VIP: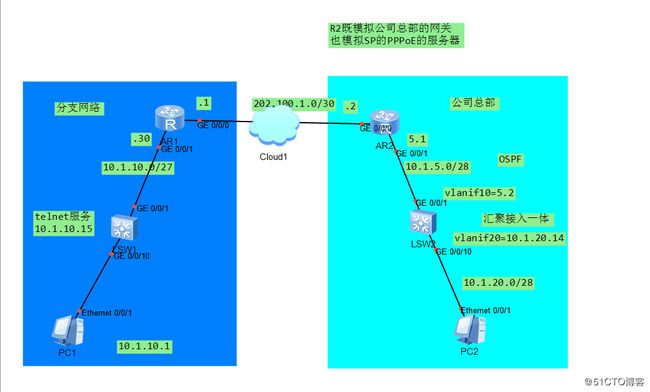
本文档包含3大部分:PPPoE、NAT和IPSEC ×××实施,是企业网接入互联网以及广域网互联重要的技术,本文档实现了综合运用
1.PPPoE
PPP over ethernet(以太网上的PPP协议)
PPP即点到点协议,是一种2层封装协议,工作串行链路(默认情况不能工作在以太
网上)
以太网的优势:以太网非常流行,速率很高,同时成本小
PPP的优势:公有协议的封装,支持认证(扩展到流量统计以及计费)
两者结合引出了PPPoE
PPPoE的3个阶段:1)发现阶段 2)会话建立 3)会话结束
PPPOE的服务器:
aaa
local-user qyt password cipher %$%$T;;MX@,(.6yB!SBS[MN(rZIB%$%$
local-user qyt service-type ppp //创建用于客户端认证的用户名和密码
ip pool PPPoE1
network 202.100.1.0 mask 255.255.255.252 //给客户端下发的网络地址段,华
为从较高地址开始下发
excluded-ip-address 202.100.1.2 //拍错202.100.1.2的地址
dns-list 114.114.114.114
[R2-ip-pool-PPPoE1]dns-list 114.114.114.114
[R2]int Virtual-Template 1 //创建虚拟模版接口
[R2-Virtual-Template1]remote address pool PPPoE1 //客户端地址从地址池
PPPoE1中获得
[R2-Virtual-Template1]ip address 202.100.1.1 30
[R2-Virtual-Template1]ppp authentication-mode chap //开启认证
[R2-Virtual-Template1]int g0/0/0
[R2-GigabitEthernet0/0/0]pppoe-server bind virtual-template 1 //把虚拟
模版接口和物理接口一起结合使用,把物理接口绑定到PPPoE中去
[R2-GigabitEthernet0/0/0]
客户端:
dialer-rule
dialer-rule 1 ip permit
interface Dialer1
link-protocol ppp
ppp chap user qyt
ppp chap password cipher %$%$#\/D5=%dXNcA,zAF)}M7,'
dialer user QYT
dialer bundle 10
dialer-group 1
interface GigabitEthernet0/0/0
pppoe-client dial-bundle-number 10
Dec 13 2017 20:20:59.935.1-08:00 R1 PPPOE-
CLIENT/7/debugging:GigabitEthernet0/0/0: PPPoE Client OUT Discovery
data (PADI), Len = 30
[R1-GigabitEthernet0/0/0]
Dec 13 2017 20:20:59.975.1-08:00 R1 PPPOE-
CLIENT/7/debugging:GigabitEthernet0/0/0: PPPoE Client IN Discovery data
(PADO), Len = 60
[R1-GigabitEthernet0/0/0]
Dec 13 2017 20:20:59.975.2-08:00 R1 PPPOE-
CLIENT/7/debugging:GigabitEthernet0/0/0: PPPoE Client OUT Discovery
data (PADR), Len = 48
[R1-GigabitEthernet0/0/0]
Dec 13 2017 20:21:00.55.1-08:00 R1 PPPOE-
CLIENT/7/debugging:GigabitEthernet0/0/0: PPPoE Client IN Discovery data
(PADS), Len = 60, Session ID = 1
[R1]display pppoe-client session summary
PPPoE Client Session:
ID Bundle Dialer Intf Client-MAC Server-MAC State
1 10 1 GE0/0/0 00e0fc840ba5 00e0fc8f08d4 UP
SID Intf State OIntf RemMAC
LocMAC
1 Virtual-Template1:0 UP GE0/0/0 00e0.fc84.0ba5
00e0.fc8f.08d4
[R1]dis ip routing-table protocol direct
Route Flags: R - relay, D - download to fib
Public routing table : Direct
Destinations : 6 Routes : 6
Direct routing table status :
Destinations : 6 Routes : 6
Destination/Mask Proto Pre Cost Flags NextHop
Interface
202.100.1.1/32 Direct 0 0 D 127.0.0.1 Dialer1
202.100.1.2/32 Direct 0 0 D 202.100.1.2
Dialer1
现在client获得了202.100.1.254的地址,202.100.1.254<---> 202.100.1.2直
连通信?
0 不能
1 能
2.NAT转换
经常有同学说:华为的NAT做不成功,这是完全错误的观点!!
2种最常用的NAT
2.1 NAT server
把内网的一台设备的服务应用(端口)映射到公网的一个端口(可以和内部服务器
的端口相同或者不同),使得外部网络的设备可以通过访问公网的端口,其实就可
以访问内网的应用(端口)
[R1-Dialer1]nat server protocol tcp global 202.100.1.1 2323 inside
10.1.10.15 23
Error: The address conflicts with interface or ARP IP //不能直接使用
公网地址
[R1-Dialer1]nat server protocol tcp global current-interface 2323
inside 10.1.10.15 23 //请使用当前接口参数,然后把公网地址的2323端口应用
转发为内网地址10.1.10.15的23端口
[R1]dis nat server
Nat Server Information:
Interface : Dialer1
Global IP/Port : current-interface/2323 (Real IP : 202.100.1.1)
Inside IP/Port : 10.1.10.15/23(telnet)
Protocol : 6(tcp)
××× instance-name : ----
Acl number : ----
Description : ----
Total : 1
测试:
供服务的
Press CTRL_] to quit telnet mode
Trying 202.100.1.1 ...
Connected to 202.100.1.1 ...
Login authentication
Password:
Info: The max number of VTY users is 5, and the number
of current VTY users on line is 1.
The current login time is 2017-12-13 21:16:51.
报文来验证华为的NAT
NAT Session Table Information:
Protocol : TCP(6)
SrcAddr Port *** : 202.100.1.2 65473
DestAddr Port *** : 202.100.1.1 4873
NAT-Info
New SrcAddr : ----
New SrcPort : ----
New DestAddr : 10.1.10.15
New DestPort : 5888
Protocol : TCP(6)
SrcAddr Port *** : 202.100.1.2 23233
DestAddr Port *** : 202.100.1.1 4873
NAT-Info
New SrcAddr : ----
New SrcPort : ----
New DestAddr : 10.1.10.15
New DestPort : 5888 2.2 EASY IP(PAT)
可以和NAT服务器一起使用!可以把指定的内部网络的不同应用转化为一个公网地址
的对应的应用(地址和端口一起转换,即复用!)
acl name NAT 3999
rule 5 permit ip source 10.1.10.0 0.0.0.31 //定义的网络通过NAT转化去访
问互联网,意味着其他网络不做NAT转化
[R1-acl-adv-NAT]int dial 1
[R1-Dialer1]nat outbound 3999 //实施easy IP
[R1]dis nat outbound //验证easy IP(华为这个验证实在不靠谱)
NAT Outbound Information:
Interface Acl Address-group/IP/Interface
Type
Dialer1 3999 202.100.1.1
easyip
Total : 1
测试:
PC>ping 202.100.1.2 //注意此时R2(模拟internet设备)并没有除了直连路由之
外的路由条目,但是依旧可以实现通信,因为做了NAT转换,是202.100.1.1和1.2
在通信
Ping 202.100.1.2: 32 data bytes, Press Ctrl_C to break
From 202.100.1.2: bytes=32 seq=1 ttl=254 time=63 ms
From 202.100.1.2: bytes=32 seq=2 ttl=254 time=47 ms
From 202.100.1.2: bytes=32 seq=3 ttl=254 time=47 ms
From 202.100.1.2: bytes=32 seq=4 ttl=254 time=47 ms
From 202.100.1.2: bytes=32 seq=5 ttl=254 time=46 ms
--- 202.100.1.2 ping statistics ---
5 packet(s) transmitted
5 packet(s) received
0.00% packet loss
round-trip min/avg/max = 46/50/63 ms
[R1]dis acl all //华为的ENSP上,在实施EASY IP的时候不能看到报文的匹配!
验证easy IP请抓包
Total quantity of nonempty ACL number is 1
Advanced ACL NAT 3999, 1 rule
Acl's step is 5
rule 5 permit ip source 10.1.10.0 0.0.0.31
dis ip routing-table
Route Flags: R - relay, D - download to fib
Route Flags: R - relay, D - download to fib
Routing Tables: Public
Destinations : 8 Routes : 8
Destination/Mask Proto Pre Cost Flags NextHop
Interface
202.100.1.0/30 Direct 0 0 D 202.100.1.2 Virtual-Template1
202.100.1.1/32 Direct 0 0 D 202.100.1.1
Virtual-Template1
202.100.1.2/32 Direct 0 0 D 127.0.0.1
Virtual-Template1
202.100.1.3/32 Direct 0 0 D 127.0.0.1
Virtual-Template1
255.255.255.255/32 Direct 0 0 D 127.0.0.1
InLoopBack0
从内网到外网先路由然后NAT转换,反之先转换再NAT!
3.站点到站点的IPSEC ×××
SPD:ACL(即定义哪些流量进行IPSEC ×××处理)
IPSEC的组成:ESP(封装安全负载)、AH(认证头部)、ISAKMP(IKE,互联网秘
钥交换)
2种SA(安全关联):IKE SA;IPSEC SA
在路由的基础上加一层“安全外壳”
加解密点的路由(最少的3条路由):
1)需要有到本地通信设备的路由
2)需要有到远端加密点的路由
3)需要有到远端通信点的路由
SPD:
acl name ×××
rule 5 permit ip source 10.1.10.0 0.0.0.31 destination 10.1.20.0
0.0.0.15
!
[R2-acl-adv-×××]rule 5 permit ip source 10.1.20.0 0.0.0.15 destination
10.1.10.0 0.0.0.31
!
ipsec proposal QYT
esp authentication-algorithm sha1
!
ipsec policy QYT 10 manual
security acl 3998
proposal QYT
tunnel local 202.100.1.1
tunnel remote 202.100.1.2
sa spi inbound esp 12345
sa string-key inbound esp simple huawei
sa spi outbound esp 54321
sa string-key outbound esp simple huawei
ipsec policy QYT 10 manual
security acl 3999
proposal QYT
tunnel local 202.100.1.2
tunnel remote 202.100.1.1
sa spi inbound esp 54321
sa string-key inbound esp simple huawei
sa spi outbound esp 12345
sa string-key outbound esp simple huawei
在一个NAT的环境下实施IPSEC ×××必须在NAT的ACL中拿掉×××流量
acl name NAT 3999
rule 5 deny ip source 10.1.10.0 0.0.0.31 destination 10.1.20.0
0.0.0.15 //用×××处理的流量不做NAT,不能去访问互联网
rule 10 permit ip source 10.1.10.0 0.0.0.31 //访问互联网的流量
[R2-ospf-1]default-route-advertise always
[R2]dis ipsec statistics esp
Inpacket count : 15
Inpacket auth count : 0
Inpacket decap count : 0
Outpacket count : 4
Outpacket auth count : 0
Outpacket encap count : 0
Inpacket drop count : 0
Outpacket drop count : 0
BadAuthLen count : 0
AuthFail count : 0
InSAAclCheckFail count : 0
PktDuplicateDrop count : 0
PktSeqNoTooSmallDrop count: 0
PktInSAMissDrop count : 0
[R2]display ipsec sa brief
Number of SAs:2
Src address Dst address SPI ××× Protocol
Algorithm
202.100.1.1 202.100.1.2 54321 0 ESP E:DES A:SHA1-96
202.100.1.2 202.100.1.1 12345 0 ESP E:DES
A:SHA1-96