- [MRCTF2020]pyFlag(详解附送多个python脚本)
迟来的幸运
python开发语言
Hex:FFD95B5365637265742046696C65205061727420313A5DASCII:ÿÙ[SecretFilePart1:]发现Setsuna.jpg尾部有多余的一部分有左侧窗口pk头,前有一段ÿÙ[SecretFilePart1:],提示是第一部分Hex:FFD95B5365637265742046696C65205061727420323A5DASCII:ÿÙ[Se
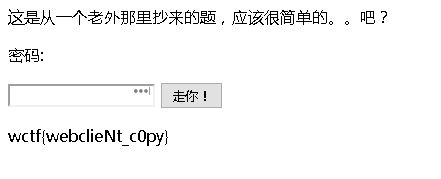
- [MRCTF2020]套娃 1
succ3
BUUCTFapachephpweb安全
知识点:Client-ip,data://,$_SERVER总结我们可以传个b+u+p+t=23333%0a,因为php在解析变量名的时候会把+、%20、*、{、[解析为_,具体可以看:https://www.freebuf.com/articles/web/213359.html有一段fuckjs代码,可以放到Console里面运行。告诉我们要post传个Merak可以看到它有三个地方过滤:第一
- python下载m3u8格式视频
fengchengwu2012
devopspython开发语言m3u8
一、安装m3u8库pipinstallrequestspipinstallrequestsm3u8二、编码实现importosimportreimportrequestsimportsubprocess#下载ts文件defdown_ts_file(base_url,m3u8_url,download_dir):#从m3u8文件中获取所有ts的分片名称信息response=requests.get(
- This is deprecated. The new driver class is com.mysql.cj.jdbc.Driver.的解决办法及原因
C4程序员
Java菜鸟之路mysql数据库java
1.问题描述Thisisdeprecated.Thenewdriverclassis`com.mysql.cj.jdbc.Driver'.2.原因Spring2.2以后的版本是默认支持MySQL8的,所以当你的MySQL版本是8及以上就需要修改你的加载驱动3.解决办法同时注意时区东八区serverTimezone=GMT%2B84.补充privatestaticStringurl="jdbc:my
- 容器神器Docker的入门篇章
悟能不能悟
容器docker
Docker就是个“打包神器”,专门用来把你的代码、环境配置、依赖库一股脑儿装进一个轻量级的“集装箱”里,扔到任何地方都能直接跑起来,完全不用操心“水土不服”的问题!举个栗子:假设你写了个Python网站,本地用Python3.10+MySQL8.0跑得好好的,但同事电脑上装的是Python2.7+MySQL5.7,结果代码一拷贝就报错。这时候Docker就能救场——你把整个环境打包成一个镜像(I
- nextjs 路由
猪猪宝儿姐
reactnative
1.官网路由介绍nextjs路由next项目的路由默认为page下面的文件生成对应的路由。http://localhost:3000/代表的/page/index.tsx.http://localhost:3000/demo指的是page-->demo-->index.tsx文件。2.动态路由在Next.js中,您可以将括号添加到页面([param])以创建动态路由(也称为urlslugs、pre
- GitHub开源的容器管理面板-Dpanel
huhy~
GitHub容器云github开源
dpanelDocker安装部署二进制部署GitHub官网一块轻量化docker可视化管理面板,由国人开发,个人觉得是比较好用的,功能都很齐全,并且可以通过修改源码,自定义前端样式等。Docker安装部署官网部署环境:Ubuntu24.04LTS安装dockerapt-yinstallapt-transport-httpsca-certificatescurlsoftware-properties
- Vite 开发服务器漏洞
故事与他645
服务器网络数据库网络安全apachelog4j
漏洞危害对于使用Vite老版本(包括但不限于>=6.2.0,=6.1.0,=6.0.0,=5.0.0,<=5.4.14;<=4.5.9)的开发者和企业运维人员来说,这是一个不容忽视的问题。因为攻击者只需在浏览器中输入特定的URL,就有可能获取目标机器上的源码、SSH密钥、数据库账号、用户数据等任意文件信息,从而导致敏感信息泄露。漏洞再现FOFAbody="/@vite/client"在浏览器中输入
- ElementUI的<el-image>组件引用网络图片加载失败
又迷茫了
框架使用elementui前端javascript
1.验证图片URL是否有效直接访问图片链接,确保URL正确且可公开访问如果浏览器无法加载图片,可能是图片服务器限制了外链或已失效。解决方法:更换为可用的图片URL。2.检查浏览器开发者工具打开浏览器开发者工具(F12),查看以下信息:Network标签:检查图片请求的状态码。状态码403:服务器拒绝访问(常见于防盗链)。状态码404:图片路径错误。Console标签:查看是否有跨域错误(如CORS
- ElementUI的<el-image>组件引用网络图片加载失败-解决办法
又迷茫了
框架使用大数据vue
1.验证图片URL是否有效直接访问图片链接,确保URL正确且可公开访问如果浏览器无法加载图片,可能是图片服务器限制了外链或已失效。解决方法:更换为可用的图片URL。2.检查浏览器开发者工具打开浏览器开发者工具(F12),查看以下信息:Network标签:检查图片请求的状态码。状态码403:服务器拒绝访问(常见于防盗链)。状态码404:图片路径错误。Console标签:查看是否有跨域错误(如CORS
- 2024年最新ctfshow-WEB-web9( MD5加密漏洞绕过)_ctfshow web9(1),网络安全架构师必备框架技能核心笔记
2401_84301227
程序员前端web安全笔记
一、网安学习成长路线图网安所有方向的技术点做的整理,形成各个领域的知识点汇总,它的用处就在于,你可以按照上面的知识点去找对应的学习资源,保证自己学得较为全面。二、网安视频合集观看零基础学习视频,看视频学习是最快捷也是最有效果的方式,跟着视频中老师的思路,从基础到深入,还是很容易入门的。三、精品网安学习书籍当我学到一定基础,有自己的理解能力的时候,会去阅读一些前辈整理的书籍或者手写的笔记资料,这些笔
- 2024年最新ctfshow-WEB-web10( with rollup注入绕过)_ctf
2301_82056337
程序员前端网络服务器
进来以后是一个登录界面,盲猜是SQL注入漏洞点击取消按钮可以获取这一关的源码,下载到本地即可源码中先根据用户名查询用户信息,用户名通过以后,再判断密码是否相同,我们绕过用户名的过滤条件,在使用withrollup注入绕过密码withrollup可以对groupby分组结果再次进行分组,并在最后添加一行数据用于展示结果(对groupby未指定的字段进行求和汇总,而groupby指定的分组字段则用nu
- 基于Flask的通用登录注册模块,并代理跳转到目标网址
vener__
通用网站搭建flaskpython后端
实现了用户密码的加密,代理跳转到目标网址,不会暴露目标路径,未登录的情况下访问proxy则自动跳转到登录页,使用时需要修改配置项config,登录注册页面背景快速修改,可以实现登录注册模块的快速复用。1.app.pyfromflaskimportFlask,render_template,request,redirect,url_for,session,Responseimportsqlite3i
- springMVC处理请求全过程
Supreme13
状态模式
目录一、SpringMVC全过程略写图二、SpringMVC处理请求源码分析2.1全过程详解图2.2执行过程:2.3源码解析三、总结全过程略写图用户发送请求,经过前端控制器Dispacherservlet(Controller的核心)将url交给处理器映射器HandlerMapping处理处理器映射器HandlerMapping处理url,返回HandlerExecutionChain(可能包含拦
- BUUCTF [极客大挑战 2019]Not Bad
A秋逝
安全
拿到题目放入ida,看看有什么函数在main看到这两个比较有用的函数,第一个函数一眼看过去就发现是有沙箱保护的,第二个函数就是正常的栈溢出函数,我们先看看程序开了什么保护什么都没开,只有沙箱保护,我们只能利用read,write,和open来攻击,也就是orw攻击,但是栈空间太小了,可能不好构造rop,在main中有一个mmap函数,给我们开辟了一个0x1000的可读可写可执行的栈,所以我们只要把
- Ubuntu上安装Docker
阿俊仔(摸鱼版)
云服务器管理实操ubuntudockerlinux
Ubuntu上安装Docker更新系统软件包安装依赖项添加Docker官方GPG密钥添加Docker官方仓库安装DockerEngine验证安装配置镜像加速更新系统软件包首先确保系统软件包是最新的:sudoapt-getupdatesudoapt-getupgrade-y安装依赖项安装Docker所需的依赖包,包括apt-transport-https、ca-certificates、curl等:
- Android手机蓝牙连接热敏打印机 打印票据
郭陈同学
Android开发笔记蓝牙手机
手机蓝牙连接热敏打印机打印票据话不多说上代码:项目地址:可直接作为项目依赖引用allprojects{repositories{...maven{url'https://jitpack.io'}}}dependencies{compile'com.github.guochenhome:BluetoothPrint:1.1.2'}如果第一步报Error:Executionfailedfortask'
- 高级java每日一道面试题-2025年3月11日-微服务篇[Eureka篇]-Eureka Client配置有哪些?
java我跟你拼了
java每日一道面试题java微服务eureka
如果有遗漏,评论区告诉我进行补充面试官:EurekaClient配置有哪些?我回答:为了提供一个全面且综合的回答,涵盖EurekaClient配置的各个方面,并结合实际应用中的最佳实践,以下是详细的分析和解释。这将帮助候选人准备高级Java面试中关于EurekaClient配置的问题。一、核心基础配置服务注册与发现eureka.client.serviceUrl.defaultZone:指定Eur
- vue项目之axios请求统一配置了超时时间,单独接口请求时重设超时时间
牛先森家的牛奶
Vuevue接口
vue项目中axios请求统一配置了超时时间,单独接口请求时重设超时时间根据官网推荐:axios配置官网默认请求时间接口请求://任务新建exportfunctionnewTaskAdd(data){returnrequest({url:'/api/taskPlan/add',method:'post',data})}重设超时时间的接口请求://任务新建exportfunctionnewTaskA
- 设计模式:完结-->设计模式总结
WeiLai1112
设计模式设计模式java后端架构分布式面试
设计模式深度解析:从阿里/字节实战看设计模式的选择与演进一、设计模式的优缺点总结1.1三大类设计模式全景分析创建型模式解耦创建逻辑产品族创建复杂对象构造克隆对象全局唯一实例创建型模式+工厂方法(FactoryMethod)+抽象工厂(AbstractFactory)+建造者(Builder)+原型(Prototype)+单例(Singleton)工厂方法抽象工厂建造者原型单例优点总结:解耦对象创建
- Gin框架全套实战教程
万才博客
golanggo语言软件框架golang
01.API的URL规则设计、带参数的路由02.是否一定要用MVC模式、路由分组03.简单Dao层代码封装、使用中间件模拟鉴权04.创建Model、参数绑定Model的初步使用05.内置验证器的初步使用、POST参数绑定06.自定义验证器结合正则验证JSON参数07.批量提交帖子数据的验证基本姿势08.到底要不要用ORM、Gorm入手、执行原始SQL09.结合Model进行数据映射、查询的基本要点
- uniapp用法--uni.navigateTo 使用与参数携带的方式示例(包含复杂类型参数)
碧海饮冰
前端
一、基本用法功能特性保留当前页面,将新页面推入导航栈顶部(适用于非tabBar页面跳转)。可通过uni.navigateBack返回原页面34。代码示例uni.navigateTo({url:'/pages/detail/detail?key=value'//目标页面路径及参数});二、可携带参数类型基础类型参数字符串/数值:直接拼接在URL后,如url:'/pages/page
- 高效运维工具箱:精选10款Linux运维神器(非常详细)零基础入门到精通,收藏这一篇就够了_运维工程师脚本软件
狂野帅哥
运维linux服务器网络安全web安全计算机网络系统安全
运维工程师在日常工作中频繁运用的10款工具,并细致阐述每款工具的功能、适用场景以及其卓越之处。1.Shell脚本功能:主要用于自动化任务和批处理作业。适用场景:频繁用于文件处理、系统管理、简单的网络管理等操作。优势:灵活且强大,能够直接与系统进行交互操作。实例:运维工程师常常使用Shell脚本来批量修改服务器上的配置文件。#!/bin/bash#配置文件的路径``config_path="/pat
- 微信小程序入门一之小程序架构
Qiang_1995
微信小程序
微信公众平台技术文档2016-9-20凌晨,微信推出应用号“小程序”内测功能;2016-11-4,正式公测,企事业单位可申请公测账号;2017-1-9,正式上线;官方社区地址:http://developers.weixin.qq.com架构分析基本目录结构主目录(项目描述文件){主逻辑文件app.js主配置文件app.json:注册页面,全局定义网络超时、窗口表现等主样式文件app.wxss:类
- Effective C++ 学习笔记 条款23 宁以non-member、non-friend替换member函数
吃着火锅x唱着歌
EffectiveC++(第三版)c++学习笔记
想象有个class用来表示网页浏览器。这样的class可能提供的众多函数中,有一些用来清除下载元素高速缓存区(cacheofdownloadedelements)、清除访问过的URLs的历史记录(historyofvisitedURLs)、以及移除系统中的所有cookies:classWebBrowser{public://...voidclearCache();voidclearHistory(
- Effective C++ 详解条款23:宁以non-member、non-friend替换member函数
慵懒小书虫
EffectiveC++c++封装成员函数面向对象编程class
总结:宁可拿non-membernon-friend函数替换member函数。这样做可以增加封装性、包裹弹性(packagingflexibility)和机能扩充性。举例:一个class用来表示网页浏览器。这样的class可能提供的众多函数中,有一些用来清除下载元素高速缓存区、清除访问过的URLS的历史记录、以及移除系统中的所有cookies:classwebBrowser{public:...v
- git无法使用git协议clone github仓库问题解决方法
uuuuu1711644
gitgithub
如果你在使用Git协议(git://)尝试克隆GitHub仓库时遇到问题,可能是因为一些网络限制或防火墙设置阻止了Git协议的访问。你可以尝试以下解决方法:使用HTTPS协议克隆:GitHub支持使用HTTPS协议进行仓库克隆。使用HTTPS协议可以通过常见的端口(通常是443)绕过一些网络限制。在克隆命令中使用HTTPSURL替代Git协议的URL。例如:gitclonehttps://gith
- MySQL字符串处理神器:SUBSTRING_INDEX函数深度解析
水涵幽树
mysql数据库sql后端学习clickhouse
一、函数概述SUBSTRING_INDEX是MySQL中用于按分隔符截取字符串的核心函数,特别适合处理包含固定分隔符的文本数据(如日志、路径、标签等)。二、语法结构SUBSTRING_INDEX(str,delimiter,count)str:被处理的原始字符串(支持字段名)delimiter:分隔符(区分大小写)count:截取方向控制参数正数:从左往右截取前N段负数:从右往左截取前N段三、核心
- 一种通过HTTP方式可部署在Linux服务器的股票交易接口探索
DaoYuanTech
同花顺通达信自动化交易接口服务器httplinux
一种通过HTTP方式可部署在Linux服务器的股票交易接口探索,支持逆回购、两融账户先来来演示怎么采用Python通过HTTP方式,对已经部署到Ubuntu服务器上交易接口进行操作:importrequests#APIURLurl='http://192.168.1.5:9527/Api/Trade'header={'User-Agent':'Mozilla/4.0',}#初始化交易接口respo
- python中如何将dict转换成json
灭绝师太也疯狂
jsonpython
userinfo={'a':'b','c':'d'}userjson=json.dumps(userinfo)res=requests.post(url,data=userjson,header={'Content-type':'application/json'})res.text/json()可适当的打印类型查看print(type())
- 项目中 枚举与注解的结合使用
飞翔的马甲
javaenumannotation
前言:版本兼容,一直是迭代开发头疼的事,最近新版本加上了支持新题型,如果新创建一份问卷包含了新题型,那旧版本客户端就不支持,如果新创建的问卷不包含新题型,那么新旧客户端都支持。这里面我们通过给问卷类型枚举增加自定义注解的方式完成。顺便巩固下枚举与注解。
一、枚举
1.在创建枚举类的时候,该类已继承java.lang.Enum类,所以自定义枚举类无法继承别的类,但可以实现接口。
- 【Scala十七】Scala核心十一:下划线_的用法
bit1129
scala
下划线_在Scala中广泛应用,_的基本含义是作为占位符使用。_在使用时是出问题非常多的地方,本文将不断完善_的使用场景以及所表达的含义
1. 在高阶函数中使用
scala> val list = List(-3,8,7,9)
list: List[Int] = List(-3, 8, 7, 9)
scala> list.filter(_ > 7)
r
- web缓存基础:术语、http报头和缓存策略
dalan_123
Web
对于很多人来说,去访问某一个站点,若是该站点能够提供智能化的内容缓存来提高用户体验,那么最终该站点的访问者将络绎不绝。缓存或者对之前的请求临时存储,是http协议实现中最核心的内容分发策略之一。分发路径中的组件均可以缓存内容来加速后续的请求,这是受控于对该内容所声明的缓存策略。接下来将讨web内容缓存策略的基本概念,具体包括如如何选择缓存策略以保证互联网范围内的缓存能够正确处理的您的内容,并谈论下
- crontab 问题
周凡杨
linuxcrontabunix
一: 0481-079 Reached a symbol that is not expected.
背景:
*/5 * * * * /usr/IBMIHS/rsync.sh
- 让tomcat支持2级域名共享session
g21121
session
tomcat默认情况下是不支持2级域名共享session的,所有有些情况下登陆后从主域名跳转到子域名会发生链接session不相同的情况,但是只需修改几处配置就可以了。
打开tomcat下conf下context.xml文件
找到Context标签,修改为如下内容
如果你的域名是www.test.com
<Context sessionCookiePath="/path&q
- web报表工具FineReport常用函数的用法总结(数学和三角函数)
老A不折腾
Webfinereport总结
ABS
ABS(number):返回指定数字的绝对值。绝对值是指没有正负符号的数值。
Number:需要求出绝对值的任意实数。
示例:
ABS(-1.5)等于1.5。
ABS(0)等于0。
ABS(2.5)等于2.5。
ACOS
ACOS(number):返回指定数值的反余弦值。反余弦值为一个角度,返回角度以弧度形式表示。
Number:需要返回角
- linux 启动java进程 sh文件
墙头上一根草
linuxshelljar
#!/bin/bash
#初始化服务器的进程PId变量
user_pid=0;
robot_pid=0;
loadlort_pid=0;
gateway_pid=0;
#########
#检查相关服务器是否启动成功
#说明:
#使用JDK自带的JPS命令及grep命令组合,准确查找pid
#jps 加 l 参数,表示显示java的完整包路径
#使用awk,分割出pid
- 我的spring学习笔记5-如何使用ApplicationContext替换BeanFactory
aijuans
Spring 3 系列
如何使用ApplicationContext替换BeanFactory?
package onlyfun.caterpillar.device;
import org.springframework.beans.factory.BeanFactory;
import org.springframework.beans.factory.xml.XmlBeanFactory;
import
- Linux 内存使用方法详细解析
annan211
linux内存Linux内存解析
来源 http://blog.jobbole.com/45748/
我是一名程序员,那么我在这里以一个程序员的角度来讲解Linux内存的使用。
一提到内存管理,我们头脑中闪出的两个概念,就是虚拟内存,与物理内存。这两个概念主要来自于linux内核的支持。
Linux在内存管理上份为两级,一级是线性区,类似于00c73000-00c88000,对应于虚拟内存,它实际上不占用
- 数据库的单表查询常用命令及使用方法(-)
百合不是茶
oracle函数单表查询
创建数据库;
--建表
create table bloguser(username varchar2(20),userage number(10),usersex char(2));
创建bloguser表,里面有三个字段
&nbs
- 多线程基础知识
bijian1013
java多线程threadjava多线程
一.进程和线程
进程就是一个在内存中独立运行的程序,有自己的地址空间。如正在运行的写字板程序就是一个进程。
“多任务”:指操作系统能同时运行多个进程(程序)。如WINDOWS系统可以同时运行写字板程序、画图程序、WORD、Eclipse等。
线程:是进程内部单一的一个顺序控制流。
线程和进程
a. 每个进程都有独立的
- fastjson简单使用实例
bijian1013
fastjson
一.简介
阿里巴巴fastjson是一个Java语言编写的高性能功能完善的JSON库。它采用一种“假定有序快速匹配”的算法,把JSON Parse的性能提升到极致,是目前Java语言中最快的JSON库;包括“序列化”和“反序列化”两部分,它具备如下特征:
- 【RPC框架Burlap】Spring集成Burlap
bit1129
spring
Burlap和Hessian同属于codehaus的RPC调用框架,但是Burlap已经几年不更新,所以Spring在4.0里已经将Burlap的支持置为Deprecated,所以在选择RPC框架时,不应该考虑Burlap了。
这篇文章还是记录下Burlap的用法吧,主要是复制粘贴了Hessian与Spring集成一文,【RPC框架Hessian四】Hessian与Spring集成
- 【Mahout一】基于Mahout 命令参数含义
bit1129
Mahout
1. mahout seqdirectory
$ mahout seqdirectory
--input (-i) input Path to job input directory(原始文本文件).
--output (-o) output The directory pathna
- linux使用flock文件锁解决脚本重复执行问题
ronin47
linux lock 重复执行
linux的crontab命令,可以定时执行操作,最小周期是每分钟执行一次。关于crontab实现每秒执行可参考我之前的文章《linux crontab 实现每秒执行》现在有个问题,如果设定了任务每分钟执行一次,但有可能一分钟内任务并没有执行完成,这时系统会再执行任务。导致两个相同的任务在执行。
例如:
<?
//
test
.php
- java-74-数组中有一个数字出现的次数超过了数组长度的一半,找出这个数字
bylijinnan
java
public class OcuppyMoreThanHalf {
/**
* Q74 数组中有一个数字出现的次数超过了数组长度的一半,找出这个数字
* two solutions:
* 1.O(n)
* see <beauty of coding>--每次删除两个不同的数字,不改变数组的特性
* 2.O(nlogn)
* 排序。中间
- linux 系统相关命令
candiio
linux
系统参数
cat /proc/cpuinfo cpu相关参数
cat /proc/meminfo 内存相关参数
cat /proc/loadavg 负载情况
性能参数
1)top
M:按内存使用排序
P:按CPU占用排序
1:显示各CPU的使用情况
k:kill进程
o:更多排序规则
回车:刷新数据
2)ulimit
ulimit -a:显示本用户的系统限制参
- [经营与资产]保持独立性和稳定性对于软件开发的重要意义
comsci
软件开发
一个软件的架构从诞生到成熟,中间要经过很多次的修正和改造
如果在这个过程中,外界的其它行业的资本不断的介入这种软件架构的升级过程中
那么软件开发者原有的设计思想和开发路线
- 在CentOS5.5上编译OpenJDK6
Cwind
linuxOpenJDK
几番周折终于在自己的CentOS5.5上编译成功了OpenJDK6,将编译过程和遇到的问题作一简要记录,备查。
0. OpenJDK介绍
OpenJDK是Sun(现Oracle)公司发布的基于GPL许可的Java平台的实现。其优点:
1、它的核心代码与同时期Sun(-> Oracle)的产品版基本上是一样的,血统纯正,不用担心性能问题,也基本上没什么兼容性问题;(代码上最主要的差异是
- java乱码问题
dashuaifu
java乱码问题js中文乱码
swfupload上传文件参数值为中文传递到后台接收中文乱码 在js中用setPostParams({"tag" : encodeURI( document.getElementByIdx_x("filetag").value,"utf-8")});
然后在servlet中String t
- cygwin很多命令显示command not found的解决办法
dcj3sjt126com
cygwin
cygwin很多命令显示command not found的解决办法
修改cygwin.BAT文件如下
@echo off
D:
set CYGWIN=tty notitle glob
set PATH=%PATH%;d:\cygwin\bin;d:\cygwin\sbin;d:\cygwin\usr\bin;d:\cygwin\usr\sbin;d:\cygwin\us
- [介绍]从 Yii 1.1 升级
dcj3sjt126com
PHPyii2
2.0 版框架是完全重写的,在 1.1 和 2.0 两个版本之间存在相当多差异。因此从 1.1 版升级并不像小版本间的跨越那么简单,通过本指南你将会了解两个版本间主要的不同之处。
如果你之前没有用过 Yii 1.1,可以跳过本章,直接从"入门篇"开始读起。
请注意,Yii 2.0 引入了很多本章并没有涉及到的新功能。强烈建议你通读整部权威指南来了解所有新特性。这样有可能会发
- Linux SSH免登录配置总结
eksliang
ssh-keygenLinux SSH免登录认证Linux SSH互信
转载请出自出处:http://eksliang.iteye.com/blog/2187265 一、原理
我们使用ssh-keygen在ServerA上生成私钥跟公钥,将生成的公钥拷贝到远程机器ServerB上后,就可以使用ssh命令无需密码登录到另外一台机器ServerB上。
生成公钥与私钥有两种加密方式,第一种是
- 手势滑动销毁Activity
gundumw100
android
老是效仿ios,做android的真悲催!
有需求:需要手势滑动销毁一个Activity
怎么办尼?自己写?
不用~,网上先问一下百度。
结果:
http://blog.csdn.net/xiaanming/article/details/20934541
首先将你需要的Activity继承SwipeBackActivity,它会在你的布局根目录新增一层SwipeBackLay
- JavaScript变换表格边框颜色
ini
JavaScripthtmlWebhtml5css
效果查看:http://hovertree.com/texiao/js/2.htm代码如下,保存到HTML文件也可以查看效果:
<html>
<head>
<meta charset="utf-8">
<title>表格边框变换颜色代码-何问起</title>
</head>
<body&
- Kafka Rest : Confluent
kane_xie
kafkaRESTconfluent
最近拿到一个kafka rest的需求,但kafka暂时还没有提供rest api(应该是有在开发中,毕竟rest这么火),上网搜了一下,找到一个Confluent Platform,本文简单介绍一下安装。
这里插一句,给大家推荐一个九尾搜索,原名叫谷粉SOSO,不想fanqiang谷歌的可以用这个。以前在外企用谷歌用习惯了,出来之后用度娘搜技术问题,那匹配度简直感人。
环境声明:Ubu
- Calender不是单例
men4661273
单例Calender
在我们使用Calender的时候,使用过Calendar.getInstance()来获取一个日期类的对象,这种方式跟单例的获取方式一样,那么它到底是不是单例呢,如果是单例的话,一个对象修改内容之后,另外一个线程中的数据不久乱套了吗?从试验以及源码中可以得出,Calendar不是单例。
测试:
Calendar c1 =
- 线程内存和主内存之间联系
qifeifei
java thread
1, java多线程共享主内存中变量的时候,一共会经过几个阶段,
lock:将主内存中的变量锁定,为一个线程所独占。
unclock:将lock加的锁定解除,此时其它的线程可以有机会访问此变量。
read:将主内存中的变量值读到工作内存当中。
load:将read读取的值保存到工作内存中的变量副本中。
- schedule和scheduleAtFixedRate
tangqi609567707
javatimerschedule
原文地址:http://blog.csdn.net/weidan1121/article/details/527307
import java.util.Timer;import java.util.TimerTask;import java.util.Date;
/** * @author vincent */public class TimerTest {
- erlang 部署
wudixiaotie
erlang
1.如果在启动节点的时候报这个错 :
{"init terminating in do_boot",{'cannot load',elf_format,get_files}}
则需要在reltool.config中加入
{app, hipe, [{incl_cond, exclude}]},
2.当generate时,遇到:
ERROR