1.
准备配置文件
[root@k8s-master1 ~]# wget https://raw.githubusercontent.com/kubernetes/dashboard/master/aio/deploy/recommended/kubernetes-dashboard.yaml
--2019-04-23 11:11:25-- https://raw.githubusercontent.com/kubernetes/dashboard/master/aio/deploy/recommended/kubernetes-dashboard.yaml
Resolving raw.githubusercontent.com (raw.githubusercontent.com)... 199.232.4.133
Connecting to raw.githubusercontent.com (raw.githubusercontent.com)|199.232.4.133|:443... connected.
HTTP request sent, awaiting response... 200 OK
Length: 4784 (4.7K) [text/plain]
Saving to: ‘kubernetes-dashboard.yaml’
100%[==================================================================>] 4,784 --.-K/s in 0.004s
[root@k8s-master1 dashboard]# ls
kubernetes-dashboard.yaml2.
配置文件简单了解
[root@k8s-master1 dashboard]# cat kubernetes-dashboard.yaml
# Copyright 2017 The Kubernetes Authors.
#
# Licensed under the Apache License, Version 2.0 (the "License");
# you may not use this file except in compliance with the License.
# You may obtain a copy of the License at
#
# http://www.apache.org/licenses/LICENSE-2.0
#
# Unless required by applicable law or agreed to in writing, software
# distributed under the License is distributed on an "AS IS" BASIS,
# WITHOUT WARRANTIES OR CONDITIONS OF ANY KIND, either express or implied.
# See the License for the specific language governing permissions and
# limitations under the License.
# ------------------- Dashboard Secrets ------------------- #
apiVersion: v1
kind: Secret
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard-certs
namespace: kube-system
type: Opaque
---
apiVersion: v1
kind: Secret
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard-csrf
namespace: kube-system
type: Opaque
data:
csrf: ""
---
# ------------------- Dashboard Service Account ------------------- #
apiVersion: v1
kind: ServiceAccount
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
---
# ------------------- Dashboard Role & Role Binding ------------------- #
kind: Role
apiVersion: rbac.authorization.k8s.io/v1
metadata:
name: kubernetes-dashboard-minimal
namespace: kube-system
rules:
# Allow Dashboard to create 'kubernetes-dashboard-key-holder' secret.
- apiGroups: [""]
resources: ["secrets"]
verbs: ["create"]
# Allow Dashboard to create 'kubernetes-dashboard-settings' config map.
- apiGroups: [""]
resources: ["configmaps"]
verbs: ["create"]
# Allow Dashboard to get, update and delete Dashboard exclusive secrets.
- apiGroups: [""]
resources: ["secrets"]
resourceNames: ["kubernetes-dashboard-key-holder", "kubernetes-dashboard-certs", "kubernetes-dashboard-csrf"]
verbs: ["get", "update", "delete"]
# Allow Dashboard to get and update 'kubernetes-dashboard-settings' config map.
- apiGroups: [""]
resources: ["configmaps"]
resourceNames: ["kubernetes-dashboard-settings"]
verbs: ["get", "update"]
# Allow Dashboard to get metrics from heapster.
- apiGroups: [""]
resources: ["services"]
resourceNames: ["heapster"]
verbs: ["proxy"]
- apiGroups: [""]
resources: ["services/proxy"]
resourceNames: ["heapster", "http:heapster:", "https:heapster:"]
verbs: ["get"]
---
apiVersion: rbac.authorization.k8s.io/v1
kind: RoleBinding
metadata:
name: kubernetes-dashboard-minimal
namespace: kube-system
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: Role
name: kubernetes-dashboard-minimal
subjects:
- kind: ServiceAccount
name: kubernetes-dashboard
namespace: kube-system
---
# ------------------- Dashboard Deployment ------------------- #
kind: Deployment
apiVersion: apps/v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
spec:
replicas: 1
revisionHistoryLimit: 10
selector:
matchLabels:
k8s-app: kubernetes-dashboard
template:
metadata:
labels:
k8s-app: kubernetes-dashboard
spec:
containers:
- name: kubernetes-dashboard
image: k8s.gcr.io/kubernetes-dashboard-amd64:v1.10.1
ports:
- containerPort: 8443
protocol: TCP
args:
- --auto-generate-certificates
# Uncomment the following line to manually specify Kubernetes API server Host
# If not specified, Dashboard will attempt to auto discover the API server and connect
# to it. Uncomment only if the default does not work.
# - --apiserver-host=http://my-address:port
volumeMounts:
- name: kubernetes-dashboard-certs
mountPath: /certs
# Create on-disk volume to store exec logs
- mountPath: /tmp
name: tmp-volume
livenessProbe:
httpGet:
scheme: HTTPS
path: /
port: 8443
initialDelaySeconds: 30
timeoutSeconds: 30
volumes:
- name: kubernetes-dashboard-certs
secret:
secretName: kubernetes-dashboard-certs
- name: tmp-volume
emptyDir: {}
serviceAccountName: kubernetes-dashboard
# Comment the following tolerations if Dashboard must not be deployed on master
tolerations:
- key: node-role.kubernetes.io/master
effect: NoSchedule
---
# ------------------- Dashboard Service ------------------- #
kind: Service
apiVersion: v1
metadata:
labels:
k8s-app: kubernetes-dashboard
name: kubernetes-dashboard
namespace: kube-system
spec:
ports:
- port: 443
targetPort: 8443
selector:
k8s-app: kubernetes-dashboard
[root@k8s-master1 dashboard]# 创建sa:kubernetes-dashboard 并指定了权限,用这个sa登陆dashboard
3.
部署
[root@k8s-master1 dashboard]# kubectl apply -f kubernetes-dashboard.yaml
secret "kubernetes-dashboard-certs" created
secret "kubernetes-dashboard-csrf" created
serviceaccount "kubernetes-dashboard" created
role.rbac.authorization.k8s.io "kubernetes-dashboard-minimal" created
rolebinding.rbac.authorization.k8s.io "kubernetes-dashboard-minimal" created
deployment.apps "kubernetes-dashboard" created
service "kubernetes-dashboard" created
[root@k8s-master1 dashboard]#
[root@k8s-master1 dashboard]# kubectl get svc,pod -n kube-system
NAME TYPE CLUSTER-IP EXTERNAL-IP PORT(S) AGE
service/kube-dns ClusterIP 10.254.0.2 53/UDP,53/TCP 20h
service/kubernetes-dashboard ClusterIP 10.254.61.18 443/TCP 5s
service/traefik-ingress-service ClusterIP 10.254.83.91 192.168.32.127 80/TCP,8080/TCP 3h
service/traefik-web-ui ClusterIP 10.254.124.127 80/TCP 21h
NAME READY STATUS RESTARTS AGE
pod/coredns-779ffd89bd-pz6s2 0/1 Unknown 1 20h
pod/coredns-779ffd89bd-wmzhf 1/1 Running 1 3h
pod/kubernetes-dashboard-65c76f6c97-zq6wr 1/1 Running 0 4s
pod/traefik-ingress-controller-6545547764-22jx6 1/1 Running 0 3h
pod/traefik-ingress-controller-6545547764-66wb8 1/1 Running 0 3h
pod/traefik-ingress-controller-6545547764-9dbt6 1/1 Running 0 3h
pod/traefik-ingress-controller-6545547764-vrf8h 1/1 Running 0 3h 4.
如何访问dashboard
用traefik配置访问dashboard
创建个Ing
[root@k8s-master1 dashboard]# cat dashboard-svc-ingress.yaml
apiVersion: extensions/v1beta1
kind: Ingress
metadata:
name: dashboard-ingress
namespace: kube-system
spec:
rules:
- host: dashboard-ingress
http:
paths:
- path: /
backend:
serviceName: kubernetes-dashboard
servicePort: 443
[root@k8s-master1 dashboard]#[root@k8s-master1 dashboard]# kubectl apply -f dashboard-svc-ingress.yaml
ingress.extensions "dashboard-ingress" created
[root@k8s-master1 dashboard]# kubectl get ing
NAME HOSTS ADDRESS PORTS AGE
httpd-svc-ingress httpd-svc.ingress 80 21h
[root@k8s-master1 dashboard]# kubectl get ing -n kube-system
NAME HOSTS ADDRESS PORTS AGE
dashboard-ingress dashboard-ingress 80 11s
traefik-web-ui traefik-ui.minikube 80 21h绑定域名,我这里是绑定dashboard-ingress到ip 192.168.32.127
访问浏览器页面报错:Internal Server Error
pod报错:
[root@k8s-master1 traefik]# kubectl get pod -n kube-system
NAME READY STATUS RESTARTS AGE
coredns-779ffd89bd-wmzhf 1/1 Running 3 1d
kubernetes-dashboard-65c76f6c97-m29nl 1/1 Running 2 19h
traefik-ingress-controller-c6978f9f7-4c767 1/1 Running 0 2m
traefik-ingress-controller-c6978f9f7-8fvjk 1/1 Running 0 2m
traefik-ingress-controller-c6978f9f7-hjfvb 1/1 Running 0 2m
[root@k8s-master1 traefik]# kubectl logs traefik-ingress-controller-c6978f9f7-hjfvb -n kube-system
time="2019-04-25T02:40:45Z" level=info msg="Using TOML configuration file /config/traefik.toml"
time="2019-04-25T02:40:45Z" level=info msg="No tls.defaultCertificate given for https: using the first item in tls.certificates as a fallback."
time="2019-04-25T02:40:45Z" level=info msg="Traefik version v1.7.10 built on 2019-03-29_12:20:34PM"
time="2019-04-25T02:40:45Z" level=info msg="\nStats collection is disabled.\nHelp us improve Traefik by turning this feature on :)\nMore details on: https://docs.traefik.io/basics/#collected-data\n"
time="2019-04-25T02:40:45Z" level=info msg="Preparing server traefik &{Address::8080 TLS: Redirect: Auth: WhitelistSourceRange:[] WhiteList: Compress:false ProxyProtocol: ForwardedHeaders:0xc000735760} with readTimeout=0s writeTimeout=0s idleTimeout=3m0s"
time="2019-04-25T02:40:45Z" level=info msg="Preparing server http &{Address::80 TLS: Redirect:0xc000082340 Auth: WhitelistSourceRange:[] WhiteList: Compress:false ProxyProtocol: ForwardedHeaders:0xc000735780} with readTimeout=0s writeTimeout=0s idleTimeout=3m0s"
time="2019-04-25T02:40:45Z" level=info msg="Preparing server https &{Address::443 TLS:0xc00021d170 Redirect: Auth: WhitelistSourceRange:[] WhiteList: Compress:false ProxyProtocol: ForwardedHeaders:0xc000735740} with readTimeout=0s writeTimeout=0s idleTimeout=3m0s"
time="2019-04-25T02:40:45Z" level=info msg="Starting provider configuration.ProviderAggregator {}"
time="2019-04-25T02:40:45Z" level=info msg="Starting server on :8080"
time="2019-04-25T02:40:45Z" level=info msg="Starting server on :80"
time="2019-04-25T02:40:45Z" level=info msg="Starting server on :443"
time="2019-04-25T02:40:45Z" level=info msg="Starting provider *kubernetes.Provider {\"Watch\":true,\"Filename\":\"\",\"Constraints\":[],\"Trace\":false,\"TemplateVersion\":0,\"DebugLogGeneratedTemplate\":false,\"Endpoint\":\"\",\"Token\":\"\",\"CertAuthFilePath\":\"\",\"DisablePassHostHeaders\":false,\"EnablePassTLSCert\":false,\"Namespaces\":null,\"LabelSelector\":\"\",\"IngressClass\":\"\",\"IngressEndpoint\":null}"
time="2019-04-25T02:40:45Z" level=info msg="ingress label selector is: \"\""
time="2019-04-25T02:40:45Z" level=info msg="Creating in-cluster Provider client"
time="2019-04-25T02:40:46Z" level=info msg="Server configuration reloaded on :80"
time="2019-04-25T02:40:46Z" level=info msg="Server configuration reloaded on :443"
time="2019-04-25T02:40:46Z" level=info msg="Server configuration reloaded on :8080"
time="2019-04-25T02:40:48Z" level=info msg="Server configuration reloaded on :80"
time="2019-04-25T02:40:48Z" level=info msg="Server configuration reloaded on :443"
time="2019-04-25T02:40:48Z" level=info msg="Server configuration reloaded on :8080"
[root@k8s-master1 traefik]# 主要报错是这条:
No tls.defaultCertificate given for https: using the first item in tls.certificates as a fallback4.
学习traefik基础知识,解决这个问题
traefik基础篇有讲过访问得几种方式,见下:
client --- (via http) ---> traefik ---- (via http) ----> services
client --- (via https) ---> traefik ---- (via http) ----> services
client --- (via https) ---> traefik ---- (via https) ----> services前面两种都在基础篇测试成功,dashboard是第三种.
这种方式非常复杂,有以下两种情况。
第一种:
是ssl-termination的安全配置模型,即client与svc8的https通信分为“两段”,client与traefik建立https连接后,traefik将client提交的加密请求解密后,
再向svc发起https请求,并重新加密请求数据.这种client端ssl的过程在反向代理或负载均衡器终结的https通信方式被称为“ssl-termination”.
第二种:
ssl-passthrough的安全配置模型,即traefik不会对client的https request进行解密,而是直接转发给svc服务,client端的ssl过程不会终结于traefik,
而是在svc对应的pod中终结.这种https通信方式被称为”ssl-passthrough”.这种配置模型尤其适合service对client端进行client certificate验证的情况.
无法访问dashboard的原因是:
因为dashboard本身就是https的结构,自带证书,无法通过自带证书的检查和认证.所以无法访问dashboard.
解决方法:
在traefik.toml中加入条参数:
insecureSkipVerify = true 这条的意思是:禁止traefik对service后端证书检查
修改后的配置文件见下:
[root@k8s-master1 config]# cat traefik.toml
insecureSkipVerify = true
defaultEntryPoints = ["http","https"]
[entryPoints]
[entryPoints.http]
address = ":80"
[entryPoints.http.redirect]
entryPoint = "https"
[entryPoints.https]
address = ":443"
[entryPoints.https.tls]
[[entryPoints.https.tls.certificates]]
certFile = "/etc/kubernetes/cert/ca.pem"
keyFile = "/etc/kubernetes/cert/ca-key.pem"
[root@k8s-master1 config]#重新生成configmap
[root@k8s-master1 config]# kubectl delete cm traefik-conf -n kube-system
configmap "traefik-conf" deleted
[root@k8s-master1 config]# kubectl create configmap traefik-conf --from-file=traefik.toml -n kube-system
configmap "traefik-conf" created
[root@k8s-master1 config]#重新部署traefik
[root@k8s-master1 traefik]# kubectl delete -f traefik-deployment.yaml
serviceaccount "traefik-ingress-controller" deleted
deployment.extensions "traefik-ingress-controller" deleted
service "traefik-ingress-service" deleted[root@k8s-master1 traefik]# kubectl apply -f traefik-deployment.yaml
serviceaccount "traefik-ingress-controller" created
deployment.extensions "traefik-ingress-controller" created
service "traefik-ingress-service" created
[root@k8s-master1 traefik]#[root@k8s-master1 traefik]# kubectl get pod -n kube-system
NAME READY STATUS RESTARTS AGE
coredns-779ffd89bd-wmzhf 1/1 Running 3 1d
kubernetes-dashboard-65c76f6c97-m29nl 1/1 Running 2 20h
traefik-ingress-controller-c6978f9f7-lkfss 1/1 Running 0 12s
traefik-ingress-controller-c6978f9f7-tsvrb 1/1 Running 0 12s
traefik-ingress-controller-c6978f9f7-xxz2w 1/1 Running 0 12s
[root@k8s-master1 traefik]#再测试访问dashboard,测试成功
5.
登陆dashboard
用部署时创建的sa:kubernetes-dashboard登陆
检索它的token
[root@k8s-master1 traefik]# kubectl describe sa kubernetes-dashboard -n kube-system
Name: kubernetes-dashboard
Namespace: kube-system
Labels: k8s-app=kubernetes-dashboard
Annotations: kubectl.kubernetes.io/last-applied-configuration={"apiVersion":"v1","kind":"ServiceAccount","metadata":{"annotations":{},"labels":{"k8s-app":"kubernetes-dashboard"},"name":"kubernetes-dashboard","name...
Image pull secrets:
Mountable secrets: kubernetes-dashboard-token-82x7w
Tokens: kubernetes-dashboard-token-82x7w
Events:
kubernetes-dashboard-token-82x7w kubernetes.io/service-account-token 3 20h [root@k8s-master1 traefik]# kubectl describe secret kubernetes-dashboard-token-82x7w -n kube-system
Name: kubernetes-dashboard-token-82x7w
Namespace: kube-system
Labels:
Annotations: kubernetes.io/service-account.name=kubernetes-dashboard
kubernetes.io/service-account.uid=b9900f44-665c-11e9-b233-000c291d7023
Type: kubernetes.io/service-account-token
Data
====
ca.crt: 1338 bytes
namespace: 11 bytes
token: eyJhbGciOiJSUzI1NiIsImtpZCI6IiJ9.eyJpc3MiOiJrdWJlcm5ldGVzL3NlcnZpY2VhY2NvdW50Iiwia3ViZXJuZXRlcy5pby9zZXJ2aWNlYWNjb3VudC9uYW1lc3BhY2UiOiJrdWJlLXN5c3RlbSIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VjcmV0Lm5hbWUiOiJrdWJlcm5ldGVzLWRhc2hib2FyZC10b2tlbi04Mng3dyIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50Lm5hbWUiOiJrdWJlcm5ldGVzLWRhc2hib2FyZCIsImt1YmVybmV0ZXMuaW8vc2VydmljZWFjY291bnQvc2VydmljZS1hY2NvdW50LnVpZCI6ImI5OTAwZjQ0LTY2NWMtMTFlOS1iMjMzLTAwMGMyOTFkNzAyMyIsInN1YiI6InN5c3RlbTpzZXJ2aWNlYWNjb3VudDprdWJlLXN5c3RlbTprdWJlcm5ldGVzLWRhc2hib2FyZCJ9.Dml76hUlYVwCITgeui32CTGjyySfsmMzGQWwOHG-mDtrvsDTswu_KZbANcUL37XUAQeNycUNELavdGnvsZAfT8XmkwUU7VzvyCY3MKj1vRCrVGchiQ5KDoxJIJGieWm3GffLmo23BsysjbVPSR_jCSWCVkBYGhezb2TGN3E7rtOvsl0Zr8cw4o_BaA4KROtjB8yLsSNlbNP-mAsL5unpkbOPr2e5JH7FO1ZzJnczc7C0RFwAqVQ8oPGu8Kft1JrKBoL_HpjCutJy6rNiFelS27SfC0OShtsSn-ioGLSDsaxPYXhJKmmtYE0D6h5xUCqyG-gnne0UZVjXSU_AaMxaSw
[root@k8s-master1 traefik]# token就是登陆需要输入的.
6.
登陆成功,但是报错很多,见下:
configmaps is forbidden: User "system:serviceaccount:kube-system:kubernetes-dashboard" cannot list resource "configmaps" in API group "" in the namespace "default"
persistentvolumeclaims is forbidden: User "system:serviceaccount:kube-system:kubernetes-dashboard" cannot list resource "persistentvolumeclaims" in API group "" in the namespace "default"
secrets is forbidden: User "system:serviceaccount:kube-system:kubernetes-dashboard" cannot list resource "secrets" in API group "" in the namespace "default"
services is forbidden: User "system:serviceaccount:kube-system:kubernetes-dashboard" cannot list resource "services" in API group "" in the namespace "default"
ingresses.extensions is forbidden: User "system:serviceaccount:kube-system:kubernetes-dashboard" cannot list resource "ingresses" in API group "extensions" in the namespace "default"
daemonsets.apps is forbidden: User "system:serviceaccount:kube-system:kubernetes-dashboard" cannot list resource "daemonsets" in API group "apps" in the namespace "default"
pods is forbidden: User "system:serviceaccount:kube-system:kubernetes-dashboard" cannot list resource "pods" in API group "" in the namespace "default"
events is forbidden: User "system:serviceaccount:kube-system:kubernetes-dashboard" cannot list resource "events" in API group "" in the namespace "default"
deployments.apps is forbidden: User "system:serviceaccount:kube-system:kubernetes-dashboard" cannot list resource "deployments" in API group "apps" in the namespace "default"
replicasets.apps is forbidden: User "system:serviceaccount:kube-system:kubernetes-dashboard" cannot list resource "replicasets" in API group "apps" in the namespace "default"
jobs.batch is forbidden: User "system:serviceaccount:kube-system:kubernetes-dashboard" cannot list resource "jobs" in API group "batch" in the namespace "default"
cronjobs.batch is forbidden: User "system:serviceaccount:kube-system:kubernetes-dashboard" cannot list resource "cronjobs" in API group "batch" in the namespace "default"
replicationcontrollers is forbidden: User "system:serviceaccount:kube-system:kubernetes-dashboard" cannot list resource "replicationcontrollers" in API group "" in the namespace "default"
statefulsets.apps is forbidden: User "system:serviceaccount:kube-system:kubernetes-dashboard" cannot list resource "statefulsets" in API group "apps" in the namespace "default"rbac权限问题.
把sa:kubernetes-dashboard绑定cluster-admin权限
[root@k8s-master1 traefik]# kubectl describe clusterroles cluster-admin
Name: cluster-admin
Labels: kubernetes.io/bootstrapping=rbac-defaults
Annotations: rbac.authorization.kubernetes.io/autoupdate=true
PolicyRule:
Resources Non-Resource URLs Resource Names Verbs
--------- ----------------- -------------- -----
*.* [] [] [*]
[*] [] [*]
[root@k8s-master1 traefik]#[root@k8s-master1 traefik]# cat kubernetes-dashboard-admin_clusterroles.yaml
apiVersion: rbac.authorization.k8s.io/v1beta1
kind: ClusterRoleBinding
metadata:
name: kubernetes-dashboard
roleRef:
apiGroup: rbac.authorization.k8s.io
kind: ClusterRole
name: cluster-admin
subjects:
- kind: ServiceAccount
name: kubernetes-dashboard
namespace: kube-system
[root@k8s-master1 traefik]#[root@k8s-master1 traefik]# kubectl apply -f kubernetes-dashboard-admin_clusterroles.yaml
clusterrolebinding.rbac.authorization.k8s.io "kubernetes-dashboard" created7.
重新登陆,一切正常.
8.
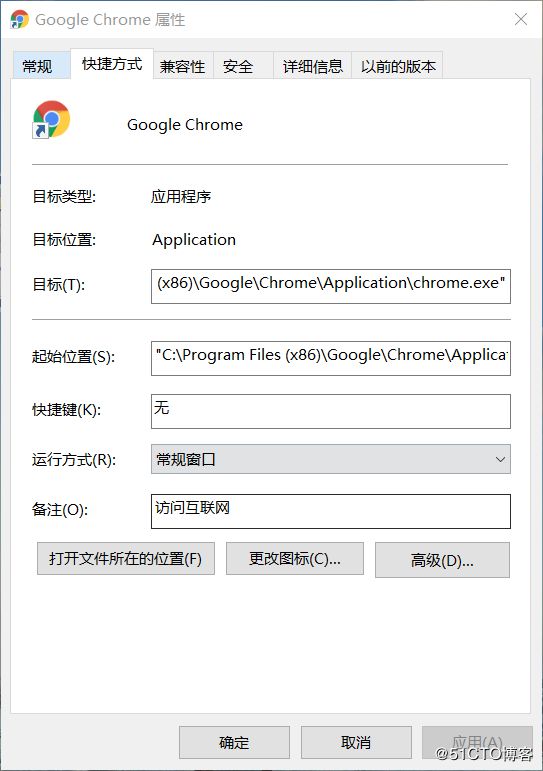
忽略chrome报错,提高访问速度
chrome打开访问的时候,一直报一个错误
登陆进去也是非常卡顿.
这个报错是可以忽略的.
鼠标右键点chrome的快捷方式选择属性
在目标这里 后面加上
--ignore-certificate-errors --allow-running-insecure-content
见下:
"C:\Program Files (x86)\Google\Chrome\Application\chrome.exe" --ignore-certificate-errors --allow-running-insecure-content
这样设置之后,访问忽略了报错,访问速度也明显快了好多.