- ENSP---通过配置实现client使用域名访问HTTP服务器
W111115_
计算机网络---HCIA服务器运维http网络协议
1.拓补图拓补图2.需求1.有一个完整的网关(路由器);2、左右两边通过交换机建立两个网段;3、Client通过IP访问http服务器、Client通过域名访问http服务器;4、使用192.168.1.0/24进行合理分配;3.需求分析1.给PC1、PC2、Client、百度服务器配置IP地址、掩码、网关。
- Unity中,Canva的三种渲染模式
Lowjin_
unityunity游戏引擎
在Unity中,Canvas组件的渲染模式(RenderMode)决定了UI元素如何渲染在屏幕上。不同的渲染模式有不同的用途和表现,主要有三种模式:屏幕空间-覆盖(ScreenSpace-Overlay)屏幕空间-摄像机(ScreenSpace-Camera)世界空间(WorldSpace)1.屏幕空间-覆盖(ScreenSpace-Overlay)解释:屏幕空间-覆盖是默认的渲染模式。在这种模式
- 微信小程序基础入门
You__An
微信小程序小程序
小程序常用UI组件text文本属性名类型默认值说明selectableBooleanfalse文本是否可选,除了text以外其他组件都无法长按选中spaceString显示连续空格,可选值:ensp英文符大小,emsp中文符大小,nbsp空格大小会根据字体大小而改变decodeBooleanfalse是否解码, <>&' 5<7v
- 基于eNSP的中小企业&校园网络规划与设计
等不到释怀
Ensp网络设计网络华为课程设计毕业设计
一、设计要求整个园区网由三台路由器,两台S5700交换机作为LSW1核心交换机和LSW2备份交换机,一台路由器做为出口,两台路由器作为AR2主路由器和AR3备份路由器。每栋楼作为一个局域网,每栋楼部署一台S3700(LSW3,LSW4.LSW5)交换机,连接到LSW1核心交换机和LSW2备份交换机。核心交换机和备份交换机通过VLAN来和路由器进行连接。在出口AR1路由器上配置NAT,通过NAT技术
- Genspark vs manus
数据分析能量站
机器学习人工智能
1.产品定位与核心技术GensparkSuperAgent定位:由前百度高管景鲲创立的MainFunc公司推出,主打“快速、准确、可控”的通用AIAgent,强调从思考到执行的全闭环能力,聚焦复杂任务自动化(如旅行规划、电话预订)。核心技术:混合代理架构(MoA):集成8个不同规模的LLM(如DeepSeekV3、Claude3.7等)、80+工具集(电话模块、视频生成工具等)及海量精选数据集,动
- eNSP WLAN WDS 手拉手
小王网
毕设课设网络搭建网络计算机网络
目录1.业务需求2.网络拓扑3.网络规划4.网络配置过程4.1VLAN的配置4.2DHCP的配置4.3WLAN的配置4.3.1配置AP上线4.3.2配置无线业务信号发射4.3.3实现WDS手拉手业务4.3.4交换机上行接口和路由配置5.网络互通测试5.1无线连接测试5.2网络连通信测试该文件原价下载请点击后面连接:eNSPWLANWDS手拉手1.业务需求在地铁列车内,WDS桥接技术为乘客提供稳定、
- eNSP企业综合网络设计拓扑图
2301_80344964
ensp综合实验合集网络
1.拓扑图2.拓扑配置此拓扑还有一些瑕疵,仅做参考和技术提升使用。想要配置的可以关注下载大型网络综合实验拓扑图(eNSP)资源-CSDN文库
- Java项目OOM排查
你这个代码我看不懂
java开发语言
排查思路Java项目出现OOM(OutOfMemory,内存溢出)问题时,排查思路如下:确认OOM类型:JavaHeapSpace:堆内存溢出,通常是对象创建过多或内存泄漏。PermGenSpace:永久代内存溢出,通常是类加载过多或类卸载不及时。Metaspace:元空间内存溢出,通常是类加载过多或类卸载不及时。查看GC日志:启用GC日志,查看垃圾回收情况,是否存在频繁的FullGC。分析GC日
- 计算机网络与技术实验报告四:应用层实验
蓝桥蓝桥
计算机网络智能路由器
实验四应用层实验一、实验目的1、掌握DHCP服务器配置过程2、掌握DNS服务器配置过程3、掌握Web服务器配置过程4、掌握FTP服务器配置过程二、实验环境Windows7/10/11,模拟软件华为eNSP三、实验内容设备:华为AR1220路由器2台,PC机2台,S5700交换机3台,Client客户端1台,服务器3台,拓扑结构如图4-1所示。图4-1网络层实验拓扑结构图要求:在实现网络连通的前提下
- 核心实验16_端口镜像_ENSP
garliccc
ENSP实验合集网络
项目场景:核心实验16_端口镜像_ENSP实搭拓扑图:具体操作:交换机:[garliccc]observe-port1interfaceGigabitEthernet0/0/3/设置0/0/3为观察口[garliccc]intg0/0/2[garliccc-GigabitEthernet0/0/2]port-mirroringtoobserve-port1both/报文(包含进和出)镜像发送到观察
- 静态路由ensp实验
Melony♚
大数据
实验:1.除R5的环回地址已固定外,整个其他所有的网段基于192.168.1.0/24进行合理的IP地址划分2.R1-R4每个路由器存在两个环回接口,用于模拟连接PC的网段,地址也在192.168.1.0/24这个网络范围3.R1-R4上不能直接编写到达5.5.5.0/24的静态路由,但依然可以访问4.全网可达,尽量减少每台路由器,路由表条目的数量,避免环路出现5.R4与R5间,正常1000M链路
- 华为ensp 镜像端口协议相关配置
EricTangLF
华为ensp华为网络
镜像端口相关配置。[R1]observe-portinterfaceGigabitEthernet0/0/2#配置观察端口。[R1-GigabitEthernet0/0/0]mirrortoobserve-portinbound#将镜像端口G0/0/0接口入方向流量镜像到观察端口;就是从G0/0/0这个方向往上去的那个路由信息,如果是onbound就是出方向流量信息,相当于从G0/0/1这个方向往
- 几何造型引擎:Parasolid
JiNan.YouQuan.Soft
CAx其他
本文以笔记的形式记录几何造型引擎Parasolid的若干知识点。注1:限于研究水平,分析难免不当,欢迎批评指正。注2:文章内容会不定期更新。一、概述二、主要数据结构三、编程接口参考文献网络资料SiemensParasolidhttps://plm.sw.siemens.com/en-US/plm-components/parasolid/
- 华为eNSP无线AC/AP组网实战
WuYiCheng666
网络智能路由器
1.实验拓扑与基础配置拓扑结构:通常包括出口路由器(AR)、核心交换机(LSW1)、无线接入控制器(AC1)和多个AP设备。IP地址规划:出口路由器接口IP:10.0.0.2/24(连接核心交换机)。AC的VLAN接口IP:172.16.1.2/24(与核心交换机直连)。AP网关地址:192.168.0.1/24(通过核心交换机VLAN5分配)。2.核心交换机与AC的配置核心交换机(LSW1)配置
- 【论文分享】基于社交媒体分析洞察市民的城市绿地文化生态系统服务体验
城市数据研习社
媒体数据分析大数据算法
本次给大家带来一篇SCI论文的全文翻译!该论文针对上海的50个UGS地点,建立了一个感知词典来聚类CES,并通过文本分析研究了景观元素对市民情感的影响。【论文题目】Insightsintocitizens’experiencesofculturalecosystemservicesinurbangreenspacesbasedonsocialmediaanalytics【题目翻译】基于社交媒体分析
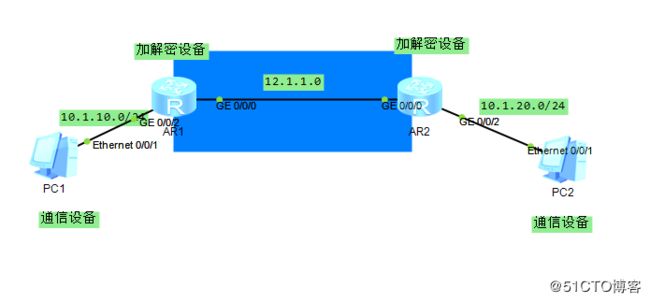
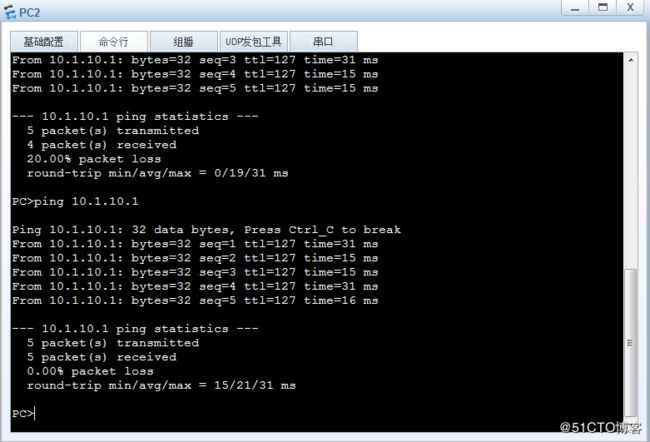
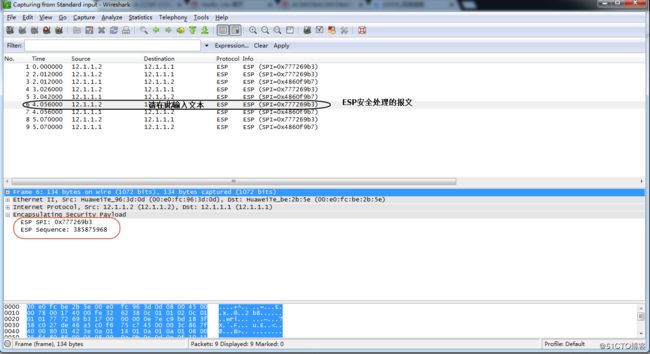
- 基于Ensp的IPsec 实验
网络攻城狮wl
ensp设计网络
目录1.实验拓扑如图2.需求3.需求分析4.ipsec配置顺序5.IPSec的配置1.实验拓扑如图2.需求总部和分部通过IPSecVPN连接总部和分部都能访问外网3.需求分析这个实验既要实现连接,也要实现外网的连接,则需要写两条acl,分别作为ipsec的感兴趣流和外网流量的匹配这个实验的难点在于IPSecVPN的配置,IPSecVPN的配置复杂,而且VPN两边参数不一致,会导致VPN无法建立4.
- scrapy爬取数据
困了又困zZ
scrapypython爬虫
1、安装scrapy2、在终端命令行输入scrapystartproject+文件夹名称(不可和网址名字重复)(base)PSD:\数据采集预处理>scrapystartprojectrenyou_book3、cd命令切换到当前路径下(base)PSD:\数据采集预处理>cd.\renyou_book\4、scrapygenspider+文件夹名称(不能和1重复)+爬取网址(base)PSD:\数
- ENSP配置命令总结
不会C语言6
笔记网络程序人生计算机网络
一、物理层(PhysicalLayer)1.接口基本配置interfaceGigabitEthernet0/0/1speed{10|100|1000|auto}#设置接口速率duplex{half|full|auto}#设置双工模式flow-control#启用流量控制portlink-type{access|trunk}#设置端口类型undoshutdown#激活接口descriptionTO_
- 小程序的内置组件
DustinWangq
#小程序基础进阶小程序
一、Text文本组件1.Text组件解析Text组件用于显示文本,类似于span标签,是行内元素user-select属性决定文本内容是否可以让用户选中space有三个取值(了解)decode是否解码(了解)decode可以解析的有 <>&' 二、Button按钮组件1.Button组件解析Button组件用于创建按钮,默认块级元素常见
- java程序默认使用的xmx_为什么JAVA进程占用内存会超过Xmx设置
保瓶儿
java程序默认使用的xmx
首先要搞清楚JVM的内存机制:JVM内存区域总体分两类,heap区和非heap区(本地内存)。–heap区:堆区分为YoungGen(新生代),TenuredGen(老年代-养老区)。其中新生代又分为EdenSpace(伊甸园)、SurvivorSpace(幸存者区)。–非heap区:CodeCache(代码缓存区)、PermGen(永久代)、JvmStack(java虚拟机栈)、LocalMet
- 华为ensp实现跨vlan通信
小诸葛的博客
华为智能路由器网络
要在网络拓扑中实现主机192.168.1.1、192.168.1.2和192.168.2.1之间的互相通信,需要正确配置交换机(S5700)和路由器(AR3260),以确保不同网段之间的通信(即VLAN间路由)。网络拓扑分析主机:PC1:192.168.1.1/24,连接到S570PC2:192.168.1.2/24,连接到S5700PC3:192.168.2.1/24,连接到S5700设备:S5
- 高质量学术引言如何妙用ChatGPT?如何写提示词?
AIWritePaper智能写作探索
AIWritePaperDeepSeekChatGPT人工智能chatgptAIWritePaperprompt智能写作引言
目录step1、引言究竟是什么?step2、引言如何构建??准备工作:在学术写作领域,巧妙利用人工智能来构建文章的引言和理论框架是一个尚待探索的领域。小编在这篇文章中探讨一种独特的方法,即利用ChatGPT作为工具来构建引言和理论框架。正如史蒂文·斯皮尔伯格(StevenSpielberg)所言,“灵魂的存在无法被想象或言说,更无法被任何算法所创造。”这一观点我们深表认同。事实上,虽然ChatGP
- 华为eNSP综合实验:单臂路由、DHCP、RIP、OSPF、VLAN、ACL
清风&明月
华为网工华为网络
202文章目录202前言试题**一、拓扑图****二、设备****三、内容要求**我的答卷**一、拓扑图****二、提交内容**前言本实验为华为eNSP综合实验,为某学校相关课程期末考试真题,当时没有完全理解,现在由于工作需求,重新温习相关技术,于是想到用本实验来练练手,提升一下实验操作能力。主要涉及交换机VLAN划分、trunk口放通vlan;路由器单臂路由配置、ACL、DHCP配置、RIP配置
- genspark
尸僵打怪兽
genspark智能体
今天遇到一个挺好玩的网站(https://www.genspark.ai/)功能挺强大的支持网页生成,,可转为PDF,还包含其他智能体
- 《eNSP - 常用查看命令》
你可知这世上再难遇我
数通-个人笔记网络华为
netstat-an查看当前所有使用接口及协议displaythis//查看当前接口、模式下的配置displayipinterfacebrief//查看接口的描述信息displayrip1route//查看RIP1的路由表displayportvlan//查看VLAN中包含的接口信息displaydhcpstatistics//查看DHCP报文统计信息displayfrinterfaceSeria
- eNSP 网络基础配置命令总结
⸝⸝ ᷇࿀ ᷆⸝⸝✿
网络智能路由器
目录一、eNSP配置命令二、静态路由配置命令三、DHCP配置命令四、RIP协议配置命令五、OSPF配置命令六、vlan配置命令七、ACL配置命令八、NAT配置命令一、eNSP配置命令不同模式具有不同权限第一级模式该模式可查看所有设备参数system-view键入系统命令[Huawei]第二级模式该模式用于管理设备第三级模式为各种专用配置模式:[Huawei---???][Huawei]interf
- is-is动态路由协议的配置实验结合原理分析理解小白看了都秒懂 isis路由重分发 网段聚合(详细的实验配置文字解析过程)(华为ensp模拟器)
wulimingde
网络原理网络iscsi路由器ripv
IS-IS动态路由协议一、简单介绍IS-IS二、IS-IS的特点三、IS-IS度量值四、IS-IS的邻居关系五、IS-IS使用NSAP地址(难点)1、NSAP地址2、NSAP的格式六、IS-IS实验(rip、路由从分发、网段聚合)详细的文字配置解析1、实验目的以及环境2、实验规划拓扑图3、实验配置(详细的文字解析)R1的配置R2的配置R3的配置R4的配置R5的配置R6的配置4、实验结果检测一、简单
- 爬虫淘宝数据案例,虽说没有一个网站可以限制爬虫的入侵,但能写一个好的爬虫也是非常头疼
技术支持者python,php
scrapy架构完美爬虫项目爬虫scrapyhttp网络协议flask
一.scrapy文档https://www.osgeo.cn/scrapy/intro/tutorial.html1.pipinstallpipenv(安装虚拟环境pipenv)2.pipinstallScrapy(安装Scrapy爬虫框架)3.scrapystartprojectArticleSpider(使用scrapy创建一个工程ArticleSpider)4.scrapygenspider
- 华为eNSP:汇总实验
23zhgjx_ywz
华为
一、实验拓扑实验的技术有:vlan的划分、vlan间的通信、静态路由、基本acl、easy-ip实验要求:VLAN之间进行通信用easy-ip是内网访问外网实验步骤:LSW1交换机划分VLAN:system-view//进入系统视图[Huawei]undoinfo-centerenable//关闭路由器输出信息[Huawei]sysnameLSW1//修改设备名为LSW1[LSW1]vlanbat
- 华为ensp的缺省_华为-ensp,IS-IS详细实验配置及解析
weixin_39864591
华为ensp的缺省
IS-IS配置:ISIS认证:接口认证:如果配置了send-only则表示仅对发送的Hello封装认证信息,而不检查收到的Hello报文是否通过了认证。在本端不需要进行认证检查且对端认证通过时,才可以建立起邻居关系。如果没有配置send-only,此时应保证同一网络所有接口的相同级别的认证密码一致。区域认证或路由器域认证:对发送的LSP和SNP都封装认证信息,并检查收到的LSP和SNP是否通过认证
- java责任链模式
3213213333332132
java责任链模式村民告县长
责任链模式,通常就是一个请求从最低级开始往上层层的请求,当在某一层满足条件时,请求将被处理,当请求到最高层仍未满足时,则请求不会被处理。
就是一个请求在这个链条的责任范围内,会被相应的处理,如果超出链条的责任范围外,请求不会被相应的处理。
下面代码模拟这样的效果:
创建一个政府抽象类,方便所有的具体政府部门继承它。
package 责任链模式;
/**
*
- linux、mysql、nginx、tomcat 性能参数优化
ronin47
一、linux 系统内核参数
/etc/sysctl.conf文件常用参数 net.core.netdev_max_backlog = 32768 #允许送到队列的数据包的最大数目
net.core.rmem_max = 8388608 #SOCKET读缓存区大小
net.core.wmem_max = 8388608 #SOCKET写缓存区大
- php命令行界面
dcj3sjt126com
PHPcli
常用选项
php -v
php -i PHP安装的有关信息
php -h 访问帮助文件
php -m 列出编译到当前PHP安装的所有模块
执行一段代码
php -r 'echo "hello, world!";'
php -r 'echo "Hello, World!\n";'
php -r '$ts = filemtime("
- Filter&Session
171815164
session
Filter
HttpServletRequest requ = (HttpServletRequest) req;
HttpSession session = requ.getSession();
if (session.getAttribute("admin") == null) {
PrintWriter out = res.ge
- 连接池与Spring,Hibernate结合
g21121
Hibernate
前几篇关于Java连接池的介绍都是基于Java应用的,而我们常用的场景是与Spring和ORM框架结合,下面就利用实例学习一下这方面的配置。
1.下载相关内容: &nb
- [简单]mybatis判断数字类型
53873039oycg
mybatis
昨天同事反馈mybatis保存不了int类型的属性,一直报错,错误信息如下:
Caused by: java.lang.NumberFormatException: For input string: "null"
at sun.mis
- 项目启动时或者启动后ava.lang.OutOfMemoryError: PermGen space
程序员是怎么炼成的
eclipsejvmtomcatcatalina.sheclipse.ini
在启动比较大的项目时,因为存在大量的jsp页面,所以在编译的时候会生成很多的.class文件,.class文件是都会被加载到jvm的方法区中,如果要加载的class文件很多,就会出现方法区溢出异常 java.lang.OutOfMemoryError: PermGen space.
解决办法是点击eclipse里的tomcat,在
- 我的crm小结
aijuans
crm
各种原因吧,crm今天才完了。主要是接触了几个新技术:
Struts2、poi、ibatis这几个都是以前的项目中用过的。
Jsf、tapestry是这次新接触的,都是界面层的框架,用起来也不难。思路和struts不太一样,传说比较简单方便。不过个人感觉还是struts用着顺手啊,当然springmvc也很顺手,不知道是因为习惯还是什么。jsf和tapestry应用的时候需要知道他们的标签、主
- spring里配置使用hibernate的二级缓存几步
antonyup_2006
javaspringHibernatexmlcache
.在spring的配置文件中 applicationContent.xml,hibernate部分加入
xml 代码
<prop key="hibernate.cache.provider_class">org.hibernate.cache.EhCacheProvider</prop>
<prop key="hi
- JAVA基础面试题
百合不是茶
抽象实现接口String类接口继承抽象类继承实体类自定义异常
/* * 栈(stack):主要保存基本类型(或者叫内置类型)(char、byte、short、 *int、long、 float、double、boolean)和对象的引用,数据可以共享,速度仅次于 * 寄存器(register),快于堆。堆(heap):用于存储对象。 */ &
- 让sqlmap文件 "继承" 起来
bijian1013
javaibatissqlmap
多个项目中使用ibatis , 和数据库表对应的 sqlmap文件(增删改查等基本语句),dao, pojo 都是由工具自动生成的, 现在将这些自动生成的文件放在一个单独的工程中,其它项目工程中通过jar包来引用 ,并通过"继承"为基础的sqlmap文件,dao,pojo 添加新的方法来满足项
- 精通Oracle10编程SQL(13)开发触发器
bijian1013
oracle数据库plsql
/*
*开发触发器
*/
--得到日期是周几
select to_char(sysdate+4,'DY','nls_date_language=AMERICAN') from dual;
select to_char(sysdate,'DY','nls_date_language=AMERICAN') from dual;
--建立BEFORE语句触发器
CREATE O
- 【EhCache三】EhCache查询
bit1129
ehcache
本文介绍EhCache查询缓存中数据,EhCache提供了类似Hibernate的查询API,可以按照给定的条件进行查询。
要对EhCache进行查询,需要在ehcache.xml中设定要查询的属性
数据准备
@Before
public void setUp() {
//加载EhCache配置文件
Inpu
- CXF框架入门实例
白糖_
springWeb框架webserviceservlet
CXF是apache旗下的开源框架,由Celtix + XFire这两门经典的框架合成,是一套非常流行的web service框架。
它提供了JAX-WS的全面支持,并且可以根据实际项目的需要,采用代码优先(Code First)或者 WSDL 优先(WSDL First)来轻松地实现 Web Services 的发布和使用,同时它能与spring进行完美结合。
在apache cxf官网提供
- angular.equals
boyitech
AngularJSAngularJS APIAnguarJS 中文APIangular.equals
angular.equals
描述:
比较两个值或者两个对象是不是 相等。还支持值的类型,正则表达式和数组的比较。 两个值或对象被认为是 相等的前提条件是以下的情况至少能满足一项:
两个值或者对象能通过=== (恒等) 的比较
两个值或者对象是同样类型,并且他们的属性都能通过angular
- java-腾讯暑期实习生-输入一个数组A[1,2,...n],求输入B,使得数组B中的第i个数字B[i]=A[0]*A[1]*...*A[i-1]*A[i+1]
bylijinnan
java
这道题的具体思路请参看 何海涛的微博:http://weibo.com/zhedahht
import java.math.BigInteger;
import java.util.Arrays;
public class CreateBFromATencent {
/**
* 题目:输入一个数组A[1,2,...n],求输入B,使得数组B中的第i个数字B[i]=A
- FastDFS 的安装和配置 修订版
Chen.H
linuxfastDFS分布式文件系统
FastDFS Home:http://code.google.com/p/fastdfs/
1. 安装
http://code.google.com/p/fastdfs/wiki/Setup http://hi.baidu.com/leolance/blog/item/3c273327978ae55f93580703.html
安装libevent (对libevent的版本要求为1.4.
- [强人工智能]拓扑扫描与自适应构造器
comsci
人工智能
当我们面对一个有限拓扑网络的时候,在对已知的拓扑结构进行分析之后,发现在连通点之后,还存在若干个子网络,且这些网络的结构是未知的,数据库中并未存在这些网络的拓扑结构数据....这个时候,我们该怎么办呢?
那么,现在我们必须设计新的模块和代码包来处理上面的问题
- oracle merge into的用法
daizj
oraclesqlmerget into
Oracle中merge into的使用
http://blog.csdn.net/yuzhic/article/details/1896878
http://blog.csdn.net/macle2010/article/details/5980965
该命令使用一条语句从一个或者多个数据源中完成对表的更新和插入数据. ORACLE 9i 中,使用此命令必须同时指定UPDATE 和INSE
- 不适合使用Hadoop的场景
datamachine
hadoop
转自:http://dev.yesky.com/296/35381296.shtml。
Hadoop通常被认定是能够帮助你解决所有问题的唯一方案。 当人们提到“大数据”或是“数据分析”等相关问题的时候,会听到脱口而出的回答:Hadoop! 实际上Hadoop被设计和建造出来,是用来解决一系列特定问题的。对某些问题来说,Hadoop至多算是一个不好的选择,对另一些问题来说,选择Ha
- YII findAll的用法
dcj3sjt126com
yii
看文档比较糊涂,其实挺简单的:
$predictions=Prediction::model()->findAll("uid=:uid",array(":uid"=>10));
第一个参数是选择条件:”uid=10″。其中:uid是一个占位符,在后面的array(“:uid”=>10)对齐进行了赋值;
更完善的查询需要
- vim 常用 NERDTree 快捷键
dcj3sjt126com
vim
下面给大家整理了一些vim NERDTree的常用快捷键了,这里几乎包括了所有的快捷键了,希望文章对各位会带来帮助。
切换工作台和目录
ctrl + w + h 光标 focus 左侧树形目录ctrl + w + l 光标 focus 右侧文件显示窗口ctrl + w + w 光标自动在左右侧窗口切换ctrl + w + r 移动当前窗口的布局位置
o 在已有窗口中打开文件、目录或书签,并跳
- Java把目录下的文件打印出来
蕃薯耀
列出目录下的文件文件夹下面的文件目录下的文件
Java把目录下的文件打印出来
>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>>
蕃薯耀 2015年7月11日 11:02:
- linux远程桌面----VNCServer与rdesktop
hanqunfeng
Desktop
windows远程桌面到linux,需要在linux上安装vncserver,并开启vnc服务,同时需要在windows下使用vnc-viewer访问Linux。vncserver同时支持linux远程桌面到linux。
linux远程桌面到windows,需要在linux上安装rdesktop,同时开启windows的远程桌面访问。
下面分别介绍,以windo
- guava中的join和split功能
jackyrong
java
guava库中,包含了很好的join和split的功能,例子如下:
1) 将LIST转换为使用字符串连接的字符串
List<String> names = Lists.newArrayList("John", "Jane", "Adam", "Tom");
- Web开发技术十年发展历程
lampcy
androidWeb浏览器html5
回顾web开发技术这十年发展历程:
Ajax
03年的时候我上六年级,那时候网吧刚在小县城的角落萌生。传奇,大话西游第一代网游一时风靡。我抱着试一试的心态给了网吧老板两块钱想申请个号玩玩,然后接下来的一个小时我一直在,注,册,账,号。
彼时网吧用的512k的带宽,注册的时候,填了一堆信息,提交,页面跳转,嘣,”您填写的信息有误,请重填”。然后跳转回注册页面,以此循环。我现在时常想,如果当时a
- 架构师之mima-----------------mina的非NIO控制IOBuffer(说得比较好)
nannan408
buffer
1.前言。
如题。
2.代码。
IoService
IoService是一个接口,有两种实现:IoAcceptor和IoConnector;其中IoAcceptor是针对Server端的实现,IoConnector是针对Client端的实现;IoService的职责包括:
1、监听器管理
2、IoHandler
3、IoSession
- ORA-00054:resource busy and acquire with NOWAIT specified
Everyday都不同
oraclesessionLock
[Oracle]
今天对一个数据量很大的表进行操作时,出现如题所示的异常。此时表明数据库的事务处于“忙”的状态,而且被lock了,所以必须先关闭占用的session。
step1,查看被lock的session:
select t2.username, t2.sid, t2.serial#, t2.logon_time
from v$locked_obj
- javascript学习笔记
tntxia
JavaScript
javascript里面有6种基本类型的值:number、string、boolean、object、function和undefined。number:就是数字值,包括整数、小数、NaN、正负无穷。string:字符串类型、单双引号引起来的内容。boolean:true、false object:表示所有的javascript对象,不用多说function:我们熟悉的方法,也就是
- Java enum的用法详解
xieke90
enum枚举
Java中枚举实现的分析:
示例:
public static enum SEVERITY{
INFO,WARN,ERROR
}
enum很像特殊的class,实际上enum声明定义的类型就是一个类。 而这些类都是类库中Enum类的子类 (java.l