编译国产openEuler 22.03 LTS系统OpenSSH 9.4的rpm安装包
目前OpenSSH版本已至9.4,其作为操作系统底层管理平台软件,需要保持更新以免遭受安全攻击,编译生成rpm包是生产环境中批量升级的最佳途径。本文在国产openEuler 22.03 LTS系统上完成OpenSSH 9.4的编译工作。
一、准备编译环境:
1、发布一台虚拟机,最小化安装openEuler 22.03 LTS,查看系统信息如下:
[root@localhost ~]# cat /etc/os-release
NAME="openEuler"
VERSION="22.03 LTS"
ID="openEuler"
VERSION_ID="22.03"
PRETTY_NAME="openEuler 22.03 LTS"
ANSI_COLOR="0;31"
[root@localhost ~]# rpm -qa|grep openssh
openssh-8.8p1-2.oe2203.x86_64
openssh-server-8.8p1-2.oe2203.x86_64
openssh-clients-8.8p1-2.oe2203.x86_642、 修改系统源为阿里源
[root@localhost ~]# cp /etc/yum.repos.d/openEuler.repo{,.bak}
[root@localhost ~]# sed -i "s/repo.openeuler.org/mirrors.aliyun.com\/openeuler/g" /etc/yum.repos.d/openEuler.repo
[root@localhost ~]# yum install tree -y
Last metadata expiration check: 0:02:14 ago on 2023年06月05日 星期一 14时42分20秒.
Dependencies resolved.
=========================================================================================================================================================================================================================================
Package Architecture Version Repository Size
=========================================================================================================================================================================================================================================
Installing:
tree x86_64 1.8.0-2.oe2203 OS 52 k
Transaction Summary
=========================================================================================================================================================================================================================================
Install 1 Package
Total download size: 52 k
Installed size: 119 k
Downloading Packages:
tree-1.8.0-2.oe2203.x86_64.rpm 149 kB/s | 52 kB 00:00
-----------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------------
Total 147 kB/s | 52 kB 00:00
Running transaction check
Transaction check succeeded.
Running transaction test
Transaction test succeeded.
Running transaction
Preparing : 1/1
Installing : tree-1.8.0-2.oe2203.x86_64 1/1
Verifying : tree-1.8.0-2.oe2203.x86_64 1/1
Installed:
tree-1.8.0-2.oe2203.x86_64
Complete!3、 准备相关目录
[root@localhost ~]# cd ~
[root@localhost ~]# mkdir -p rpmbuild/{SOURCES,SPECS}
[root@localhost ~]# tree
.
├── anaconda-ks.cfg
└── rpmbuild
├── SOURCES
└── SPECS
3 directories, 1 file4、 准备源文件
[root@localhost ~]# cd rpmbuild/SOURCES/
[root@localhost SOURCES]# wget https://ftp.openbsd.org/pub/OpenBSD/OpenSSH/portable/openssh-9.4p1.tar.gz --no-check-certificate
--2023-06-05 14:46:27-- https://ftp.openbsd.org/pub/OpenBSD/OpenSSH/portable/openssh-9.4p1.tar.gz
正在解析主机 ftp.openbsd.org (ftp.openbsd.org)... 199.185.178.81
正在连接 ftp.openbsd.org (ftp.openbsd.org)|199.185.178.81|:443... 已连接。
警告: “ftp.openbsd.org” 的证书不可信。
警告: “ftp.openbsd.org” 的证书还未生效。
证书还未激活
已发出 HTTP 请求,正在等待回应... 200 OK
长度:1845094 (1.8M) [text/plain]
正在保存至: “openssh-9.4p1.tar.gz”
openssh-9.4p1.tar.gz 100%[=====================================================================================================================================>] 1.76M 111KB/s 用时 26s
2023-06-05 14:46:56 (70.4 KB/s) - 已保存 “openssh-9.4p1.tar.gz” [1845094/1845094])
[root@localhost SOURCES]# wget https://src.fedoraproject.org/repo/pkgs/openssh/x11-ssh-askpass-1.2.4.1.tar.gz/8f2e41f3f7eaa8543a2440454637f3c3/x11-ssh-askpass-1.2.4.1.tar.gz
...
2023-09-05 18:41:14 (114 KB/s) - 已保存 “x11-ssh-askpass-1.2.4.1.tar.gz” [29229/29229]
[root@localhost SOURCES]# wget https://www.openssl.org/source/openssl-1.1.1v.tar.gz --no-check-certificate
...
2023-09-06 21:56:18 (901 KB/s) - 已保存 “openssl-1.1.1v.tar.gz” [9893443/9893443])
[root@localhost SOURCES]# vi sshd.pam.oe2203
[root@localhost SOURCES]# cat sshd.pam.oe2203
#%PAM-1.0
auth substack password-auth
auth include postlogin
account required pam_sepermit.so
account required pam_nologin.so
account include password-auth
password include password-auth
# pam_selinux.so close should be the first session rule
session required pam_selinux.so close
session required pam_loginuid.so
# pam_selinux.so open should only be followed by sessions to be executed in the user context
session required pam_selinux.so open env_params
session required pam_namespace.so
session optional pam_keyinit.so force revoke
session optional pam_motd.so
session include password-auth
session include postlogin
5、 安装编译工具
[root@localhost SOURCES]# cd ../SPECS
[root@localhost SPECS]# yum install rpm-build zlib-devel openssl-devel gcc perl-devel pam-devel -y
Last metadata expiration check: 0:14:53 ago on 2023年06月05日 星期一 14时42分20秒.
Package gcc-10.3.1-10.oe2203.x86_64 is already installed.
Package perl-devel-4:5.34.0-3.oe2203.x86_64 is already installed.
Dependencies resolved.
...
Upgraded:
cpp-10.3.1-11.oe2203.x86_64 gcc-10.3.1-11.oe2203.x86_64 libgcc-10.3.1-11.oe2203.x86_64 libgomp-10.3.1-11.oe2203.x86_64 openssl-1:1.1.1m-22.oe2203.x86_64 openssl-libs-1:1.1.1m-22.oe2203.x86_64
pam-1.5.2-6.oe2203.x86_64 perl-4:5.34.0-9.oe2203.x86_64 perl-devel-4:5.34.0-9.oe2203.x86_64 perl-libs-4:5.34.0-9.oe2203.x86_64 python3-rpm-4.17.0-14.oe2203.x86_64 rpm-4.17.0-14.oe2203.x86_64
rpm-libs-4.17.0-14.oe2203.x86_64 zlib-1.2.11-22.oe2203.x86_64
Installed:
babeltrace-1.5.8-2.oe2203.x86_64 debugedit-5.0-2.oe2203.x86_64 dwz-0.14-3.oe2203.x86_64 e2fsprogs-devel-1.46.4-7.oe2203.x86_64 gdb-headless-11.1-1.oe2203.x86_64 keyutils-libs-devel-1.6.3-3.oe2203.x86_64
krb5-devel-1.19.2-2.oe2203.x86_64 libipt-2.0.4-1.oe2203.x86_64 libselinux-devel-3.3-1.oe2203.x86_64 libsepol-devel-3.3-2.oe2203.x86_64 libverto-devel-0.3.2-1.oe2203.x86_64 openssl-devel-1:1.1.1m-22.oe2203.x86_64
pam-devel-1.5.2-6.oe2203.x86_64 patch-2.7.6-12.oe2203.x86_64 pcre2-devel-10.39-1.oe2203.x86_64 rpm-build-4.17.0-14.oe2203.x86_64 zlib-devel-1.2.11-22.oe2203.x86_64
Complete!6、 编写spec文件
[root@localhost SPECS]# vi /root/rpmbuild/SPECS/openssh.spec
[root@localhost SPECS]# cat /root/rpmbuild/SPECS/openssh.spec
%{?!opensslver: %global opensslver 1.1.1v}
%{?!opensshver: %global opensshver 9.4p1}
%define static_openssl 1
# wheather to build openssl
%global no_build_openssl 0
#if defined openssl_dir, don't build it
%{?openssl_dir:%global no_build_openssl 1}
%global ver %{?opensshver}
%global rel %{?opensshpkgrel}%{?dist}oe2203
# OpenSSH privilege separation requires a user & group ID
%global sshd_uid 74
%global sshd_gid 74
# Version of ssh-askpass
%global aversion 1.2.4.1
# Do we want to disable building of x11-askpass? (1=yes 0=no)
%global no_x11_askpass 1
# Do we want to disable building of gnome-askpass? (1=yes 0=no)
%global no_gnome_askpass 1
# Do we want to link against a static libcrypto? (1=yes 0=no)
%global static_libcrypto 0
# Do we want smartcard support (1=yes 0=no)
%global scard 0
# Use GTK2 instead of GNOME in gnome-ssh-askpass
%global gtk2 1
# Use build6x options for older RHEL builds
# RHEL 7 not yet supported
%if 0%{?rhel} > 6
%global build6x 0
%else
%global build6x 0
%endif
%if 0%{?fedora} >= 26
%global compat_openssl 1
%else
%global compat_openssl 0
%endif
# Do we want kerberos5 support (1=yes 0=no)
%global kerberos5 1
# Reserve options to override askpass settings with:
# rpm -ba|--rebuild --define 'skip_xxx 1'
%{?skip_x11_askpass:%global no_x11_askpass 1}
%{?skip_gnome_askpass:%global no_gnome_askpass 1}
# Add option to build without GTK2 for older platforms with only GTK+.
# RedHat <= 7.2 and Red Hat Advanced Server 2.1 are examples.
# rpm -ba|--rebuild --define 'no_gtk2 1'
%{?no_gtk2:%global gtk2 0}
# Is this a build for RHL 6.x or earlier?
%{?build_6x:%global build6x 1}
# If this is RHL 6.x, the default configuration has sysconfdir in /usr/etc.
%if %{build6x}
%global _sysconfdir /etc
%endif
# Options for static OpenSSL link:
# rpm -ba|--rebuild --define "static_openssl 1"
%{?static_openssl:%global static_libcrypto 1}
# Options for Smartcard support: (needs libsectok and openssl-engine)
# rpm -ba|--rebuild --define "smartcard 1"
%{?smartcard:%global scard 1}
# Is this a build for the rescue CD (without PAM, with MD5)? (1=yes 0=no)
%global rescue 0
%{?build_rescue:%global rescue 1}
# Turn off some stuff for resuce builds
%if %{rescue}
%global kerberos5 0
%endif
Summary: The OpenSSH implementation of SSH protocol version 2.
Name: openssh
Version: %{ver}
%if %{rescue}
Release: %{rel}rescue
%else
Release: %{rel}
%endif
URL: https://www.openssh.com/portable.html
Source0: https://ftp.openbsd.org/pub/OpenBSD/OpenSSH/portable/openssh-%{version}.tar.gz
Source1: http://www.jmknoble.net/software/x11-ssh-askpass/x11-ssh-askpass-%{aversion}.tar.gz
Source2: sshd.pam.oe2203
%if ! %{no_build_openssl}
Source3: https://www.openssl.org/source/openssl-%{opensslver}.tar.gz
%endif
License: BSD
Group: Applications/Internet
BuildRoot: %{_tmppath}/%{name}-%{version}-buildroot
Obsoletes: ssh
%if %{build6x}
PreReq: initscripts >= 5.00
%else
Requires: initscripts >= 5.20
%endif
BuildRequires: perl
#%if %{compat_openssl}
#BuildRequires: compat-openssl10-devel
#%else
#BuildRequires: openssl-devel >= 1.0.1
#BuildRequires: openssl-devel < 1.1
#%endif
BuildRequires: /bin/login
%if ! %{build6x}
BuildRequires: glibc-devel, pam
%else
BuildRequires: /usr/include/security/pam_appl.h
%endif
%if ! %{no_x11_askpass}
BuildRequires: /usr/include/X11/Xlib.h
# Xt development tools
BuildRequires: libXt-devel
# Provides xmkmf
BuildRequires: imake
# Rely on relatively recent gtk
%if %{gtk2}
BuildRequires: gtk2-devel
%endif
%endif
%if ! %{no_gnome_askpass}
BuildRequires: pkgconfig
%endif
%if %{kerberos5}
BuildRequires: krb5-devel
BuildRequires: krb5-libs
%endif
%package clients
Summary: OpenSSH clients.
Requires: openssh = %{version}-%{release}
Group: Applications/Internet
Obsoletes: ssh-clients
%package server
Summary: The OpenSSH server daemon.
Group: System Environment/Daemons
Obsoletes: ssh-server
Requires: openssh = %{version}-%{release}, chkconfig >= 0.9
%if ! %{build6x}
Requires: /etc/pam.d/system-auth
%endif
%package askpass
Summary: A passphrase dialog for OpenSSH and X.
Group: Applications/Internet
Requires: openssh = %{version}-%{release}
Obsoletes: ssh-extras
%package askpass-gnome
Summary: A passphrase dialog for OpenSSH, X, and GNOME.
Group: Applications/Internet
Requires: openssh = %{version}-%{release}
Obsoletes: ssh-extras
%description
SSH (Secure SHell) is a program for logging into and executing
commands on a remote machine. SSH is intended to replace rlogin and
rsh, and to provide secure encrypted communications between two
untrusted hosts over an insecure network. X11 connections and
arbitrary TCP/IP ports can also be forwarded over the secure channel.
OpenSSH is OpenBSD's version of the last free version of SSH, bringing
it up to date in terms of security and features, as well as removing
all patented algorithms to separate libraries.
This package includes the core files necessary for both the OpenSSH
client and server. To make this package useful, you should also
install openssh-clients, openssh-server, or both.
%description clients
OpenSSH is a free version of SSH (Secure SHell), a program for logging
into and executing commands on a remote machine. This package includes
the clients necessary to make encrypted connections to SSH servers.
You'll also need to install the openssh package on OpenSSH clients.
%description server
OpenSSH is a free version of SSH (Secure SHell), a program for logging
into and executing commands on a remote machine. This package contains
the secure shell daemon (sshd). The sshd daemon allows SSH clients to
securely connect to your SSH server. You also need to have the openssh
package installed.
%description askpass
OpenSSH is a free version of SSH (Secure SHell), a program for logging
into and executing commands on a remote machine. This package contains
an X11 passphrase dialog for OpenSSH.
%description askpass-gnome
OpenSSH is a free version of SSH (Secure SHell), a program for logging
into and executing commands on a remote machine. This package contains
an X11 passphrase dialog for OpenSSH and the GNOME GUI desktop
environment.
%prep
%if ! %{no_x11_askpass}
%setup -q -a 1
%else
%setup -q
%endif
%if ! %{no_build_openssl}
%define openssl_dir %{_builddir}/%{name}-%{version}/openssl
mkdir -p openssl
tar xfz %{SOURCE3} --strip-components=1 -C openssl
pushd openssl
./config shared zlib -fPIC
make %{?_smp_mflags}
popd
%endif
%build
%if %{rescue}
CFLAGS="$RPM_OPT_FLAGS -Os"; export CFLAGS
%endif
export LD_LIBRARY_PATH="%{openssl_dir}"
%configure \
--sysconfdir=%{_sysconfdir}/ssh \
--libexecdir=%{_libexecdir}/openssh \
--datadir=%{_datadir}/openssh \
--with-default-path=/usr/local/bin:/bin:/usr/bin \
--with-superuser-path=/usr/local/sbin:/usr/local/bin:/sbin:/bin:/usr/sbin:/usr/bin \
--with-privsep-path=%{_var}/empty/sshd \
--with-md5-passwords \
--mandir=%{_mandir} \
--with-mantype=man \
--disable-strip \
--with-ssl-dir="%{openssl_dir}" \
%if %{scard}
--with-smartcard \
%endif
%if %{rescue}
--without-pam \
%else
--with-pam \
%endif
%if %{kerberos5}
--with-kerberos5=$K5DIR \
%endif
%if %{static_libcrypto}
#perl -pi -e "s|-lcrypto|%{_libdir}/libcrypto.a|g" Makefile
perl -pi -e "s|-lcrypto|%{openssl_dir}/libcrypto.a -lpthread|g" Makefile
%endif
make %{?_smp_mflags}
%if ! %{no_x11_askpass}
pushd x11-ssh-askpass-%{aversion}
%configure --libexecdir=%{_libexecdir}/openssh
xmkmf -a
make -j
popd
%endif
# Define a variable to toggle gnome1/gtk2 building. This is necessary
# because RPM doesn't handle nested %if statements.
%if %{gtk2}
gtk2=yes
%else
gtk2=no
%endif
%if ! %{no_gnome_askpass}
pushd contrib
if [ $gtk2 = yes ] ; then
make gnome-ssh-askpass2
mv gnome-ssh-askpass2 gnome-ssh-askpass
else
make gnome-ssh-askpass1
mv gnome-ssh-askpass1 gnome-ssh-askpass
fi
popd
%endif
%install
rm -rf $RPM_BUILD_ROOT
mkdir -p -m755 $RPM_BUILD_ROOT%{_sysconfdir}/ssh
mkdir -p -m755 $RPM_BUILD_ROOT%{_libexecdir}/openssh
mkdir -p -m755 $RPM_BUILD_ROOT%{_var}/empty/sshd
make install DESTDIR=$RPM_BUILD_ROOT
echo -e 'PubkeyAcceptedAlgorithms +ssh-rsa\nUsePAM yes\nPermitRootLogin yes\nUseDNS no' >> $RPM_BUILD_ROOT/etc/ssh/sshd_config
install -d $RPM_BUILD_ROOT/etc/pam.d/
install -d $RPM_BUILD_ROOT/etc/rc.d/init.d
install -d $RPM_BUILD_ROOT%{_libexecdir}/openssh
install -m755 contrib/ssh-copy-id $RPM_BUILD_ROOT/usr/bin/ssh-copy-id
install -m644 %{SOURCE2} $RPM_BUILD_ROOT/etc/pam.d/sshd
install -m755 contrib/redhat/sshd.init $RPM_BUILD_ROOT/etc/rc.d/init.d/sshd
%if ! %{no_x11_askpass}
install x11-ssh-askpass-%{aversion}/x11-ssh-askpass $RPM_BUILD_ROOT%{_libexecdir}/openssh/x11-ssh-askpass
ln -s x11-ssh-askpass $RPM_BUILD_ROOT%{_libexecdir}/openssh/ssh-askpass
%endif
%if ! %{no_gnome_askpass}
install contrib/gnome-ssh-askpass $RPM_BUILD_ROOT%{_libexecdir}/openssh/gnome-ssh-askpass
%endif
%if ! %{scard}
rm -f $RPM_BUILD_ROOT/usr/share/openssh/Ssh.bin
%endif
%if ! %{no_gnome_askpass}
install -m 755 -d $RPM_BUILD_ROOT%{_sysconfdir}/profile.d/
install -m 755 contrib/redhat/gnome-ssh-askpass.csh $RPM_BUILD_ROOT%{_sysconfdir}/profile.d/
install -m 755 contrib/redhat/gnome-ssh-askpass.sh $RPM_BUILD_ROOT%{_sysconfdir}/profile.d/
%endif
perl -pi -e "s|$RPM_BUILD_ROOT||g" $RPM_BUILD_ROOT%{_mandir}/man*/*
%clean
rm -rf $RPM_BUILD_ROOT
%triggerun server -- ssh-server
if [ "$1" != 0 -a -r /var/run/sshd.pid ] ; then
touch /var/run/sshd.restart
fi
%triggerun server -- openssh-server < 2.5.0p1
# Count the number of HostKey and HostDsaKey statements we have.
gawk 'BEGIN {IGNORECASE=1}
/^hostkey/ || /^hostdsakey/ {sawhostkey = sawhostkey + 1}
END {exit sawhostkey}' /etc/ssh/sshd_config
# And if we only found one, we know the client was relying on the old default
# behavior, which loaded the the SSH2 DSA host key when HostDsaKey wasn't
# specified. Now that HostKey is used for both SSH1 and SSH2 keys, specifying
# one nullifies the default, which would have loaded both.
if [ $? -eq 1 ] ; then
echo HostKey /etc/ssh/ssh_host_rsa_key >> /etc/ssh/sshd_config
echo HostKey /etc/ssh/ssh_host_dsa_key >> /etc/ssh/sshd_config
fi
%triggerpostun server -- ssh-server
if [ "$1" != 0 ] ; then
/sbin/chkconfig --add sshd
if test -f /var/run/sshd.restart ; then
rm -f /var/run/sshd.restart
/sbin/service sshd start > /dev/null 2>&1 || :
fi
fi
%pre server
%{_sbindir}/groupadd -r -g %{sshd_gid} sshd 2>/dev/null || :
%{_sbindir}/useradd -d /var/empty/sshd -s /bin/false -u %{sshd_uid} \
-g sshd -M -r sshd 2>/dev/null || :
%post server
/sbin/chkconfig --add sshd
%postun server
/sbin/service sshd condrestart > /dev/null 2>&1 || :
%preun server
if [ "$1" = 0 ]
then
/sbin/service sshd stop > /dev/null 2>&1 || :
/sbin/chkconfig --del sshd
fi
%files
%defattr(-,root,root)
%doc CREDITS ChangeLog INSTALL LICENCE OVERVIEW README* PROTOCOL* TODO
%attr(0755,root,root) %{_bindir}/scp
%attr(0644,root,root) %{_mandir}/man1/scp.1*
%attr(0755,root,root) %dir %{_sysconfdir}/ssh
%attr(0600,root,root) %config(noreplace) %{_sysconfdir}/ssh/moduli
%if ! %{rescue}
%attr(0755,root,root) %{_bindir}/ssh-keygen
%attr(0755,root,root) %{_bindir}/ssh-copy-id
%attr(0644,root,root) %{_mandir}/man1/ssh-keygen.1*
%attr(0755,root,root) %dir %{_libexecdir}/openssh
%attr(4711,root,root) %{_libexecdir}/openssh/ssh-keysign
%attr(0755,root,root) %{_libexecdir}/openssh/ssh-pkcs11-helper
%attr(0755,root,root) %{_libexecdir}/openssh/ssh-sk-helper
%attr(0644,root,root) %{_mandir}/man8/ssh-keysign.8*
%attr(0644,root,root) %{_mandir}/man8/ssh-pkcs11-helper.8*
%attr(0644,root,root) %{_mandir}/man8/ssh-sk-helper.8*
%endif
%if %{scard}
%attr(0755,root,root) %dir %{_datadir}/openssh
%attr(0644,root,root) %{_datadir}/openssh/Ssh.bin
%endif
%files clients
%defattr(-,root,root)
%attr(0755,root,root) %{_bindir}/ssh
%attr(0644,root,root) %{_mandir}/man1/ssh.1*
%attr(0644,root,root) %{_mandir}/man5/ssh_config.5*
%attr(0644,root,root) %config(noreplace) %{_sysconfdir}/ssh/ssh_config
%if ! %{rescue}
%attr(2755,root,nobody) %{_bindir}/ssh-agent
%attr(0755,root,root) %{_bindir}/ssh-add
%attr(0755,root,root) %{_bindir}/ssh-keyscan
%attr(0755,root,root) %{_bindir}/sftp
%attr(0644,root,root) %{_mandir}/man1/ssh-agent.1*
%attr(0644,root,root) %{_mandir}/man1/ssh-add.1*
%attr(0644,root,root) %{_mandir}/man1/ssh-keyscan.1*
%attr(0644,root,root) %{_mandir}/man1/sftp.1*
%endif
%if ! %{rescue}
%files server
%defattr(-,root,root)
%dir %attr(0111,root,root) %{_var}/empty/sshd
%attr(0755,root,root) %{_sbindir}/sshd
%attr(0755,root,root) %{_libexecdir}/openssh/sftp-server
%attr(0644,root,root) %{_mandir}/man8/sshd.8*
%attr(0644,root,root) %{_mandir}/man5/moduli.5*
%attr(0644,root,root) %{_mandir}/man5/sshd_config.5*
%attr(0644,root,root) %{_mandir}/man8/sftp-server.8*
%attr(0755,root,root) %dir %{_sysconfdir}/ssh
%attr(0600,root,root) %config(noreplace) %{_sysconfdir}/ssh/sshd_config
%attr(0600,root,root) %config(noreplace) /etc/pam.d/sshd
%attr(0755,root,root) %config /etc/rc.d/init.d/sshd
%endif
%if ! %{no_x11_askpass}
%files askpass
%defattr(-,root,root)
%doc x11-ssh-askpass-%{aversion}/README
%doc x11-ssh-askpass-%{aversion}/ChangeLog
%doc x11-ssh-askpass-%{aversion}/SshAskpass*.ad
%{_libexecdir}/openssh/ssh-askpass
%attr(0755,root,root) %{_libexecdir}/openssh/x11-ssh-askpass
%endif
%if ! %{no_gnome_askpass}
%files askpass-gnome
%defattr(-,root,root)
%attr(0755,root,root) %config %{_sysconfdir}/profile.d/gnome-ssh-askpass.*
%attr(0755,root,root) %{_libexecdir}/openssh/gnome-ssh-askpass
%endif7、查看当前文件情况
[root@localhost SOURCES]# cd /root/rpmbuild && tree
.
├── SOURCES
│ ├── openssh-9.4p1.tar.gz
│ ├── openssl-1.1.1v.tar.gz
│ ├── sshd.pam.oe2203
│ └── x11-ssh-askpass-1.2.4.1.tar.gz
└── SPECS
└── openssh.spec
二、编译
[root@localhost rpmbuild]# cd /root/rpmbuild/SOURCES/
[root@localhost SPECS]# rpmbuild -bb openssh.spec
[root@localhost SPECS]# rpmbuild -bb openssh.spec
正在执行(%prep):/bin/sh -e /var/tmp/rpm-tmp.IJGzlM
+ umask 022
+ cd /root/rpmbuild/BUILD
+ cd /root/rpmbuild/BUILD
+ rm -rf openssh-9.4p1
+ /usr/bin/gzip -dc /root/rpmbuild/SOURCES/openssh-9.4p1.tar.gz
+ /usr/bin/tar -xof -
+ STATUS=0
+ '[' 0 -ne 0 ']'
+ cd openssh-9.4p1
+ /usr/bin/chmod -Rf a+rX,u+w,g-w,o-w .
+ mkdir -p openssl
+ tar xfz /root/rpmbuild/SOURCES/openssl-1.1.1v.tar.gz --strip-components=1 -C openssl
+ pushd openssl
~/rpmbuild/BUILD/openssh-9.4p1/openssl ~/rpmbuild/BUILD/openssh-9.4p1
+ ./config shared zlib -fPIC
Operating system: x86_64-whatever-linux2
Configuring OpenSSL version 1.1.1v (0x1010116fL) for linux-x86_64
Using os-specific seed configuration
Creating configdata.pm
Creating Makefile
...
检查未打包文件:/usr/lib/rpm/check-files /root/rpmbuild/BUILDROOT/openssh-9.4p1-oe2203.x86_64
已写至:/root/rpmbuild/RPMS/x86_64/openssh-debuginfo-9.4p1-oe2203.x86_64.rpm
已写至:/root/rpmbuild/RPMS/x86_64/openssh-9.4p1-oe2203.x86_64.rpm
已写至:/root/rpmbuild/RPMS/x86_64/openssh-server-9.4p1-oe2203.x86_64.rpm
已写至:/root/rpmbuild/RPMS/x86_64/openssh-debugsource-9.4p1-oe2203.x86_64.rpm
已写至:/root/rpmbuild/RPMS/x86_64/openssh-clients-9.4p1-oe2203.x86_64.rpm
正在执行(%clean):/bin/sh -e /var/tmp/rpm-tmp.oM9HyP
+ umask 022
+ cd /root/rpmbuild/BUILD
+ cd openssh-9.4p1
+ rm -rf /root/rpmbuild/BUILDROOT/openssh-9.4p1-oe2203.x86_64
+ RPM_EC=0
++ jobs -p
+ exit 0生成一堆rpm,取后返回“ + exit 0”,大功告成,去除临时文件:
[root@localhost SPECS]# cd ..
[root@localhost rpmbuild]# ll
总用量 24K
drwxr-xr-x. 3 root root 4.0K 9月 8 17:07 BUILD
drwxr-xr-x. 2 root root 4.0K 9月 8 17:11 BUILDROOT
drwxrwxr-x. 3 AAAA AAAA 4.0K 9月 8 17:11 RPMS
drwxrwxr-x. 2 AAAA AAAA 4.0K 9月 8 16:55 SOURCES
drwxrwxr-x. 2 AAAA AAAA 4.0K 9月 8 17:07 SPECS
drwxrwxr-x. 2 AAAA AAAA 4.0K 6月 5 14:41 SRPMS
[root@localhost rpmbuild]# rm -rf BUILD* SRPMS -rf
[root@localhost rpmbuild]# ll
总用量 16K
drwxrwxr-x. 3 AAAA AAAA 4.0K 9月 8 17:11 RPMS
drwxrwxr-x. 2 AAAA AAAA 4.0K 9月 8 16:55 SOURCES
drwxrwxr-x. 2 AAAA AAAA 4.0K 9月 8 17:07 SPECS
[root@localhost rpmbuild]# tree
.
├── RPMS
│ └── x86_64
│ ├── openssh-9.4p1-oe2203.x86_64.rpm
│ ├── openssh-clients-9.4p1-oe2203.x86_64.rpm
│ ├── openssh-debuginfo-9.4p1-oe2203.x86_64.rpm
│ ├── openssh-debugsource-9.4p1-oe2203.x86_64.rpm
│ └── openssh-server-9.4p1-oe2203.x86_64.rpm
├── SOURCES
│ ├── openssh-9.4p1.tar.gz
│ ├── openssl-1.1.1v.tar.gz
│ ├── sshd.pam.oe2203
│ └── x11-ssh-askpass-1.2.4.1.tar.gz
└── SPECS
└── openssh.spec
三、测试验证
1、安装升级
[root@localhost rpmbuild]# cd /root/rpmbuild/RPMS/x86_64
[root@localhost x86_64]# ll
总用量 16M
-rw-r--r--. 1 root root 4.7M 9月 8 17:11 openssh-9.4p1-oe2203.x86_64.rpm
-rw-r--r--. 1 root root 4.8M 9月 8 17:11 openssh-clients-9.4p1-oe2203.x86_64.rpm
-rw-r--r--. 1 root root 3.9M 9月 8 17:11 openssh-debuginfo-9.4p1-oe2203.x86_64.rpm
-rw-r--r--. 1 root root 779K 9月 8 17:11 openssh-debugsource-9.4p1-oe2203.x86_64.rpm
-rw-r--r--. 1 root root 1.5M 9月 8 17:11 openssh-server-9.4p1-oe2203.x86_64.rpm
[root@localhost x86_64]# dnf update *
Last metadata expiration check: 0:17:06 ago on 2023年09月08日 星期五 16时57分48秒.
Package openssh-debuginfo not installed, cannot update it.
No match for argument: openssh-debuginfo-9.4p1-oe2203.x86_64.rpm
Package openssh-debugsource not installed, cannot update it.
No match for argument: openssh-debugsource-9.4p1-oe2203.x86_64.rpm
Dependencies resolved.
=========================================================================================================================================================
Package Architecture Version Repository Size
=========================================================================================================================================================
Upgrading:
openssh x86_64 9.4p1-oe2203 @commandline 4.7 M
openssh-clients x86_64 9.4p1-oe2203 @commandline 4.8 M
openssh-server x86_64 9.4p1-oe2203 @commandline 1.5 M
Transaction Summary
=========================================================================================================================================================
Upgrade 3 Packages
Total size: 11 M
Is this ok [y/N]: y
Downloading Packages:
Running transaction check
Transaction check succeeded.
Running transaction test
Transaction test succeeded.
Running transaction
Preparing : 1/1
Running scriptlet: openssh-9.4p1-oe2203.x86_64 1/1
Upgrading : openssh-9.4p1-oe2203.x86_64 1/6
Upgrading : openssh-clients-9.4p1-oe2203.x86_64 2/6
Running scriptlet: openssh-server-9.4p1-oe2203.x86_64 3/6
Upgrading : openssh-server-9.4p1-oe2203.x86_64 3/6
警告:/etc/ssh/sshd_config 已建立为 /etc/ssh/sshd_config.rpmnew
Running scriptlet: openssh-server-9.4p1-oe2203.x86_64 3/6
Cleanup : openssh-clients-8.8p1-2.oe2203.x86_64 4/6
Cleanup : openssh-8.8p1-2.oe2203.x86_64 5/6
Running scriptlet: openssh-server-8.8p1-2.oe2203.x86_64 6/6
Cleanup : openssh-server-8.8p1-2.oe2203.x86_64 6/6
Running scriptlet: openssh-server-8.8p1-2.oe2203.x86_64 6/6
Verifying : openssh-9.4p1-oe2203.x86_64 1/6
Verifying : openssh-8.8p1-2.oe2203.x86_64 2/6
Verifying : openssh-clients-9.4p1-oe2203.x86_64 3/6
Verifying : openssh-clients-8.8p1-2.oe2203.x86_64 4/6
Verifying : openssh-server-9.4p1-oe2203.x86_64 5/6
Verifying : openssh-server-8.8p1-2.oe2203.x86_64 6/6
Upgraded:
openssh-9.4p1-oe2203.x86_64 openssh-clients-9.4p1-oe2203.x86_64 openssh-server-9.4p1-oe2203.x86_64
Complete!
2、因为openssh9.*加密算法只支持256位以上,因此原来v8.8的配置文件不能直接用了,先替换配置文件,再重启服务,因是CRT远程连接,建议可多重启几次:
[root@localhost x86_64]# cp /etc/ssh/sshd_config.rpmnew /etc/ssh/sshd_config
cp:是否覆盖'/etc/ssh/sshd_config'? y
[root@localhost ssh]# systemctl restart sshd
[root@localhost ssh]# systemctl status sshd
● sshd.service - SYSV: OpenSSH server daemon
Loaded: loaded (/etc/rc.d/init.d/sshd; generated)
Active: active (running) since Fri 2023-09-08 17:15:55 CST; 1s ago
Docs: man:systemd-sysv-generator(8)
Process: 32624 ExecStart=/etc/rc.d/init.d/sshd start (code=exited, status=0/SUCCESS)
Main PID: 32633 (sshd)
Tasks: 11 (limit: 4172)
Memory: 169.8M
CGroup: /system.slice/sshd.service
├─ 1544 "sshd: AAAA [priv]" "" "" ""
├─ 1548 "sshd: AAAA@notty" "" "" "" ""
├─ 1549 /usr/libexec/openssh/sftp-server -l INFO -f AUTH
├─ 2114 "sshd: AAAA [priv]" "" "" ""
├─ 2118 "sshd: AAAA@pts/0" "" "" "" ""
├─ 2119 -bash
├─ 2205 su -
├─ 2232 -bash
├─32633 "sshd: /usr/sbin/sshd [listener] 0 of 10-100 startups"
├─32635 systemctl status sshd
└─32636 less
9月 08 17:15:55 localhost.localdomain systemd[1]: Starting SYSV: OpenSSH server daemon...
9月 08 17:15:55 localhost.localdomain sshd[32630]: /sbin/restorecon: lstat(/etc/ssh/ssh_host_dsa_key.pub) failed: No such file or directory
9月 08 17:15:55 localhost.localdomain sshd[32633]: Server listening on 0.0.0.0 port 22.
9月 08 17:15:55 localhost.localdomain sshd[32633]: Server listening on :: port 22.
9月 08 17:15:55 localhost.localdomain sshd[32624]: Starting sshd:[ 确定 ]
9月 08 17:15:55 localhost.localdomain systemd[1]: Started SYSV: OpenSSH server daemon.
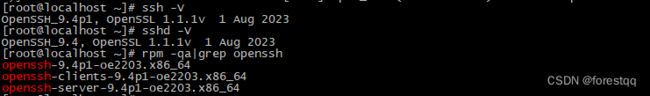
[root@localhost ssh]# systemctl restart sshd3、核对版本信息:
[root@localhost ssh]# ssh -V
OpenSSH_9.4p1, OpenSSL 1.1.1v 1 Aug 2023
[root@localhost ssh]# sshd -V
OpenSSH_9.4, OpenSSL 1.1.1v 1 Aug 2023
[root@localhost ssh]# rpm -qa |grep openssh
openssh-9.4p1-oe2203.x86_64
openssh-clients-9.4p1-oe2203.x86_64
openssh-server-9.4p1-oe2203.x86_64可以将/root/rpmbuild/RPMS/x86_64下的软件包进行拷贝分发或放到http服务器共享。至此,rpm包制作完成。
附1:异常倒回
[root@localhost ssh]# yum remove openssh openssh-server openssh-clients
[root@localhost ssh]# yum install openssh openssh-server openssh-clients -y
附2:连接问题
openssh升级到9.*后加密算法最低要求256位,因此升级openssh后低版本的客户端和CRT都将无法连接,报以下错误:
Key exchange failed.
No compatible key-exchange method. The server supports these methods: [email protected],curve25519-sha256,[email protected],ecdh-sha2-nistp256,ecdh-sha2-nistp384,ecdh-sha2-nistp521,diffie-hellman-group-exchange-sha256,diffie-hellman-group16-sha512,diffie-hellman-group18-sha512,diffie-hellman-group14-sha256
此时其它未升级openssh的Linux服务器也会连不上更新服务器的,不要以为升级失败了,只需将需要连接本服务器的主机的openssh-client也升级了即可。
Windows连接请升级SecureCRT到8.*.*版本,同时会话属性中仅启用256或512位算法,即可正常连接。
![]()
![]()
![]()
可以看到连接也是没有任何问题的。
本人编译的软件包下载:
openssh9.4p1 for openeuler 2203 LTS