MSA 是一种 AD DS 对象类别,能够简化服务帐户的密码及 SPN 的管理。MSA 是从 Windows 7和 Windows Server 2008 R2 开始引入。
MSA 是储存在 AD DS 中当成一种 msDS-ManagedServiceAccount 对象。这个类别 ( class ) 从计算机类别继承架构概念,而从用户类别继承而来。这使得 MSA 能够实现类似用户的功能,例如:执行服务时可以提供验证和安全性的内容,同时也让 MSA 可以使用在 AD DS 中计算机对象所使用的密码自动更新机制,这是一个不需要用户互动的机制流程。
MSA 提供下列好处来简化管理:
自动密码管理。MSA 维护它自己的密码,包含自动变更密码机制。
简化 SPN 管理。如果你配置你的域是在 Windows Server 2008 R2 域功能级别或更高级别时,则会
自动进行 SPN 管理。
Let’s try to get the password of the account under which SQL Server is run.
There is:
Domain controller at Windows Server 2012 R2
SQL Server Express 2012
During the SQL Server installation specify the existing domain account (the password length is less than 14 symbols) to run it.![]()
Use the gsecdump utility to extract passwords.
Run PowerShell as administrator and run the command:
gsecdump-v2b5.exe -1
The result is:
![]()
What is Managed Service Accounts
The Managed Service Accounts (MSA) mechanism has been developed as the protection from such attacks in Windows Server 2008 R2.
Managed Service Accounts are managed accounts in a domain that provide automatic password management and simplified management of the participant service names including delegating control to other administrators.
Advantages of Managed Service Accounts
An automatic password change. By default a password is changed every 30 days
A complex password. A complex, automatically generated password consisting of 240 random symbols (the first half includes English letters, the second half — numerals and other symbols)
No superfluous rights
An opportunity to use one MSA on several servers (gMSA) in case when all service instances should use a single subject, e.g., for using in NLB
SPN Management
Automatic update of the SPN after the renaming
server account
dnshostname property of the server account
changing addition-aldnshostname property of the server account
changing additionalsam-accountname property of the server account
Services that support MSA:
IIS
AD LDS
SQL Server 2008 R2 SP1, 2012
MS Exchange 2010, 2013
MSA Requirements
Domain and forest level – Windows Server 2008 R2
Windows Server 2008 R2, Windows 7 (Professional, Enterprise, Ultimate) and above
.Net Framework 3.5x
Active Directory administration module for PowerShell
The installed patch KB2494158
If a forest and a domain don’t have the 2008 R2 (MSA) and 2012 (gMSA) levels, you have to increase the forest level using the command:
adprep /forestprep
And increase the domain level using the command:
adprep /domainprep
in each domain, in which you have to create and use managed service accounts.
How to Enable MSA in PowerShell
Run the cmdlet:
Import-Module ActiveDirectory
To create an MSA account, you have to run the cmdlet:
New-ADServiceAccount serviceaccount -RestrictToSingleComputer
where serviceaccount is the name of the MSA account
The parameter RestrictToSingleComputer means that MSA will be linked only to a single server. You can go to Active Directory Users and Computers and make sure that MSA has been created (for the section Managed Service Accounts to appear, you have to enable Advanced Features in the View menu of the AD snap-in).

To link MSA to the server, run the cmdlet:
Add-ADComputerServiceAccount -Identity server -ServiceAccount serviceaccount
where server is the name of the server which is associated with MSA
serviceaccount is the name of the MSA
To check if the operation has succeeded, go to Active Directory Users and Computers, then move to the server properties and check msDS-HostServiceAccount attribute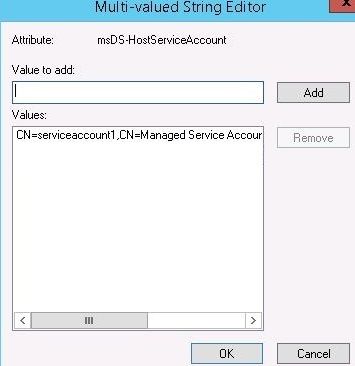
Install the managed service account on the local computer
You have to run the cmdlet:Install-ADServiceAccount -Identity serviceaccount
where serviceaccount is the name of the MSA
Test the MSA (Windows 8.1, Windows PowerShell 4.0, Windows Server 2012 R2)
Run the cmdlet:Test-ADServiceAccount serviceaccount
where serviceaccount is the name of the MSA
It returns the value True or FalseSet to run Windows service as MSA and restart the service.
Don’t forget to put ‘$‘ at the end of the MSA name
The field Password should be left empty.
Let’s check the service account password using the gsecdump utility
Group Managed Service Accounts in Windows Server 2012
In Windows Server 2012 there appeared Group Managed Service Accounts (gMSA). They allow to link a managed account not to a single server, but to several of them.
It can become necessary, for example, in Network Load Balancing or Windows cluster.
Requirements:
Schema level – Windows Server 2012
Windows Server 2012 (R2) domain controller running Microsoft Key Distribution Service
Windows Server 2012, 2012 R2, 8, 8.1
Active Directory administration module for PowerShell
How to Enable gMSA in PowerShell
Make sure that Microsoft Key Distribution Service is on “Microsoft Key Distribution Service uses a shared secret to generate account keys. These keys are changed from time to time. Along the other attributes of the Group Managed Service Accounts the Windows Server 2012 domain controller gets a password for a key provided by key distribution services. By addressing to the Windows Server 2012 domain controller Windows Server 2012 and Windows 8 hosts can get a current and a previous passwords.”
Create a Root Key
Root Key can be created with the cmdlet:Add-KdsRootKey
To create a new Root Key, run the following cmdlet:
Add-KdsRootKey -EffectiveImmediately
In this case the key will be available in 10 hours, until replicated.
You can also run a cmdlet:Add-KdsRootKey -EffectiveTime ((get-data).addhours(-10))
Then the key will become available immediately (10 hours of work are saved)
Create gMSA
Run the cmdlet:New-ADServiceAccount serviceaccount -DNSHostName tst.test.com -PrincipalsAllowedToRetrieveManagedPasswork $test
where serviceaccount is the name of the gMSA
tst.test.com is the name of the server, on which a Root Key has been created
$test is the name of the server that can address KDS to get dataYou can go to Active Directory Users and Computers and make sure that gMSA has been created (for the section Managed Service Accounts to appear, you have to enable Advanced Features in the View menu of the AD snap-in).
Install the managed service account on the local computer
You have to run the cmdlet:Install-ADServiceAccount -Identity serviceaccount
where serviceaccount is the name of the gMSA
Test the gMSA (Windows 8.1, Windows PowerShell 4.0, Windows Server 2012 R2)
Run the cmdlet:Test-ADServiceAccount serviceaccount
where serviceaccount is the name of the gMSA
It returns the value True or FalseSet to run Windows service as gMSA and restart the service.
Don’t forget to put ‘$’ at the end of the gMSA name
The field Password should be left empty.
Let’s check the service account password using the gsecdump utility![]()
MSA/gMSA can be uninstalled using the cmdlet Uninstall-ADServiceAccount
You can set MSA/gMSA parameters with the cmdlet Set-ADServiceAccount
Set the interval of password change:
Set-ADServiceAccount serviceaccount -ManagedPasswordIntervalInDays 60
where serviceaccount is the name of the gMSA
60 is a period of time, after which the password will be changed
Set Kerberos encryption algorithms to be used by MSA
Variants: RC4, AES128, AES256
Set-ADServiceAccount serviceaccount -KerberosEncryptionType RC4,AES128,AES256
Set SPN @{Add=added SPN}
Set NetBIOS name of the service (SAMAccountName)
If it is not set, an ID Name is used
If it is set, the display name in AD will be from Name and the login ID will be from SAMAccountName
Set-ADServiceAccount serviceaccunt -SamAccountName test
MSA is great way to improve the network security.
转自:http://woshub.com/active-directory-managed-service-accounts/