是一种分层、轻量级并且高性能的文件系统,它支持对文件系统的修改作为一次提交来一层层的叠加,同时可以将不同目录挂载到同一个虚拟文件系统下(unite several directories into a single virtual filesystem)。Union 文件系统是 Docker 镜像的基础。镜像可以通过分层来进行继承,基于基础镜像(没有父镜像),可以制作各种具体的应用镜像。
特性:一次同时加载多个文件系统,但从外面看起来,只能看到一个文件系统,联合加载会把各层文件系统叠加起来,这样最终的文件系统会包含所有底层的文件和目录
4.2 镜像加载原理
Docker镜像加载原理:
docker的镜像实际上由一层一层的文件系统组成,这种层级的文件系统UnionFS。bootfs(boot file system)主要包含bootloader和kernel, bootloader主要是引导加载kernel, Linux刚启动时会加载bootfs文件系统,==在Docker镜像的最底层是引导文件系统bootfs。==这一层与我们典型的Linux/Unix系统是一样的,包含boot加载器和内核。当boot加载完成之后整个内核就都在内存中了,此时内存的使用权已由bootfs转交给内核,此时系统也会卸载bootfs。
rootfs (root file system) ,在bootfs之上。包含的就是典型 Linux 系统中的 /dev, /proc, /bin, /etc 等标准目录和文件。rootfs就是各种不同的操作系统发行版,比如Ubuntu,Centos等等。
对于一个精简的OS,rootfs可以很小,只需要包括最基本的命令、工具和程序库就可以了,因为底层直接用Host的kernel,自己只需要提供 rootfs 就行了。由此可见对于不同的linux发行版, bootfs基本是一致的, rootfs会有差别, 因此不同的发行版可以公用bootfs。
4.3 为什么镜像要分层
镜像分层最大的一个好处就是共享资源,方便复制迁移,就是为了复用。
比如说有多个镜像都从相同的 base 镜像构建而来,那么 Docker Host 只需在磁盘上保存一份 base 镜像;
同时内存中也只需加载一份 base 镜像,就可以为所有容器服务了。而且镜像的每一层都可以被共享。
4.4 重点理解
看了好几遍docker了,这个真的很重要!
Docker镜像层都是只读的,容器层是可写的
当容器启动时,一个新的可写层被加载到镜像的顶部。这一层通常被称作“容器层”,“容器层”之下的都叫“镜像层”。
所有对容器的改动 - 无论添加、删除、还是修改文件都只会发生在容器层中。只有容器层是可写的,容器层下面的所有镜像层都是只读的。
4.5 操作案例
新镜像
docker commit提交容器副本使之成为一个新的镜像
docker commit -m=“提交的描述信息” -a=“作者” 容器ID 要创建的目标镜像名:[标签名]
ubuntu安装vim命令
apt-get update
apt-get -y install vim
本地镜像发布阿里云
- 登录
$ docker login --username=用户名 registry.cn-hangzhou.aliyuncs.com
用于登录的用户名为阿里云账号全名,密码为开通服务时设置的密码。
- 推送
docker tag [ImageId] registry.cn-hangzhou.aliyuncs.com/pengyuyan_ubuntu/pengyuyan_repository:[镜像版本号]
docker push registry.cn-hangzhou.aliyuncs.com/pengyuyan_ubuntu/pengyuyan_repository:[镜像版本号]
下载阿里云镜像到本地
docker pull registry.cn-hangzhou.aliyuncs.com/pengyuyan_ubuntu/pengyuyan_repository:[镜像版本号]
本地镜像发布到私有库
私有库:
1 官方Docker Hub地址:https://hub.docker.com/,中国大陆访问太慢了且准备被阿里云取代的趋势,不太主流。
2 Dockerhub、阿里云这样的公共镜像仓库可能不太方便,涉及机密的公司不可能提供镜像给公网,所以需要创建一个本地私人仓库供给团队使用,基于公司内部项目构建镜像。
Docker Registry是官方提供的工具,可以用于构建私有镜像仓库
- 安装运行私有仓库
docker pull registry
docker run -d -p 5000:5000 -v /myregistry/:/tmp/registry --privileged=true registry
默认情况,仓库被创建在容器的/var/lib/registry目录下,建议自行用容器卷映射,方便于宿主机联调
- 给容器增加命令
docker run -it ubuntu /bin/bash
apt-get update
apt-get install net-tools
公式:
docker commit -m=“提交的描述信息” -a=“作者” 容器ID 要创建的目标镜像名:[标签名]
命令:在容器外执行,记得
docker commit -m=“ifconfig cmd add” -a=“pyy” a69d7c825c4f pyyubuntu:1.2
- 打标签,改配置
docker tag pyyubuntu:1.2 192.168.100.10:5000/pyyubuntu:1.2
vim /etc/docker/daemon.json
{
“registry-mirrors”: [“https://pengyuyan227.mirror.aliyuncs.com”],
“insecure-registries”: [“192.168.100.10:5000”]
}
- 上传
docker push 192.168.111.162:5000/zzyyubuntu:1.2
4.6 小总结
Docker中的镜像分层,支持通过扩展现有镜像,创建新的镜像。类似Java继承于一个Base基础类,自己再按需扩展。
新镜像是从 base 镜像一层一层叠加生成的。每安装一个软件,就在现有镜像的基础上增加一层
五、容器卷
–privileged=true
Docker挂载主机目录访问如果出现cannot open directory .: Permission denied
解决办法:在挂载目录后多加一个–privileged=true参数即可
5.1 是什么
一句话:有点类似我们Redis里面的rdb和aof文件
将docker容器内的数据保存进宿主机的磁盘中
运行一个带有容器卷存储功能的容器实例
docker run -it --privileged=true -v /宿主机绝对路径目录:/容器内目录 镜像名
5.2 能干嘛
*将运用与运行的环境打包镜像,run后形成容器实例运行 ,但是我们对数据的要求希望是持久化的
Docker容器产生的数据,如果不备份,那么当容器实例删除后,容器内的数据自然也就没有了。
为了能保存数据在docker中我们使用卷。
特点:
1:数据卷可在容器之间共享或重用数据
2:卷中的更改可以直接实时生效,爽
3:数据卷中的更改不会包含在镜像的更新中
4:数据卷的生命周期一直持续到没有容器使用它为止
5.3 数据卷案例
[root@VM-16-8-centos ~]# docker run -it --privileged=true -v /tmp/host_data:/tmp/docker_data --name=u1 ubuntu
root@2e431ba4f3bf:/# cd /tmp/docker_data/
root@2e431ba4f3bf:/tmp/docker_data# mkdir test_docker.txt
[root@VM-16-8-centos ~]# cd /tmp/host_data/
[root@VM-16-8-centos host_data]# ll
total 4
drwxr-xr-x 2 root root 4096 Apr 3 16:10 test_docker.txt
[root@VM-16-8-centos host_data]# mkdir test_host.txt
root@2e431ba4f3bf:/tmp/docker_data# ll
total 16
drwxr-xr-x 4 root root 4096 Apr 3 08:13 ./
drwxrwxrwt 1 root root 4096 Apr 3 08:10 ../
drwxr-xr-x 2 root root 4096 Apr 3 08:10 test_docker.txt/
drwxr-xr-x 2 root root 4096 Apr 3 08:13 test_host.txt/
可以发现,容器卷和挂载在本地的目录内容是一致的
查看改容器详细信息,也能查看到
docker inspect imageID
5.4 卷的继承
–volumes-from 要继承的容器名
[root@VM-16-8-centos ~]# docker run -it --privileged=true --volumes-from u1 --name u2 ubuntu
root@de0f937528ac:/# cd /tmp
root@de0f937528ac:/tmp# cd docker_data/
root@de0f937528ac:/tmp/docker_data# ll
total 16
drwxr-xr-x 4 root root 4096 Apr 3 08:13 ./
drwxrwxrwt 1 root root 4096 Apr 3 08:26 ../
drwxr-xr-x 2 root root 4096 Apr 3 08:10 test_docker.txt/
drwxr-xr-x 2 root root 4096 Apr 3 08:13 test_host.txt/
六、常用软件安装
6.1 Tomcat
[root@VM-16-8-centos ~]# docker pull tomcat
Using default tag: latest
latest: Pulling from library/tomcat
dbba69284b27: Pull complete
9baf437a1bad: Pull complete
6ade5c59e324: Pull complete
b19a994f6d4c: Pull complete
43c0aceedb57: Pull complete
24e7c71ec633: Pull complete
612cf131e488: Pull complete
dc655e69dd90: Pull complete
efe57b7441f6: Pull complete
8db51a0119f4: Pull complete
Digest: sha256:263f93ac29cb2dbba4275a4e647b448cb39a66334a6340b94da8bf13bde770aa
Status: Downloaded newer image for tomcat:latest
docker.io/library/tomcat:latest
[root@VM-16-8-centos ~]# docker images
REPOSITORY TAG IMAGE ID CREATED SIZE
124.221.228.148:5000/pyyubuntu 1.1 138c010d2c99 About an hour ago 109MB
ubuntu 1.0 138c010d2c99 About an hour ago 109MB
tomcat latest b00440a36b99 37 hours ago 680MB
registry latest d3241e050fc9 4 days ago 24.2MB
ubuntu latest ff0fea8310f3 2 weeks ago 72.8MB
新版tomcat,首页不在webapp下了
把webapps.dist目录换成webapps
当然我们不修改也是可以的,只需要下载tomcat8即可
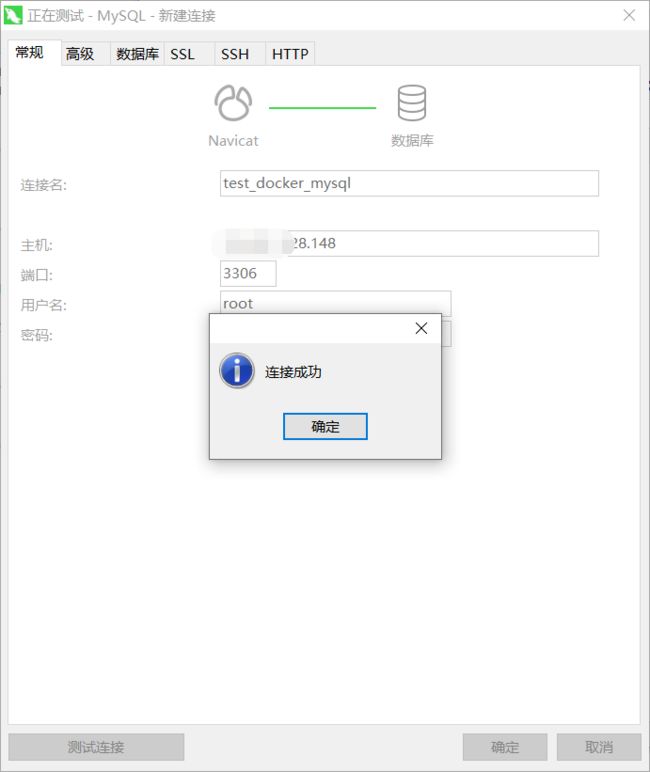
6.2 Mysql
[root@VM-16-8-centos ~]# docker run --name test-mysql -p 3306:3306 -e MYSQL_ROOT_PASSWORD=a -d mysql:5.7
b0fbfe45fce1ef90b4caf946efacbef0e50a425a25dec1d8e15902244e43747b
[root@VM-16-8-centos ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
b0fbfe45fce1 mysql:5.7 "docker-entrypoint.s…" 8 seconds ago Up 7 seconds 3306/tcp, 33060/tcp test-mysql
ce89351d51ec tomcat "catalina.sh run" 16 minutes ago Up 16 minutes 0.0.0.0:8080->8080/tcp funny_bose
de0f937528ac ubuntu "bash" 29 minutes ago Up 29 minutes u2
2e431ba4f3bf ubuntu "bash" 45 minutes ago Up 45 minutes u1
9dabfdf1b57d registry "/entrypoint.sh /etc…" About an hour ago Up About an hour 0.0.0.0:5000->5000/tcp sharp_brown
1f1ed5798baa ubuntu "/bin/bash" 6 hours ago Up 47 minutes vigorous_dewdney
[root@VM-16-8-centos ~]# docker exec -it b0fbfe45fce1 /bin/bash
root@b0fbfe45fce1:/# mysql -uroot -pa
mysql: [Warning] Using a password on the command line interface can be insecure.
Welcome to the MySQL monitor. Commands end with ; or \g.
Your MySQL connection id is 2
Server version: 5.7.37 MySQL Community Server (GPL)
Copyright (c) 2000, 2022, Oracle and/or its affiliates.
Oracle is a registered trademark of Oracle Corporation and/or its
affiliates. Other names may be trademarks of their respective
owners.
Type 'help;' or '\h' for help. Type '\c' to clear the current input statement.
mysql> create database test_mysql;
Query OK, 1 row affected (0.00 sec)
mysql> use test_mysql;
Database changed
mysql> create table docker_mysql (id int,name varchar(22));
Query OK, 0 rows affected (0.02 sec)
mysql> insert into docker_mysql values(1,'zs'),(2,'ls');
Query OK, 2 rows affected (0.01 sec)
Records: 2 Duplicates: 0 Warnings: 0
mysql> select count(*) Sum from docker_mysql;
+-----+
| Sum |
+-----+
| 2 |
+-----+
1 row in set (0.00 sec)
mysql> SHOW VARIABLES LIKE 'character%';
+--------------------------+----------------------------+
| Variable_name | Value |
+--------------------------+----------------------------+
| character_set_client | latin1 |
| character_set_connection | latin1 |
| character_set_database | latin1 |
| character_set_filesystem | binary |
| character_set_results | latin1 |
| character_set_server | latin1 |
| character_set_system | utf8 |
| character_sets_dir | /usr/share/mysql/charsets/ |
+--------------------------+----------------------------+
8 rows in set (0.00 sec)
navicat测试连接
6.2.1 编码问题的解决
插入中文会报错
在本地写好my.cnf文件
[root@VM-16-8-centos conf]# cat my.cnf
[client]
default_character_set=utf-8
[mysqld]
collation_server=utf8_general_ci
character_set_server=utf8
[root@VM-16-8-centos conf]# pwd
/pyy/mysql/conf
重新启动mysql容器实例再重新进入并查看字符编码
6.3 Redis
复制一份好的redis配置文件,
6.3.1 Redis配置文件
开启redis验证 可选
requirepass 123允许redis外地连接 必须
注释掉 # bind 127.0.0.1daemonize no
将daemonize yes注释起来或者 daemonize no设置,因为该配置和docker run中-d参数冲突,会导致容器一直启动失败开启redis数据持久化 appendonly yes 可选
[root@VM-16-8-centos ~]# cat /app/redis/redis.conf
# redis configuration file example.
####### Main configuration start #######
#注释掉bind 127.0.0.1,使redis可以外部访问
#bind 127.0.0.1
# 端口号
port 6379
#给redis设置密码
requirepass redis123
##redis持久化 默认是no
appendonly yes
#开启protected-mode保护模式,需配置bind ip或者设置访问密码
#关闭protected-mode模式,此时外部网络可以直接访问
protected-mode no
#是否开启集群
#cluster-enabled no
#集群的配置文件,该文件自动生成
#cluster-config-file nodes.conf
#集群的超时时间
#cluster-node-timeout 5000
#用守护线程的方式启动
daemonize no
#防止出现远程主机强迫关闭了一个现有的连接的错误 默认是300
tcp-keepalive 300
####### Main configuration end #######
timeout 0
tcp-backlog 511
# Note: these supervision methods only signal "process is ready."
# They do not enable continuous liveness pings back to your supervisor.
supervised no
# If a pid file is specified, Redis writes it where specified at startup
# and removes it at exit.
#
# When the server runs non daemonized, no pid file is created if none is
# specified in the configuration. When the server is daemonized, the pid file
# is used even if not specified, defaulting to "/var/run/redis.pid".
#
# Creating a pid file is best effort: if Redis is not able to create it
# nothing bad happens, the server will start and run normally.
pidfile /var/run/redis_6379.pid
# Specify the server verbosity level.
# This can be one of:
# debug (a lot of information, useful for development/testing)
# verbose (many rarely useful info, but not a mess like the debug level)
# notice (moderately verbose, what you want in production probably)
# warning (only very important / critical messages are logged)
loglevel notice
# Specify the log file name. Also the empty string can be used to force
# Redis to log on the standard output. Note that if you use standard
# output for logging but daemonize, logs will be sent to /dev/null
logfile ""
# To enable logging to the system logger, just set 'syslog-enabled' to yes,
# and optionally update the other syslog parameters to suit your needs.
# syslog-enabled no
# Specify the syslog identity.
# syslog-ident redis
# Specify the syslog facility. Must be USER or between LOCAL0-LOCAL7.
# syslog-facility local0
# Set the number of databases. The default database is DB 0, you can select
# a different one on a per-connection basis using SELECT where
# dbid is a number between 0 and 'databases'-1
databases 16
# By default Redis shows an ASCII art logo only when started to log to the
# standard output and if the standard output is a TTY. Basically this means
# that normally a logo is displayed only in interactive sessions.
#
# However it is possible to force the pre-4.0 behavior and always show a
# ASCII art logo in startup logs by setting the following option to yes.
always-show-logo yes
################################ SNAPSHOTTING ################################
#
# Save the DB on disk:
#
# save
#
# Will save the DB if both the given number of seconds and the given
# number of write operations against the DB occurred.
#
# In the example below the behaviour will be to save:
# after 900 sec (15 min) if at least 1 key changed
# after 300 sec (5 min) if at least 10 keys changed
# after 60 sec if at least 10000 keys changed
#
# Note: you can disable saving completely by commenting out all "save" lines.
#
# It is also possible to remove all the previously configured save
# points by adding a save directive with a single empty string argument
# like in the following example:
#
# save ""
save 900 1
save 300 10
save 60 10000
# By default Redis will stop accepting writes if RDB snapshots are enabled
# (at least one save point) and the latest background save failed.
# This will make the user aware (in a hard way) that data is not persisting
# on disk properly, otherwise chances are that no one will notice and some
# disaster will happen.
#
# If the background saving process will start working again Redis will
# automatically allow writes again.
#
# However if you have setup your proper monitoring of the Redis server
# and persistence, you may want to disable this feature so that Redis will
# continue to work as usual even if there are problems with disk,
# permissions, and so forth.
stop-writes-on-bgsave-error yes
# Compress string objects using LZF when dump .rdb databases?
# For default that's set to 'yes' as it's almost always a win.
# If you want to save some CPU in the saving child set it to 'no' but
# the dataset will likely be bigger if you have compressible values or keys.
rdbcompression yes
# Since version 5 of RDB a CRC64 checksum is placed at the end of the file.
# This makes the format more resistant to corruption but there is a performance
# hit to pay (around 10%) when saving and loading RDB files, so you can disable it
# for maximum performances.
#
# RDB files created with checksum disabled have a checksum of zero that will
# tell the loading code to skip the check.
rdbchecksum yes
# The filename where to dump the DB
dbfilename dump.rdb
# Remove RDB files used by replication in instances without persistence
# enabled. By default this option is disabled, however there are environments
# where for regulations or other security concerns, RDB files persisted on
# disk by masters in order to feed replicas, or stored on disk by replicas
# in order to load them for the initial synchronization, should be deleted
# ASAP. Note that this option ONLY WORKS in instances that have both AOF
# and RDB persistence disabled, otherwise is completely ignored.
#
# An alternative (and sometimes better) way to obtain the same effect is
# to use diskless replication on both master and replicas instances. However
# in the case of replicas, diskless is not always an option.
rdb-del-sync-files no
# The working directory.
#
# The DB will be written inside this directory, with the filename specified
# above using the 'dbfilename' configuration directive.
#
# The Append Only File will also be created inside this directory.
#
# Note that you must specify a directory here, not a file name.
dir ./
# When a replica loses its connection with the master, or when the replication
# is still in progress, the replica can act in two different ways:
#
# 1) if replica-serve-stale-data is set to 'yes' (the default) the replica will
# still reply to client requests, possibly with out of date data, or the
# data set may just be empty if this is the first synchronization.
#
# 2) if replica-serve-stale-data is set to 'no' the replica will reply with
# an error "SYNC with master in progress" to all the kind of commands
# but to INFO, replicaOF, AUTH, PING, SHUTDOWN, REPLCONF, ROLE, CONFIG,
# SUBSCRIBE, UNSUBSCRIBE, PSUBSCRIBE, PUNSUBSCRIBE, PUBLISH, PUBSUB,
# COMMAND, POST, HOST: and LATENCY.
#
replica-serve-stale-data yes
# You can configure a replica instance to accept writes or not. Writing against
# a replica instance may be useful to store some ephemeral data (because data
# written on a replica will be easily deleted after resync with the master) but
# may also cause problems if clients are writing to it because of a
# misconfiguration.
#
# Since Redis 2.6 by default replicas are read-only.
#
# Note: read only replicas are not designed to be exposed to untrusted clients
# on the internet. It's just a protection layer against misuse of the instance.
# Still a read only replica exports by default all the administrative commands
# such as CONFIG, DEBUG, and so forth. To a limited extent you can improve
# security of read only replicas using 'rename-command' to shadow all the
# administrative / dangerous commands.
replica-read-only yes
# When diskless replication is used, the master waits a configurable amount of
# time (in seconds) before starting the transfer in the hope that multiple
# replicas will arrive and the transfer can be parallelized.
#
# With slow disks and fast (large bandwidth) networks, diskless replication
# works better.
repl-diskless-sync no
# When diskless replication is enabled, it is possible to configure the delay
# the server waits in order to spawn the child that transfers the RDB via socket
# to the replicas.
#
# This is important since once the transfer starts, it is not possible to serve
# new replicas arriving, that will be queued for the next RDB transfer, so the
# server waits a delay in order to let more replicas arrive.
#
# The delay is specified in seconds, and by default is 5 seconds. To disable
# it entirely just set it to 0 seconds and the transfer will start ASAP.
repl-diskless-sync-delay 5
# In many cases the disk is slower than the network, and storing and loading
# the RDB file may increase replication time (and even increase the master's
# Copy on Write memory and salve buffers).
# However, parsing the RDB file directly from the socket may mean that we have
# to flush the contents of the current database before the full rdb was
# received. For this reason we have the following options:
#
# "disabled" - Don't use diskless load (store the rdb file to the disk first)
# "on-empty-db" - Use diskless load only when it is completely safe.
# "swapdb" - Keep a copy of the current db contents in RAM while parsing
# the data directly from the socket. note that this requires
# sufficient memory, if you don't have it, you risk an OOM kill.
repl-diskless-load disabled
# Disable TCP_NODELAY on the replica socket after SYNC?
#
# If you select "yes" Redis will use a smaller number of TCP packets and
# less bandwidth to send data to replicas. But this can add a delay for
# the data to appear on the replica side, up to 40 milliseconds with
# Linux kernels using a default configuration.
#
# If you select "no" the delay for data to appear on the replica side will
# be reduced but more bandwidth will be used for replication.
#
# By default we optimize for low latency, but in very high traffic conditions
# or when the master and replicas are many hops away, turning this to "yes" may
# be a good idea.
repl-disable-tcp-nodelay no
# The replica priority is an integer number published by Redis in the INFO
# output. It is used by Redis Sentinel in order to select a replica to promote
# into a master if the master is no longer working correctly.
#
# A replica with a low priority number is considered better for promotion, so
# for instance if there are three replicas with priority 10, 100, 25 Sentinel
# will pick the one with priority 10, that is the lowest.
#
# However a special priority of 0 marks the replica as not able to perform the
# role of master, so a replica with priority of 0 will never be selected by
# Redis Sentinel for promotion.
#
# By default the priority is 100.
replica-priority 100
# ACL LOG
#
# The ACL Log tracks failed commands and authentication events associated
# with ACLs. The ACL Log is useful to troubleshoot failed commands blocked
# by ACLs. The ACL Log is stored in memory. You can reclaim memory with
# ACL LOG RESET. Define the maximum entry length of the ACL Log below.
acllog-max-len 128
# Using an external ACL file
#
# Instead of configuring users here in this file, it is possible to use
# a stand-alone file just listing users. The two methods cannot be mixed:
# if you configure users here and at the same time you activate the exteranl
# ACL file, the server will refuse to start.
#
# The format of the external ACL user file is exactly the same as the
# format that is used inside redis.conf to describe users.
#
# aclfile /etc/redis/users.acl
# Command renaming (DEPRECATED).
#
# ------------------------------------------------------------------------
# WARNING: avoid using this option if possible. Instead use ACLs to remove
# commands from the default user, and put them only in some admin user you
# create for administrative purposes.
# ------------------------------------------------------------------------
#
# It is possible to change the name of dangerous commands in a shared
# environment. For instance the CONFIG command may be renamed into something
# hard to guess so that it will still be available for internal-use tools
# but not available for general clients.
#
# Example:
#
# rename-command CONFIG b840fc02d524045429941cc15f59e41cb7be6c52
#
# It is also possible to completely kill a command by renaming it into
# an empty string:
#
# rename-command CONFIG ""
#
# Please note that changing the name of commands that are logged into the
# AOF file or transmitted to replicas may cause problems.
################################### CLIENTS ####################################
# Set the max number of connected clients at the same time. By default
# this limit is set to 10000 clients, however if the Redis server is not
# able to configure the process file limit to allow for the specified limit
# the max number of allowed clients is set to the current file limit
# minus 32 (as Redis reserves a few file descriptors for internal uses).
#
# Once the limit is reached Redis will close all the new connections sending
# an error 'max number of clients reached'.
#
# IMPORTANT: When Redis Cluster is used, the max number of connections is also
# shared with the cluster bus: every node in the cluster will use two
# connections, one incoming and another outgoing. It is important to size the
# limit accordingly in case of very large clusters.
#
# maxclients 10000
############################## MEMORY MANAGEMENT ################################
# Set a memory usage limit to the specified amount of bytes.
# When the memory limit is reached Redis will try to remove keys
# according to the eviction policy selected (see maxmemory-policy).
#
# If Redis can't remove keys according to the policy, or if the policy is
# set to 'noeviction', Redis will start to reply with errors to commands
# that would use more memory, like SET, LPUSH, and so on, and will continue
# to reply to read-only commands like GET.
#
# This option is usually useful when using Redis as an LRU or LFU cache, or to
# set a hard memory limit for an instance (using the 'noeviction' policy).
#
# WARNING: If you have replicas attached to an instance with maxmemory on,
# the size of the output buffers needed to feed the replicas are subtracted
# from the used memory count, so that network problems / resyncs will
# not trigger a loop where keys are evicted, and in turn the output
# buffer of replicas is full with DELs of keys evicted triggering the deletion
# of more keys, and so forth until the database is completely emptied.
#
# In short... if you have replicas attached it is suggested that you set a lower
# limit for maxmemory so that there is some free RAM on the system for replica
# output buffers (but this is not needed if the policy is 'noeviction').
#
# maxmemory " if needed.
latency-monitor-threshold 0
# By default all notifications are disabled because most users don't need
# this feature and the feature has some overhead. Note that if you don't
# specify at least one of K or E, no events will be delivered.
notify-keyspace-events ""
############################### ADVANCED CONFIG ###############################
# Hashes are encoded using a memory efficient data structure when they have a
# small number of entries, and the biggest entry does not exceed a given
# threshold. These thresholds can be configured using the following directives.
hash-max-ziplist-entries 512
hash-max-ziplist-value 64
# Lists are also encoded in a special way to save a lot of space.
# The number of entries allowed per internal list node can be specified
# as a fixed maximum size or a maximum number of elements.
# For a fixed maximum size, use -5 through -1, meaning:
# -5: max size: 64 Kb <-- not recommended for normal workloads
# -4: max size: 32 Kb <-- not recommended
# -3: max size: 16 Kb <-- probably not recommended
# -2: max size: 8 Kb <-- good
# -1: max size: 4 Kb <-- good
# Positive numbers mean store up to _exactly_ that number of elements
# per list node.
# The highest performing option is usually -2 (8 Kb size) or -1 (4 Kb size),
# but if your use case is unique, adjust the settings as necessary.
list-max-ziplist-size -2
# Lists may also be compressed.
# Compress depth is the number of quicklist ziplist nodes from *each* side of
# the list to *exclude* from compression. The head and tail of the list
# are always uncompressed for fast push/pop operations. Settings are:
# 0: disable all list compression
# 1: depth 1 means "don't start compressing until after 1 node into the list,
# going from either the head or tail"
# So: [head]->node->node->...->node->[tail]
# [head], [tail] will always be uncompressed; inner nodes will compress.
# 2: [head]->[next]->node->node->...->node->[prev]->[tail]
# 2 here means: don't compress head or head->next or tail->prev or tail,
# but compress all nodes between them.
# 3: [head]->[next]->[next]->node->node->...->node->[prev]->[prev]->[tail]
# etc.
list-compress-depth 0
# Sets have a special encoding in just one case: when a set is composed
# of just strings that happen to be integers in radix 10 in the range
# of 64 bit signed integers.
# The following configuration setting sets the limit in the size of the
# set in order to use this special memory saving encoding.
set-max-intset-entries 512
# Similarly to hashes and lists, sorted sets are also specially encoded in
# order to save a lot of space. This encoding is only used when the length and
# elements of a sorted set are below the following limits:
zset-max-ziplist-entries 128
zset-max-ziplist-value 64
# The suggested value is ~ 3000 in order to have the benefits of
# the space efficient encoding without slowing down too much PFADD,
# which is O(N) with the sparse encoding. The value can be raised to
# ~ 10000 when CPU is not a concern, but space is, and the data set is
# composed of many HyperLogLogs with cardinality in the 0 - 15000 range.
hll-sparse-max-bytes 3000
# Streams macro node max size / items. The stream data structure is a radix
# tree of big nodes that encode multiple items inside. Using this configuration
# it is possible to configure how big a single node can be in bytes, and the
# maximum number of items it may contain before switching to a new node when
# appending new stream entries. If any of the following settings are set to
# zero, the limit is ignored, so for instance it is possible to set just a
# max entires limit by setting max-bytes to 0 and max-entries to the desired
# value.
stream-node-max-bytes 4096
stream-node-max-entries 100
# use "activerehashing yes" if you don't have such hard requirements but
# want to free memory asap when possible.
activerehashing yes
# Instead there is a default limit for pubsub and replica clients, since
# subscribers and replicas receive data in a push fashion.
#
# Both the hard or the soft limit can be disabled by setting them to zero.
client-output-buffer-limit normal 0 0 0
client-output-buffer-limit replica 256mb 64mb 60
client-output-buffer-limit pubsub 32mb 8mb 60
# Client query buffers accumulate new commands. They are limited to a fixed
# amount by default in order to avoid that a protocol desynchronization (for
# instance due to a bug in the client) will lead to unbound memory usage in
# the query buffer. However you can configure it here if you have very special
# needs, such us huge multi/exec requests or alike.
#
# client-query-buffer-limit 1gb
# In the Redis protocol, bulk requests, that are, elements representing single
# strings, are normally limited ot 512 mb. However you can change this limit
# here.
#
# proto-max-bulk-len 512mb
# The range is between 1 and 500, however a value over 100 is usually not
# a good idea. Most users should use the default of 10 and raise this up to
# 100 only in environments where very low latency is required.
hz 10
# When dynamic HZ is enabled, the actual configured HZ will be used
# as a baseline, but multiples of the configured HZ value will be actually
# used as needed once more clients are connected. In this way an idle
# instance will use very little CPU time while a busy instance will be
# more responsive.
dynamic-hz yes
# When a child rewrites the AOF file, if the following option is enabled
# the file will be fsync-ed every 32 MB of data generated. This is useful
# in order to commit the file to the disk more incrementally and avoid
# big latency spikes.
aof-rewrite-incremental-fsync yes
# When redis saves RDB file, if the following option is enabled
# the file will be fsync-ed every 32 MB of data generated. This is useful
# in order to commit the file to the disk more incrementally and avoid
# big latency spikes.
rdb-save-incremental-fsync yes
# Jemalloc background thread for purging will be enabled by default
jemalloc-bg-thread yes
6.3.2 启动实例
因为前面设置的有redis认证密码,所以输入auth 密码即可完成认证
[root@VM-16-8-centos ~]# docker run -p 6379:6379 --name redis2 --privileged=true -v /app/redis/redis.conf:/etc/redis/redis.conf -v /app/data:/data -d redis:6.0.8 redis-server /etc/redis/redis.conf --appendonly yes
561618b1a13521e7119536ed3cdaf3e4344c2962d1c968acc01a60cc802af7d0
[root@VM-16-8-centos ~]# docker ps
CONTAINER ID IMAGE COMMAND CREATED STATUS PORTS NAMES
561618b1a135 redis:6.0.8 "docker-entrypoint.s…" 45 minutes ago Up 45 minutes 0.0.0.0:6379->6379/tcp redis2
[root@VM-16-8-centos ~]# docker exec -it 561618b1a135 bash
root@561618b1a135:/data# redis-cli
127.0.0.1:6379> auth redis123
OK
127.0.0.1:6379> set k1 v1
OK
127.0.0.1:6379> get k1
"v1"
127.0.0.1:6379>